DC-1靶機
阿新 • • 發佈:2020-11-06
## 文章前提概述
本文介紹DC-1靶機的滲透測試流程
涉及知識點(比較基礎):
nmap掃描網段埠服務
msf的漏洞搜尋
drupal7的命令執行利用
netcat反向shell
mysql的基本操作
sudi提權
## 基本環境搭建
靶機下載地址:[http://www.five86.com/downloads/DC-1.zip](http://www.five86.com/downloads/DC-1.zip)
[https://download.vulnhub.com/dc/DC-1.zip](https://download.vulnhub.com/dc/DC-1.zip)
VMware(windows):[https://www.52pojie.cn/thread-1026907-1-1.html](https://www.52pojie.cn/thread-1026907-1-1.html)
選擇高版本的vmware,不然可能不支援ova匯入
下載匯入開機vmware設定選擇nat模式,目的讓你的攻擊機和靶機在一個網段,可以根據網路環境自行設定只要在一個網段就行。
## 基礎資訊收集
### nmap掃描
```
nmap -A 192.168.124.0/24
```
掃描結果
開發80,111,22ssh埠
```
Host is up (0.00039s latency).
Not shown: 997 closed ports
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 6.0p1 Debian 4+deb7u7 (protocol 2.0)
| ssh-hostkey:
| 1024 c4:d6:59:e6:77:4c:22:7a:96:16:60:67:8b:42:48:8f (DSA)
| 2048 11:82:fe:53:4e:dc:5b:32:7f:44:64:82:75:7d:d0:a0 (RSA)
|_ 256 3d:aa:98:5c:87:af:ea:84:b8:23:68:8d:b9:05:5f:d8 (ECDSA)
80/tcp open http Apache httpd 2.2.22 ((Debian))
|_http-generator: Drupal 7 (http://drupal.org)
| http-robots.txt: 36 disallowed entries (15 shown)
| /includes/ /misc/ /modules/ /profiles/ /scripts/
| /themes/ /CHANGELOG.txt /cron.php /INSTALL.mysql.txt
| /INSTALL.pgsql.txt /INSTALL.sqlite.txt /install.php /INSTALL.txt
|_/LICENSE.txt /MAINTAINERS.txt
|_http-server-header: Apache/2.2.22 (Debian)
|_http-title: Welcome to Drupal Site | Drupal Site
111/tcp open rpcbind 2-4 (RPC #100000)
| rpcinfo:
| program version port/proto service
| 100000 2,3,4 111/tcp rpcbind
| 100000 2,3,4 111/udp rpcbind
| 100000 3,4 111/tcp6 rpcbind
| 100000 3,4 111/udp6 rpcbind
| 100024 1 37454/udp status
| 100024 1 39208/udp6 status
| 100024 1 52048/tcp status
|_ 100024 1 57763/tcp6 status
MAC Address: 00:0C:29:A6:59:A3 (VMware)
Device type: general purpose
Running: Linux 3.X
OS CPE: cpe:/o:linux:linux_kernel:3
OS details: Linux 3.2 - 3.16
Network Distance: 1 hop
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel
TRACEROUTE
HOP RTT ADDRESS
1 0.39 ms 192.168.124.145
```
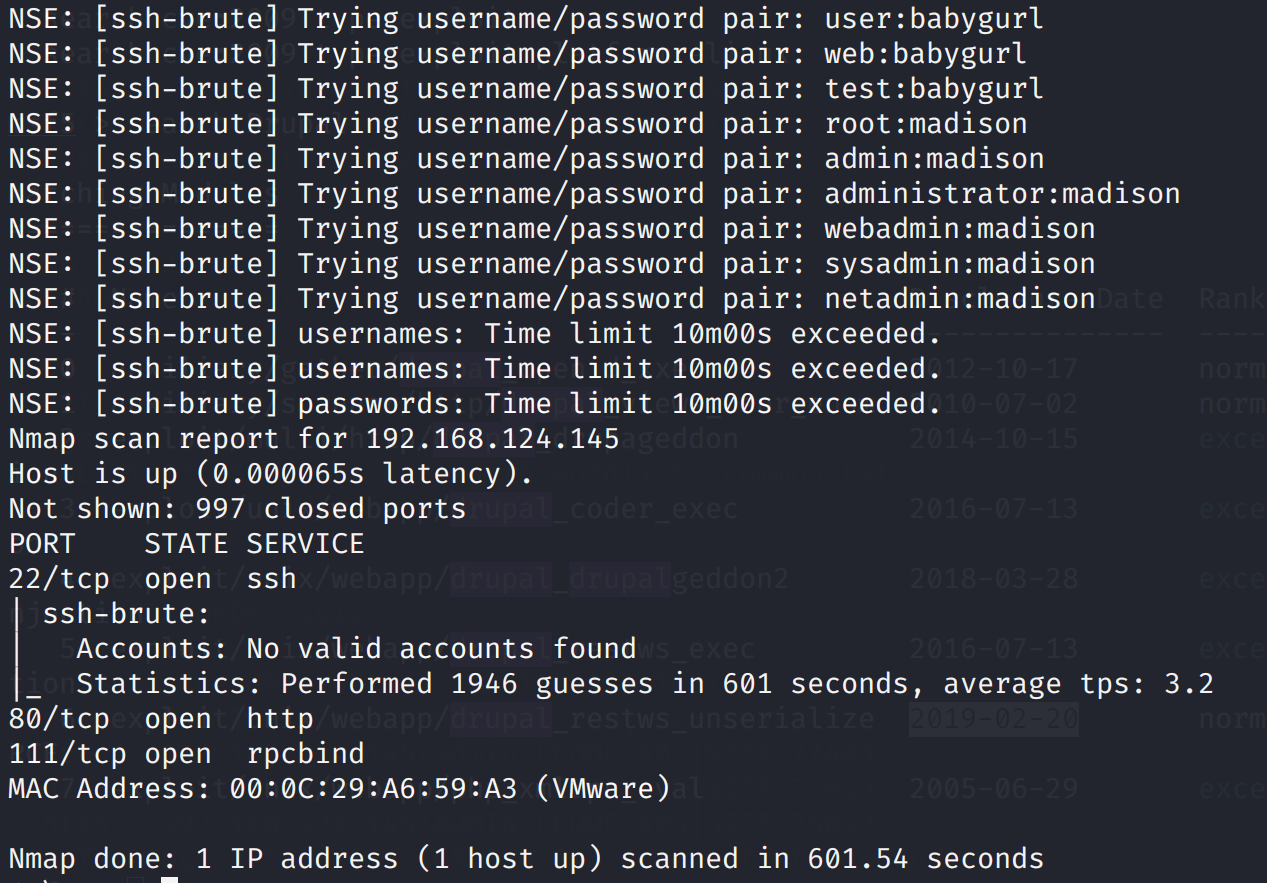
### 先爆破一下ssh吧(無結果)
```
nmap --script=ssh-brute 192.168.124.145
```
### 訪問80埠
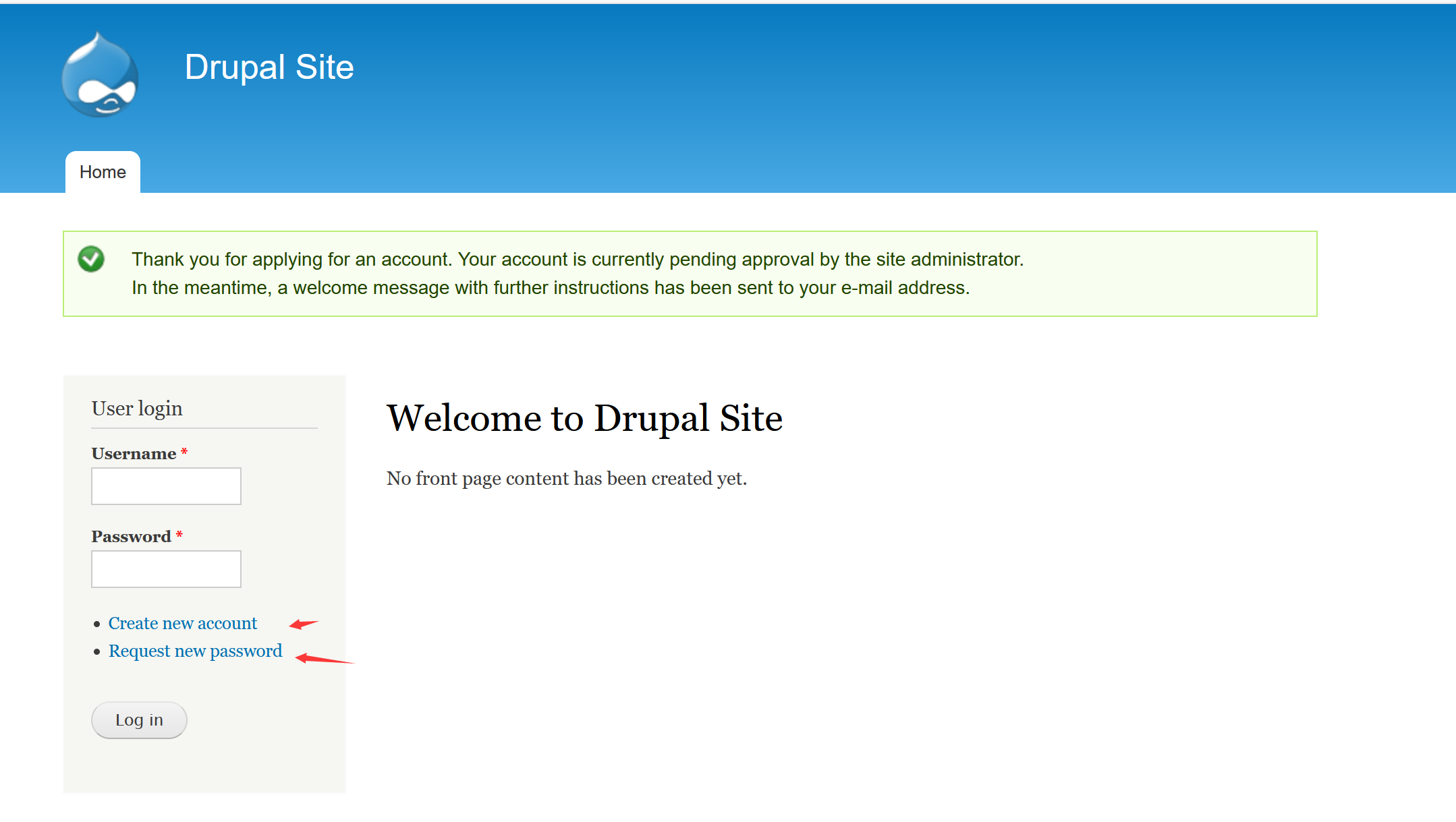
嘗試了註冊,登入的弱密碼,修改密碼,無效,但發現admin使用者存在
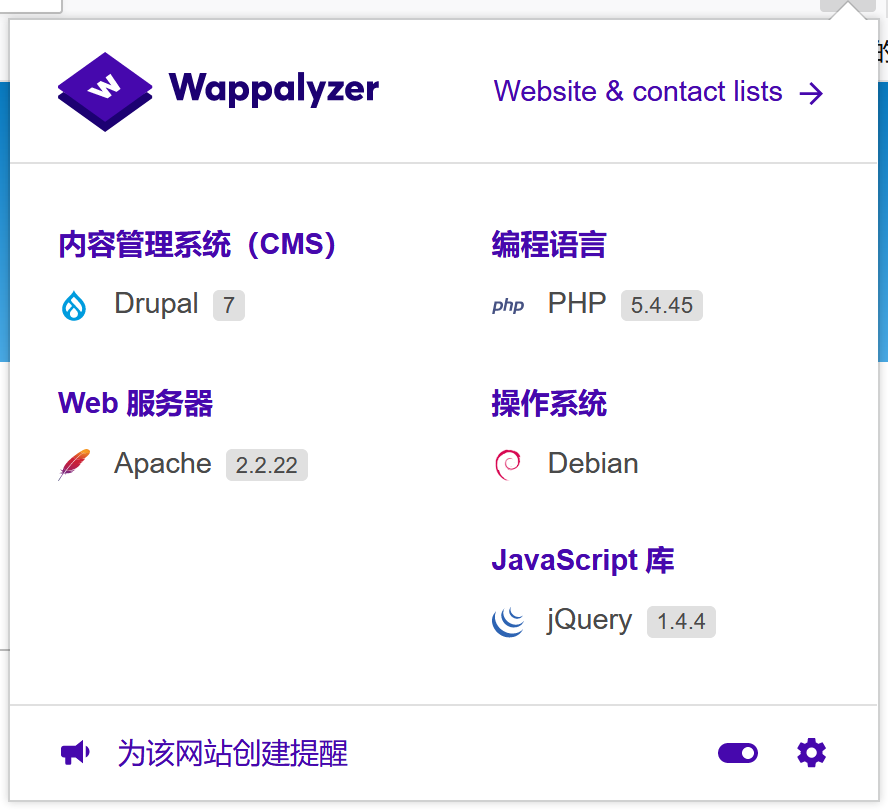
wappalyzer指紋識別,發現室Drupal系統
## 去漏洞庫和msf搜尋一下
```
msfconsole
search Drupal
```
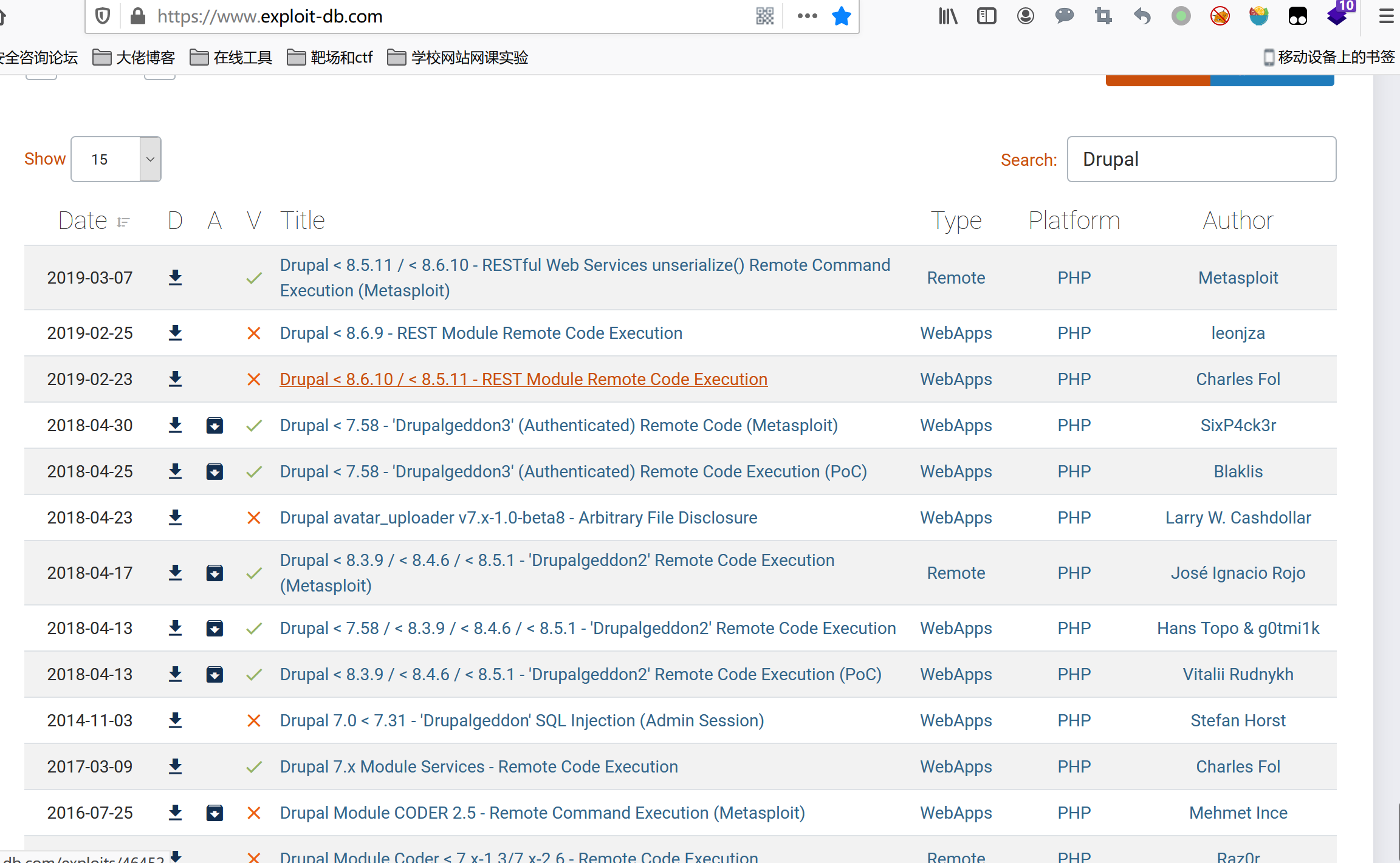
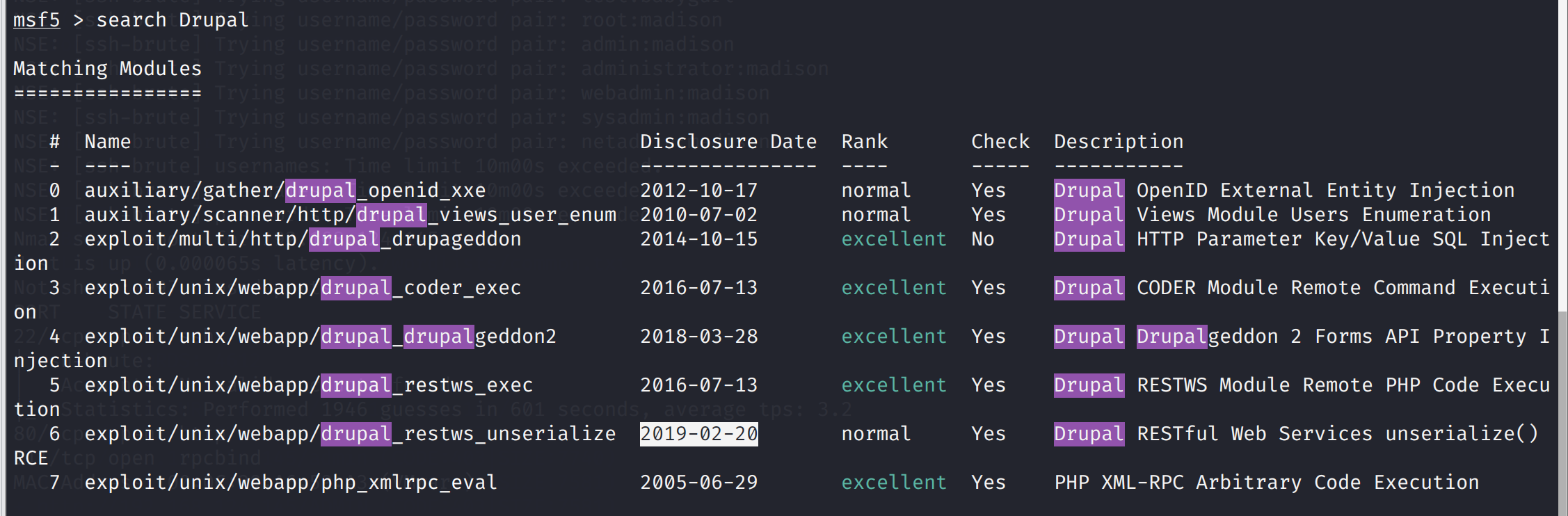
發現有漏洞可以用那就開始msf吧
使用2018年的漏洞吧,是個遠端程式碼執行(程式碼審計現在真心看不懂,
