springboot+security+JWT實現單點登入
本次整合實現的目標:1、SSO單點登入2、基於角色和spring security註解的許可權控制。
整合過程如下:
1、使用maven構建專案,加入先關依賴,pom.xml如下:
<?xml version="1.0" encoding="UTF-8"?> <project xmlns="http://maven.apache.org/POM/4.0.0" xmlns:xsi="http://www.w3.org/2001/XMLSchema-instance" xsi:schemaLocation="http://maven.apache.org/POM/4.0.0 http://maven.apache.org/xsd/maven-4.0.0.xsd"> <modelVersion>4.0.0</modelVersion> <groupId>powerx.io</groupId> <artifactId>springboot-security-jwt</artifactId> <version>0.0.1-SNAPSHOT</version> <packaging>jar</packaging> <name>springboot-security-jwt</name><description>Demo project for Spring Boot</description> <parent> <groupId>org.springframework.boot</groupId> <artifactId>spring-boot-starter-parent</artifactId> <version>2.0.5.RELEASE</version> <relativePath/> <!-- lookup parent from repository --> </parent> <properties> <project.build.sourceEncoding>UTF-8</project.build.sourceEncoding> <project.reporting.outputEncoding>UTF-8</project.reporting.outputEncoding> <java.version>1.8</java.version> </properties> <dependencies> <dependency> <groupId>org.springframework.boot</groupId> <artifactId>spring-boot-starter-web</artifactId> </dependency> <dependency> <groupId>org.springframework.boot</groupId> <artifactId>spring-boot-starter-security</artifactId> </dependency> <dependency> <groupId>io.jsonwebtoken</groupId> <artifactId>jjwt</artifactId> <version>0.7.0</version> </dependency> <dependency> <groupId>org.springframework.boot</groupId> <artifactId>spring-boot-starter-test</artifactId> <scope>test</scope> </dependency> </dependencies> <build> <plugins> <plugin> <groupId>org.springframework.boot</groupId> <artifactId>spring-boot-maven-plugin</artifactId> </plugin> </plugins> </build> </project>
2、JWT相關的兩個過濾器:認證過濾器JWTLoginFilter和鑑權過濾器JWTAuthenticationFilter,為了簡單,這裡沒有寫專門的JWTUtils工具類來進行token的一系列操作,只是簡單的利用JWT的第三方jar生成了token。
JWTLoginFilter.java
package com.example.demo; import java.io.IOException; import java.io.PrintWriter; import java.util.ArrayList; import java.util.Date; import java.util.stream.Collectors; import javax.servlet.FilterChain; import javax.servlet.ServletException; import javax.servlet.http.HttpServletRequest; import javax.servlet.http.HttpServletResponse; import org.springframework.security.authentication.AuthenticationManager; import org.springframework.security.authentication.UsernamePasswordAuthenticationToken; import org.springframework.security.core.Authentication; import org.springframework.security.core.AuthenticationException; import org.springframework.security.web.authentication.UsernamePasswordAuthenticationFilter; import io.jsonwebtoken.Claims; import io.jsonwebtoken.Jwts; import io.jsonwebtoken.SignatureAlgorithm; /** * 驗證使用者名稱密碼正確後,生成一個token,並將token返回給客戶端 * 該類繼承自UsernamePasswordAuthenticationFilter,重寫了其中的2個方法 , * attemptAuthentication:接收並解析使用者憑證。 * successfulAuthentication:使用者成功登入後,這個方法會被呼叫,我們在這個方法裡生成token並返回。 * */ public class JWTLoginFilter extends UsernamePasswordAuthenticationFilter { private AuthenticationManager authenticationManager; public JWTLoginFilter(AuthenticationManager authenticationManager) { this.authenticationManager = authenticationManager; } @Override public Authentication attemptAuthentication(HttpServletRequest request, HttpServletResponse response) throws AuthenticationException { String username = request.getParameter("username"); String password = request.getParameter("password"); return authenticationManager.authenticate(new UsernamePasswordAuthenticationToken(username, password, new ArrayList<>())); } @Override protected void successfulAuthentication(HttpServletRequest request, HttpServletResponse response, FilterChain chain, Authentication auth) throws IOException, ServletException { Claims claims = Jwts.claims(); claims.put("role", auth.getAuthorities().stream().map(s -> s.getAuthority()).collect(Collectors.toList())); String token = Jwts.builder() .setClaims(claims) .setSubject(auth.getName()) .setExpiration(new Date(System.currentTimeMillis() + 60 * 60 * 24 * 1000)) .signWith(SignatureAlgorithm.HS512, "MyJwtSecret11").compact(); response.setCharacterEncoding("UTF-8"); response.setContentType("application/json; charset=utf-8"); String str = "{\"token\":\"" + token + "\"}"; PrintWriter out; try { out = response.getWriter(); out.print(str); out.flush(); out.close(); } catch (IOException e) { e.printStackTrace(); } } }
JWTAuthenticationFilter.java
package com.example.demo; import java.io.IOException; import java.util.List; import java.util.stream.Collectors; import javax.servlet.FilterChain; import javax.servlet.ServletException; import javax.servlet.http.HttpServletRequest; import javax.servlet.http.HttpServletResponse; import org.springframework.security.authentication.AuthenticationManager; import org.springframework.security.authentication.UsernamePasswordAuthenticationToken; import org.springframework.security.core.authority.SimpleGrantedAuthority; import org.springframework.security.core.context.SecurityContextHolder; import org.springframework.security.web.authentication.www.BasicAuthenticationFilter; import io.jsonwebtoken.Claims; import io.jsonwebtoken.Jwts; public class JWTAuthenticationFilter extends BasicAuthenticationFilter { public JWTAuthenticationFilter(AuthenticationManager authenticationManager) { super(authenticationManager); } /** * 在攔截器中獲取token並解析,拿到使用者資訊,放置到SecurityContextHolder,這樣便完成了springsecurity和jwt的整合。 */ @Override protected void doFilterInternal(HttpServletRequest request, HttpServletResponse response, FilterChain chain) throws IOException, ServletException { String header = request.getHeader("Authorization"); if (header == null || !header.startsWith("Bearer ")) { chain.doFilter(request, response); return; } UsernamePasswordAuthenticationToken authentication = getAuthentication(request); SecurityContextHolder.getContext().setAuthentication(authentication); chain.doFilter(request, response); } private UsernamePasswordAuthenticationToken getAuthentication(HttpServletRequest request) { String token = request.getHeader("Authorization"); if (token != null) { Claims claims = Jwts.parser().setSigningKey("MyJwtSecret11").parseClaimsJws(token.replace("Bearer ", "")) .getBody(); String user = claims.getSubject(); @SuppressWarnings("unchecked") List<String> roles = claims.get("role", List.class); List<SimpleGrantedAuthority> auth = roles.stream().map(s -> new SimpleGrantedAuthority(s)).collect(Collectors.toList()); if (user != null) { return new UsernamePasswordAuthenticationToken(user, null, auth); } return null; } return null; } }
3、spring security基礎配置和測試的controller。
WebSecurityConfig.java
package com.example.demo; import java.util.ArrayList; import java.util.Collection; import org.springframework.beans.factory.annotation.Autowired; import org.springframework.context.annotation.Bean; import org.springframework.context.annotation.Configuration; import org.springframework.security.config.annotation.authentication.builders.AuthenticationManagerBuilder; import org.springframework.security.config.annotation.method.configuration.EnableGlobalMethodSecurity; import org.springframework.security.config.annotation.web.builders.HttpSecurity; import org.springframework.security.config.annotation.web.configuration.EnableWebSecurity; import org.springframework.security.config.annotation.web.configuration.WebSecurityConfigurerAdapter; import org.springframework.security.core.GrantedAuthority; import org.springframework.security.core.authority.SimpleGrantedAuthority; import org.springframework.security.core.userdetails.User; import org.springframework.security.core.userdetails.UserDetailsService; import org.springframework.security.crypto.password.PasswordEncoder; import org.springframework.security.provisioning.InMemoryUserDetailsManager; @Configuration @EnableWebSecurity @EnableGlobalMethodSecurity(prePostEnabled = true) public class WebSecurityConfig extends WebSecurityConfigurerAdapter { @Autowired private MyAuthenticationProvider provider;// 自定義的AuthenticationProvider @Bean public PasswordEncoder myPasswordEncoder() { return new MyPasswordEncoder();//自定義的加密工具 } @Override protected void configure(HttpSecurity http) throws Exception { http.authorizeRequests() .anyRequest().authenticated() .and() .formLogin().loginProcessingUrl("/login") .and() .csrf().disable() .addFilter(new JWTLoginFilter(authenticationManager())) .addFilter(new JWTAuthenticationFilter(authenticationManager())); } @Override public void configure(AuthenticationManagerBuilder auth) throws Exception { auth.authenticationProvider(provider); auth.userDetailsService(userDetailsService()); } @Bean public UserDetailsService userDetailsService() { InMemoryUserDetailsManager iud = new InMemoryUserDetailsManager(); Collection<GrantedAuthority> adminAuth = new ArrayList<>(); adminAuth.add(new SimpleGrantedAuthority("ROLE_ADMIN")); iud.createUser(new User("zhangsan", "123456", adminAuth)); return iud; } }
MyAuthenticationProvider.java
package com.example.demo; import org.springframework.beans.factory.annotation.Autowired; import org.springframework.security.authentication.AuthenticationProvider; import org.springframework.security.authentication.UsernamePasswordAuthenticationToken; import org.springframework.security.core.Authentication; import org.springframework.security.core.AuthenticationException; import org.springframework.security.core.userdetails.UserDetails; import org.springframework.security.core.userdetails.UserDetailsService; import org.springframework.stereotype.Component; @Component public class MyAuthenticationProvider implements AuthenticationProvider { @Autowired private UserDetailsService userDetailsService; /** * 自定義驗證方式 */ @Override public Authentication authenticate(Authentication authentication) throws AuthenticationException { String username = authentication.getName(); String password = (String) authentication.getCredentials(); UserDetails user = userDetailsService.loadUserByUsername(username); if(user.getPassword().equals(password)) { return new UsernamePasswordAuthenticationToken(username, null, user.getAuthorities()); } return null; } @Override public boolean supports(Class<?> arg0) { return true; } }
MyPasswordEncoder.java
package com.example.demo; import org.springframework.security.crypto.password.PasswordEncoder; public class MyPasswordEncoder implements PasswordEncoder { @Override public String encode(CharSequence charSequence) { return charSequence.toString(); } @Override public boolean matches(CharSequence charSequence, String s) { return s.equals(charSequence.toString()); } }
UserController.java
package com.example.demo; import org.springframework.security.access.prepost.PreAuthorize; import org.springframework.web.bind.annotation.RequestMapping; import org.springframework.web.bind.annotation.RestController; @RestController public class UserController { @RequestMapping("/hello") public String hello() { return "hello"; } @PreAuthorize("hasAuthority('ROLE_USER')") @RequestMapping("/test1") public String test1() { return "test1"; } @PreAuthorize("hasAuthority('ROLE_ADMIN')") @RequestMapping("/test2") public String test2() { return "test2"; } }
至此,核心程式碼都以經貼上,啟動專案,使用postman訪問http://localhost:8099/login?username=zhangsan&password=123456,響應如下:

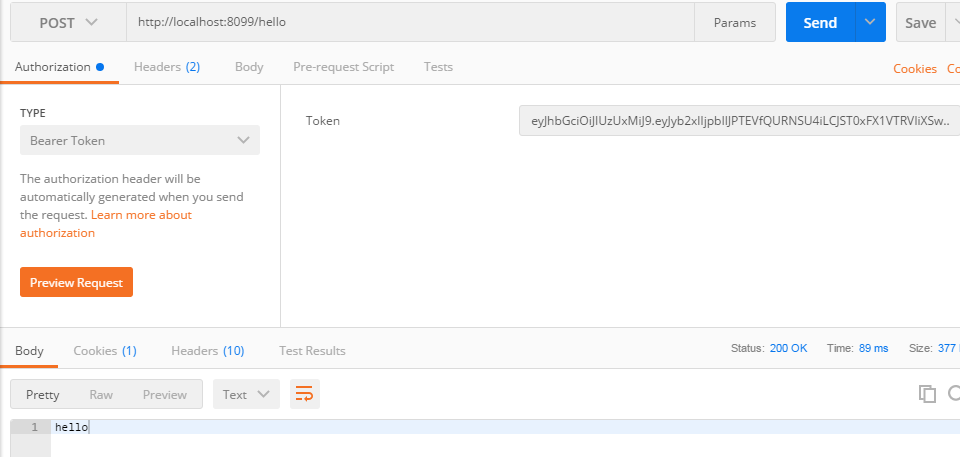
我們訪問http://localhost:8099/hello,同時在請求頭上加入auth,如下:
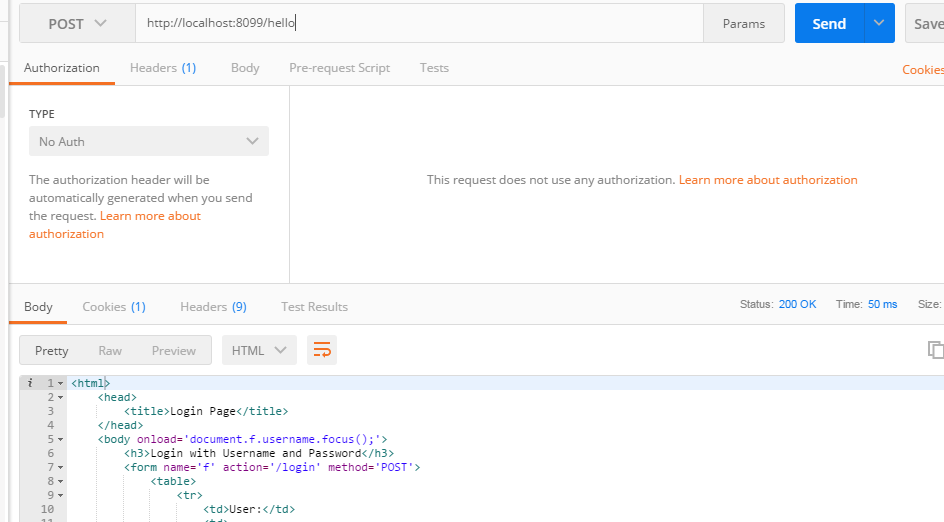
同樣的url,不加auth則會給我們返回預設的登入頁,如下:
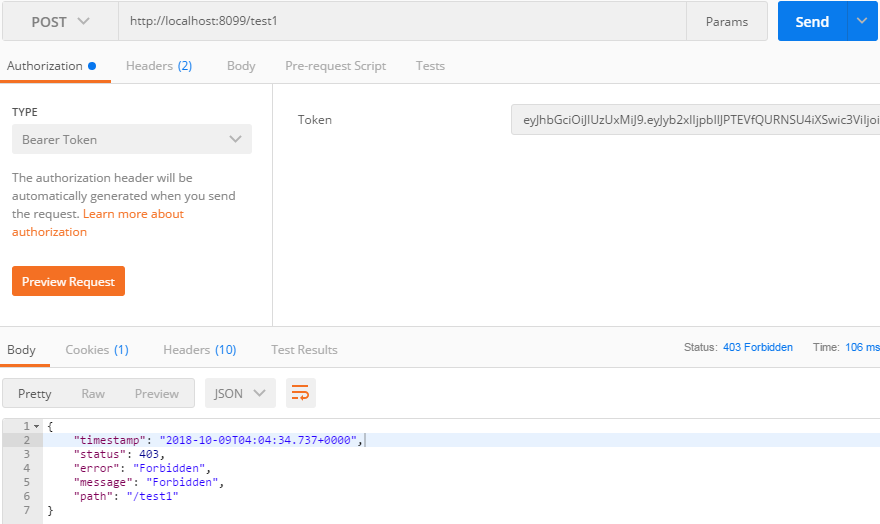
訪問http://localhost:8099/test1,則提示許可權不夠,因為我們只為zhangsan使用者分配了ROLE_ADMIN角色,而test1需要ROLE_USER。如下:
訪問http://localhost:8099/test2,如下:

為了驗證是否實現了單點登入,我們可以複製我們的專案,使用postman在第一個專案中拿到token,發現這個token在第二個專案中也可以使用,也就證明了我們的專案可以實現單點登入功能,在實際開發中,我們只需要在一個專案中去頒發token,而其他的專案中去按照相同的規則去解析這個token,這樣就可以實現單點登入,需要注意的就是在解析token時的簽名密碼要一致或者對應。
此外說一下,我在寫demo中遇到的坑,第一個就是springboot2.0版本以上必須要有一個加密工具的實現,不然會報錯;第二個就是在加入我們自己的過濾器後,必須使用預設的登入url即/login,不支援自定義的登入url了,具體原因我也不清楚;第三個就是在生成token時加入角色資訊,不能直接加入auth.getAuthorities(),不然在解析時會出現型別不匹配,具體可參考我的程式碼。
