分組密碼SM4演算法的程式碼實現
阿新 • • 發佈:2018-11-17
SM4分組密碼演算法,原名SMS4,國家密碼管理局於2012年3月21日釋出。該演算法的分組長度為128位元,金鑰長度為128位元。加密算法與金鑰擴充套件演算法都採用32輪非線性迭代結構。解密演算法與加密演算法的結構相同,只是輪金鑰的使用順序相反,解密輪金鑰是加密輪金鑰的逆序。
- 演算法中採用的三種種基本運算:
- ⊕: 32位元異;
- <<<i : 特迴圈左移i位;
- 反序變換R(A0, A1, A2, A3) = (A3, A2, A1, A0);
#define Reverse(_x, _y) (((_x) << (_y)) | ((_x) >> (32 - (_y))))
- 金鑰相關變數的定義:
2:加密金鑰:長度128位元,表示為MK=(MK0,MK1, MK2,MK3),每4個位元組一組;
3:FK=(FK0,FK1,FK2,FK3)為系統固定引數, FK0=(A3B1BAC6),FKj=(56AA3350),FK2=(677D9197),FK3=(B27022DC);
4:CK=(CK0,CK1...CK31)為系統固定引數。
/*CK為固定引數*/ const unsigned int CK[32] = { 0x00070e15, 0x1c232a31, 0x383f464d, 0x545b6269, 0x70777e85, 0x8c939aa1, 0xa8afb6bd, 0xc4cbd2d9, 0xe0e7eef5, 0xfc030a11, 0x181f262d, 0x343b4249, 0x50575e65, 0x6c737a81, 0x888f969d, 0xa4abb2b9, 0xc0c7ced5, 0xdce3eaf1, 0xf8ff060d, 0x141b2229, 0x30373e45, 0x4c535a61, 0x686f767d, 0x848b9299, 0xa0a7aeb5, 0xbcc3cad1, 0xd8dfe6ed, 0xf4fb0209, 0x10171e25, 0x2c333a41, 0x484f565d, 0x646b7279 };
5:S盒置換:計算過程為查表過程,Sbox(69) = 22,即S表中第六行第九列的值為22;
const unsigned char Sbox[256] = { 0xd6,0x90,0xe9,0xfe,0xcc,0xe1,0x3d,0xb7,0x16,0xb6,0x14,0xc2,0x28,0xfb,0x2c,0x05, 0x2b,0x67,0x9a,0x76,0x2a,0xbe,0x04,0xc3,0xaa,0x44,0x13,0x26,0x49,0x86,0x06,0x99, 0x9c,0x42,0x50,0xf4,0x91,0xef,0x98,0x7a,0x33,0x54,0x0b,0x43,0xed,0xcf,0xac,0x62, 0xe4,0xb3,0x1c,0xa9,0xc9,0x08,0xe8,0x95,0x80,0xdf,0x94,0xfa,0x75,0x8f,0x3f,0xa6, 0x47,0x07,0xa7,0xfc,0xf3,0x73,0x17,0xba,0x83,0x59,0x3c,0x19,0xe6,0x85,0x4f,0xa8, 0x68,0x6b,0x81,0xb2,0x71,0x64,0xda,0x8b,0xf8,0xeb,0x0f,0x4b,0x70,0x56,0x9d,0x35, 0x1e,0x24,0x0e,0x5e,0x63,0x58,0xd1,0xa2,0x25,0x22,0x7c,0x3b,0x01,0x21,0x78,0x87, 0xd4,0x00,0x46,0x57,0x9f,0xd3,0x27,0x52,0x4c,0x36,0x02,0xe7,0xa0,0xc4,0xc8,0x9e, 0xea,0xbf,0x8a,0xd2,0x40,0xc7,0x38,0xb5,0xa3,0xf7,0xf2,0xce,0xf9,0x61,0x15,0xa1, 0xe0,0xae,0x5d,0xa4,0x9b,0x34,0x1a,0x55,0xad,0x93,0x32,0x30,0xf5,0x8c,0xb1,0xe3, 0x1d,0xf6,0xe2,0x2e,0x82,0x66,0xca,0x60,0xc0,0x29,0x23,0xab,0x0d,0x53,0x4e,0x6f, 0xd5,0xdb,0x37,0x45,0xde,0xfd,0x8e,0x2f,0x03,0xff,0x6a,0x72,0x6d,0x6c,0x5b,0x51, 0x8d,0x1b,0xaf,0x92,0xbb,0xdd,0xbc,0x7f,0x11,0xd9,0x5c,0x41,0x1f,0x10,0x5a,0xd8, 0x0a,0xc1,0x31,0x88,0xa5,0xcd,0x7b,0xbd,0x2d,0x74,0xd0,0x12,0xb8,0xe5,0xb4,0xb0, 0x89,0x69,0x97,0x4a,0x0c,0x96,0x77,0x7e,0x65,0xb9,0xf1,0x09,0xc5,0x6e,0xc6,0x84, 0x18,0xf0,0x7d,0xec,0x3a,0xdc,0x4d,0x20,0x79,0xee,0x5f,0x3e,0xd7,0xcb,0x39,0x48 };
- 演算法中使用的置換運算:
1.非線性變換t:t由4個並行的S盒構成,設輸入為 A = (a0,a1,a2,a3),輸出為 B = (b0,b1,b2,b3),t變換計算公式如下:
(b0,b1,b2,b3) = t(a0,a1,a2,a3) = (Sbox (a0), Sbox (a1), Sbox (a2), Sbox (a3))
#define SboxTrans(_A) (Sbox[(_A) >> 24 & 0xFF] << 24 ^ Sbox[(_A) >> 16 & 0xFF] << 16 ^ Sbox[(_A) >> 8 & 0xFF] << 8 ^ Sbox[(_A) & 0xFF])2.線性變換L:非線性變換t的輸出是線性變換L的輸入,本演算法中使用的L變換計算公式有兩處:
加密演算法: L1(B) = B ⊕ (B <<< 2) ⊕ ( B <<< 10) ⊕ (B <<< 18) ⊕ (B <<< 24); 金鑰擴充套件演算法:L2(B) = B⊕(B <<< 13)⊕(B <<< 23);
#define L1(_B) ((_B) ^ Rotl(_B, 2) ^ Rotl(_B, 10) ^ Rotl(_B, 18) ^ Rotl(_B, 24))
#define L2(_B) ((_B) ^ Rotl(_B, 13) ^ Rotl(_B, 23))- 金鑰擴充套件演算法
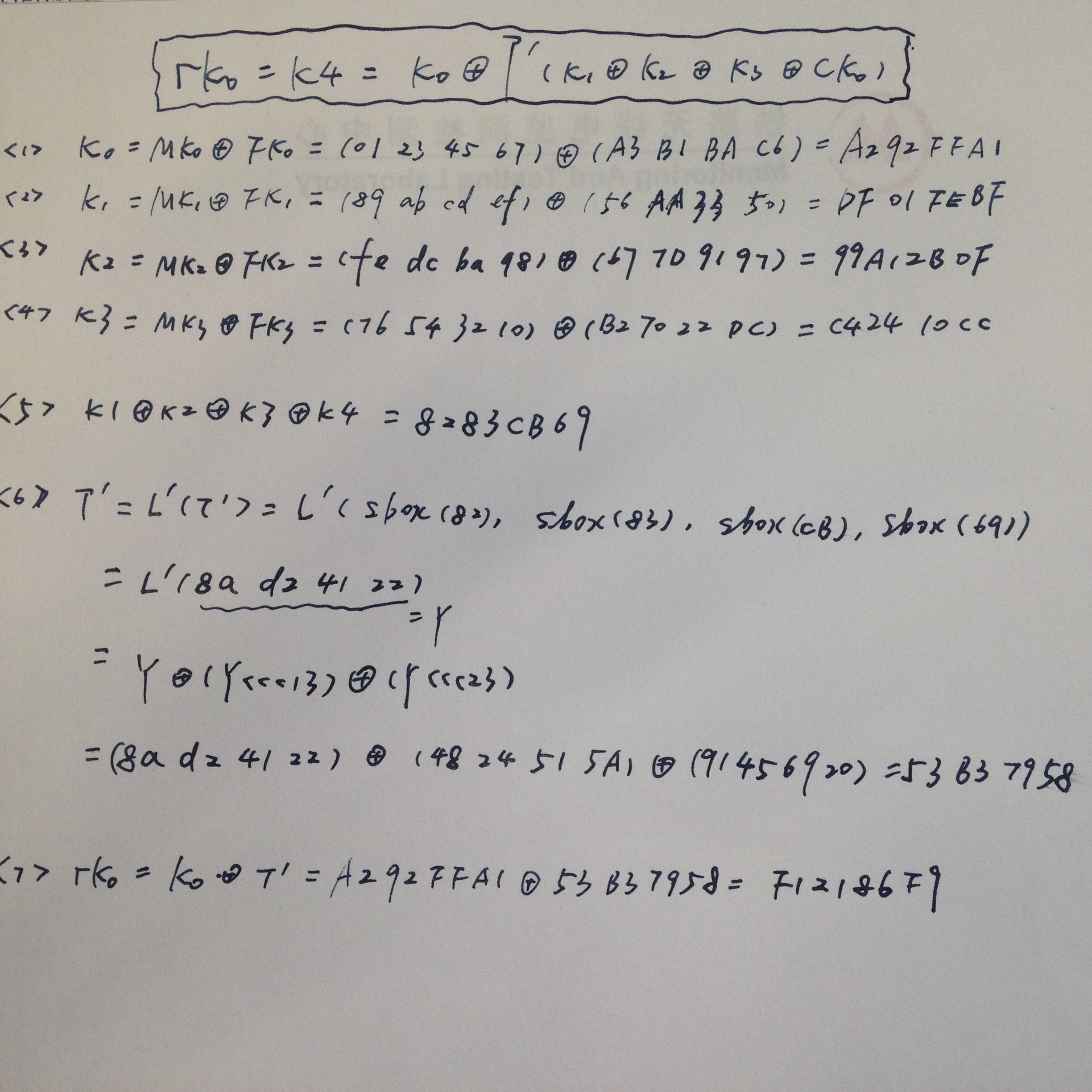
本演算法中加密演算法的輪金鑰由加密金鑰通過金鑰擴充套件演算法生成,擴充套件金鑰生成公式:
(K0, K1, K2,K3) =(MK0⊕FK0,MK1⊕FK1,MK2⊕FK2,MK3⊕FK3);
rk i = K 4 = K i ⊕ T(K i+1⊕ K i+2⊕ K i+3⊕CK i);void SM4KeyExt(unsigned char *key, unsigned int *rk, unsigned int CryptFlag)
{
unsigned int r, tmp, k0, k1, k2, k3;
/*(k0,k1,k2,k3) = (key0 xor FK0, key1 xor FK1, key2 xor FK2, key3 xor FK3)*/
/*系統引數FK0 = 0xa3b1bac6、FK1 = 0x56aa3350、FK2 = 0x677d9197、FK3 = 0xb27022dc; */
k0 = key[0] ^ 0xa3b1bac6;
k1 = key[1] ^ 0x56aa3350;
k2 = key[2] ^ 0x677d9197;
k3 = key[3] ^ 0xb27022dc;
for (r = 0; r < 32; r += 4)
{
/*rk(i) = k(4+i) = k(i) xor T[k(i+1) xor k(i+2) xor k(i+3) xor CK(i)]*/
/*合成置換T的過程包括非線性變換(ByteSub函式,從SBox中查詢)和線性變換(L2函式,移位和異或運算)*/
tmp = k1 ^ k2 ^ k3 ^ CK[r + 0];
tmp = SboxTrans(tmp);
k0 = k0 ^ L2(tmp);
rk[r + 0] = k0;
tmp = k2 ^ k3 ^ k0 ^ CK[r + 1];
tmp = SboxTrans(tmp);
k1 = k1 ^ L2(tmp);
rk[r + 1] = k1;
tmp = k3 ^ k0 ^ k1 ^ CK[r + 2];
tmp = SboxTrans(tmp);
k2 = k2 ^ L2(tmp);
rk[r + 2] = k2;
tmp = k0 ^ k1 ^ k2 ^ CK[r + 3];
tmp = SboxTrans(tmp);
k3 = k3 ^ L2(tmp);
rk[r + 3] = k3;
}
if (CryptFlag == 1)
{
for (r = 0; r < 16; r++)
tmp = rk[r], rk[r] = rk[31 - r], rk[31 - r] = tmp;
}
}- 加密演算法
加密變換公式為:
Xi+4= F(Xi, Xi+1, Xi+2,Xi+3, rki)= Xi ⊕ T(Xi+1⊕Xi+2⊕Xi+3⊕rki);
(Y0, Y1, Y2,Y3) = R(X32, X33, X34,X35) =(X35,X34,X33,X32);
本演算法的解密變換與加密變換結構相同,不同的僅是輪金鑰的使用順序。 加密時輪金鑰的使用順序為: (rk0,rk1 … rk31) , 解密時輪金鑰的使用順序為: (rk 31,rk30 … rk0 )。
void SM4Crypt(unsigned char *Input, unsigned char *Output, unsigned int *rk)
{
unsigned int r, tmp, x0, x1, x2, x3, *y;
y = (unsigned int *)Input;
x0 = y[0];
x1 = y[1];
x2 = y[2];
x3 = y[3];
for (r = 0; r < 32; r += 4)
{
/*x4 = x0 ^ T(x1 ^ x2 ^ x3 ^ rk[0])*/
tmp = x1 ^ x2 ^ x3 ^ rk[r + 0];
tmp = SboxTrans(tmp);
x0 ^= L1(tmp);
tmp = x2 ^ x3 ^ x0 ^ rk[r + 1];
tmp = SboxTrans(tmp);
x1 ^= L1(tmp);
tmp = x3 ^ x0 ^ x1 ^ rk[r + 2];
tmp = SboxTrans(tmp);
x2 ^= L1(tmp);
tmp = x0 ^ x1 ^ x2 ^ rk[r + 3];
tmp = SboxTrans(tmp);
x3 ^= L1(tmp);
}
y = (unsigned int *)Output;
/*(y0,y1,y2,y3) = (x35,x34,x33,x32)*/
y[0] = x3;
y[1] = x2;
y[2] = x1;
y[3] = x0;
}- 加密例項
加密金鑰: 01 23 45 67 89 ab cd ef fe dc ba 98 76 54 32 10
輪金鑰與每輪輸出狀態:
rk[ 0] = f12186f9 rk[ 1] = 41662b61 rk[ 2] = 5a6ab19a rk[ 3] = 7ba92077
rk[ 4] = 367360f4 rk[ 5] = 776a0c61 rk[ 6] = b6bb89b3 rk[ 7] = 24763151
rk[ 8] = a520307c rk[ 9] = b7584dbd rk[10] = c30753ed rk[11] = 7ee55b57
rk[12] = 6988608c rk[13] = 30d895b7 rk[14] = 44ba14af rk[15] = 104495a1
rk[16] = d120b428 rk[17] = 73b55fa3 rk[18] = cc874966 rk[19] = 92244439
rk[20] = e89e641f rk[21] = 98ca015a rk[22] = c7159060 rk[23] = 99e1fd2e
rk[24] = b79bd80c rk[25] = 1d2115b0 rk[26] = 0e228aeb rk[27] = f1780c81
rk[28] = 428d3654 rk[29] = 62293496 rk[30] = 01cf72e5 rk[31] = 9124a012
X[0] = 27fad345, X[1] = a18b4cb2, X[2] = 11c1e22a, X[3] = cc13e2ee, X[4] = f87c5bd5, X[5] = 33220757, X[6] = 77f4c297, X[7] = 7a96f2eb, X[8] = 27dac07f, X[9] = 42dd0f19, X[10] = b8a5da02, X[11] = 907127fa, X[12] = 8b952b83, X[13] = d42b7c59, X[14] = 2ffc5831,X[15] = f69e6888, X[16] = af2432c4, X[17] = ed1ec85e, X[18] = 55a3ba22, X[19] = 124b18aa, X[20] = 6ae7725f, X[21] = f4cba1f9, X[22] = 1dcdfa10, X[23] = 2ff60603, X[24] = eff24fdc, X[25] = 6fe46b75, X[26] = 893450ad, X[27] = 7b938f4c , X[28] = 536e4246, X[29] = 86b3e94f, X[30] = d206965e, X[31] = 681edf34. 輪金鑰計算方法:
密文: 68 1e df 34 d2 06 96 5e 86 b3 e9 4f 53 6e 42 46
