nginx+lua+redis實現GET請求接口之黑名單(二)
阿新 • • 發佈:2018-06-06
實現GET請求接口之黑名單(二)一、概述
需求:所有訪問/webapi/**的請求必須是GET請求,而且根據請求參數過濾不符合規則的非法請求(黑名單),可以返回具體的http狀態碼,提示客戶端IP被列入黑名單,遭到請求的限制
實現思路:通過在Nginx上進行訪問限制,通過Lua來靈活實現業務需求,而Redis用於存儲黑名單列表。
二、具體實現
1.lua代碼
本例中限制規則包括(post請求,ip地址黑名單,請求參數中imsi,tel值和黑名單)
[root@git-server ~]# cat /usr/local/nginx/conf/lua/ipblacklist.lua ngx.req.read_body() local redis = require "resty.redis" local red = redis.new() red.connect(red, ‘127.0.0.1‘, ‘6379‘) local myIP = ngx.req.get_headers()["X-Real-IP"] if myIP == nil then myIP = ngx.req.get_headers()["x_forwarded_for"] end if myIP == nil then myIP = ngx.var.remote_addr end if ngx.re.match(ngx.var.uri,"^(/webapi/).*$") then local method = ngx.var.request_method if method == ‘GET‘ then local args = ngx.req.get_post_args() local hasIP = red:sismember(‘black.ip‘,myIP) local hasIMSI = red:sismember(‘black.imsi‘,args.imsi) local hasTEL = red:sismember(‘black.tel‘,args.tel) if hasIP==1 or hasIMSI==1 or hasTEL==1 then --ngx.say("This is ‘Black List‘ request") ngx.exit(ngx.HTTP_FORBIDDEN) end else ngx.say("This is ‘POST‘ request") --ngx.exit(ngx.HTTP_FORBIDDEN) end end
2.ngnx的server虛擬主機配置文件
server { listen 80; server_name www.kjios.com kjios.com; index index.html index.htm index.php; root /data/www/www.kjios.com; location ~ .*\.(php|php5)?$ { fastcgi_pass unix:/tmp/php-cgi.sock; fastcgi_index index.php; include fastcgi.conf; } location ~ .*\.(gif|jpg|jpeg|png|bmp|swf)$ { expires 30d; } location ~ .*\.(js|css)?$ { expires 1h; } location ~ /webapi/ { access_by_lua_file /usr/local/nginx/conf/lua/ipblacklist.lua; default_type ‘text/plain‘; content_by_lua ‘ ngx.say("<p> hello lua </p>")‘; } access_log /data/wwwlogs/kjios.com_access.log; }
從新加載nginx服務,使配置文件生效
3.在redis中添加黑名單規則數據
#redis-cli sadd black.ip ‘153.34.118.50‘ #redis-cli sadd black.imsi ‘460123456789‘ #redis-cli sadd black.tel ‘15888888888‘ [root@git-server ~]# redis-cli -h 127.0.0.1 -p 6379 127.0.0.1:6379> smembers black.ip 1) "124.207.48.234" 2) "21.95.1.233" 127.0.0.1:6379> smembers black.tel 1) "15888888888" 127.0.0.1:6379> smembers black.imsi 1) "460123456789" 127.0.0.1:6379>
4.驗證結果
[root@git-server ~]# curl -d "imsi=460123456789&tel=15800000000" "http://www.kjios.com/webapi/111"
This is ‘POST‘ request[root@git-server ~]# tail -3 /data/wwwlogs/kjios.com_access.log
21.95.1.233 - - [05/Jun/2018:23:18:51 +0800] "POST /myapi/111 HTTP/1.1" 404 162 "-" "curl/7.19.7 (x86_64-redhat-linux-gnu) libcurl/7.19.7 NSS/3.27.1 zlib/1.2.3 libidn/1.18 libssh2/1.4.2"
21.95.1.233 - - [05/Jun/2018:23:19:00 +0800] "POST /webapi/111 HTTP/1.1" 200 34 "-" "curl/7.19.7 (x86_64-redhat-linux-gnu) libcurl/7.19.7 NSS/3.27.1 zlib/1.2.3 libidn/1.18 libssh2/1.4.2"
21.95.1.233 - - [05/Jun/2018:23:20:56 +0800] "POST /webapi/111 HTTP/1.1" 200 34 "-" "curl/7.19.7 (x86_64-redhat-linux-gnu) libcurl/7.19.7 NSS/3.27.1 zlib/1.2.3 libidn/1.18 libssh2/1.4.2"
[root@git-server ~]# 登錄redis把家裏的ip設置為黑名單,來測試
127.0.0.1:6379> sadd black.ip 211.144.7.32
(integer) 1
127.0.0.1:6379> smembers black.ip
1) "211.144.7.32"

去掉家裏的ip黑名單測試
127.0.0.1:6379> srem black.ip 211.144.7.32
(integer) 1
127.0.0.1:6379> smembers black.ip
1) "124.207.48.234"
2) "21.95.1.233"
127.0.0.1:6379> 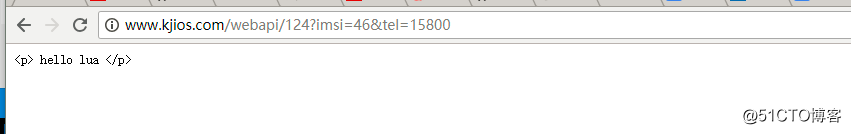
nginx訪問日誌如下:
[root@git-server ~]# tail -3 /data/wwwlogs/kjios.com_access.log
211.144.7.32 - - [05/Jun/2018:23:24:37 +0800] "GET /webapi/124?imsi=46&tel=15800 HTTP/1.1" 403 564 "-" "Mozilla/5.0 (Windows NT 10.0; WOW64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/67.0.3396.62 Safari/537.36"
211.144.7.32 - - [05/Jun/2018:23:26:38 +0800] "GET /webapi/124?imsi=46&tel=15800 HTTP/1.1" 200 50 "-" "Mozilla/5.0 (Windows NT 10.0; WOW64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/67.0.3396.62 Safari/537.36"
211.144.7.32 - - [05/Jun/2018:23:26:40 +0800] "GET /webapi/124?imsi=46&tel=15800 HTTP/1.1" 200 50 "-" "Mozilla/5.0 (Windows NT 10.0; WOW64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/67.0.3396.62 Safari/537.36"到此處演示完畢,歡迎網友們一塊討論學習lua+ngnx+redis。
nginx+lua+redis實現GET請求接口之黑名單(二)
