PHP+MYSQL的SQL約束攻擊(原理+實現)
阿新 • • 發佈:2018-11-20
SQL約束攻擊環境搭建
MYSQL:
表結構:
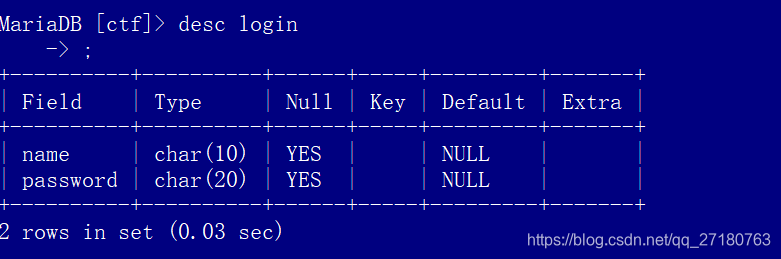
建立表命令:create table ctf(name char(10),password char(20));
表內資料:
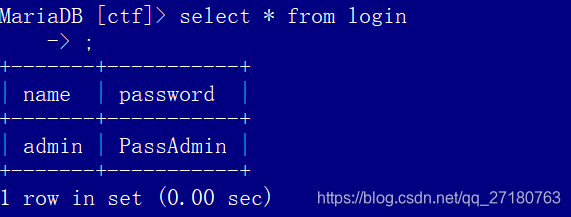
插入命令:insert into ctf values(‘admin’,‘PassAdmin’);
PHP
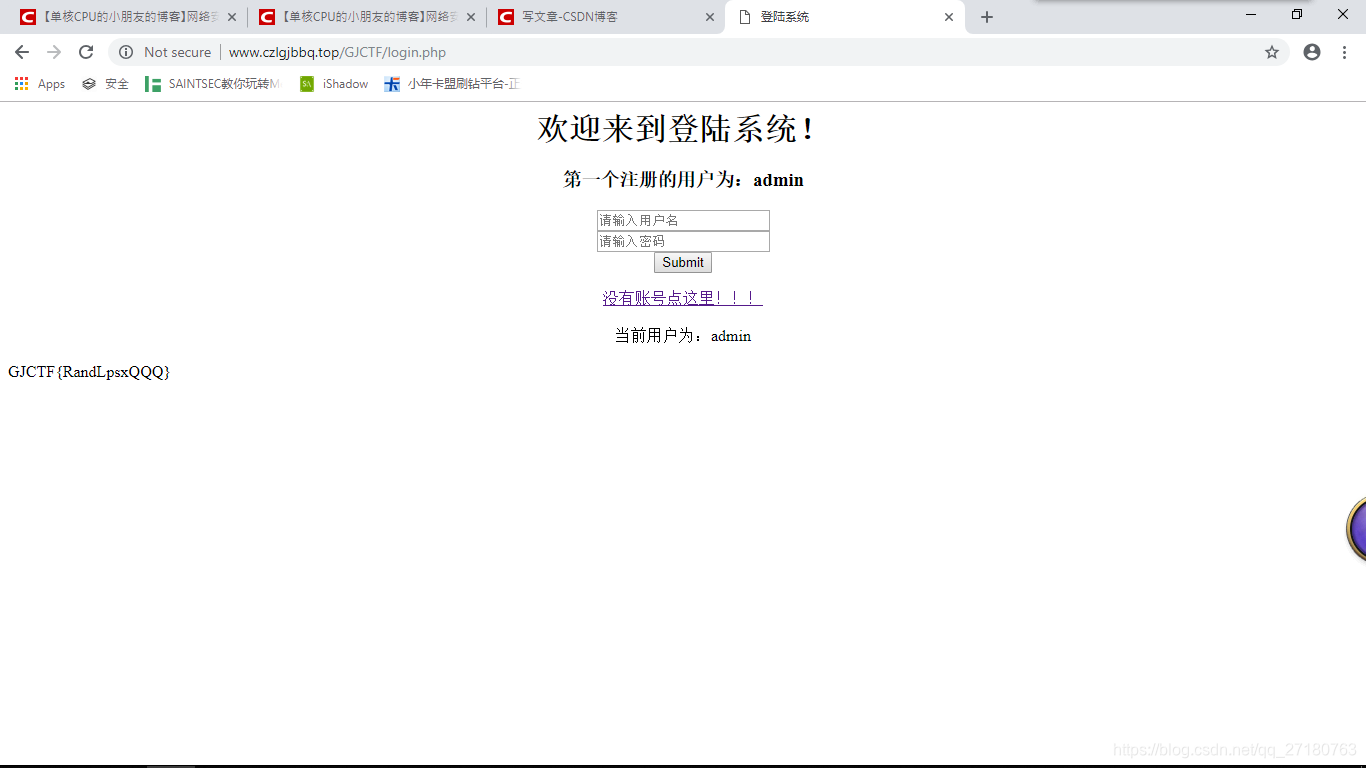
LOGIN頁面:
<html> <head><title>登陸系統</title></head> <body> <center> <h1>歡迎來到登陸系統!</h1> <h3>第一個註冊的使用者為:admin</h3> </center> <form action="./login.php" method="post"> <center><input type="text" name="username" placeholder="請輸入使用者名稱"></center> <center><input type="text" name="password" placeholder="請輸入密碼" ></center> <center><input type="submit" name="submit"></center> </form> <center><a href="./register.php">沒有賬號點這裡!!!</a><br><br></center> </body> </html> <?php if(isset($_POST['submit'])){ $username = $_POST['username']; if($username == 'admin'){ echo "<center>admin已被禁用!</center>"; exit(0); } $password = $_POST['password']; try{ $db = new PD('mysql:host=7fp9co9h.2326.dnstoo.com:5505;dbname=czlgj','czlgj_f','Wa360218171'); }catch(PDOException $e){ echo $e; } $query = "select * from login where name = ? and password = ?;"; $sql = $db -> prepare($query); $sql->execute(array($username,$password)); $arr = $sql->fetchAll(); $arr[0][0] = str_replace(' ','',$arr[0][0]); echo "<center>當前使用者為:".$arr[0][0]."</center><br>"; if(!empty($arr) && trim($arr[0][0] == 'admin')) { echo "GJCTF{RandLpsxQQQ}"; exit(0); }else if(!empty($arr)){ echo "<center>登陸成功。然並卵。</center>"; exit(0); }else{ echo "登陸失敗。"; exit(0); } } ?>
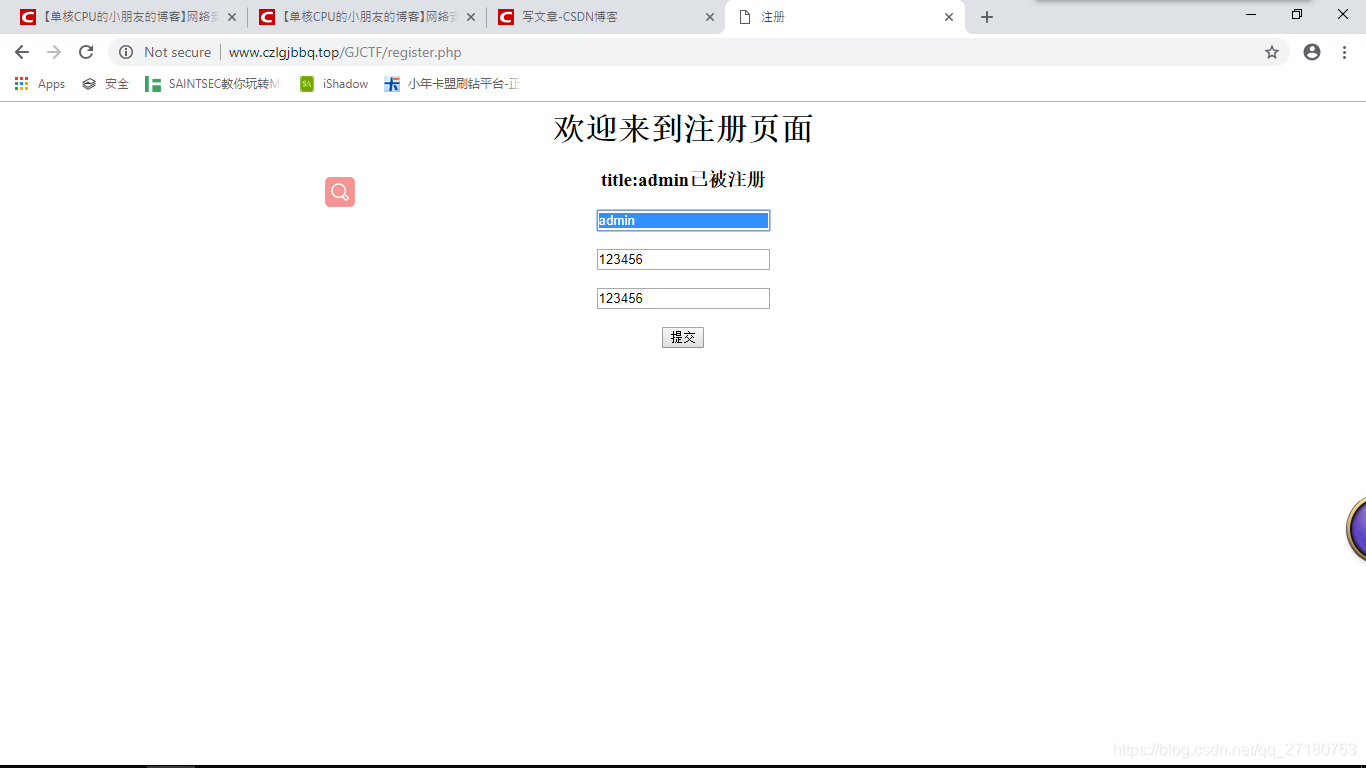
註冊介面:
<html> <head><title>註冊</title></head> <body> <center><h1>歡迎來到註冊頁面</h1></center> <center><h3>title:admin已被註冊</h3></center> <center> <form action="./register.php" method="post"> <input type="text" name="username" placeholder="請輸入使用者名稱"><br><br> <input type="text" name="password" placeholder="請輸入密碼"><br><br> <input type="text" name="password2" placeholder="請再次輸入密碼"><br><br> <input type="submit" name="submit" value="提交"><br><br> </form> </center> </body> </html> <?php if(!empty($_POST['submit'])) { $username = addslashes(htmlspecialchars($_POST['username'])); $password = addslashes(htmlspecialchars($_POST['password'])); $password2 = addslashes(htmlspecialchars($_POST['password2'])); if($username == 'admin'){ echo "<script>alert('admin已被註冊!');window.location.href='./register.php';</script>"; exit(0); } if($password !=$password2){ echo "<script>alert('請確保兩次輸入的密碼相同。');window.location.href='./register.php';</script>"; exit(0); } try{ $db = new PDO('mysql:host=7fp9co9h.2326.dnstoo.com:5505;dbname=czlgj','czlgj_f','Wa360218171'); }catch (PDOException $e){ echo $e; } $sql = $db->prepare("insert into login values(?,?)"); $sql->execute(array($username,$password)); $number = $sql->rowCount(); if($number!=0){ echo "<script>alert('註冊成功!');window.location.href='./login.php'</script>"; }else{ echo "<script>alert('註冊失敗!');window.location.href='./register.php';</script>"; } } ?>
不過我自己搭了一個平臺放在外網上了,有興趣的可以上去看看。
環境連結:http://www.czlgjbbq.top/GJCTF/login.php
攻擊演示
使用者名稱可以打很多的空格。密碼隨意。
登陸的時候直接登入,在資料庫中會忽略使用者名稱結尾的空格。所以就當成admin登陸了。所以就可以直接拿到flag了。