基於httpd-2.4配置虛擬主機web站點,並提供https服務(二)
> 1.建立httpd服務,要求:
> 1) 提供兩個基於名稱的虛擬主機www1, www2;要求每個虛擬主機都有單獨的錯誤日誌和訪問日誌;
> 2) 通過www1的/server-status提供狀態信息,且僅允許172.16.0.1主機訪問;
> 3) www2不允許192.168.1.0/24網絡中任意主機訪問;
> 2.為上面的第2)個虛擬主機提供https服務。
>
基於httpd-2.4配置虛擬主機web站點,並提供https服務:
1.準備:(1)在VMwareWorkstation平臺下的CentOS7.2一枚;(2)真實機客戶端一個;
2.環境:(1)CentOS7.2系統中安裝httpd應用程序並啟動httpd服務;(2)關閉防火墻;(3)設置SELinux;
(1) [root@chenliang ~]# yum -y install httpd
[root@chenliang ~]# systemctl restart http.service
Active: active (running)
(2) [root@chenliang ~]# iptables -F
(3) [root@chenliang ~]# setenforce 0
3.操作步驟:
[root@chenliang ~]# cd /etc/httpd/conf.d
創建兩個基於主機名的web站點:
[root@chenliang conf.d]# vim www1.conf
<VirtualHost 172.16.72.1:80>
ServerName www1.cl7.com
DocumentRoot /var/www/www1
ErrorLog logs/www1-error_log
CustomLog logs/www1-access_log combined
<Location /server-status>
SetHandler server-status
Require all denied //httpd-2.4中統一使用Require來允許或阻止客戶端主機訪問,只要沒有明確的指明允許哪些客戶端主機訪問,則拒絕所有客戶端主機訪問;
Require ip 172.16.0.1
</Location>
</VirtualHost>
[root@chenliang conf.d]# vim www2.conf
<VirtualHost 172.16.72.1:80>
ServerName www2.cl7.com
DocumentRoot "/var/www/www2"
ErrorLog logs/www2-error_log
CustomLog logs/www2-access_log combiend
<Directory "/var/www/www2">
Options None
AllowOverride None
<RequireAll> //如果允許和拒絕等訪問控制要同時設置,則所有的Require指令必須要放置在<RequireAny>或者<RequireAll>容器指令中
Require not ip 192.168.1.0/24
Require all granted
</RequireAll>
</Directory>
</VirtualHost>
檢查創建的虛擬主機語法有沒有錯誤:
[root@chenliang conf.d]# httpd -t
AH00557: httpd: apr_sockaddr_info_get() failed for chenliang
AH00558: httpd: Could not reliably determine the server's fully qualified domain name, using 127.0.0.1. Set the 'ServerName' directive globally to suppress this message
Syntax OK
創建路徑映射目錄:
[root@chenliang conf]# mkdir -pv /var/www/www{1,2}
mkdir: 已創建目錄 "/var/www/www1"
mkdir: 已創建目錄 "/var/www/www2"
[root@chenliang conf]# echo "WWW1's page~~" > /var/www/www1/index.html
[root@chenliang conf]# echo "WWW2's page~~" > /var/www/www2/index.html
添加域名解析:
[root@chenliang conf.d]# echo "172.16.72.1 www1.cl.com www2.cl.com" >> /etc/hosts
重啟httpd服務:
[root@chenliang conf.d]# systemctl restart httpd.service
在真實機端打開系統盤:C:\Windows\System32\drivers\etc\hosts,使用文本編輯器編輯添加並保存添加內容:172.16.72.1 www1.cl7.com www2.cl7.com
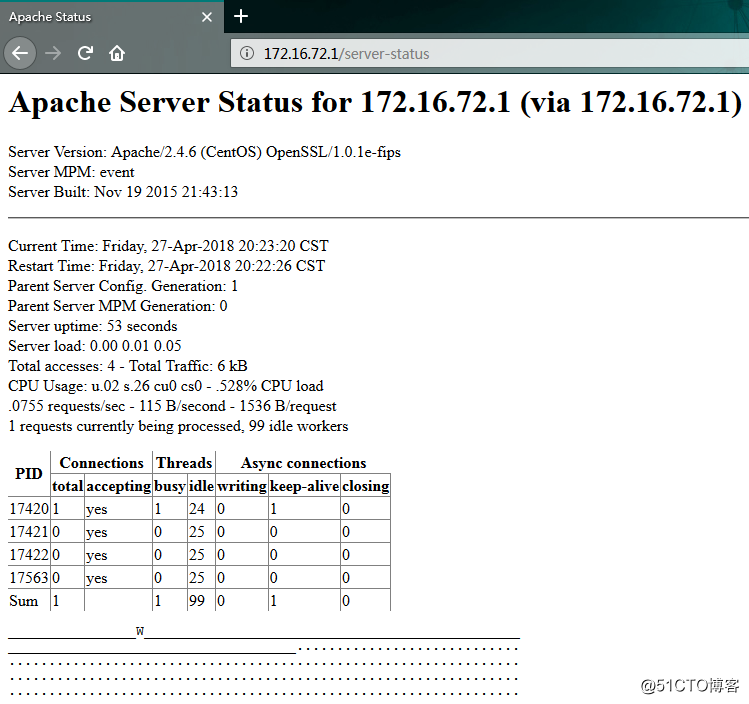
使用客戶端測試結果如下:
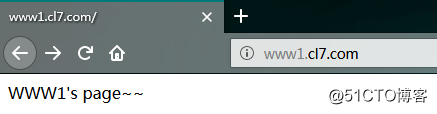
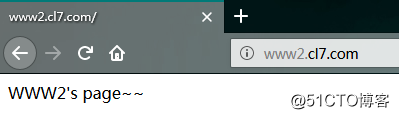
測試www1是否能允許172.16.0.1網段內的主機查看服務器屬性:
4.為虛擬主機www2提供https服務:
(1) 創建私有CA:
1)生成私鑰:
[root@chenliang ~]# cd /etc/pki/CA
[root@chenliang CA]# ls
certs crl newcerts private
[root@chenliang CA]# (umask 077; openssl genrsa -out private/cakey.pem 4096)
Generating RSA private key, 4096 bit long modulus
............................................................................................................................................................++
.....................................................................................................................................................................................................................................................++
e is 65537 (0x10001)
2)生成自簽證書:
[root@chenliang CA]# openssl req -new -x509 -key private/cakey.pem -out cacert.pem
You are about to be asked to enter information that will be incorporated
into your certificate request.
What you are about to enter is what is called a Distinguished Name or a DN.
There are quite a few fields but you can leave some blank
For some fields there will be a default value,
If you enter '.', the field will be left blank.
-----
Country Name (2 letter code) [XX]:CN
State or Province Name (full name) []:Hebei
Locality Name (eg, city) [Default City]:Handan
Organization Name (eg, company) [Default Company Ltd]:chenliang
Organizational Unit Name (eg, section) []:chenliang
Common Name (eg, your name or your server's hostname) []:chenliang
Email Address []:
[root@chenliang CA]# ls
cacert.pem certs crl newcerts private
3)將文本文件和目錄添加完成私有CA配置:
[root@chenliang CA]# touch index.txt
[root@chenliang CA]# echo 01 > serial
(2)創建https站點:{前提要安裝httpd模塊列表中的mod_ssl模塊}
1)生成私鑰並生成證書請求:
[root@chenliang ~]# mkdir -pv /etc/httpd/ssl
mkdir: 已創建目錄 "/etc/httpd/ssl"
[root@chenliang ~]# cd /etc/httpd/ssl
[root@chenliang ssl]# ls
[root@chenliang ssl]# (umask 077;openssl genrsa -out httpd.key 4096)
Generating RSA private key, 4096 bit long modulus
...............................++
......................++
e is 65537 (0x10001)
[root@chenliang ssl]# openssl req -new -key httpd.key -out httpd.csr
You are about to be asked to enter information that will be incorporated
into your certificate request.
What you are about to enter is what is called a Distinguished Name or a DN.
There are quite a few fields but you can leave some blank
For some fields there will be a default value,
If you enter '.', the field will be left blank.
-----
Country Name (2 letter code) [XX]:CN
State or Province Name (full name) []:Hebei
Locality Name (eg, city) [Default City]:Handan
Organization Name (eg, company) [Default Company Ltd]:chenliang
Organizational Unit Name (eg, section) []:chenliang
Common Name (eg, your name or your server's hostname) []:chenliang
Email Address []:
Please enter the following 'extra' attributes
to be sent with your certificate request
A challenge password []:123456
An optional company name []:CL
[root@chenliang ssl]# ls
httpd.csr httpd.key
2)將證書請求發送到CA:
[root@chenliang ssl]# cp httpd.csr /tmp/
3)在CA上為此次請求簽發證書:
[root@chenliang ssl]# openssl ca -in /tmp/httpd.csr -out /etc/pki/CA/certs/httpd.crt
Using configuration from /etc/pki/tls/openssl.cnf
Check that the request matches the signature
Signature ok
Certificate Details:
Serial Number: 1 (0x1)
Validity
Not Before: Apr 27 12:51:29 2018 GMT
Not After : Apr 27 12:51:29 2019 GMT
Subject:
countryName = CN
stateOrProvinceName = Hebei
organizationName = chenliang
organizationalUnitName = chenliang
commonName = chenliang
X509v3 extensions:
X509v3 Basic Constraints:
CA:FALSE
Netscape Comment:
OpenSSL Generated Certificate
X509v3 Subject Key Identifier:
92:A4:5B:5C:88:0D:CE:84:67:5F:2A:9B:1F:57:15:AD:12:A9:13:CE
X509v3 Authority Key Identifier:
keyid:B6:C0:56:B6:E7:CF:C6:9B:CB:35:6D:1F:C9:06:94:69:D2:D9:23:68
Certificate is to be certified until Apr 27 12:51:29 2019 GMT (365 days)
Sign the certificate? [y/n]:y
1 out of 1 certificate requests certified, commit? [y/n]y
Write out database with 1 new entries
Data Base Updated
4)在CA上將CA簽發的證書傳送到httpd服務器:
[root@chenliang ssl]# scp /etc/pki/CA/certs/httpd.crt /etc/httpd/ssl/
5)在httpd服務器上,刪除證書請求文件:
[root@chenliang ssl]# ls
httpd.crt httpd.csr httpd.key
[root@chenliang ssl]# rm -fr httpd.csr
[root@chenliang ssl]# ls
httpd.crt httpd.key
6)在httpd服務器上配置ssl支持:(需要安裝httpd中的mod_ssl模塊,沒有安裝需要提前安裝)
配置https的虛擬主機:
[root@chenliang ~]# vim /etc/httpd/conf.d/ssl.conf
<VirtualHost>
DocumentRoot "/data/vhosts/www2"
ServerName www2.magedu.com:443
SSLCertificateFile /etc/httpd/ssl/httpd.crt
SSLCertificateKeyFile /etc/httpd/ssl/httpd.key
</VirtualHost>
5.測試https是否配置成功:

至此,httpd-2.4基於主機名建立虛擬主機並實現web站點的https服務完成
基於httpd-2.4配置虛擬主機web站點,並提供https服務(二)
