第十七期 ASA【防火墻】基本配置
阿新 • • 發佈:2018-02-01
com nag extend eve -o process 2.2.0 謝謝 防火墻 實驗目的:1. DMZ發布Web服務器,Client2可以訪問Server3
- 使用命令show conn detail查看Conn表
- 查看ASA和AR【R1】的路由表
-
配置ACL禁止Client3訪問Sever2
實驗步驟:- 配置ASA及路由器:
R1:配置IP地址:interface GigabitEthernet0/0/0
ip address 192.168.1.1 255.255.255.0
interface GigabitEthernet0/0/1
ip address 10.1.1.254 255.255.255.0
interface GigabitEthernet0/0/2
ip address 10.2.2.254 255.255.255.0配置下一跳: ip route-static 0.0.0.0 0.0.0.0 192.168.1.254 -
配置ASA及端口:
ASA:配置接口:
interface GigabitEthernet0
nameif inside
security-level 100\inside默認安全級別為100
ip address 192.168.1.254 255.255.255.0
interface GigabitEthernet1
nameif outside
security-level 0\outside默認安全級別為0
ip address 192.168.8.254 255.255.255.0interface GigabitEthernet2 nameif DMZ security-level 50\\DMZ默認安全級別為0-100之間即可 ip address 192.168.3.254 255.255.255.0 route inside 10.1.1.0 255.255.255.0 192.168.1.1 1\\配置下一跳route inside 10.2.2.0 255.255.255.0 192.168.1.1 1\配置下一跳
- 配置ASA及路由器:
- 配置ACL:ASA(config)# show ru access-list
access-list ICMP extended permit icmp any any \設置ping包成功【ping為ICMP】
access-list in-to-out extended deny ip 10.1.1.0 255.255.255.0 any
access-list in-to-out extended permit ip any any
access-list DMZ extended permit tcp host 192.168.8.1 host 192.168.3.100access-list C3-S2 extended deny tcp host 192.168.3.1 host 192.168.8.100
access-list C3-S2 extended deny tcp host 192.168.3.1 host 192.168.8.100 - 調用ACL:access-group C3-S2 in interface outside
access-group DMZ in interface outside
實驗結果:
使用命令show conn detail查看Conn表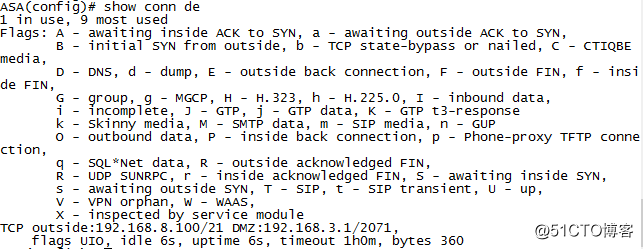
查看ASA的路由表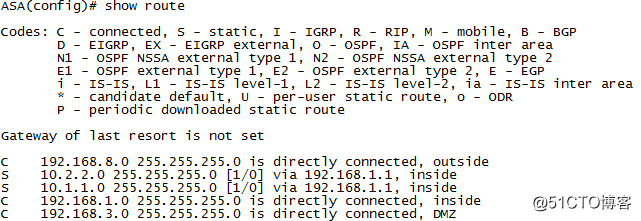
DMZ發布Web服務器,Client2可以訪問Server3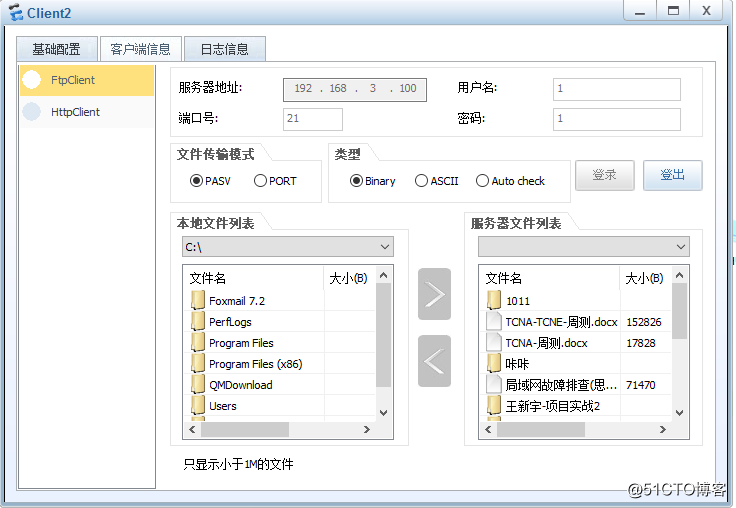
配置ACL禁止Client3訪問Server2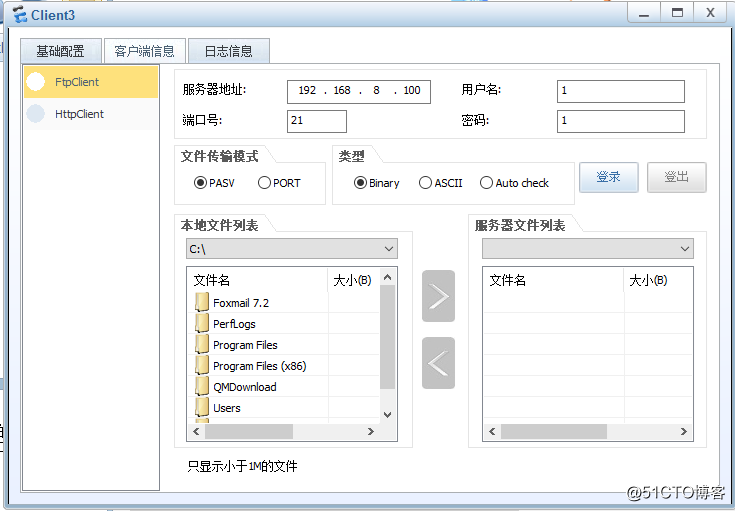
查看AR【R1】路由表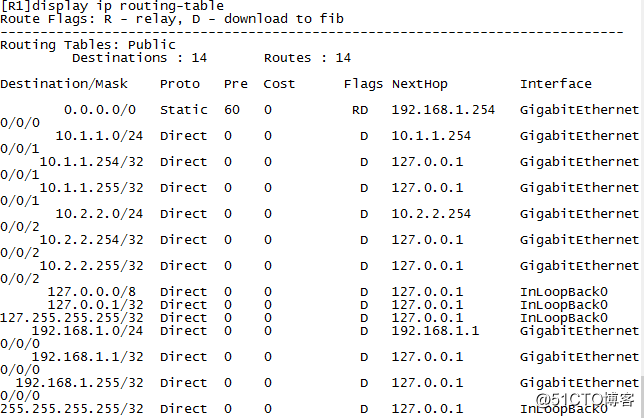
謝謝大家支持
第十七期 ASA【防火墻】基本配置
