puppet介紹與安裝
puppet是什麼
puppet是一種基於ruby語言開發的Lnux、Unix、windows平臺的集中配置管理系統。它使用自有的puppet描述語言,可管理配置檔案file、使用者user、cron任務、軟體包、系統服務等系統實體。
puppet把這些系統實體稱之為資源,puppet設計目標是簡化對這些資源的管理以及妥善處理資源間的依賴關係。
puppet依賴於C/S(客戶端/伺服器)的部署架構。它需要在puppet伺服器上安裝puppet-server軟體包(以下簡稱master),在需要管理的目標主機上安裝puppet客戶端軟體(以下簡稱agent)。
當agent連線上master後,定義在master端的配置檔案會被編譯,然後在agent上執行。每個agent預設30分鐘會連線一次master,確認配置資訊的更新情況。但是這種方式在很多場景下不是很符合系統管理員的要求,所以很多系統管理員也會將agent通過crontab(任務計劃)來管理,這樣會更加靈活一些。
puppet優點
puppet的語法允許你建立一個單獨的指令碼,用來在你所有的目標主機上建立一個使用者。所有的目標主機會依次使用適合本地系統的語法來解釋和執行這個模組。如果這個配置是在Red Hat伺服器上執行的話,建立使用者使用useradd命令,如果這個配置是在FreddBSD伺服器上執行的話,則使用adduser命令。
puppet另外一個卓越的地方就是它的靈活性。源於開源軟體的天性,你可以自由地獲得puppet的原始碼。如果你遇到問題並且有能力處理的話,你可以修改或加強puppet的程式碼使其適用於你的環境,然後解決這個問題。
puppet也是易於擴充套件的。定製軟體包的支援功能和特殊的系統環境配置能夠快速簡單地新增至puppet的安裝程式中。
基本安裝環境centos6.5
IP配置圖
192.168.186.151 Master-node.localdomain #主
192.168.186.178 Agent-node1.localdomain #從
192.168.186.163 Agent-node2.localdomain #從
192.168.186.175 Agent-node3.localdomain #從
需要官方提供的yum源
wget http://yum.puppetlabs.com/el/6/products/x86_64/puppetlabs-release-6-10.noarch.rpm
yum install puppetlabs-release-6-1.noarch.rpm
在四臺主機上去安裝官方yum源如上:^
在master主機上安裝如下:
yum install -y ruby facter puppet-server
service puppet start #啟動客戶端
service puppetmaster start #啟動服務端
chkconfig puppet on
chkconfig puppetmaster on
在客戶端(agent)安裝如下:
[[email protected] ~]# yum install -y ruby facter puppet
[[email protected] ~]# service puppet start #啟動
[[email protected] ~]# chkconfig puppet on
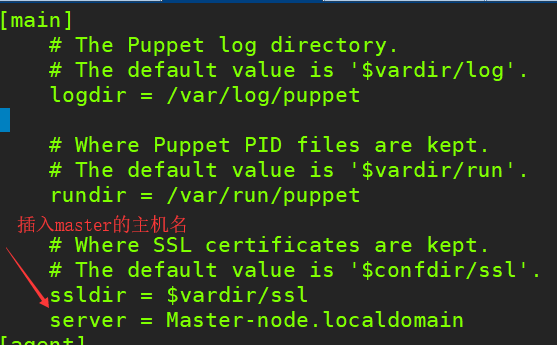
[[email protected] ~]# vim /etc/puppet/puppet.conf
[[email protected] ~]# /etc/init.d/puppet restart #重啟服務
從日誌中我們可以看出第一次啟動master端時,puppet服務會在本地建立認證中心,給自己授權證書和key,我們可以檢視/var/lib/puppet/ssl看到那些證書和key。如下:
[[email protected] ~]# tail -f /var/log/messages
......
Jul 25 15:02:13 puppet01 puppet-master[23689]: Signed certificate request
for
ca
Jul 25 15:02:14 puppet01 puppet-master[23689]: Master-node has a waiting certificate request
Jul 25 15:02:14 puppet01 puppet-master[23689]: Signed certificate request
for
Master-node
Jul 25 15:02:14 puppet01 puppet-master[23689]: Removing
file
Puppet::SSL::CertificateRequest Master-node at
'/var/lib/puppet/ssl/ca/requests/Master-node.pem'
Jul 25 15:02:14 puppet01 puppet-master[23689]: Removing
file
Puppet::SSL::CertificateRequest Master-node at
'/var/lib/puppet/ssl/certificate_requests/Master-node.pem'
Jul 25 15:02:14 puppet01 puppet-master[23727]: Reopening log files
Jul 25 15:02:14 puppet01 puppet-master[23727]: Starting Puppet master version 3.8.7
Jul 25 15:03:00 puppet01 puppet-master[23727]: puppet02.bkjk.cn has a waiting certificate request
在實際操作的過程中日誌的顯示結果有差異
[[email protected] ~]
# ll /var/lib/puppet/ssl
drwxr-xr-x. 5 puppet puppet 4096 1月 1 19:38 ca
drwxr-xr-x. 2 puppet puppet 4096 1月 1 19:39 certificate_requests
drwxr-xr-x. 2 puppet puppet 4096 1月 1 19:39 certs
drwxr-x---. 2 puppet puppet 4096 1月 1 19:38 private
drwxr-x---. 2 puppet puppet 4096 1月 1 19:39 private_keys
drwxr-xr-x. 2 puppet puppet 4096 1月 1 19:39 public_keys
這個目錄下的資訊和
/etc/puppet/puppet
.conf檔案中配置的ssldir路徑是對應的
在檢視master端給自己授權的證書檔案
[[email protected] ~]
# ll /var/lib/puppet/ssl/ca/signed
-rw-r--r--. 1 puppet puppet 2098 1月 1 19:39 master-node.localdomain.pem
一、手動註冊(批量效率高)
手動註冊是由Agent端先發起證書申請請求,然後由Puppetserver端確認認證方可註冊成功,這種註冊方式安全係數中等,逐一註冊(puppet cert --sign certnmame)
在節點數量較大的情況下是比較麻煩的,效率也低,批量註冊(puppet cert --sign --all)效率很高,一次性便可註冊所有的Agent的請求,但是這種方式安全係數較低,
因為錯誤的請求也會被註冊上。
1)需要先在Agent節點申請註冊(三臺Agent節點機都要操作)
由於已經Agent的puppet.conf檔案裡設定了server地址,因此下面向Master請求認證的命令中不需要跟服務端地址。
否則需要在下面的命令中新增Master服務端地址,即新增
"--server Master-node"
[[email protected] ~]
# puppet agent --test
Info: Creating a new SSL key
for
agent-node1
Info: Caching certificate
for
ca
Info: csr_attributes
file
loading from
/etc/puppet/csr_attributes
.yaml
Info: Creating a new SSL certificate request
for
agent-node1
Info: Certificate Request fingerprint (SHA256): E0:B4:04:52:46:C0:D4:38:92:7B:EA:90:3A:5E:EF:D8:6E:85:D3:61:77:6A:34:10:24:0F:15:B6:1A:9C:13:EC
Info: Caching certificate
for
ca
Exiting; no certificate found and waitforcert is disabled
2)Master伺服器端確定認證
現在Master伺服器端檢視認證情況
[[email protected] ~]
# puppet cert --list
"agent-node2.localdomain" (SHA256) 7F:18:02:1F:7B:AB:F6:15:41:1C:C5:5A:ED:9A:40:16:22:55:AA:13:FF:A1:F0:4A:80:E9:AC:0B:3D:6D:88:5F
"agent-node3.localdomain" (SHA256) 35:B6:F8:D0:2A:CC:FD:2A:66:A1:43:D9:CA:4A:C9:CC:12:42:1E:5A:04:2C:4F:1B:C3:CC:49:1A:AB:C5:19:14
[[email protected] ~]
# puppet cert --list --all //加--all引數,就能檢視到puppet所有簽發的本地證書了
"agent-node2.localdomain" (SHA256) 7F:18:02:1F:7B:AB:F6:15:41:1C:C5:5A:ED:9A:40:16:22:55:AA:13:FF:A1:F0:4A:80:E9:AC:0B:3D:6D:88:5F
"agent-node3.localdomain" (SHA256) 35:B6:F8:D0:2A:CC:FD:2A:66:A1:43:D9:CA:4A:C9:CC:12:42:1E:5A:04:2C:4F:1B:C3:CC:49:1A:AB:C5:19:14
+ "master-node.localdomain" (SHA256) D4:A4:44:54:FA:2B:A0:A2:53:CD:DA:FE:B7:85:F0:26:49:24:2A:06:E1:89:B1:41:5B:04:97:4D:76:07:AD:34 (alt names: "DNS:Master-node.localdomain", "DNS:master-node.localdomain", "DNS:puppet", "DNS:puppet.localdomain")
以上結果中:
左邊有+號的,表示已經簽發,puppet首先會給自己簽發一個本地證書;客戶端的證書前沒+號,這就等待服務端簽發。
接著Master服務端簽發證書,及註冊Agent節點
[[email protected] ~]
# puppet cert --list agent-node1
[[email protected] ~]
# puppet cert --list agent-node2
[[email protected] ~]
# puppet cert --list agent-node3
[[email protected] ~]
# puppet cert --sign --all //上面三個命令是分別給單獨的一個Agent頒發證書,效率低下!可以使用這個命令代替,表示簽發所有Agent的證書
再次檢視認證情況,發現已經都認證了(+號代表已經認證)
[[email protected] ~]
# puppet cert --list --all
+ "agent-node1.localdomain" (SHA256) 26:6B:8F:36:BD:5D:58:E6:9A:99:49:13:24:7C:1D:43:6A:32:94:D7:FF:DD:2C:16:B0:A1:15:7B:9F:E9:D5:7C
+ "agent-node2.localdomain" (SHA256) 7F:18:02:1F:7B:AB:F6:15:41:1C:C5:5A:ED:9A:40:16:22:55:AA:13:FF:A1:F0:4A:80:E9:AC:0B:3D:6D:88:5F
+ "agent-node3.localdomain" (SHA256) 35:B6:F8:D0:2A:CC:FD:2A:66:A1:43:D9:CA:4A:C9:CC:12:42:1E:5A:04:2C:4F:1B:C3:CC:49:1A:AB:C5:19:14
+ "master-node.localdomain" (SHA256) D4:A4:44:54:FA:2B:A0:A2:53:CD:DA:FE:B7:85:F0:26:49:24:2A:06:E1:89:B1:41:5B:04:97:4D:76:07:AD:34 (alt names: "DNS:Master-node.localdomain", "DNS:master-node.localdomain", "DNS:puppet", "DNS:puppet.localdomain")
另一種檢視認證的方法:
[[email protected] ~]
# tree /var/lib/puppet/ssl/ //可以使用"yum install -y tree" 安裝tree命令
/var/lib/puppet/ssl/
├── ca
│ ├── ca_crl.pem
│ ├── ca_crt.pem
│ ├── ca_key.pem
│ ├── ca_pub.pem
│ ├── inventory.txt
│ ├── private
│ │ └── ca.pass
│ ├── requests
│ ├── serial
│ └── signed
│ ├── agent-node1.pem
│ ├── agent-node2.pem
│ ├── agent-node3.pem
│ └── master-node.pem
├── certificate_requests
├── certs
│ ├── ca.pem
│ └── master-node.pem
├── crl.pem
├── private
├── private_keys
│ └── master-node.pem
└── public_keys
└── master-node.pem
最後在Agent端進行motd模組測試(即客戶端取回通過的證書)
[[email protected] ~]
# puppet agent --test //--test也可以替換為-t
Info: Caching certificate for agent-node1.localdomain
Info: Caching certificate_revocation_list for ca
Info: Caching certificate for agent-node1.localdomain
Warning: Unable to fetch my node definition, but the agent run will continue:
Warning: undefined method `include?' for nil:NilClass
Info: Retrieving pluginfacts
Info: Retrieving plugin
Info: Caching catalog for agent-node1.localdomain
Info: Applying configuration version '1546343527'
Info: Creating state file /var/lib/puppet/state/state.yaml
-------------------------------------------------------------------------------
也可以直接使用命令
"puppet agent --no-daemonize --onetime --verbose --debug"
,列印證書申請過程中的詳細資訊
--no-daemonize 前臺輸出日誌
--verbose 輸入更加詳細的日誌
--debug 更加詳細的日誌,排錯的時候使用
--
test
表示測試,就帶一個–
test
引數就可以
-------------------------------------------------------------------------------
-------------------------------證書管理------------------------------
當出現問題需要重新申請證書或重新安裝puppet時使用,需要登出證書和刪除證書
登出證書既是要證書過期(--revoke)
[[email protected] ~]
# puppet cert --revoke agent-node1
Notice: Revoked certificate with serial 10
[[email protected] ~]
# puppet cert --list --all //如下,過期的證書籤名是"-"號
+ "agent-node1.localdomain" (SHA256) 26:6B:8F:36:BD:5D:58:E6:9A:99:49:13:24:7C:1D:43:6A:32:94:D7:FF:DD:2C:16:B0:A1:15:7B:9F:E9:D5:7C
+ "agent-node2.localdomain" (SHA256) 7F:18:02:1F:7B:AB:F6:15:41:1C:C5:5A:ED:9A:40:16:22:55:AA:13:FF:A1:F0:4A:80:E9:AC:0B:3D:6D:88:5F
+ "agent-node3.localdomain" (SHA256) 35:B6:F8:D0:2A:CC:FD:2A:66:A1:43:D9:CA:4A:C9:CC:12:42:1E:5A:04:2C:4F:1B:C3:CC:49:1A:AB:C5:19:14
- "master-node.localdomain" (SHA256) D4:A4:44:54:FA:2B:A0:A2:53:CD:DA:FE:B7:85:F0:26:49:24:2A:06:E1:89:B1:41:5B:04:97:4D:76:07:AD:34 (alt names: "DNS:Master-node.localdomain", "DNS:master-node.localdomain", "DNS:puppet", "DNS:puppet.localdomain")
[[email protected] ~]
# puppet cert --revoke --all //登出所有證書
上面只是讓證書失效,客戶端連線會失敗,並沒有刪除證書檔案。
刪除證書(--clean)
[[email protected] ~]
# puppet cert --clean agent-node1 //刪除agent-node1證書
[[email protected] ~]
# puppet cert --clean --all //刪除所有證書
證書籤名的過期或刪除需要重啟puppetmaster服務後才能生效。
[[email protected] ~]
# /etc/init.d/puppetmaster restart
Stopping puppetmaster: [ OK ]
Starting puppetmaster: [ OK ]
重啟後,puppet會給自己自動簽發一個本地證書
[[email protected] ~]
# puppet cert --list --all
+ "master-node.localdomain" (SHA256) D4:A4:44:54:FA:2B:A0:A2:53:CD:DA:FE:B7:85:F0:26:49:24:2A:06:E1:89:B1:41:5B:04:97:4D:76:07:AD:34 (alt names: "DNS:Master-node.localdomain", "DNS:master-node.localdomain", "DNS:puppet", "DNS:puppet.localdomain")
注意刪除證書到重新請求證書的流程:
在Master端刪除證書(puppet cert --clean agent-node1)
在Agent端刪除註冊過的證書檔案:
rm
-rf
/var/lib/puppet/ssl/
*
在Agent端重新請求證書(puppet agent ----
test
)
-----------------------------------------------------------------------------------------------------------------------------------------------
二、自動註冊(安全係數低,效率高)
這種註冊方式簡單來講是通過Puppetmaster端的ACL列表進行控制的,安全系統較低,也就是說符合預先定義的ACL列表中的所有節點請求不需要確認都會被自動註冊上,
也就是說你只需要知道ACL列表要求,其次能和PuppetMaster端通訊便可輕易註冊成功。當然,它的最大優點就是效率非常高。
1)清除Master端已經註冊的agent的證書
[[email protected] ~]
# puppet cert --clean agent-node1 //可以一個個的針對單個agent節點進行清除
[[email protected] ~]
# puppet cert --clean --all //也可以清除所有agent節點的證書
2)在agent端刪除註冊的所有資訊,包括證書。這個很重要!!當在PupperMaster端刪除agent的證書後,一定要登入對應的agent節點上執行下面的操作:刪除註冊過的證書,
否則再次註冊就會報錯失敗!
[[email protected] ~]
# rm -rf /var/lib/puppet/ssl/*
3)在master端編寫ACL列表
設定master自動簽發所有的證書
[[email protected] ~]
# vim /etc/puppet/puppet.conf //在檔案底部新增下面內容
[main]
autosign =
true
autosign =
/etc/puppet/autosign
.conf
[[email protected] ~]
# vim /etc/puppet/autosign.conf //設定下面內容,*表示允許所有域下的主機註冊本Master端的證書
*
[[email protected] ~]
# /etc/init.d/puppet restart
[[email protected] ~]
# service puppetmaster restart
[[email protected] ~]
# puppet cert --list --all
+ "master-node.localdomain" (SHA256) D4:A4:44:54:FA:2B:A0:A2:53:CD:DA:FE:B7:85:F0:26:49:24:2A:06:E1:89:B1:41:5B:04:97:4D:76:07:AD:34 (alt names: "DNS:Master-node.localdomain", "DNS:master-node.localdomain", "DNS:puppet", "DNS:puppet.localdomain")
接著在所有的Agent節點申請證書
[[email protected] ~]
# puppet agent --test
Info: Creating a new SSL key
for
agent-node1
Info: Caching certificate
for
ca
Info: csr_attributes
file
loading from
/etc/puppet/csr_attributes
.yaml
Info: Creating a new SSL certificate request
for
agent-node1
Info: Certificate Request fingerprint (SHA256): 79:F5:6B:9B:0C:38:68:B7:A6:C3:9E:E4:7E:19:76:8B:61:35:CA:D0:66:E4:81:B4:15:09:DB:24:ED:3F:E2:3F
Info: Caching certificate
for
agent-node1
Info: Caching certificate_revocation_list
for
ca
Info: Caching certificate
for
ca
Info: Retrieving pluginfacts
Info: Retrieving plugin
Info: Caching catalog
for
agent-node1
Info: Applying configuration version
'1495879417'
Notice: Finished catalog run
in
0.05 seconds
然後在Master端檢視證書是否已經自動註冊上了。如下,發現已經自動註冊了
[[email protected] ~]
# puppet cert --list --all
+ "agent-node1.localdomain" (SHA256) 26:6B:8F:36:BD:5D:58:E6:9A:99:49:13:24:7C:1D:43:6A:32:94:D7:FF:DD:2C:16:B0:A1:15:7B:9F:E9:D5:7C
+ "agent-node2.localdomain" (SHA256) 7F:18:02:1F:7B:AB:F6:15:41:1C:C5:5A:ED:9A:40:16:22:55:AA:13:FF:A1:F0:4A:80:E9:AC:0B:3D:6D:88:5F
+ "agent-node3.localdomain" (SHA256) 35:B6:F8:D0:2A:CC:FD:2A:66:A1:43:D9:CA:4A:C9:CC:12:42:1E:5A:04:2C:4F:1B:C3:CC:49:1A:AB:C5:19:14
+ "master-node.localdomain" (SHA256) D4:A4:44:54:FA:2B:A0:A2:53:CD:DA:FE:B7:85:F0:26:49:24:2A:06:E1:89:B1:41:5B:04:97:4D:76:07:AD:34 (alt names: "DNS:Master-node.localdomain", "DNS:master-node.localdomain", "DNS:puppet", "DNS:puppet.localdomain")
最後在Agent節點測試
[[email protected] ~]
# puppet agent --test
Info: Retrieving pluginfacts
Info: Retrieving plugin
Info: Caching catalog
for
agent-node1
Info: Applying configuration version
'1495879417'
Notice: Finished catalog run
in
0.07 seconds
-----------------------------------------------------------------------------------------------------------------------------------------------
三、預簽名註冊(推薦生產環境中使用此方式進行註冊,既安全
預簽名註冊是在agent端未提出申請的情況下,預先在puppet master端生成agent端的證書,然後把證書複製到agent節點對應的目錄下即可註冊成功,這樣可以避
免自動簽名的危險。這種方式安全係數最高,但是操作麻煩,需要提前預知所有節點伺服器的certname名稱,其次需要將生成的證書逐步copy到所有節點上去。
不過,如果你的系統中安裝了kickstart或者cobbler這樣的自動化工具,倒是可以將證書部分轉換成指令碼整合到統一自動化部署中
1)清除Master端已經註冊的agent的證書
[[email protected] ~]
# puppet cert --clean --all //清除所有註冊過的證書,也可以指定某個Agent節點的證書清除
[[email protected] ~]
# puppet cert --list --all //檢視證書是否已清除
[[email protected] ~]
# /etc/init.d/puppetmaster restart
2)在agent端刪除註冊的所有資訊,包括證書。
[[email protected] ~]
# rm -rf /var/lib/puppet/*
3)在Master端刪除自動註冊ACL列表
[[email protected] ~]
# mv /etc/puppet/autosign.conf /etc/puppet/autosign.conf.bak
4)在Master端預先生成Agent證書(這個只能針對agent端的節點一個個的生成證書了)
[[email protected] ~]
# puppet cert generate agent-node1
[[email protected] ~]
# puppet cert generate agent-node2
[[email protected] ~]
# puppet cert generate agent-node3
檢視證書
[[email protected] ~]
# puppet cert --list --all
+ "agent-node1.localdomain" (SHA256) 26:6B:8F:36:BD:5D:58:E6:9A:99:49:13:24:7C:1D:43:6A:32:94:D7:FF:DD:2C:16:B0:A1:15:7B:9F:E9:D5:7C
+ "agent-node2.localdomain" (SHA256) 7F:18:02:1F:7B:AB:F6:15:41:1C:C5:5A:ED:9A:40:16:22:55:AA:13:FF:A1:F0:4A:80:E9:AC:0B:3D:6D:88:5F
+ "agent-node3.localdomain" (SHA256) 35:B6:F8:D0:2A:CC:FD:2A:66:A1:43:D9:CA:4A:C9:CC:12:42:1E:5A:04:2C:4F:1B:C3:CC:49:1A:AB:C5:19:14
+ "master-node.localdomain" (SHA256) D4:A4:44:54:FA:2B:A0:A2:53:CD:DA:FE:B7:85:F0:26:49:24:2A:06:E1:89:B1:41:5B:04:97:4D:76:07:AD:34 (alt names: "DNS:Master-node.localdomain", "DNS:master-node.localdomain", "DNS:puppet", "DNS:puppet.localdomain")
6)然後把Master端預先生成的證書copy到agent端的各個節點上
[[email protected] ~]
# mkdir -p /var/lib/puppet/ssl/private_keys
[[email protected] ~]
# mkdir -p /var/lib/puppet/ssl/certs
[[email protected] ~]
# rsync -e "ssh -p22" -avpgolr 182.48.115.233:/var/lib/puppet/ssl/private_keys/agent-node1.pem /var/lib/puppet/ssl/private_keys/
[[email protected] ~]
# rsync -e "ssh -p22" -avpgolr 182.48.115.233:/var/lib/puppet/ssl/certs/agent-node1.pem /var/lib/puppet/ssl/certs/
[[email protected] ~]
# rsync -e "ssh -p22" -avpgolr 182.48.115.233:/var/lib/puppet/ssl/certs/ca.pem /var/lib/puppet/ssl/certs/
[[email protected] ~]
# mkdir -p /var/lib/puppet/ssl/private_keys
[[email protected] ~]
# mkdir -p /var/lib/puppet/ssl/certs
[[email protected] ~]
# rsync -e "ssh -p22" -avpgolr 182.48.115.233:/var/lib/puppet/ssl/private_keys/agent-node2.pem /var/lib/puppet/ssl/private_keys/
[[email protected] ~]
# rsync -e "ssh -p22" -avpgolr 182.48.115.233:/var/lib/puppet/ssl/certs/agent-node2.pem /var/lib/puppet/ssl/certs/
[[email protected] ~]
# rsync -e "ssh -p22" -avpgolr 182.48.115.233:/var/lib/puppet/ssl/certs/ca.pem /var/lib/puppet/ssl/certs/
[[email protected] ~]
# mkdir -p /var/lib/puppet/ssl/private_keys
[[email protected] ~]
# mkdir -p /var/lib/puppet/ssl/certs
[[email protected] ~]
# rsync -e "ssh -p22" -avpgolr 182.48.115.233:/var/lib/puppet/ssl/private_keys/agent-node3.pem /var/lib/puppet/ssl/private_keys/
[[email protected] ~]
# rsync -e "ssh -p22" -avpgolr 182.48.115.233:/var/lib/puppet/ssl/certs/agent-node3.pem /var/lib/puppet/ssl/certs/
[[email protected] ~]
# rsync -e "ssh -p22" -avpgolr 182.48.115.233:/var/lib/puppet/ssl/certs/ca.pem /var/lib/puppet/ssl/certs/
最後在各個Agent節點測試
[[email protected] ~]
# puppet agent -t
Info: Caching certificate_revocation_list
for
ca
Info: Retrieving pluginfacts
Info: Retrieving plugin
Info: Caching catalog
for
agent-node1
Info: Applying configuration version
'1495896021'
Info: Creating state
file
/var/lib/puppet/state/state
.yaml
Notice: Finished catalog run
in
0.07 seconds
在Master端檢視證書情況
[[email protected] ~]
# tree /var/lib/puppet/ssl/
/var/lib/puppet/ssl/
├── ca
│ ├── ca_crl.pem
│ ├── ca_crt.pem
│ ├── ca_key.pem
│ ├── ca_pub.pem
│ ├── inventory.txt
│ ├── private
│ │ └── ca.pass
│ ├── requests
│ ├── serial
│ └── signed
│ ├── agent-node1.pem
│ ├── agent-node2.pem
│ ├── agent-node3.pem
│ └── master-node.pem
├── certificate_requests
├── certs
│ ├── agent-node1.pem
│ ├── agent-node2.pem
│ ├── agent-node3.pem
│ ├── ca.pem
│ └── master-node.pem
├── crl.pem
├── private
├── private_keys
│ ├── agent-node1.pem
│ ├── agent-node2.pem
│ ├── agent-node3.pem
│ └── master-node.pem
└── public_keys
├── agent-node1.pem
├── agent-node2.pem
├── agent-node3.pem
└── master-node.pem
Puppet的Dashboard搭建
puppet dashboard是GUI(圖形使用者介面)方式管理puppet,可以分析puppet執行日誌。
1)安裝mysql
[[email protected] ~]
# yum install -y mysql mysql-devel mysql-server
[[email protected] ~]
# vim /etc/my.cnf //在[mysqld]欄位,增加下面一行內容
[mysqld]
......
max_allowed_packet = 32M
啟動服務
[[email protected] ~]
# /etc/init.d/mysqld start
[[email protected] ~]
# chkconfig mysqld on
設定mysql密碼為
"password"
[[email protected] ~]
# mysqladmin -u root password 'password'
建立一個dashboard資料庫
[[email protected] ~]
# mysql -ppassword
mysql> CREATE DATABASE dashboard CHARACTER SET utf8;
mysql> CREATE USER
'dashboard'
@
'localhost'
IDENTIFIED BY
'password'
;
mysql> GRANT ALL PRIVILEGES ON dashboard.* TO
'dashboard'
@
'localhost'
;
mysql> FLUSH PRIVILEGES;
2)安裝Passenger+Apache+Dashboard
