SpringBoot整合mybatis、shiro、redis實現基於資料庫的細粒度動態許可權管理系統例項
1.前言
本文主要介紹使用SpringBoot與shiro實現基於資料庫的細粒度動態許可權管理系統例項。
使用技術:SpringBoot、mybatis、shiro、thymeleaf、pagehelper、Mapper外掛、druid、dataTables、ztree、jQuery
開發工具:intellij idea
資料庫:mysql、redis
基本上是基於使用SpringSecurity的demo上修改而成,地址 http://blog.csdn.net/poorcoder_/article/details/70231779
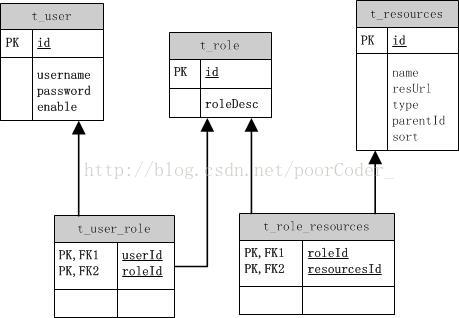
2.表結構
還是是用標準的5張表來展現許可權。如下圖:
分別為使用者表,角色表,資源表,使用者角色表,角色資源表。在這個demo中使用了mybatis-generator自動生成程式碼。執行mybatis-generator:generate -e 根據資料庫中的表,生成 相應的model,mapper單表的增刪改查。不過如果是匯入本專案的就別執行這個命令了。新增表的話,也要修改mybatis-generator-config.xml中的tableName,指定表名再執行。
3.maven配置
<?xml version="1.0" encoding="UTF-8"?>
<project xmlns="http://maven.apache.org/POM/4.0.0" 4.配置Druid
package com.study.config;
import com.alibaba.druid.support.http.StatViewServlet;
import com.alibaba.druid.support.http.WebStatFilter;
import org.springframework.boot.web.servlet.FilterRegistrationBean;
import org.springframework.boot.web.servlet.ServletRegistrationBean;
import org.springframework.context.annotation.Bean;
import org.springframework.context.annotation.Configuration;
/**
* Created by yangqj on 2017/4/19.
*/
@Configuration
public class DruidConfig {
@Bean
public ServletRegistrationBean druidServlet() {
ServletRegistrationBean servletRegistrationBean = new ServletRegistrationBean(new StatViewServlet(), "/druid/*");
//登入檢視資訊的賬號密碼.
servletRegistrationBean.addInitParameter("loginUsername","admin");
servletRegistrationBean.addInitParameter("loginPassword","123456");
return servletRegistrationBean;
}
@Bean
public FilterRegistrationBean filterRegistrationBean() {
FilterRegistrationBean filterRegistrationBean = new FilterRegistrationBean();
filterRegistrationBean.setFilter(new WebStatFilter());
filterRegistrationBean.addUrlPatterns("/*");
filterRegistrationBean.addInitParameter("exclusions", "*.js,*.gif,*.jpg,*.png,*.css,*.ico,/druid/*");
return filterRegistrationBean;
}
}
在application.properties中加入:
# 資料來源基礎配置
spring.datasource.type=com.alibaba.druid.pool.DruidDataSource
spring.datasource.driver-class-name=com.mysql.jdbc.Driver
spring.datasource.url=jdbc:mysql://localhost:3306/shiro
spring.datasource.username=root
spring.datasource.password=root
# 連線池配置
# 初始化大小,最小,最大
spring.datasource.initialSize=1
spring.datasource.minIdle=1
spring.datasource.maxActive=205.配置mybatis
使用springboot 整合mybatis非常方便,只需在application.properties
mybatis.type-aliases-package=com.study.model
mybatis.mapper-locations=classpath:mapper/*.xml
mapper.mappers=com.study.util.MyMapper
mapper.not-empty=false
mapper.identity=MYSQL
pagehelper.helperDialect=mysql
pagehelper.reasonable=true
pagehelper.supportMethodsArguments=true
pagehelper.params=count\=countSql將相應的路徑改成專案包所在的路徑即可。配置檔案中可以看出來還加入了pagehelper 和Mapper外掛。如果不需要,把上面配置檔案中的 pagehelper刪除。
MyMapper:
package com.study.util;
/**
* Created by yangqj on 2017/4/20.
*/
import tk.mybatis.mapper.common.Mapper;
import tk.mybatis.mapper.common.MySqlMapper;
public interface MyMapper<T> extends Mapper<T>, MySqlMapper<T> {
}
6.thymeleaf配置
thymeleaf是springboot官方推薦的,所以來試一下。
首先加入配置:
#spring.thymeleaf.prefix=classpath:/templates/
#spring.thymeleaf.suffix=.html
#spring.thymeleaf.mode=HTML5
#spring.thymeleaf.encoding=UTF-8
# ;charset=<encoding> is added
#spring.thymeleaf.content-type=text/html
# set to false for hot refresh
spring.thymeleaf.cache=false
spring.thymeleaf.mode=LEGACYHTML5
可以看到其實上面都是註釋了的,因為springboot會根據約定俗成的方式幫我們配置好。所以上面註釋部分是springboot自動配置的,如果需要自定義配置,只需要修改上註釋部分即可。
後兩行沒有註釋的部分,spring.thymeleaf.cache=false表示關閉快取,這樣修改檔案後不需要重新啟動,快取預設是開啟的,所以指定為false。但是在intellij idea中還需要按Ctrl + Shift + F9.
對於spring.thymeleaf.mode=LEGACYHTML5。thymeleaf對html中的語法要求非常嚴格,像我從網上找的模板,使用thymeleaf後報一堆的語法錯誤,後來沒辦法,使用弱語法校驗,所以加入配置spring.thymeleaf.mode=LEGACYHTML5。加入這個配置後還需要在maven中加入
<dependency>
<groupId>net.sourceforge.nekohtml</groupId>
<artifactId>nekohtml</artifactId>
<version>1.9.22</version>
</dependency>否則會報錯的。
在前端頁面的頭部加入一下配置後,就可以使用thymeleaf了
<link rel="stylesheet" th:href="@{/css/bootstrap.min.css}" />不過這個專案因為使用了datatables都是使用jquery 的ajax來訪問資料與處理資料,所以用到的thymeleaf語法非常少,基本上可以參考的就是js即css的匯入和類似於jsp的include功能的部分頁面引入。
對於靜態檔案的引入:
<link rel="stylesheet" th:href="@{/css/bootstrap.min.css}" />而檔案在專案中的位置是static-css-bootstrap.min.css。為什麼這樣可以訪問到該檔案,也是因為springboot對於靜態檔案會自動查詢/static public、/resources、/META-INF/resources下的檔案。所以不需要加static.
頁面引入:
區域性頁面如下:
<div th:fragment="top">
...
</div>主體頁面映入方式:
<div th:include="common/top :: top"></div>inclide=”檔案路徑::區域性程式碼片段名稱”
7.shiro配置
配置檔案ShiroConfig
package com.study.config;
import at.pollux.thymeleaf.shiro.dialect.ShiroDialect;
import com.github.pagehelper.util.StringUtil;
import com.study.model.Resources;
import com.study.service.ResourcesService;
import com.study.shiro.MyShiroRealm;
import org.apache.shiro.authc.credential.HashedCredentialsMatcher;
import org.apache.shiro.mgt.SecurityManager;
import org.apache.shiro.spring.LifecycleBeanPostProcessor;
import org.apache.shiro.spring.security.interceptor.AuthorizationAttributeSourceAdvisor;
import org.apache.shiro.spring.web.ShiroFilterFactoryBean;
import org.apache.shiro.web.mgt.DefaultWebSecurityManager;
import org.apache.shiro.web.session.mgt.DefaultWebSessionManager;
import org.crazycake.shiro.RedisCacheManager;
import org.crazycake.shiro.RedisManager;
import org.crazycake.shiro.RedisSessionDAO;
import org.springframework.beans.factory.annotation.Autowired;
import org.springframework.beans.factory.annotation.Value;
import org.springframework.context.annotation.Bean;
import org.springframework.context.annotation.Configuration;
import java.util.LinkedHashMap;
import java.util.List;
import java.util.Map;
/**
* Created by yangqj on 2017/4/23.
*/
@Configuration
public class ShiroConfig {
@Autowired(required = false)
private ResourcesService resourcesService;
@Value("${spring.redis.host}")
private String host;
@Value("${spring.redis.port}")
private int port;
@Value("${spring.redis.timeout}")
private int timeout;
@Bean
public static LifecycleBeanPostProcessor getLifecycleBeanPostProcessor() {
return new LifecycleBeanPostProcessor();
}
/**
* ShiroDialect,為了在thymeleaf裡使用shiro的標籤的bean
* @return
*/
@Bean
public ShiroDialect shiroDialect() {
return new ShiroDialect();
}
/**
* ShiroFilterFactoryBean 處理攔截資原始檔問題。
* 注意:單獨一個ShiroFilterFactoryBean配置是或報錯的,因為在
* 初始化ShiroFilterFactoryBean的時候需要注入:SecurityManager
*
Filter Chain定義說明
1、一個URL可以配置多個Filter,使用逗號分隔
2、當設定多個過濾器時,全部驗證通過,才視為通過
3、部分過濾器可指定引數,如perms,roles
*
*/
@Bean
public ShiroFilterFactoryBean shirFilter(SecurityManager securityManager){
System.out.println("ShiroConfiguration.shirFilter()");
ShiroFilterFactoryBean shiroFilterFactoryBean = new ShiroFilterFactoryBean();
// 必須設定 SecurityManager
shiroFilterFactoryBean.setSecurityManager(securityManager);
// 如果不設定預設會自動尋找Web工程根目錄下的"/login.jsp"頁面
shiroFilterFactoryBean.setLoginUrl("/login");
// 登入成功後要跳轉的連結
shiroFilterFactoryBean.setSuccessUrl("/usersPage");
//未授權介面;
shiroFilterFactoryBean.setUnauthorizedUrl("/403");
//攔截器.
Map<String,String> filterChainDefinitionMap = new LinkedHashMap<String,String>();
//配置退出 過濾器,其中的具體的退出程式碼Shiro已經替我們實現了
filterChainDefinitionMap.put("/logout", "logout");
filterChainDefinitionMap.put("/css/**","anon");
filterChainDefinitionMap.put("/js/**","anon");
filterChainDefinitionMap.put("/img/**","anon");
filterChainDefinitionMap.put("/font-awesome/**","anon");
//<!-- 過濾鏈定義,從上向下順序執行,一般將 /**放在最為下邊 -->:這是一個坑呢,一不小心程式碼就不好使了;
//<!-- authc:所有url都必須認證通過才可以訪問; anon:所有url都都可以匿名訪問-->
//自定義載入許可權資源關係
List<Resources> resourcesList = resourcesService.queryAll();
for(Resources resources:resourcesList){
if (StringUtil.isNotEmpty(resources.getResurl())) {
String permission = "perms[" + resources.getResurl()+ "]";
filterChainDefinitionMap.put(resources.getResurl(),permission);
}
}
filterChainDefinitionMap.put("/**", "authc");
shiroFilterFactoryBean.setFilterChainDefinitionMap(filterChainDefinitionMap);
return shiroFilterFactoryBean;
}
@Bean
public SecurityManager securityManager(){
DefaultWebSecurityManager securityManager = new DefaultWebSecurityManager();
//設定realm.
securityManager.setRealm(myShiroRealm());
// 自定義快取實現 使用redis
//securityManager.setCacheManager(cacheManager());
// 自定義session管理 使用redis
securityManager.setSessionManager(sessionManager());
return securityManager;
}
@Bean
public MyShiroRealm myShiroRealm(){
MyShiroRealm myShiroRealm = new MyShiroRealm();
myShiroRealm.setCredentialsMatcher(hashedCredentialsMatcher());
return myShiroRealm;
}
/**
* 憑證匹配器
* (由於我們的密碼校驗交給Shiro的SimpleAuthenticationInfo進行處理了
* 所以我們需要修改下doGetAuthenticationInfo中的程式碼;
* )
* @return
*/
@Bean
public HashedCredentialsMatcher hashedCredentialsMatcher(){
HashedCredentialsMatcher hashedCredentialsMatcher = new HashedCredentialsMatcher();
hashedCredentialsMatcher.setHashAlgorithmName("md5");//雜湊演算法:這裡使用MD5演算法;
hashedCredentialsMatcher.setHashIterations(2);//雜湊的次數,比如雜湊兩次,相當於 md5(md5(""));
return hashedCredentialsMatcher;
}
/**
* 開啟shiro aop註解支援.
* 使用代理方式;所以需要開啟程式碼支援;
* @param securityManager
* @return
*/
@Bean
public AuthorizationAttributeSourceAdvisor authorizationAttributeSourceAdvisor(SecurityManager securityManager){
AuthorizationAttributeSourceAdvisor authorizationAttributeSourceAdvisor = new AuthorizationAttributeSourceAdvisor();
authorizationAttributeSourceAdvisor.setSecurityManager(securityManager);
return authorizationAttributeSourceAdvisor;
}
/**
* 配置shiro redisManager
* 使用的是shiro-redis開源外掛
* @return
*/
public RedisManager redisManager() {
RedisManager redisManager = new RedisManager();
redisManager.setHost(host);
redisManager.setPort(port);
redisManager.setExpire(1800);// 配置快取過期時間
redisManager.setTimeout(timeout);
// redisManager.setPassword(password);
return redisManager;
}
/**
* cacheManager 快取 redis實現
* 使用的是shiro-redis開源外掛
* @return
*/
public RedisCacheManager cacheManager() {
RedisCacheManager redisCacheManager = new RedisCacheManager();
redisCacheManager.setRedisManager(redisManager());
return redisCacheManager;
}
/**
* RedisSessionDAO shiro sessionDao層的實現 通過redis
* 使用的是shiro-redis開源外掛
*/
@Bean
public RedisSessionDAO redisSessionDAO() {
RedisSessionDAO redisSessionDAO = new RedisSessionDAO();
redisSessionDAO.setRedisManager(redisManager());
return redisSessionDAO;
}
/**
* shiro session的管理
*/
@Bean
public DefaultWebSessionManager sessionManager() {
DefaultWebSessionManager sessionManager = new DefaultWebSessionManager();
sessionManager.setSessionDAO(redisSessionDAO());
return sessionManager;
}
}
配置自定義Realm
package com.study.shiro;
import com.study.model.Resources;
import com.study.model.User;
import com.study.service.ResourcesService;
import com.study.service.UserService;
import org.apache.shiro.SecurityUtils;
import org.apache.shiro.authc.*;
import org.apache.shiro.authz.AuthorizationInfo;
import org.apache.shiro.authz.SimpleAuthorizationInfo;
import org.apache.shiro.realm.AuthorizingRealm;
import org.apache.shiro.session.Session;
import org.apache.shiro.subject.PrincipalCollection;
import org.apache.shiro.util.ByteSource;
import javax.annotation.Resource;
import java.util.HashMap;
import java.util.List;
import java.util.Map;
/**
* Created by yangqj on 2017/4/21.
*/
public class MyShiroRealm extends AuthorizingRealm {
@Resource
private UserService userService;
@Resource
private ResourcesService resourcesService;
//授權
@Override
protected AuthorizationInfo doGetAuthorizationInfo(PrincipalCollection principalCollection) {
User user= (User) SecurityUtils.getSubject().getPrincipal();//User{id=1, username='admin', password='3ef7164d1f6167cb9f2658c07d3c2f0a', enable=1}
Map<String,Object> map = new HashMap<String,Object>();
map.put("userid",user.getId());
List<Resources> resourcesList = resourcesService.loadUserResources(map);
// 許可權資訊物件info,用來存放查出的使用者的所有的角色(role)及許可權(permission)
SimpleAuthorizationInfo info = new SimpleAuthorizationInfo();
for(Resources resources: resourcesList){
info.addStringPermission(resources.getResurl());
}
return info;
}
//認證
@Override
protected AuthenticationInfo doGetAuthenticationInfo(AuthenticationToken token) throws AuthenticationException {
//獲取使用者的輸入的賬號.
String username = (String)token.getPrincipal();
User user = userService.selectByUsername(username);
if(user==null) throw new UnknownAccountException();
if (0==user.getEnable()) {
throw new LockedAccountException(); // 帳號鎖定
}
SimpleAuthenticationInfo authenticationInfo = new SimpleAuthenticationInfo(
user, //使用者
user.getPassword(), //密碼
ByteSource.Util.bytes(username),
getName() //realm name
);
// 當驗證都通過後,把使用者資訊放在session裡
Session session = SecurityUtils.getSubject().getSession();
session.setAttribute("userSession", user);
session.setAttribute("userSessionId", user.getId());
return authenticationInfo;
}
}
認證:
shiro的主要模組分別就是授權和認證和會話管理。
我們先講認證。認證就是驗證使用者。比如使用者登入的時候驗證賬號密碼是否正確。
我們可以把對登入的驗證交給shiro。我們執行要查詢相應的使用者資訊,並傳給shiro。如下程式碼則為使用者登入:
@RequestMapping(value="/login",method=RequestMethod.POST)
public String login(HttpServletRequest request, User user, Model model){
if (StringUtils.isEmpty(user.getUsername()) || StringUtils.isEmpty(user.getPassword())) {
request.setAttribute("msg", "使用者名稱或密碼不能為空!");
return "login";
}
Subject subject = SecurityUtils.getSubject();
UsernamePasswordToken token=new UsernamePasswordToken(user.getUsername(),user.getPassword());
try {
subject.login(token);
return "redirect:usersPage";
}catch (LockedAccountException lae) {
token.clear();
request.setAttribute("msg", "使用者已經被鎖定不能登入,請與管理員聯絡!");
return "login";
} catch (AuthenticationException e) {
token.clear();
request.setAttribute("msg", "使用者或密碼不正確!");
return "login";
}
}可見使用者登陸的程式碼主要就是 subject.login(token);呼叫後就會進去我們自定義的realm中的doGetAuthenticationInfo()方法。
//認證
@Override
protected AuthenticationInfo doGetAuthenticationInfo(AuthenticationToken token) throws AuthenticationException {
//獲取使用者的輸入的賬號.
String username = (String)token.getPrincipal();
User user = userService.selectByUsername(username);
if(user==null) throw new UnknownAccountException();
if (0==user.getEnable()) {
throw new LockedAccountException(); // 帳號鎖定
}
SimpleAuthenticationInfo authenticationInfo = new SimpleAuthenticationInfo(
user, //使用者
user.getPassword(), //密碼
ByteSource.Util.bytes(username),
getName() //realm name
);
// 當驗證都通過後,把使用者資訊放在session裡
Session session = SecurityUtils.getSubject().getSession();
session.setAttribute("userSession", user);
session.setAttribute("userSessionId", user.getId());
return authenticationInfo;
}而我們在ShiroConfig中配置了憑證匹配器:
@Bean
public MyShiroRealm myShiroRealm(){
MyShiroRealm myShiroRealm = new MyShiroRealm();
myShiroRealm.setCredentialsMatcher(hashedCredentialsMatcher());
return myShiroRealm;
}
@Bean
public HashedCredentialsMatcher hashedCredentialsMatcher(){
HashedCredentialsMatcher hashedCredentialsMatcher = new HashedCredentialsMatcher();
hashedCredentialsMatcher.setHashAlgorithmName("md5");//雜湊演算法:這裡使用MD5演算法;
hashedCredentialsMatcher.setHashIterations(2);//雜湊的次數,比如雜湊兩次,相當於 md5(md5(""));
return hashedCredentialsMatcher;
}所以在認證時的密碼是加過密的,使用md5散發將密碼與鹽值組合加密兩次。則我們在增加使用者的時候,對使用者的密碼則要進過相同規則的加密才行。
新增使用者程式碼如下:
@RequestMapping(value = "/add")
public String add(User user) {
User u = userService.selectByUsername(user.getUsername());
if(u != null)
return "error";
try {
user.setEnable(1);
PasswordHelper passwordHelper = new PasswordHelper();
passwordHelper.encryptPassword(user);
userService.save(user);
return "success";
} catch (Exception e) {
e.printStackTrace();
return "fail";
}
}PasswordHelper:
package com.study.util;
import com.study.model.User;
import org.apache.shiro.crypto.RandomNumberGenerator;
import org.apache.shiro.crypto.SecureRandomNumberGenerator;
import org.apache.shiro.crypto.hash.SimpleHash;
import org.apache.shiro.util.ByteSource;
public class PasswordHelper {
//private RandomNumberGenerator randomNumberGenerator = new SecureRandomNumberGenerator();
private String algorithmName = "md5";
private int hashIterations = 2;
public void encryptPassword(User user) {
//String salt=randomNumberGenerator.nextBytes().toHex();
String newPassword = new SimpleHash(algorithmName, user.getPassword(), ByteSource.Util.bytes(user.getUsername()), hashIterations).toHex();
//String newPassword = new SimpleHash(algorithmName, user.getPassword()).toHex();
user.setPassword(newPassword);
}
public static void main(String[] args) {
PasswordHelper passwordHelper = new PasswordHelper();
User user = new User();
user.setUsername("admin");
user.setPassword("admin");
passwordHelper.encryptPassword(user);
System.out.println(user);
}
}
授權:
接下來講下授權。在自定義relalm中的程式碼為:
//授權
@Override
protected AuthorizationInfo doGetAuthorizationInfo(PrincipalCollection principalCollection) {
User user= (User) SecurityUtils.getSubject().getPrincipal();//User{id=1, username='admin', password='3ef7164d1f6167cb9f2658c07d3c2f0a', enable=1}
Map<String,Object> map = new HashMap<String,Object>();
map.put("userid",user.getId());
List<Resources> resourcesList = resourcesService.loadUserResources(map);
// 許可權資訊物件info,用來存放查出的使用者的所有的角色(role)及許可權(permission)
SimpleAuthorizationInfo info = new SimpleAuthorizationInfo();
for(Resources resources: resourcesList){
info.addStringPermission(resources.getResurl());
}
return info;
}從以上程式碼中可以看出來,我根據使用者id查詢出使用者的許可權,放入SimpleAuthorizationInfo。關聯表user_role,role_resources,resources,三張表,根據使用者所擁有的角色,角色所擁有的許可權,查詢出分配給該使用者的所有許可權的url。當訪問的連結中配置在shiro中時,或者使用shiro標籤,shiro許可權註解時,則會訪問該方法,判斷該使用者是否擁有相應的許可權。
在ShiroConfig中有如下程式碼:
@Bean
public ShiroFilterFactoryBean shirFilter(SecurityManager securityManager){
System.out.println("ShiroConfiguration.shirFilter()");
ShiroFilterFactoryBean shiroFilterFactoryBean = new ShiroFilterFactoryBean();
// 必須設定 SecurityManager
shiroFilterFactoryBean.setSecurityManager(securityManager);
// 如果不設定預設會自動尋找Web工程根目錄下的"/login.jsp"頁面
shiroFilterFactoryBean.setLoginUrl("/login");
// 登入成功後要跳轉的連結
shiroFilterFactoryBean.setSuccessUrl("/usersPage");
//未授權介面;
shiroFilterFactoryBean.setUnauthorizedUrl("/403");
//攔截器.
Map<String,String> filterChainDefinitionMap = new LinkedHashMap<String,String>();
//配置退出 過濾器,其中的具體的退出程式碼Shiro已經替我們實現了
filterChainDefinitionMap.put("/logout", "logout");
filterChainDefinitionMap.put("/css/**","anon");
filterChainDefinitionMap.put("/js/**","anon");
filterChainDefinitionMap.put("/img/**","anon");
filterChainDefinitionMap.put("/font-awesome/**","anon");
//<!-- 過濾鏈定義,從上向下順序執行,一般將 /**放在最為下邊 -->:這是一個坑呢,一不小心程式碼就不好使了;
//<!-- authc:所有url都必須認證通過才可以訪問; anon:所有url都都可以匿名訪問-->
//自定義載入許可權資源關係
List<Resources> resourcesList = resourcesService.queryAll();
for(Resources resources:resourcesList){
if (StringUtil.isNotEmpty(resources.getResurl())) {
String permission = "perms[" + resources.getResurl()+ "]";
filterChainDefinitionMap.put(resources.getResurl(),permission);
}
}
filterChainDefinitionMap.put("/**", "authc");
shiroFilterFactoryBean.setFilterChainDefinitionMap(filterChainDefinitionMap);
return shiroFilterFactoryBean;
}
該程式碼片段為配置shiro的過濾器。以上程式碼將靜態檔案設定為任何許可權都可訪問,然後
List<Resources> resourcesList = resourcesService.queryAll();
for(Resources resources:resou