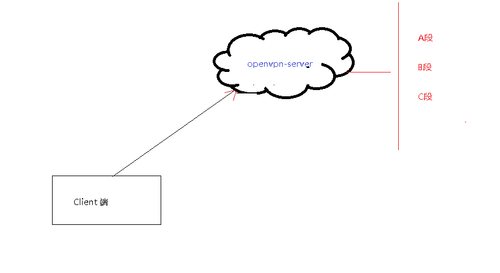
openvpn-server 搭建
1、需求vps 下搭建openvpn,並推送相關路由,此種vpn與商業化的SSL vpn幾乎等同無異。穩定性不相 上下,但沒有ssl 搭建維護方便
2、vpn 安裝在/usr/local/openvpn 目錄下、並做配置
tar xvzf openvpn-2.0.9.tar.gz
mkdir /usr/local/openvpn
cd openvpn
./configure --prefix=/usr/local/openvpn
make && make install
mkdir /etc/openvpn
[[email protected]]# cp -R easy-rsa/ /etc/openvpn/
[[email protected]]# cp sample-config-files/server.conf /etc/openvpn/
#進入配置目錄
[[email protected]]# cd /etc/openvpn/easy-rsa/2.0/
#編緝vars
export KEY_COUNTRY="CN"
export KEY_PROVINCE="BJ"
export KEY_CITY="Beijing"
export KEY_ORG="OpenVPN ORG"
export KEY_EMAIL="自己郵箱"
#查看在/keys/目錄下生成文件:
[[email protected]]# ls keys/
ca.crt ca.key index.txt serial
#生成服務器端證書
./build-key-server server 選項空格帶過即可
[[email protected]]# ls keys/
01.pem ca.key index.txt.attr serial server.crt server.key
ca.crt index.txt index.txt.old serial.old server.csr
#生成客戶端CA證書及密鑰
[[email protected]]# ./build-key client 選項空格帶過即可
#./build-dh 直接回車即可
[[email protected]]# ./build-dh
#啟動openvpn
/usr/sbin/openvpn --config /etc/openvpn/config/ client.conf >/dev/null 2>&1 &
#iptables規則
vim /etc/sysconfig/iptables
-A POSTROUTING -s 10.8.0.0/16 -o eth0 -j MASQUERADE
三、生成 server、client 端配置,已做精簡
[[email protected] ~]# cat /etc/openvpn/server.conf
#server端ip
local 你的ip
#端口
port 1194
#選擇tcp
proto tcp
#tunnel選項
dev tun
#證書目錄
cert /etc/openvpn/server.crt
key /etc/openvpn/server.key
dh /etc/openvpn/dh1024.pem
#IP
server 10.8.0.0 255.255.255.0
#路由推送,可以多條
push "route x.x.0.0 255.255.0.0"
#超時時間默認即可
keepalive 10 120
persist-key
persist-tun
#vpn log
status openvpn-status.log
log openvpn.log
verb 3
#client端配置
Windows Client 端的配置
client
dev tun
proto tcp
remote openvpn-server-ip地址
resolv-retry infinite
nobind
persist-key
persist-tun
ca ca.crt
cert client.crt
key client.key
ns-cert-type server
verb 3
#除此之外還有ldap認證方式,搭建環境太費時,此處不展示
本文出自 “keep” 博客,請務必保留此出處http://keep11.blog.51cto.com/1443840/1963281
openvpn-server 搭建
