Http Digest認證協議
其認證的基本框架為挑戰認證的結構,如下圖所示:
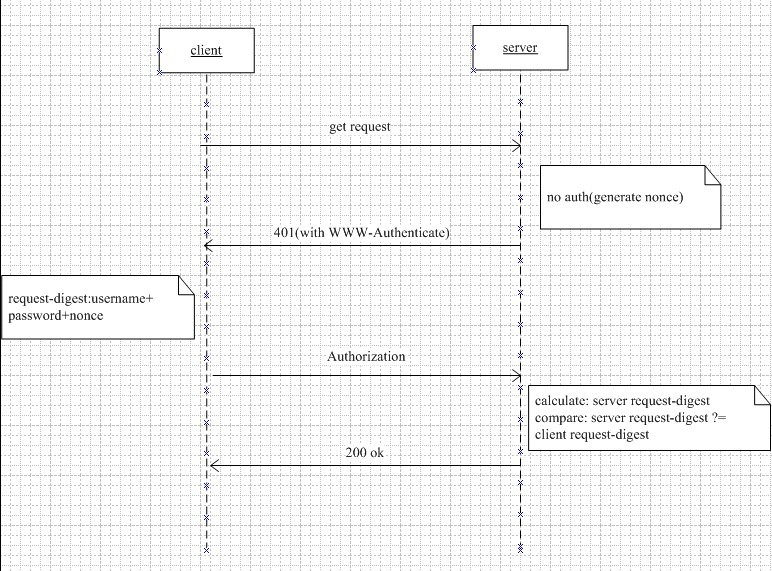
1.客戶端希望取到伺服器上的某個資源,向伺服器傳送Get請求。
2.伺服器收到客戶端的請求後,發現這個資源需要認證資訊,判斷請求報文中是否帶有Authorization頭,如果沒有,返回一個401(Unauthorized)給客戶端。在這個401的回覆中,同時伺服器會加入一個WWW-Authenticate的頭,其中有如下資訊(各個欄位的詳細解釋見RFC2617):
challenge = "Digest" digest-challenge
digest-challenge = 1#( realm | [ domain ] | nonce |
[ opaque ] |[ stale ] | [ algorithm ] |
[ qop-options ] | [auth-param] )
domain = "domain" "=" <"> URI ( 1*SP URI ) <">
URI = absoluteURI | abs_path
nonce = "nonce" "=" nonce-value
nonce-value = quoted-string
opaque = "opaque" "=" quoted-string
stale = "stale" "=" ( "true" | "false" )
algorithm = "algorithm" "=" ( "MD5" | "MD5-sess" |
token )
qop-options = "qop" "=" <"> 1#qop-value <">
qop-value = "auth" | "auth-int" | token
3.客戶端收到伺服器的401(Unauthorized)回覆後,使用伺服器回覆報文中的nonce值,加上username,password, http method, http uri利用MD5(或者伺服器指定的其他演算法)計算出request-digest,作為repsonse頭域的值。並重新發送請求,請求報文中包含Authorization 頭,其中有如下資訊:
credentials = "Digest" digest-response
digest-response = 1#( username | realm | nonce | digest-uri
| response | [ algorithm ] | [cnonce] |
[opaque] | [message-qop] |
[nonce-count] | [auth-param] )
username = "username" "=" username-value
username-value = quoted-string
digest-uri = "uri" "=" digest-uri-value
digest-uri-value = request-uri ; As specified by HTTP/1.1
message-qop = "qop" "=" qop-value
cnonce = "cnonce" "=" cnonce-value
cnonce-value = nonce-value
nonce-count = "nc" "=" nc-value
nc-value = 8LHEX
response = "response" "=" request-digest
request-digest = <"> 32LHEX <">
LHEX = "0" | "1" | "2" | "3" |
"4" | "5" | "6" | "7" |
"8" | "9" | "a" | "b" |
"c" | "d" | "e" | "f"
4.伺服器收到客戶端發來的請求後,根據username,查找出使用者的password,用和客戶端同樣的方法計算出request-digest(response)。然後和收到的request-digest進行對比,如果一致,則驗證成功,接受客戶端的請求,成功返回結果。
