自己動手程式設計實現並講解TCP connect scan/TCP stealth scan/TCP XMAS scan/UDP scan
阿新 • • 發佈:2018-11-19
實驗5 自己動手程式設計實現並講解TCP connect scan/TCP stealth scan/TCP XMAS scan/UDP scan
實驗工具
- scapy version 2.4.0
- ipython version 5.5.0
- netcat version 1.10-41.1
實驗背景
-
實驗中可能用到的指令
- 使用netcat監聽
tcp:80埠
nc -nvlp 80 - 使用netcat監聽
udp :9000埠,並回復payload為 hello的udp資料包
echo -n "hello " | nc -nvulp 9000 - 在kali scapy 中執行python原始碼
run filepath - nmap 掃描 tcp服務
nmap ip - nmap 掃描udp服務某埠
nmap -sU ip - p 埠號
- 使用netcat監聽
-
實驗中四種 scan 掃描原始碼 (轉自此處,二次加工)
- TCP connect scan source code
# -*-coding:utf-8 -*-
#! /usr/bin/python3
import logging
logging.getLogger("scapy.runtime").setLevel( - TCP stealth scan
#! /usr/bin/python
import logging
logging.getLogger("scapy.runtime").setLevel(logging.ERROR)
from scapy.all import *
dst_ip = "192.168.1.2"
src_port = RandShort()
dst_port=80
stealth_scan_resp = sr1(IP(dst=dst_ip)/TCP(sport=src_port,dport=dst_port,flags="S"),timeout=10)
if(str(type(stealth_scan_resp))=="<type 'NoneType'>"):# no responce
with open("/mnt/share/1.txt", "w") as file:
file.write ("Filtered1")
elif(stealth_scan_resp.haslayer(TCP)):
if(stealth_scan_resp.getlayer(TCP).flags == 0x12): #receive SA port open
send_rst = sr(IP(dst=dst_ip)/TCP(sport=src_port,dport=dst_port,flags="R"),timeout=10) #reply R
with open("/mnt/share/1.txt", "w") as file:
file.write("open")
elif (stealth_scan_resp.getlayer(TCP).flags == 0x14):# receive RA port closed
with open("/mnt/share/1.txt", "w") as file:
file.write("closed")
elif(stealth_scan_resp.haslayer(ICMP)): #receive ICMP and type Destination Unreachable (3)
if(int(stealth_scan_resp.getlayer(ICMP).type)==3 and int(stealth_scan_resp.getlayer(ICMP).code) in [1,2,3,9,10,13]):
with open("/mnt/share/1.txt", "w") as file:
file.write("Filtered2")
- TCP XMAS scan
#! /usr/bin/python
import logging
logging.getLogger("scapy.runtime").setLevel(logging.ERROR)
from scapy.all import *
dst_ip = "192.168.1.2"
src_port = RandShort()
dst_port=80
xmas_scan_resp = sr1(IP(dst=dst_ip)/TCP(dport=dst_port,flags="FPU"),timeout=10)
if (str(type(xmas_scan_resp))=="<type 'NoneType'>"):
with open("/mnt/share/1.txt", "w") as file:
file.write("Open|Filtered")
elif(xmas_scan_resp.haslayer(TCP)):
if(xmas_scan_resp.getlayer(TCP).flags == 0x14):
with open("/mnt/share/1.txt", "w") as file:
file.write("Closed")
elif(xmas_scan_resp.haslayer(ICMP)):
if(int(xmas_scan_resp.getlayer(ICMP).type)==3 and int(xmas_scan_resp.getlayer(ICMP).code) in [1,2,3,9,10,13]):
with open("/mnt/share/1.txt", "w") as file:
file.write("Filtered")
- UDP scan
#! /usr/bin/python
import logging
logging.getLogger("scapy.runtime").setLevel(logging.ERROR)
from scapy.all import *
dst_ip = "192.168.1.2"
src_port = RandShort()
dst_port= 9000
dst_timeout=10
def udp_scan(dst_ip,dst_port,dst_timeout):
udp_scan_resp = sr1(IP(dst=dst_ip)/UDP(dport=dst_port),timeout=dst_timeout)
if (str(type(udp_scan_resp))=="<type 'NoneType'>"): #no response
with open("/mnt/share/1.txt", "w") as file:
file.write("open|flitered")
elif (udp_scan_resp.haslayer(UDP)): # response open
with open("/mnt/share/1.txt", "w") as file:
file.write("open")
elif(udp_scan_resp.haslayer(ICMP)): # response icmp
if(int(udp_scan_resp.getlayer(ICMP).type)==3 and int(udp_scan_resp.getlayer(ICMP).code)==3):#desination unreachable
with open("/mnt/share/1.txt", "w") as file:
file.write("closed")
elif(int(udp_scan_resp.getlayer(ICMP).type)==3 and int(udp_scan_resp.getlayer(ICMP).code) in [1,2,9,10,13]):#filter
with open("/mnt/share/1.txt", "w") as file:
file.write("closed")
else:
with open("/mnt/share/1.txt", "w") as file:
file.write(str(type(udp_scan_resp)))
udp_scan(dst_ip,dst_port,dst_timeout)
- 使用 python socket 程式設計臨時開啟 udp server,原始碼如下:
from socket import *
from time import ctime
host = ''
port = 9000
bufsize = 1024
addr = (host,port)
udpServer = socket(AF_INET,SOCK_DGRAM)
udpServer.bind(addr)
while True:
#print('Waiting for connection...')
data,addr = udpServer.recvfrom(bufsize)
data = data.decode(encoding='utf-8').upper()
#data = "at %s :%s"%(ctime(),data)
#print('recv', data)
udpServer.sendto(data.encode(encoding='utf-8'),addr)
break
udpServer.close()
print("yes")
實驗內容
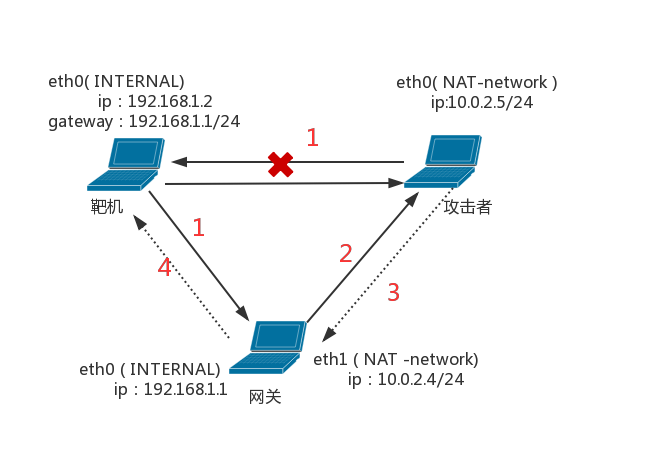
實驗拓撲圖結構如下:(沿用實驗一配置)
實驗內容及結果如下:
- 使用nc + scapy 測試四種掃描
其中開啟tcp:80服務使用nc -nvlp 80
開啟udp:9000服務使用echo -n "hello " | nc -nvulp 9000
四種 scan 均為在kali 終端 scapy中執行上文中的指令碼
| 掃描型別 | 掃描源 | 被掃描者 | 被掃描者提供的服務及埠 | 掃描源獲取的掃描結果 | |
|---|---|---|---|---|---|
| TCP connect scan | 閘道器 | 靶機 | 無 | closed2 (RST) | |
| TCP connect scan | 閘道器 | 靶機 | tcp:80 | open (SYN-ACK) | |
| TCP connect scan | 攻擊者 | 靶機 | 無 | closed1 (no response) | |
| TCP connect scan | 攻擊者 | 靶機 | tcp:80 | closed1 (no response) | |
| TCP stealth scan | 閘道器 | 靶機 | 無 | closed | |
| TCP stealth scan | 閘道器 | 靶機 | tcp:80 | open | |
| TCP stealth scan | 攻擊者 | 靶機 | 無 | filter1 (no response) | |
| TCP stealth scan | 攻擊者 | 靶機 | tcp:80 | filter1 (no response) | |
| TCP XMAS scan | 閘道器 | 靶機 | 無 | closed | |
| TCP XMAS scan | 閘道器 | 靶機 | tcp:80 | open/filtered (no response) | |
| TCP XMAS scan | 攻擊者 | 靶機 | 無 | open/filtered (no response) | |
| TCP XMAS scan | 攻擊者 | 靶機 | tcp:80 | open/filtered (no response) | |
| UDP scan | 閘道器 | 靶機 | 無 | open/filtered (no response) | |
| UDP scan | 閘道器 | 靶機 | udp:9000 | open | |
| UDP scan | 攻擊者 | 靶機 | 無 | open/filtered (no response) | |
| UDP scan | 攻擊者 | 靶機 | udp:9000 | open/filtered (no response) |
實驗完成結果和給定的查閱資料基本符合。
其中,當攻擊者試圖掃描靶機時,由於資料包根本無法到達靶機,所以攻擊者對靶機的埠掃描都是無響應的。
- 使用socket 程式設計開啟udp:9000服務,並用 nmap測試結果
掃描者 :閘道器指令nmap -sU 192.168.1.2 - p 9000
被掃描者:靶機指令run /mnt/share/udpserver.py
掃描者掃描結果
[email protected]:~# nmap -sU 192.168.1.2 -p 9000
Starting Nmap 7.70 ( https://nmap.org ) at 2018-10-18 12:01 EDT
Nmap scan report for localhost (192.168.1.2)
Host is up (0.00024s latency).
PORT STATE SERVICE
9000/udp open cslistener
MAC Address: 08:00:27:3C:0F:56 (Oracle VirtualBox virtual NIC)
Nmap done: 1 IP address (1 host up) scanned in 0.13 seconds
截圖如下:
參考資料
