ansible自動化管理windows系統實戰
1、說明
日常系統自動化運維過程中難免會有windows系列服務器,就開源軟件來說目前大多的對windows批量管理兼容性不太好;不像Linux系統便捷,但現實中確實有些業務需要跑在windows上;搜索查找折騰一番後,發現python開發的ansible(已經被redhat收購)有比較好的解決方案,通過一番折騰,整理出來,以備忘交流;
2、實驗環境
服務器端:
CentOS7.4_x64 自帶python 2.7.5 ip:172.16.3.167
源碼安裝ansible
被管理windows端:
win7sp1_x32 需要powershell 3.0+ ip:172.16.3.188 並開啟winrm服務 開啟防火墻規則
3、實驗目標
能通過ansible 的各模塊對windows進行傳輸文件,管理賬號,執行腳本等批量自動化管理工作;
二、ansible配置
1、簡介
Ansible 從1.7+版本開始支持Windows,但管理機必須為Linux系統,遠程主機的通信方式也由Linux下的SSH變為PowerShell,管理機需要安裝Python的pywinrm模塊,但PowerShell需3.0+版本且Management Framework 3.0+版本,實測Windows 7 SP1和Windows Server 2008 R2及以上版本系統經簡單配置可正常與Ansible通信。
2、環境準備
以下配置在CentOS7.4_x64下
下載pip
#wget https://bootstrap.pypa.io/get-pip.py
#python get-pip.py
安裝依賴
#pip install paramiko PyYAML Jinja2 httplib2 six
3、源碼安裝ansible
# git clone git://github.com/ansible/ansible.git --recursive
#cd ./ansible
#source ./hacking/env-setup運行了env-setup腳本,就意味著Ansible基於源碼運行起來了.默認的inventory文件是 /etc/ansible/hosts
註:可以把這步添加到開機自啟中;
[win7]
172.16.3.188 ansible_ssh_user="virtual" ansible_ssh_pass="myself." ansible_ssh_port=5985 ansible_connection="winrm" ansible_winrm_server_cert_validation=ignore
註意上信息在一行;以空格隔開,[win7] 是這臺主機的標題;下面的是ip和連接信息等;
以上ansible管理端已經配置好,被管理端win7還沒有配置,相對來說稍稍麻煩點
三、被管理端win7配置
1、環境簡介
和Linux稍有區別,被管理端系統如果是Windows系列時;需預先有以下配置:
安裝Framework 3.0+ (有可能需要下載)
配置powershell策略為remotesigned (需要修改)
升級PowerShell至3.0+(win7默認是2.0)
設置Windows遠端管理,英文全稱WS-Management(WinRM)
2、環境配置
a、升級或安裝Framework 4.5
如果Framework版不滿足請至微軟官方下載
b、修改powershell策略為remotesigned
如圖: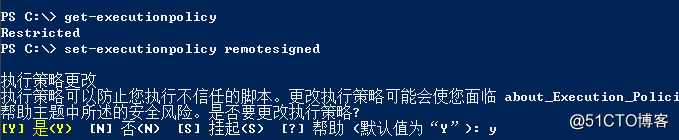
c、升級PowerShell至3.0
保存以下腳本為upgrade_to_ps3.ps1
# Powershell script to upgrade a PowerShell 2.0 system to PowerShell 3.0
# based on http://occasionalutility.blogspot.com/2013/11/everyday-powershell-part-7-powershell.html
# some Ansible modules that may use Powershell 3 features, so systems may need
# to be upgraded. This may be used by a sample playbook. Refer to the windows
# documentation on docs.ansible.com for details.
# - hosts: windows
# tasks:
# - script: upgrade_to_ps3.ps1
# Get version of OS
# 6.0 is 2008
# 6.1 is 2008 R2
# 6.2 is 2012
# 6.3 is 2012 R2
if ($PSVersionTable.psversion.Major -ge 3)
{
write-host "Powershell 3 Installed already; You don‘t need this"
Exit
}
$powershellpath = "C:\powershell"
function download-file
{
param ([string]$path, [string]$local)
$client = new-object system.net.WebClient
$client.Headers.Add("user-agent", "PowerShell")
$client.downloadfile($path, $local)
}
if (!(test-path $powershellpath))
{
New-Item -ItemType directory -Path $powershellpath
}
# .NET Framework 4.0 is necessary.
#if (($PSVersionTable.CLRVersion.Major) -lt 2)
#{
# $DownloadUrl = "http://download.microsoft.com/download/B/A/4/BA4A7E71-2906-4B2D-A0E1-80CF16844F5F/dotNetFx45_Full_x86_x64.exe"
# $FileName = $DownLoadUrl.Split(‘/‘)[-1]
# download-file $downloadurl "$powershellpath\$filename"
# ."$powershellpath\$filename" /quiet /norestart
#}
#You may need to reboot after the .NET install if so just run the script again.
# If the Operating System is above 6.2, then you already have PowerShell Version > 3
if ([Environment]::OSVersion.Version.Major -gt 6)
{
write-host "OS is new; upgrade not needed."
Exit
}
$osminor = [environment]::OSVersion.Version.Minor
$architecture = $ENV:PROCESSOR_ARCHITECTURE
if ($architecture -eq "AMD64")
{
$architecture = "x64"
}
else
{
$architecture = "x86"
}
if ($osminor -eq 1)
{
$DownloadUrl = "http://download.microsoft.com/download/E/7/6/E76850B8-DA6E-4FF5-8CCE-A24FC513FD16/Windows6.1-KB2506143-" + $architecture + ".msu"
}
elseif ($osminor -eq 0)
{
$DownloadUrl = "http://download.microsoft.com/download/E/7/6/E76850B8-DA6E-4FF5-8CCE-A24FC513FD16/Windows6.0-KB2506146-" + $architecture + ".msu"
}
else
{
# Nothing to do; In theory this point will never be reached.
Exit
}
$FileName = $DownLoadUrl.Split(‘/‘)[-1]
download-file $downloadurl "$powershellpath\$filename"
Start-Process -FilePath "$powershellpath\$filename" -ArgumentList /quiet 腳本來源於github upgrade_to_ps3.ps1
右擊-->以管理員運行 稍等幾分鐘(具體時間看下載的速度,只要任務管理器中有powershell就說明還在下載安裝),系統會自動重啟升級安裝powershell到3.0
如圖: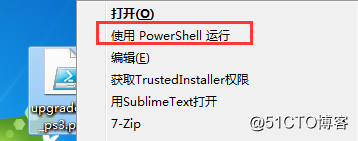
重啟後查看powershell信息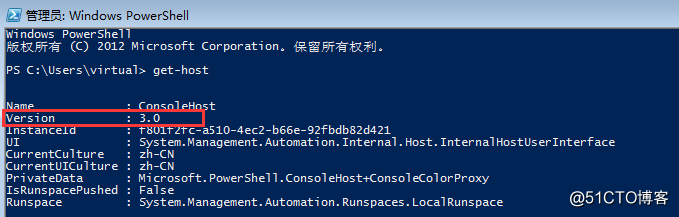
d、設置Windows遠端管理(WS-Management,WinRM)服務
winrm 服務默認都是未啟用的狀態;註意以下操作在cmd中執行,而非powershell中
對winrm服務進行基礎配置:
winrm quickconfig
C:\Users\san02>winrm quickconfig
已在此計算機上運行 WinRM 服務。
WinRM 沒有設置成為了管理此計算機而允許對其進行遠程訪問。
必須進行以下更改:
在 HTTP://* 上創建 WinRM 偵聽程序接受 WS-Man 對此機器上任意 IP 的請求。
啟用 WinRM 防火墻異常。
執行這些更改嗎[y/n]? y
WinRM 已經進行了更新,以用於遠程管理。
在 HTTP://* 上創建 WinRM 偵聽程序接受 WS-Man 對此機器上任意 IP 的請求。
WinRM 防火墻異常已啟用。
查看winrm service listener
winrm e winrm/config/listener
C:\Users\san02>winrm e winrm/config/listener
Listener
Address = *
Transport = HTTP
Port = 5985
Hostname
Enabled = true
URLPrefix = wsman
CertificateThumbprint
ListeningOn = 127.0.0.1, 172.16.3.137, ::1, fe80::100:7f:fffe%13, fe80::5efe
:172.16.3.137%12, fe80::4865:97de:bb1f:877%11
配置auth 為true(默認為false)
winrm set winrm/config/service/auth @{Basic="true"}C:\Users\san02>winrm set winrm/config/service/auth @{Basic="true"}
Auth
Basic = true
Kerberos = true
Negotiate = true
Certificate = false
CredSSP = false
CbtHardeningLevel = Relaxed
配置允許非加密方式
winrm set winrm/config/service @{AllowUnencrypted="true"}
C:\Users\san02>winrm set winrm/config/service @{AllowUnencrypted="true"}
Service
RootSDDL = O:NSG:BAD:P(A;;GA;;;BA)(A;;GR;;;IU)S:P(AU;FA;GA;;;WD)(AU;SA;GXGW;
;;WD)
MaxConcurrentOperations = 4294967295
MaxConcurrentOperationsPerUser = 1500
EnumerationTimeoutms = 240000
MaxConnections = 300
MaxPacketRetrievalTimeSeconds = 120
AllowUnencrypted = true
Auth
Basic = true
......以下省略.......至此被管理端win7的環境配置完成!
四、測試Ansible管理windows
1、查看連接狀態
[root@localhost ~]# ansible win7 -m win_ping
172.16.3.188 | SUCCESS => {
"attempts": 1,
"changed": false,
"failed": false,
"ping": "pong"
}2、獲取Windows Facts
[root@localhost ~]# ansible win7 -m setup
172.16.3.188 | SUCCESS => {
"ansible_facts": {
"ansible_architecture": "32-bit",
"ansible_bios_date": "12/01/2006",
"ansible_bios_version": "VirtualBox",
"ansible_date_time": {
"date": "2018-01-24",
"day": "24",
"epoch": "1516816620.86637",
"hour": "17",
"iso8601": "2018-01-24T09:57:00Z",
"iso8601_basic": "20180124T175700861308",
"iso8601_basic_short": "20180124T175700",
"iso8601_micro": "2018-01-24T09:57:00.861308Z",
"minute": "57",
"month": "01",
"second": "00",
......以下省略.......3、遠程執行命令
默認是亂碼,需要修改winrm模塊文件
sed -i "s#tdout_buffer.append(stdout)#tdout_buffer.append(stdout.decode(‘gbk‘).encode(‘utf-8‘))#g" /usr/lib/python2.7/site-packages/winrm/protocol.py
sed -i "s#stderr_buffer.append(stderr)#stderr_buffer.append(stderr.decode(‘gbk‘).encode(‘utf-8‘))#g" /usr/lib/python2.7/site-packages/winrm/protocol.py
獲取ip地址
[root@localhost ~]# ansible win7 -m raw -a "ipconfig"
172.16.3.188 | SUCCESS | rc=0 >>
Windows IP Configuration
Ethernet adapter 本地連接:
Connection-specific DNS Suffix . :
Link-local IPv6 Address . . . . . : fe80::c55d:90f1:8d60:5d97%11
IPv4 Address. . . . . . . . . . . : 172.16.3.188
Subnet Mask . . . . . . . . . . . : 255.255.255.0
Default Gateway . . . . . . . . . : fe80::daae:90ff:fe02:9d81%11
172.16.3.1
4、文件傳輸到win7被管理端
把/etc/issue文件復制到當前目錄(也可以直接/etc/issue)再傳送到目標主機D盤下(可以修改文件名)
[root@localhost ~]# ansible win7 -m win_copy -a "src=issue dest=D:\issue"
172.16.3.188 | SUCCESS => {
"attempts": 1,
"changed": true,
"checksum": "5c76e3b565c91e21bee303f15c728c71e6b39540",
"dest": "D:\\issue",
"failed": false,
"operation": "file_copy",
"original_basename": "issue",
"size": 23,
"src": "issue"
}
更多好用的模塊請參考官方windows可用模塊,包括自動配置等;
ansible自動化管理windows系統實戰
