Apache下配置https雙向認證
阿新 • • 發佈:2019-01-24
1.Apache安裝並開啟ssl
略
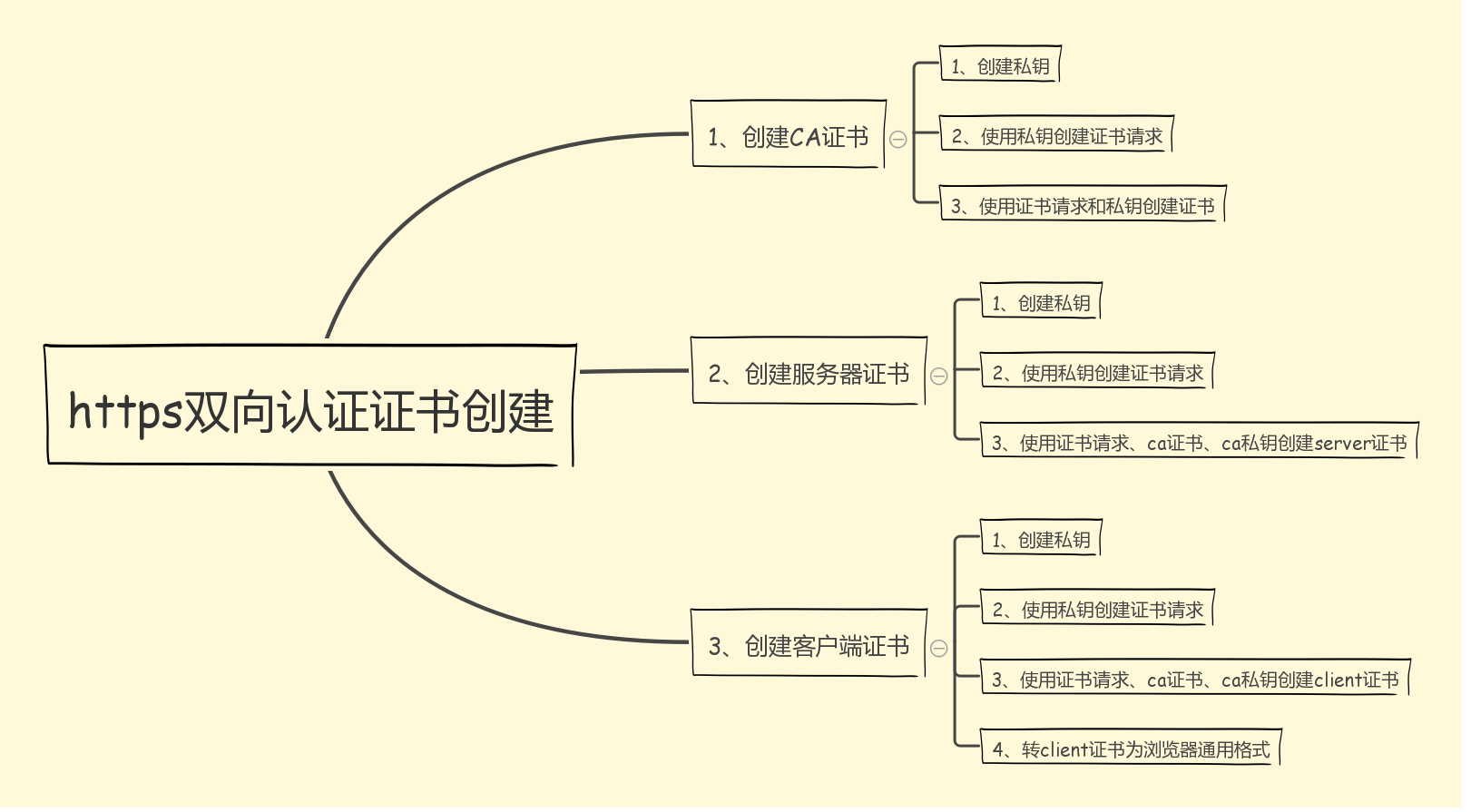
2.建立證書
建立證書的步驟如下
2.1建立相關目錄
這裡apache目錄位於/data/webapps/apache
在apache目錄下建立ca目錄(方便管理,可自定義)
mkdir /data/webapps/apache/ca
在ca目錄下建立相關目錄
cd /data/webapps/apache/ca
mkdirs conf newcerts private server users
2.2建立相關檔案
在conf目錄下建立openssl.conf
cd conf
vi openssl.conf
內容如下:
[ ca ]
default_ca = foo # The default ca section
[ foo ]
dir = /data/webapps/apache/ca # top dir
database = /data/webapps/apache/ca/index.txt # index file.
new_certs_dir = /data/webapps/apache/ca/newcerts # new certs dir 在ca目錄建立1_create_ca.sh指令碼
cd ..
vi 1_create_ca.sh
內容如下:
#!/bin/sh
basedir="/data/webapps/apache/ca"
# Generate the key.
openssl genrsa -out private/ca.key
# Generate a certificate request.
openssl req -new -key private/ca.key -out private/ca.csr
# Self signing key is bad... this could work with a third party signed key... registeryfly has them on for $16 but I'm too cheap lazy to get one on a lark.
# I'm also not 100% sure if any old certificate will work or if you have to buy a special one that you can sign with. I could investigate further but since this
# service will never see the light of an unencrypted Internet see the cheap and lazy remark.
# So self sign our root key.
openssl x509 -req -days 365 -in private/ca.csr -signkey private/ca.key -out private/ca.crt
# Setup the first serial number for our keys... can be any 4 digit hex string... not sure if there are broader bounds but everything I've seen uses 4 digits.
echo FACE > serial
# Create the CA's key database.
touch index.txt
# Create a Certificate Revocation list for removing 'user certificates.'
openssl ca -gencrl -out ${basedir}/private/ca.crl -crldays 7 -config "${basedir}/conf/openssl.conf"建立2_create_server.sh
vi 2_create_server.sh
內容如下:
#!/bin/bash
basedir="/data/webapps/apache/ca"
# Create us a key. Don't bother putting a password on it since you will need it to start apache. If you have a better work around I'd love to hear it.
openssl genrsa -out server/server.key
# Take our key and create a Certificate Signing Request for it.
openssl req -new -key server/server.key -out server/server.csr
# Sign this bastard key with our bastard CA key.
openssl ca -in server/server.csr -cert private/ca.crt -keyfile private/ca.key -out server/server.crt -config "${basedir}/conf/openssl.conf"建立3_create_user.sh
vi 3_create_user.sh
內容如下:
#!/bin/sh
# The base of where our SSL stuff lives.
base="/data/webapps/apache/ca"
# Were we would like to store keys... in this case we take the username given to us and store everything there.
mkdir -p $base/users/
# Let's create us a key for this user... yeah not sure why people want to use DES3 but at least let's make us a nice big key.
openssl genrsa -des3 -out $base/users/client.key 1024
# Create a Certificate Signing Request for said key.
openssl req -new -key $base/users/client.key -out $base/users/client.csr
# Sign the key with our CA's key and cert and create the user's certificate out of it.
openssl ca -in $base/users/client.csr -cert $base/private/ca.crt -keyfile $base/private/ca.key -out $base/users/client.crt -config "${base}/conf/openssl.conf"
# This is the tricky bit... convert the certificate into a form that most browsers will understand PKCS12 to be specific.
# The export password is the password used for the browser to extract the bits it needs and insert the key into the user's keychain.
# Take the same precaution with the export password that would take with any other password based authentication scheme.
openssl pkcs12 -export -clcerts -in $base/users/client.crt -inkey $base/users/client.key -out $base/users/client.p122.3 按順序執行指令碼,建立所有證書
sh ./1_create_ca.sh
sh ./2_create_server.sh
sh ./3_create_user.sh建立過程中如下注冊資訊需一致
Country Name:CN
State or Province Name:Shanghai
Locality Name (eg, city):Shanghai
Organization Name (eg, company):pers
Organizational Unit Name:jack
Common Name:pers.jack
Email Address:qsjwork@163.com2.4 配置apache
編輯%HTTPD_HOME%/conf/extra/http-ssl.conf檔案
新增或修改如下內容:
SSLEngine on
SSLCertificateFile "/data/webapps/apache/ca/server/server.crt"
SSLCertificateKeyFile "/data/webapps/apache/ca/server/server.key"
SSLCACertificateFile "/data/webapps/apache/ca/private/ca.crt"
SSLVerifyClient require
SSLVerifyDepth 10