記一次處理簡訊盜刷問題的解決方案
前言
最近公司的註冊介面經常在半夜被惡意訪問,從而引發簡訊盜刷事件,原本在手機號等引數校驗通過後,註冊介面會對圖形驗證碼進行正確性校驗,校驗通過後再進行簡訊傳送。通過簡訊傳送記錄發現我們的圖形驗證碼很容易就被識別了,沒有起到安全過濾的作用,同時對簡訊傳送次數沒有進行上限設定,所以這此簡訊盜刷問題我們做了以下解決方案。
一、圖形驗證碼增加識別難度
1.1自定義圖形驗證碼
我們需要實現一個生成圖形驗證碼的工具類VerifyCodeImageUtil.java
import java.awt.Color;
import java.awt.Font;
import java.awt.Graphics;
import 通過以上方法生成如下圖形驗證碼
1.2使用kaptcha驗證碼元件
Kaptcha是一個基於SimpleCaptcha的驗證碼開源專案。
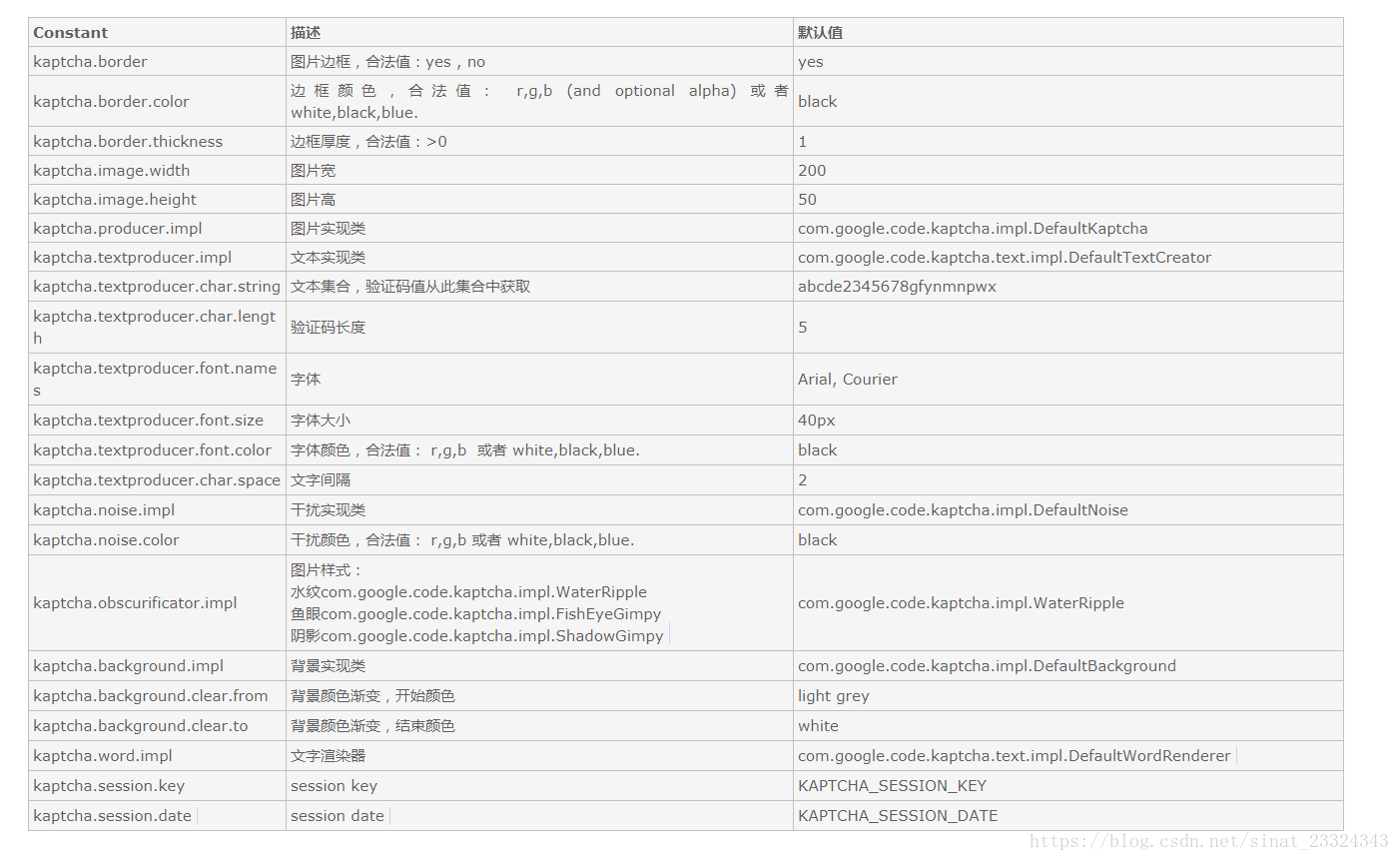
KAPTCHA 引數詳解
- pom.xml中配置依賴
<dependency>
<groupId>com.github.penggle</groupId>
<artifactId>kaptcha</artifactId>
<version>2.3.2</version>
</dependency>- 配置驗證碼Kaptcha相關設定
import java.util.Properties;
import org.springframework.context.annotation.Bean;
import org.springframework.stereotype.Component;
import com.google.code.kaptcha.impl.DefaultKaptcha;
import com.google.code.kaptcha.util.Config;
@Component
public class KaptchaConfig {
@Bean
public DefaultKaptcha getDefaultKaptcha(){
com.google.code.kaptcha.impl.DefaultKaptcha defaultKaptcha = new com.google.code.kaptcha.impl.DefaultKaptcha();
Properties properties = new Properties();
properties.setProperty("kaptcha.border", "yes");
properties.setProperty("kaptcha.border.color", "105,179,90");
properties.setProperty("kaptcha.image.width", "200");
properties.setProperty("kaptcha.image.height", "90");
properties.setProperty("kaptcha.session.key", "code");
properties.setProperty("kaptcha.textproducer.font.color", "black");
properties.setProperty("kaptcha.textproducer.font.size", "70");
properties.setProperty("kaptcha.textproducer.char.length", "4");
properties.setProperty("kaptcha.textproducer.font.names", "宋體,楷體,微軟雅黑");
Config config = new Config(properties);
defaultKaptcha.setConfig(config);
return defaultKaptcha;
}
}
或者在resources下建立myKaptcher.xml檔案
<?xml version="1.0" encoding="UTF-8"?>
<beans xmlns="http://www.springframework.org/schema/beans"
xmlns:xsi="http://www.w3.org/2001/XMLSchema-instance"
xsi:schemaLocation="http://www.springframework.org/schema/beans http://www.springframework.org/schema/beans/spring-beans.xsd">
<bean id="captchaProducer" class="com.google.code.kaptcha.impl.DefaultKaptcha">
<property name="config">
<bean class="com.google.code.kaptcha.util.Config">
<constructor-arg type="java.util.Properties">
<props>
<prop key = "kaptcha.border ">yes</prop>
<prop key="kaptcha.border.color">105,179,90</prop>
<prop key="kaptcha.textproducer.font.color">blue</prop>
<prop key="kaptcha.image.width">100</prop>
<prop key="kaptcha.image.height">50</prop>
<prop key="kaptcha.textproducer.font.size">27</prop>
<prop key="kaptcha.session.key">code</prop>
<prop key="kaptcha.textproducer.char.length">4</prop>
<prop key="kaptcha.textproducer.font.names">宋體,楷體,微軟雅黑</prop>
<prop key="kaptcha.textproducer.char.string">23456789ABCEFGHJKMNOPQRSTUVWXYZ</prop>
<prop key="kaptcha.obscurificator.impl">com.google.code.kaptcha.impl.WaterRipple</prop>
<prop key="kaptcha.noise.color">black</prop>
<prop key="kaptcha.noise.impl">com.google.code.kaptcha.impl.NoNoise</prop>
<!--<prop key="kaptcha.noise.impl">com.google.code.kaptcha.impl.DefaultNoise</prop>-->
<prop key="kaptcha.background.clear.from">185,56,213</prop>
<prop key="kaptcha.background.clear.to">white</prop>
<prop key="kaptcha.textproducer.char.space">3</prop>
</props>
</constructor-arg>
</bean>
</property>
</bean>
</beans>然後在啟動類Application中載入配置
@Configuration
@EnableAutoConfiguration
@ComponentScan(basePackages = { "com.lll" })
@SpringBootApplication
@EnableAspectJAutoProxy
@EnableAsync
@EnableScheduling
@ImportResource(locations={"classpath:mykaptcha.xml"})
public class Application extends SpringBootServletInitializer {
public static void main(String[] args) throws Exception {
SpringApplication.run(Application.class, args);
}
}- 實現類
package com.example.demo.util;
import java.awt.image.BufferedImage;
import java.io.ByteArrayOutputStream;
import javax.imageio.ImageIO;
import javax.servlet.ServletOutputStream;
import javax.servlet.http.HttpServletRequest;
import javax.servlet.http.HttpServletResponse;
import org.springframework.beans.factory.annotation.Autowired;
import org.springframework.web.bind.annotation.RequestMapping;
import com.google.code.kaptcha.impl.DefaultKaptcha;
public class KaptchaTest {
@Autowired
DefaultKaptcha defaultKaptcha;
@RequestMapping("/defaultKaptcha")
public void defaultKaptcha(HttpServletRequest httpServletRequest,HttpServletResponse httpServletResponse) throws Exception{
byte[] captchaChallengeAsJpeg = null;
ByteArrayOutputStream jpegOutputStream = new ByteArrayOutputStream();
try {
//生產驗證碼字串並儲存到session中
String createText = defaultKaptcha.createText();
httpServletRequest.getSession().setAttribute("vrifyCode", createText);
//使用生產的驗證碼字串返回一個BufferedImage物件並轉為byte寫入到byte陣列中
BufferedImage challenge = defaultKaptcha.createImage(createText);
ImageIO.write(challenge, "jpg", jpegOutputStream);
} catch (IllegalArgumentException e) {
httpServletResponse.sendError(HttpServletResponse.SC_NOT_FOUND);
return;
}
//定義response輸出型別為image/jpeg型別,使用response輸出流輸出圖片的byte陣列
captchaChallengeAsJpeg = jpegOutputStream.toByteArray();
httpServletResponse.setHeader("Cache-Control", "no-store");
httpServletResponse.setHeader("Pragma", "no-cache");
httpServletResponse.setDateHeader("Expires", 0);
httpServletResponse.setContentType("image/jpeg");
ServletOutputStream responseOutputStream =
httpServletResponse.getOutputStream();
responseOutputStream.write(captchaChallengeAsJpeg);
responseOutputStream.flush();
responseOutputStream.close();
}
}使用Kaptcha生成圖形驗證碼
二、針對ip進行訪問次數限制
2.1獲取真實的IP地址
public String getRemoteIp(HttpServletRequest request) {
String remoteIp = "";
remoteIp = request.getHeader("x-forwarded-for");
if (remoteIp == null || remoteIp.isEmpty() || "unknown".equalsIgnoreCase(remoteIp)) {
remoteIp = request.getHeader("X-Real-IP");
}
if (remoteIp == null || remoteIp.isEmpty() || "unknown".equalsIgnoreCase(remoteIp)) {
remoteIp = request.getHeader("Proxy-Client-IP");
}
if (remoteIp == null || remoteIp.isEmpty() || "unknown".equalsIgnoreCase(remoteIp)) {
remoteIp = request.getHeader("WL-Proxy-Client-IP");
}
if (remoteIp == null || remoteIp.isEmpty() || "unknown".equalsIgnoreCase(remoteIp)) {
remoteIp = request.getHeader("HTTP_CLIENT_IP");
}
if (remoteIp == null || remoteIp.isEmpty() || "unknown".equalsIgnoreCase(remoteIp)) {
remoteIp = request.getHeader("HTTP_X_FORWARDED_FOR");
}
if (remoteIp == null || remoteIp.isEmpty() || "unknown".equalsIgnoreCase(remoteIp)) {
remoteIp = request.getRemoteAddr();
}
if (remoteIp == null || remoteIp.isEmpty() || "unknown".equalsIgnoreCase(remoteIp)) {
remoteIp = request.getRemoteHost();
}
return remoteIp;
}對於通過多個代理的情況,我們會得到例如:112.28.176.62,10.102.201.130 這樣的結果,那麼第一個IP為客戶端真實IP,多個IP按照’,’分割 ,以上程式碼可以獲取到使用者沒有進行偽造的請求。
如果執行這段程式碼後仍然獲取的是Nginx代理地址的話,說明需要對Nginx進行配置。
在代理的每個location處加上以下配置:
proxy_set_header Host $http_host;
proxy_set_header X-Real-IP $remote_addr;
proxy_set_header X-Forwarded-For $proxy_add_x_forwarded_for;
proxy_set_header X-Forwarded-Proto $scheme;
Nginx反向代理後,Servlet應用通過request.getRemoteAddr()取到的IP是Nginx的IP地址,並非客戶端真實IP,通過request.getRequestURL()獲取的域名、協議、埠都是Nginx訪問Web應用時的域名、協議、埠,而非客戶端瀏覽器位址列上的真實域名、協議、埠。
Nginx的反向代理實際上是客戶端和真實的應用伺服器之間的一個橋樑,客戶端(一般是瀏覽器)訪問Nginx伺服器,Nginx再去訪問Web應用伺服器。對於Web應用來說,這次HTTP請求的客戶端是Nginx而非真實的客戶端瀏覽器,如果不做特殊處理的話,Web應用會把Nginx當作請求的客戶端,獲取到的客戶端資訊就是Nginx的一些資訊。
解決這個問題要從兩個方面來解決:
1. 由於Nginx是代理伺服器,所有客戶端請求都從Nginx轉發到Tomcat,如果Nginx不把客戶端真實IP、域名、協議、埠告訴Tomcat,那麼Tomcat應用是永遠不會知道這些資訊的,所以需要Nginx配置一些HTTP Header來將這些資訊告訴被代理的Tomcat;
2. Tomcat這一端,不能再傻乎乎的獲取直接和它連線的客戶端(也就是Nginx)的資訊,而是要從Nginx傳遞過來的HTTP Header中獲取客戶端資訊。
原連結:https://blog.csdn.net/it_0101/article/details/78390700
2.2設定訪問限制
根據IP和手機號碼針對該介面請求:
1、同一號碼在同一天內只能傳送不超過5條驗證碼;
2、同一IP在1分鐘內出現3次以上
3、同一IP在30分鐘內超過5次
4、同一IP在24*60分鐘內出現10次以上
5、同一IP在48*60內出現20以上
將以上IP列為黑名單;黑名單可以手動刪除;
經過這次的安全訪問限制,簡訊盜刷的請求在圖形驗證碼校驗時就被拒絕了,目前還沒有黑名單生成。產品方面也針對其他型別的圖形驗證碼方案進行評審,下次說不定就是人臉識別了。。。