DRF比Django的認證和許可權高在哪裡
阿新 • • 發佈:2020-12-20
Django可以用`LoginRequiredMixin`和`PermissionRequiredMixin`給類檢視新增認證和許可權,DRF做了高階封裝,提供了更簡潔的實現方式。我們通過繼續學習官網教程來進行了解。
# 更新model
首先修改`Snippet`模型,新增2個欄位:`owner`,儲存snippet建立者,`highlighted`,儲存高亮HTML。同時重寫`save`方法,在同步資料庫的時候,使用`pygments`包把`code`格式化後存到`highlighted`欄位。修改後的`snippets/models.py`完整程式碼如下:
```python
from django.db import models
from pygments.lexers import get_all_lexers
from pygments.styles import get_all_styles
from pygments.lexers import get_lexer_by_name
from pygments.formatters.html import HtmlFormatter
from pygments import highlight
LEXERS = [item for item in get_all_lexers() if item[1]]
LANGUAGE_CHOICES = sorted([(item[1][0], item[0]) for item in LEXERS])
STYLE_CHOICES = sorted([(item, item) for item in get_all_styles()])
class Snippet(models.Model):
created = models.DateTimeField(auto_now_add=True)
title = models.CharField(max_length=100, blank=True, default='')
code = models.TextField()
linenos = models.BooleanField(default=False)
language = models.CharField(choices=LANGUAGE_CHOICES, default='python', max_length=100)
style = models.CharField(choices=STYLE_CHOICES, default='friendly', max_length=100)
owner = models.ForeignKey('auth.User', related_name='snippets', on_delete=models.CASCADE)
highlighted = models.TextField()
class Meta:
ordering = ['created']
def save(self, *args, **kwargs):
"""
Use the `pygments` library to create a highlighted HTML
representation of the code snippet.
"""
lexer = get_lexer_by_name(self.language)
linenos = 'table' if self.linenos else False
options = {'title': self.title} if self.title else {}
formatter = HtmlFormatter(style=self.style, linenos=linenos,
full=True, **options)
self.highlighted = highlight(self.code, lexer, formatter)
super(Snippet, self).save(*args, **kwargs)
```
接著刪除資料庫和`migrations`,重新遷移資料庫:
```shell
rm -f db.sqlite3
rm -r snippets/migrations
python manage.py makemigrations snippets
python manage.py migrate
```
並建立超級管理員:
```shell
python manage.py createsuperuser
```
# User新增Endpoint
Endpoint,表示API的具體網址。我們按照`models.py`→`serializers.py`→`views.py`→`urls.py`的程式碼編寫順序,給User模型新增Endpoint。
**models.py**
直接使用Django預設User模型,不需要修改程式碼。
**serializers.py**
新增`UserSerializer`,由於User沒有`snippets`欄位,所以需要顯式新增:
```python
from django.contrib.auth.models import User
class UserSerializer(serializers.ModelSerializer):
snippets = serializers.PrimaryKeyRelatedField(many=True, queryset=Snippet.objects.all())
class Meta:
model = User
fields = ['id', 'username', 'snippets']
```
**views.py**
新增只讀的列表檢視`UserList`和詳情檢視`UserDetail`,分別用到了`ListAPIView`和`RetrieveAPIView`:
```python
from django.contrib.auth.models import User
from snippets.serializers import UserSerializer
class UserList(generics.ListAPIView):
queryset = User.objects.all()
serializer_class = UserSerializer
class UserDetail(generics.RetrieveAPIView):
queryset = User.objects.all()
serializer_class = UserSerializer
```
**urls.py**
新增訪問路徑:
```python
path('users/', views.UserList.as_view()),
path('users//', views.UserDetail.as_view()),
```
# 關聯User和Snippet
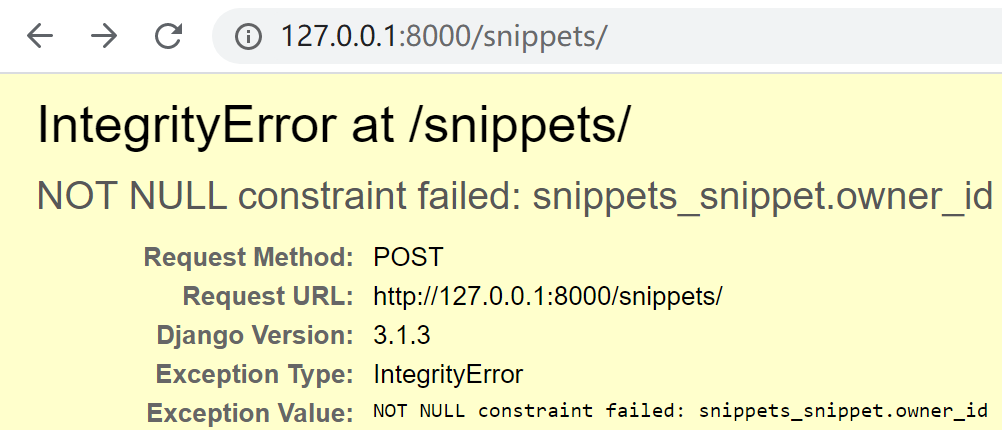
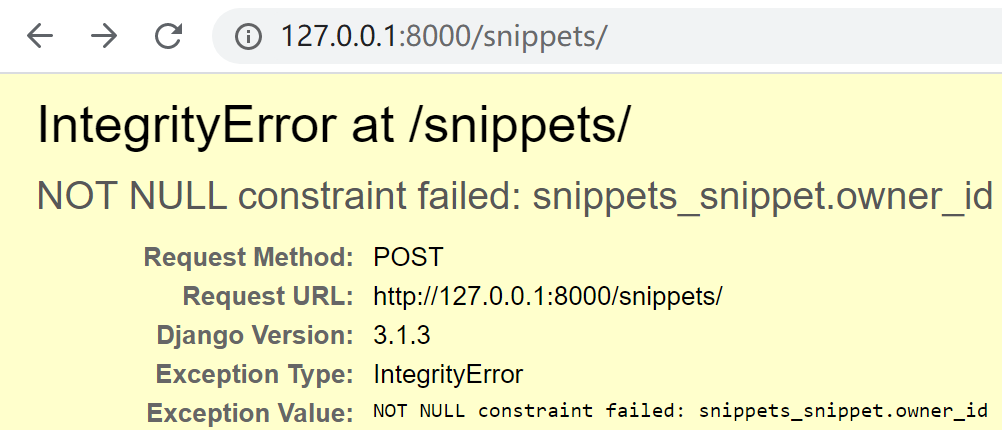
如果使用POST方法請求`http://127.0.0.1:8000/snippets/`,嘗試新增1條資料:
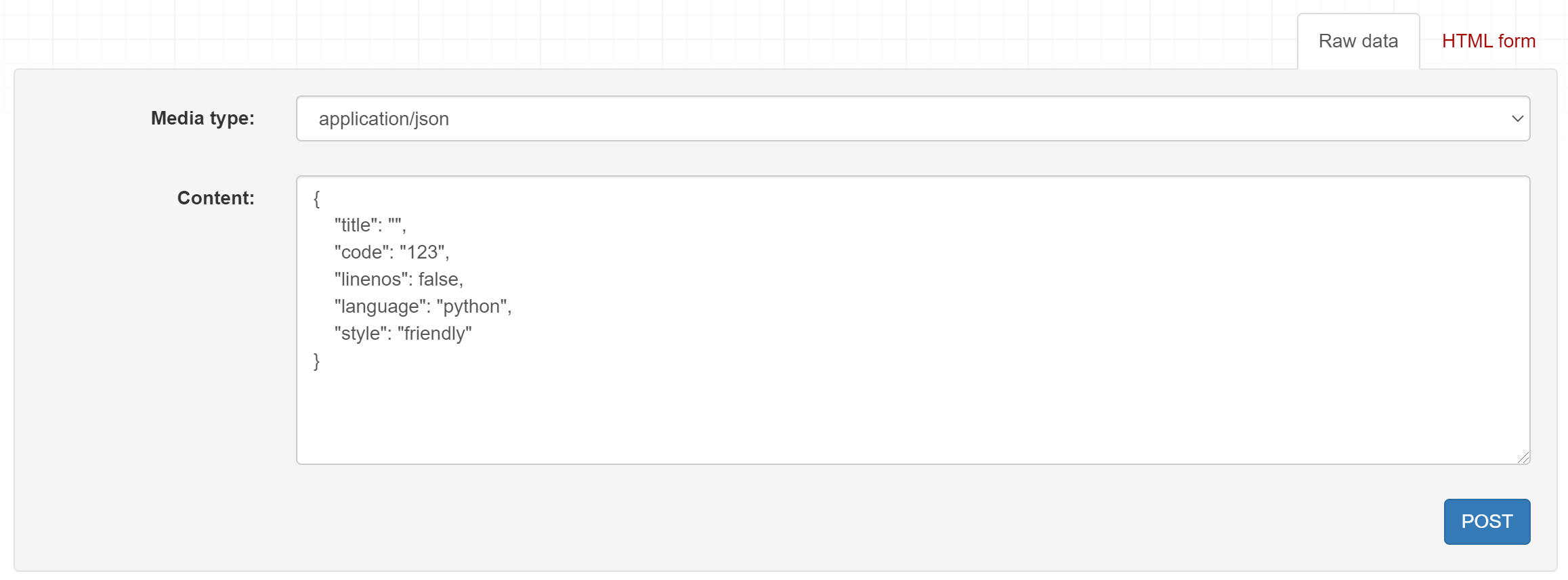
會發現介面報錯了: