SSL/TLS深度解析--在 Nginx 上部署 TLS
利用 openssl 原始碼安裝 Nginx
[[email protected] software]# tar xf nginx-1.15.5.tar.gz
[[email protected] software]# cd nginx-1.15.5/
[[email protected] nginx-1.15.5]# groupadd nginx
[[email protected] nginx-1.15.5]# useradd nginx -M -s /sbin/nologin -g nginx
[[email protected] nginx-1.15.5]# mkdir -p /project/nginx1.15.0
[ 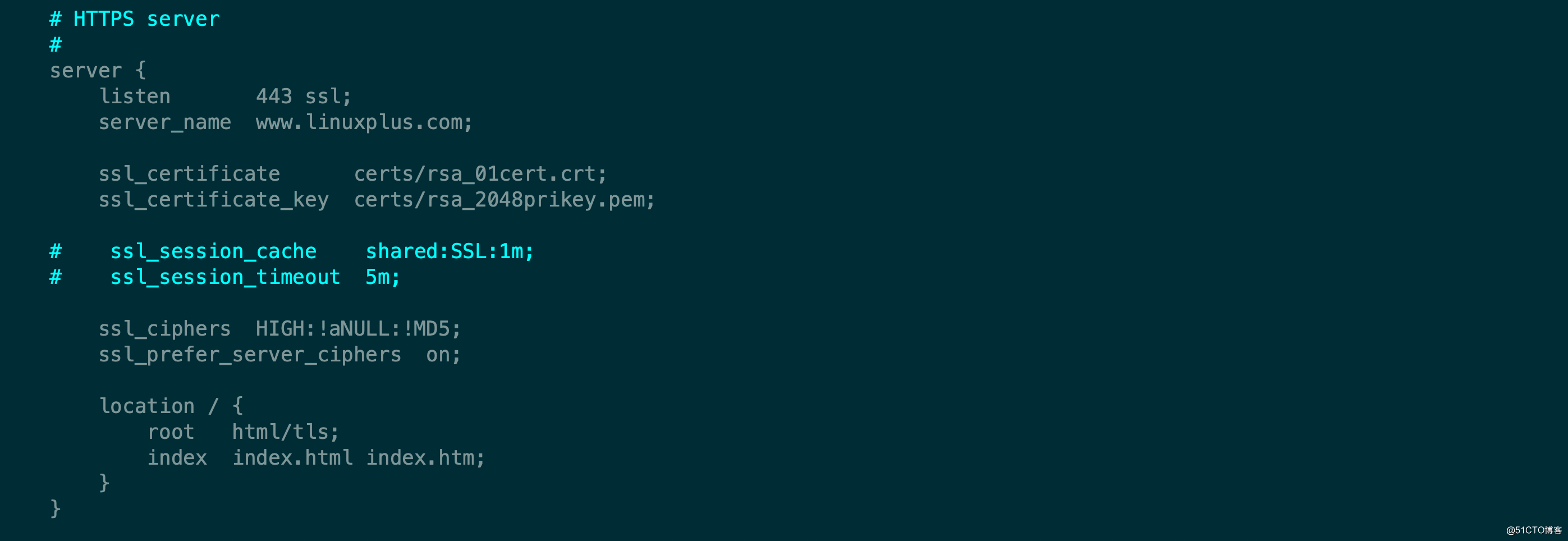
TLS 協議的配置
Nginx協議配置有3個主要的配置項
- ssl_protocols :用來指定所開啟協議的版本,目前1.2是主流而且更高效。不安全的SSLv2 和 SSLv3 都要禁用。
ssl_protocols TLSv1 TLSv1.1 TLSv1.2;
目前最新的TLS是1.3版本,不過目前也沒有大範圍使用,不過要支援TLS1.3,要使用openssl的1.1.1系列版本,所以要使用TLS1.3,升級openssl 並且在編譯安裝nginx的時候指定。ssl_protocols TLSv1 TLSv1.1 TLSv1.2; - ssl_prefer_server_ciphers ,在伺服器與客戶端TLS握手時啟用伺服器演算法優先,由
伺服器端選擇演算法,這樣可以避免很多客戶端被***或比較老舊而引起的安全問題。
ssl_prefer_server_ciphers on;- ssl_ciphers ,指定使用的演算法套件以及它們的優先順序。
ssl_ciphers "ECDHE-ECDSA-AES128-GCM-SHA256 ECDHE-ECDSA-AES256-GCM-SHA384 ECDHE-RSA-AES128-GCM-SHA256 ECDHE-RSA-AES256-GCM
-SHA384 ECDHE-ECDSA-AES128-GCM-SHA256 ECDHE-RSA-AES128-SHA256 ECDHE-ECDSA-AES128-SHA ECDHE-ECDSA-AES256-SHA ECDHE-RSA-AES256-SHA
AES128-SHA AES256-SHA ECDHE-RSA-RC4-SHA RC4-SHA"; #排在前面的優先使用- 萬用字元證書是證書的CN採用通配形式,即 *.linuxplus.com 這樣的模式。如果確定採用全站https的話,這樣的通配證書是可行的,很多大站點也是這樣做的,例如淘寶。
- 如果多個不同域名(二級域名)的站點使用同一個證書,可以把它們部署在同一個IP地址上。還是建議使用SNI,使每個站點有自己單獨的證書。
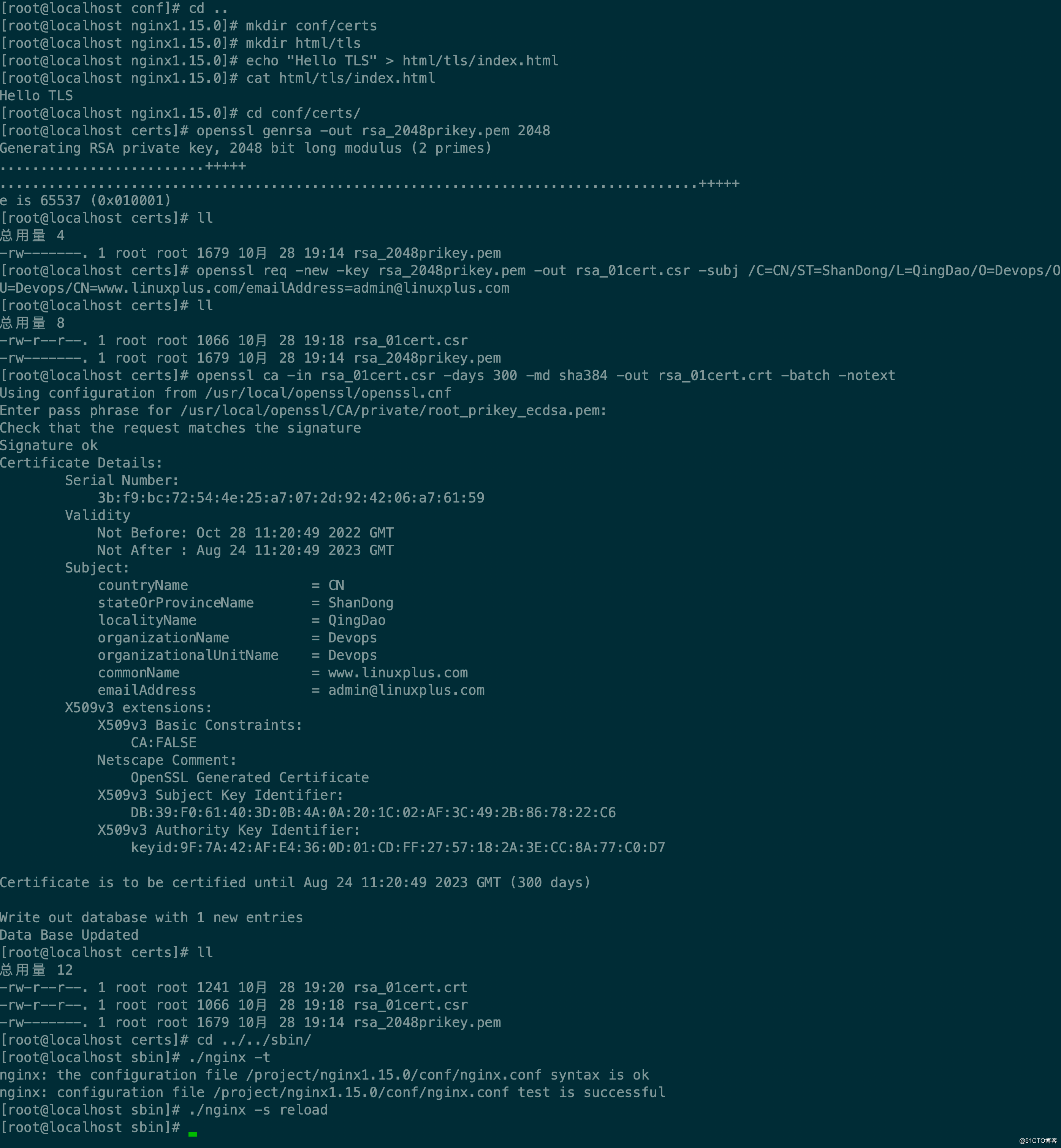
配置雙證書
[[email protected] certs]# openssl ecparam -genkey -name prime256v1 -out ecdsa_01prikey.pem
[[email protected] certs]# openssl req -new -key ecdsa_01prikey.pem -out ecc01.csr -subj /C=CN/ST=ShanDong/L=QingDao/O=Devops/OU=Devops/CN=www.linuxplus.com/[email protected]
[[email protected] certs]# openssl ca -in ecc01.csr -days 365 -out ecc_01cert.crt -batch -notext Using configuration from /usr/local/openssl/openssl.cnf
Enter pass phrase for /usr/local/openssl/CA/private/root_prikey_ecdsa.pem:
Check that the request matches the signature
Signature ok
Certificate Details:
Serial Number:
92:f4:3b:df:f9:ac:3b:5c:aa:31:89:d6:61:c6:9a:fc
Validity
Not Before: Nov 10 14:32:15 2018 GMT
Not After : Nov 10 14:32:15 2019 GMT
Subject:
countryName = CN
stateOrProvinceName = ShanDong
localityName = QingDao
organizationName = Devops
organizationalUnitName = Devops
commonName = www.linuxplus.com
emailAddress = [email protected]
X509v3 extensions:
X509v3 Basic Constraints:
CA:FALSE
Netscape Comment:
OpenSSL Generated Certificate
X509v3 Subject Key Identifier:
67:7B:E7:71:A6:D5:63:C7:C3:E7:6F:E4:40:B4:06:1C:D5:B6:84:58
X509v3 Authority Key Identifier:
keyid:7A:15:85:5F:24:70:45:4C:86:C3:FD:AA:9A:88:3E:5B:E6:63:70:56
Certificate is to be certified until Nov 10 14:32:15 2019 GMT (365 days)
Write out database with 1 new entries
Data Base Updated
[[email protected] ~]# cd /project/nginx1.15.0/conf/
[[email protected] conf]# vim nginx.conf
......
ssl_certificate certs/ecc_01cert.crt;
ssl_certificate_key certs/ecdsa_01prikey.pem;
ssl_certificate certs/rsa_01cert.crt;
ssl_certificate_key certs/rsa_2048prikey.pem;
ssl_protocols TLSv1 TLSv1.1 TLSv1.2;
[[email protected] conf]# ../sbin/nginx -t
nginx: the configuration file /project/nginx1.15.0/conf/nginx.conf syntax is ok
nginx: configuration file /project/nginx1.15.0/conf/nginx.conf test is successful
[[email protected] conf]# ../sbin/nginx -s reload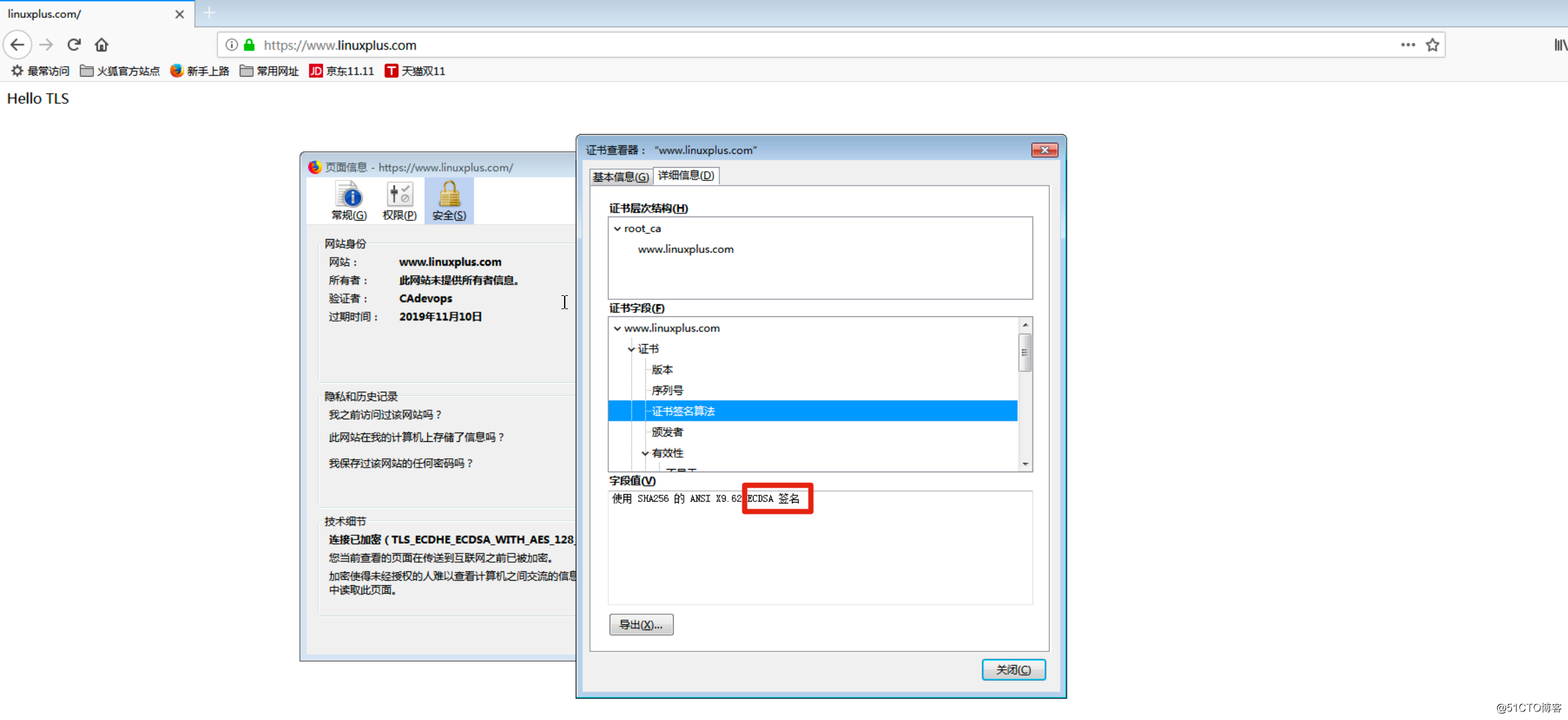
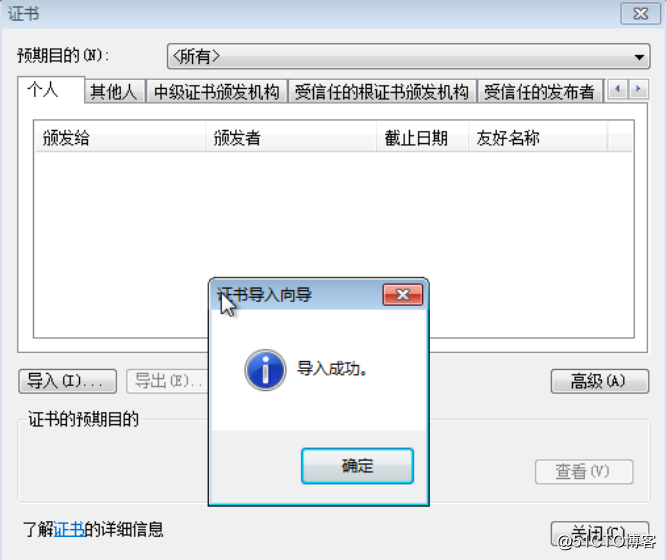
客戶端身份驗證
客戶端驗證,是為了實現只有有證書的客戶端才能訪問那個站點或服務,證書由站點管理和頒發
[[email protected] certs]# openssl genrsa -out client01.key 2048
Generating RSA private key, 2048 bit long modulus (2 primes)
...........................................................................................................+++++
........................+++++
e is 65537 (0x010001)
[[email protected] certs]# openssl req -new -key client01.key -out client01.csr -subj /C=CN/ST=ShanXi/L=XiAn/O=Devops01/OU=Devops01/CN=www.linuxplus.com/[email protected]
[[email protected] certs]# openssl ca -in client01.csr -md sha384 -out client01_cert.crt -batch -notext
Using configuration from /usr/local/openssl/openssl.cnf
Enter pass phrase for /usr/local/openssl/CA/private/root_prikey_ecdsa.pem:
Check that the request matches the signature
Signature ok
Certificate Details:
Serial Number:
92:f4:3b:df:f9:ac:3b:5c:aa:31:89:d6:61:c6:9a:fd
Validity
Not Before: Nov 11 06:06:53 2018 GMT
Not After : Nov 11 06:06:53 2019 GMT
Subject:
countryName = CN
stateOrProvinceName = ShanXi
localityName = XiAn
organizationName = Devops01
organizationalUnitName = Devops01
commonName = www.linuxplus.com
emailAddress = [email protected]
X509v3 extensions:
X509v3 Basic Constraints:
CA:FALSE
Netscape Comment:
OpenSSL Generated Certificate
X509v3 Subject Key Identifier:
AC:6C:C1:A7:5A:C5:91:BD:97:3C:4A:2D:CA:03:53:91:38:E9:3B:E6
X509v3 Authority Key Identifier:
keyid:7A:15:85:5F:24:70:45:4C:86:C3:FD:AA:9A:88:3E:5B:E6:63:70:56
Certificate is to be certified until Nov 11 06:06:53 2019 GMT (365 days)
Write out database with 1 new entries
Data Base Updated
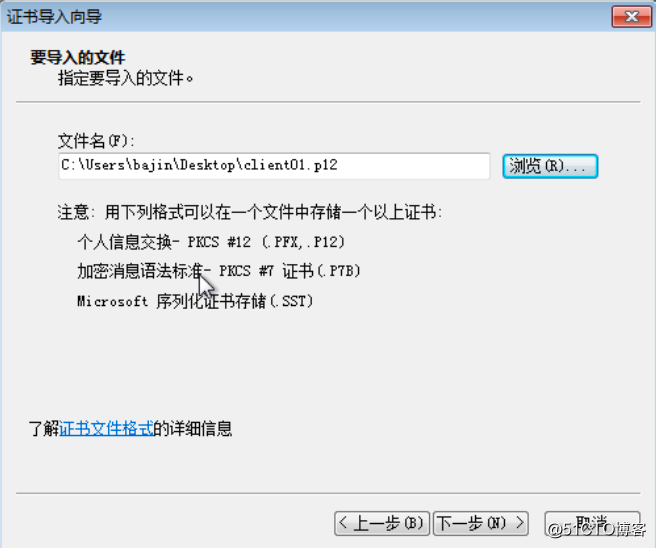
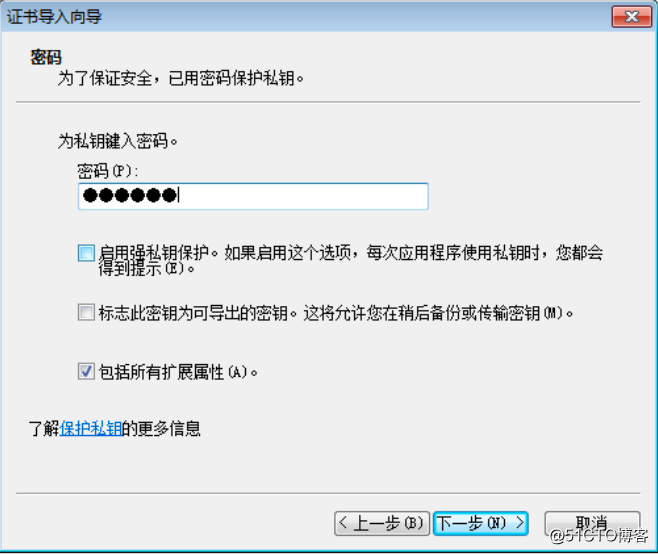
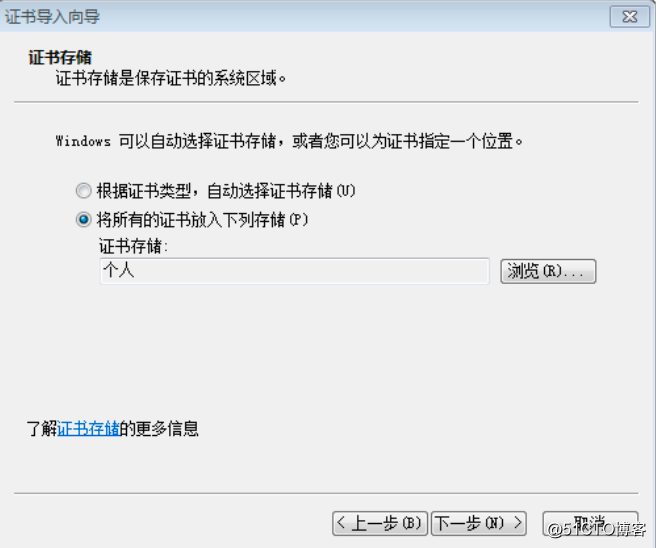
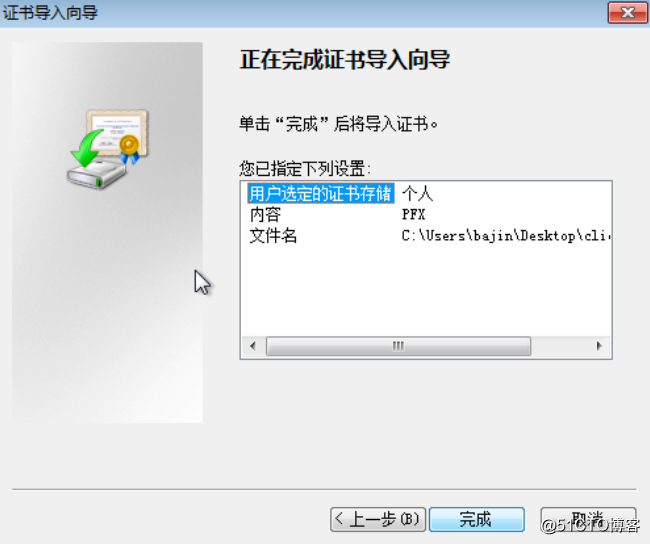
[[email protected] certs]# openssl pkcs12 -export -clcerts -passout pass:123456 -in client01_cert.crt -inkey client01.key -out client01.p12
[[email protected] ~]# cd /project/nginx1.15.0/conf/
[[email protected] conf]# vim nginx.conf
ssl_certificate certs/ecc_01cert.crt;
ssl_certificate_key certs/ecdsa_01prikey.pem;
ssl_certificate certs/rsa_01cert.crt;
ssl_certificate_key certs/rsa_2048prikey.pem;
ssl_protocols TLSv1 TLSv1.1 TLSv1.2;
# 開啟客戶端身份驗證
ssl_verify_client on;
# 指定客戶端證書到根證書的深度
# ssl_verify_depth 2;
# 指定簽發客戶端證書的CA證書
ssl_client_certificate /usr/local/openssl/CA/root_cacert_ecc.pem;
# 完整證書鏈中需要包含的其他CA證書
# ssl_trusted_certificate rootca.crt;
# 證書吊銷列表,有更新時Nginx需要重新載入
ssl_crl /usr/local/openssl/CA/crl.pem;
#on:是開啟只接有客戶端證書的請求。如果請求未包含證書或者證書校驗失敗,nginx會返回一個400錯誤響應。
#off:是關閉
#optional:不會強制阻斷訪問,不返回400。可在 $ssl_client_verify 變數中檢視各種狀態, NONE表示沒有證書, FAILED表示證書未通過驗證, SUCCESS 表示證書有效。
[[email protected] conf]# ../sbin/nginx -t
nginx: the configuration file /project/nginx1.15.0/conf/nginx.conf syntax is ok
nginx: configuration file /project/nginx1.15.0/conf/nginx.conf test is successful
[[email protected] conf]# ../sbin/nginx -s reload-
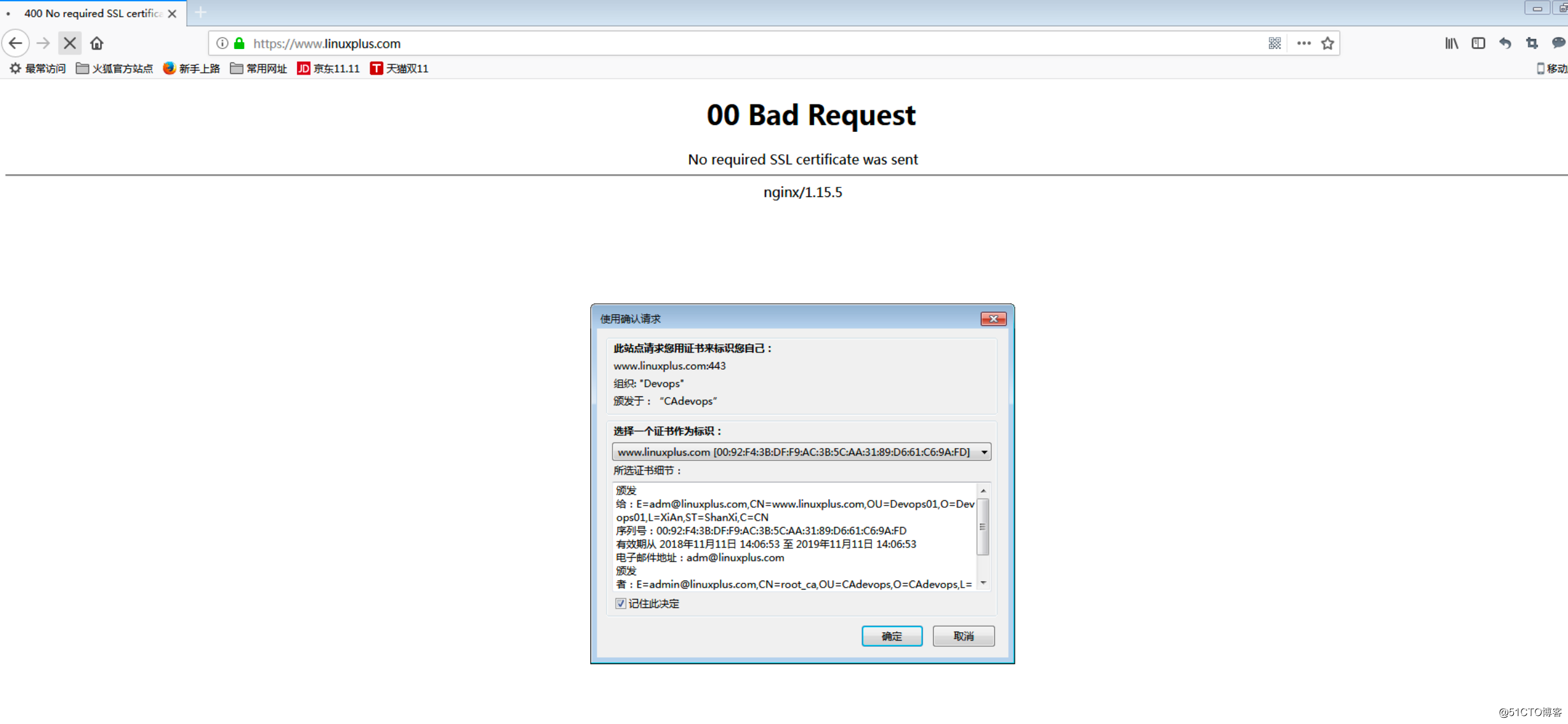
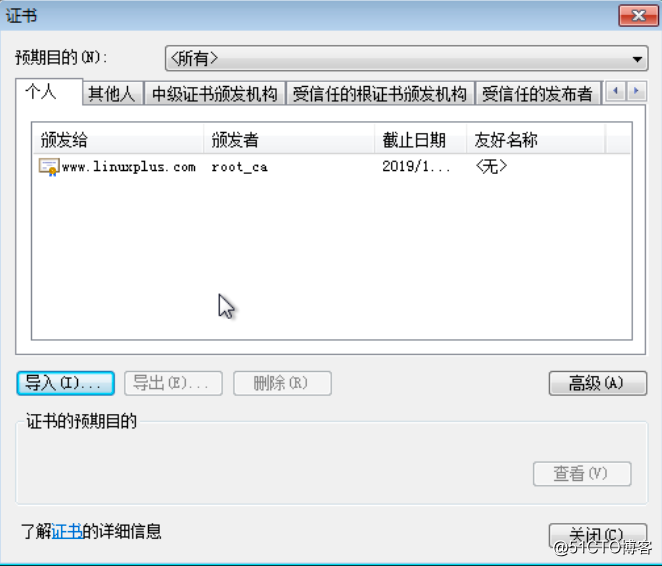
沒有匯入證書

-
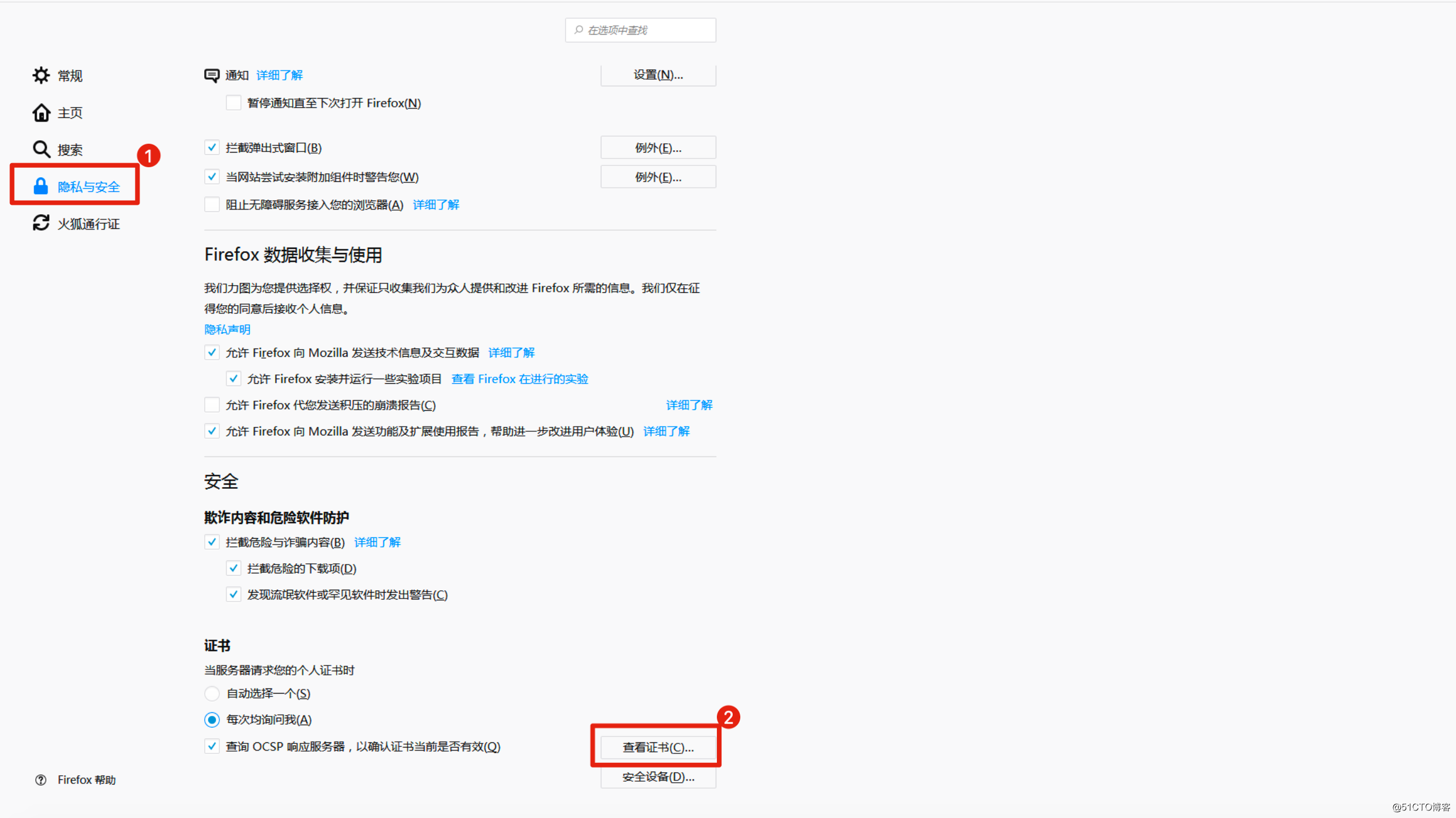
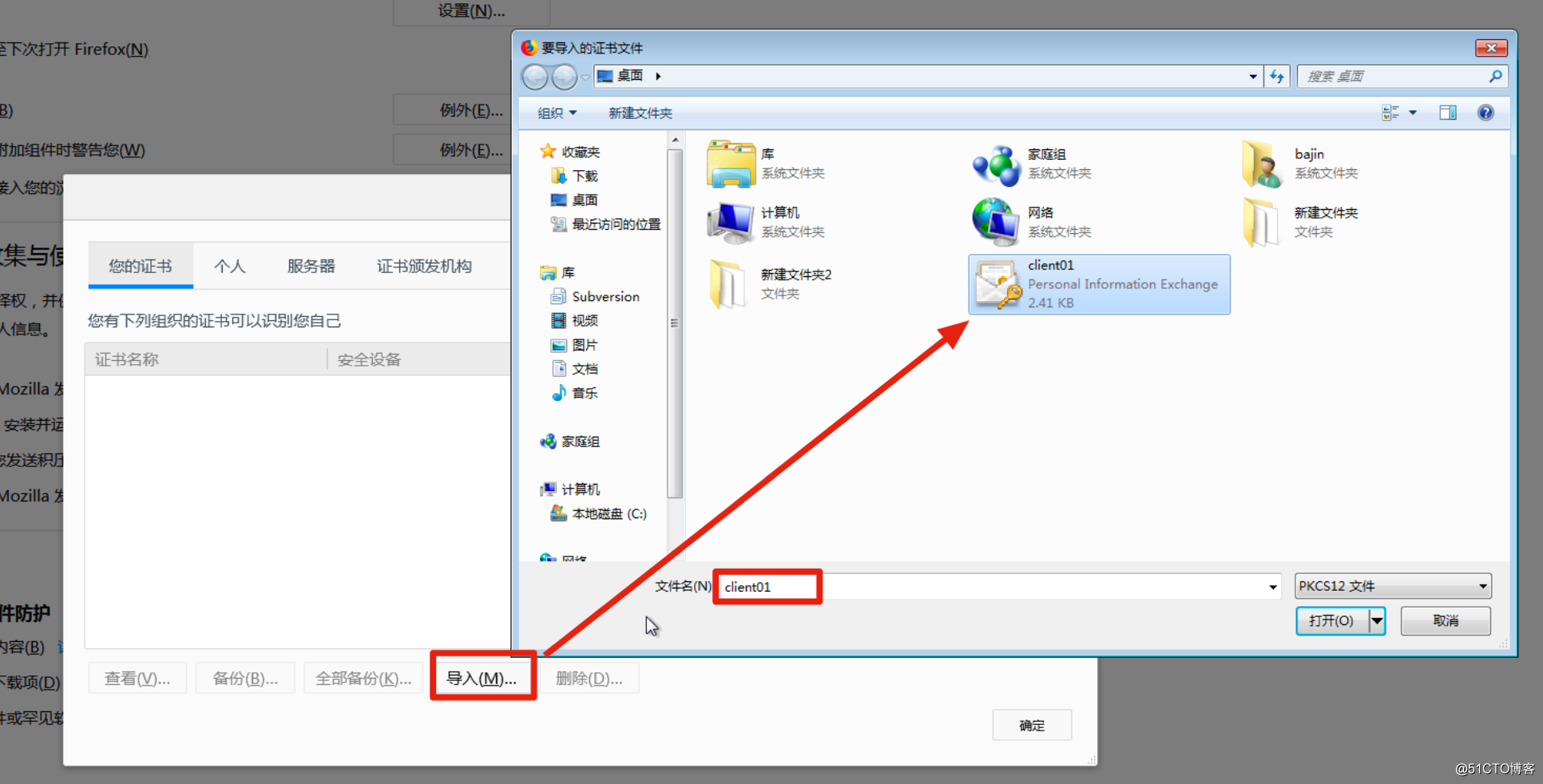
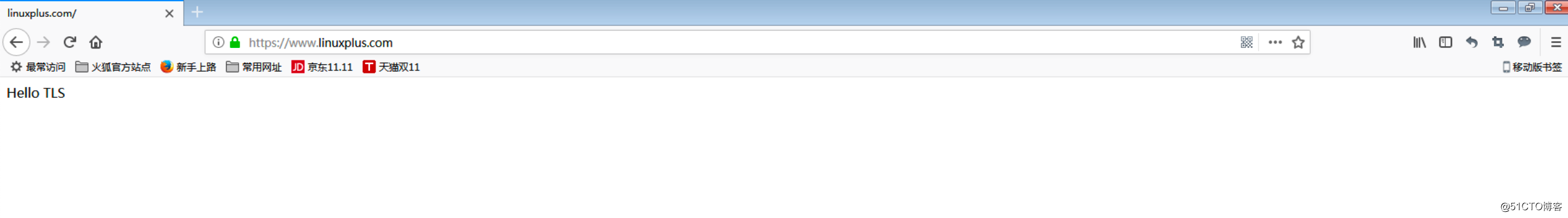
Firefox 匯入證書



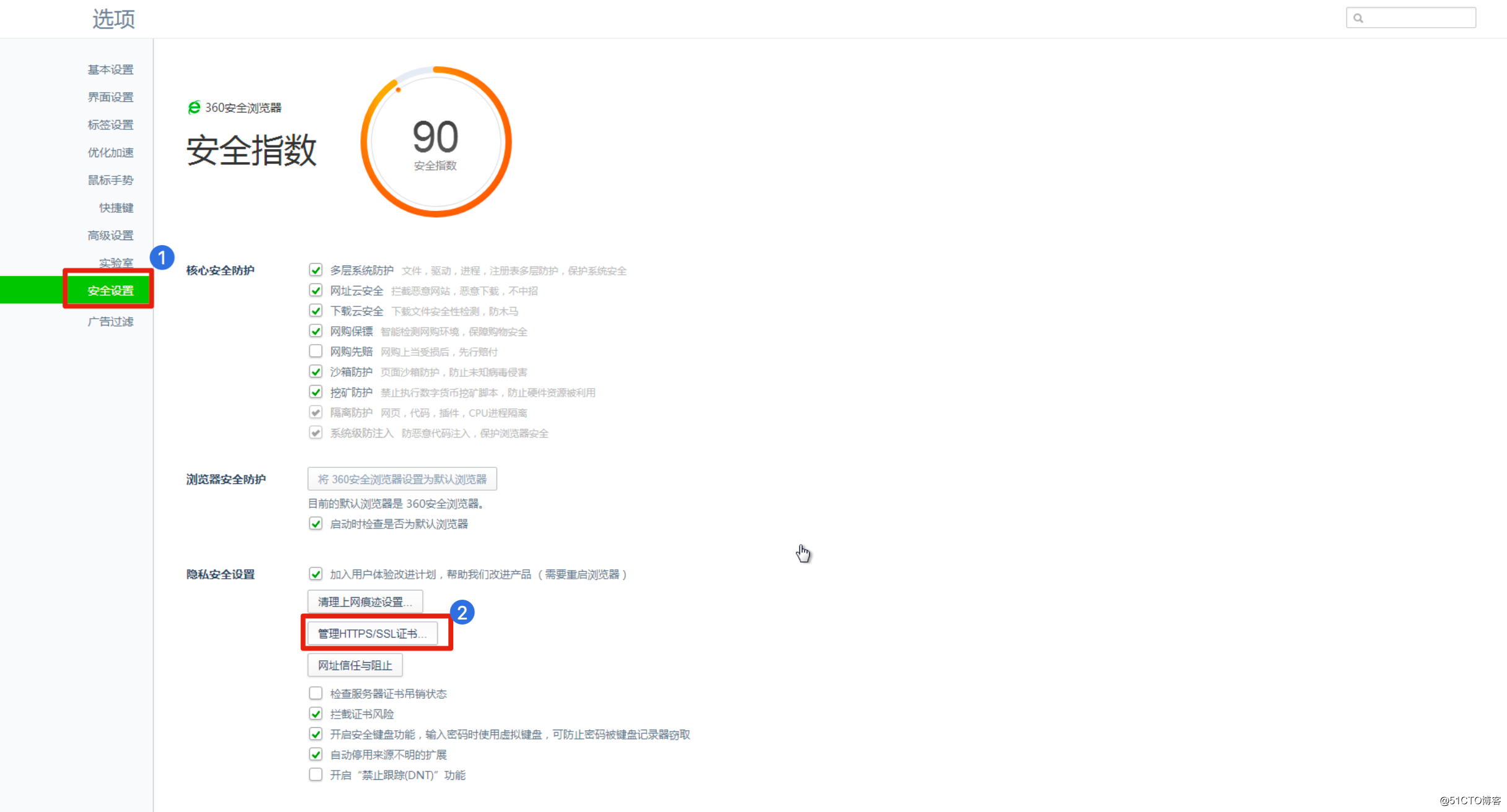
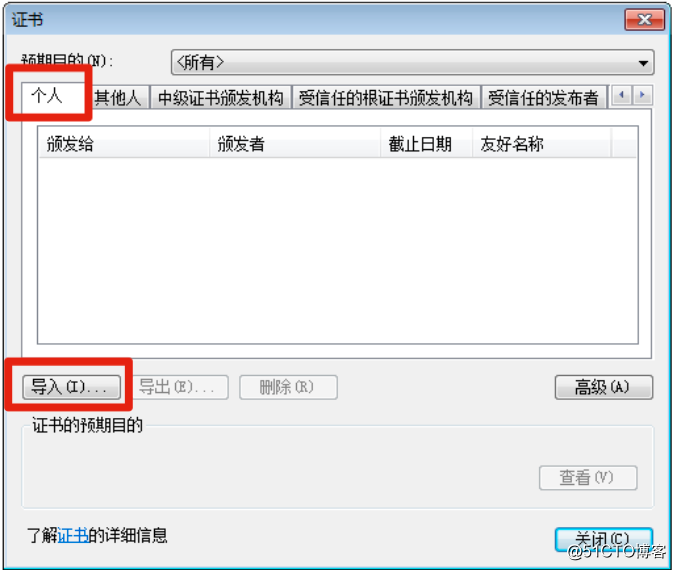
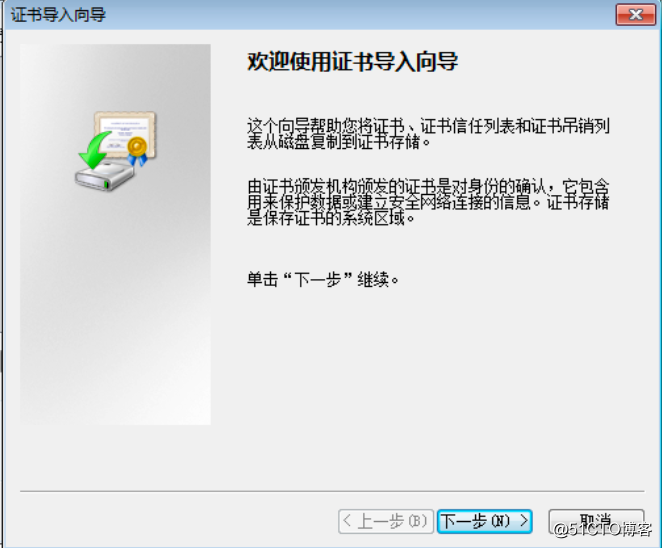
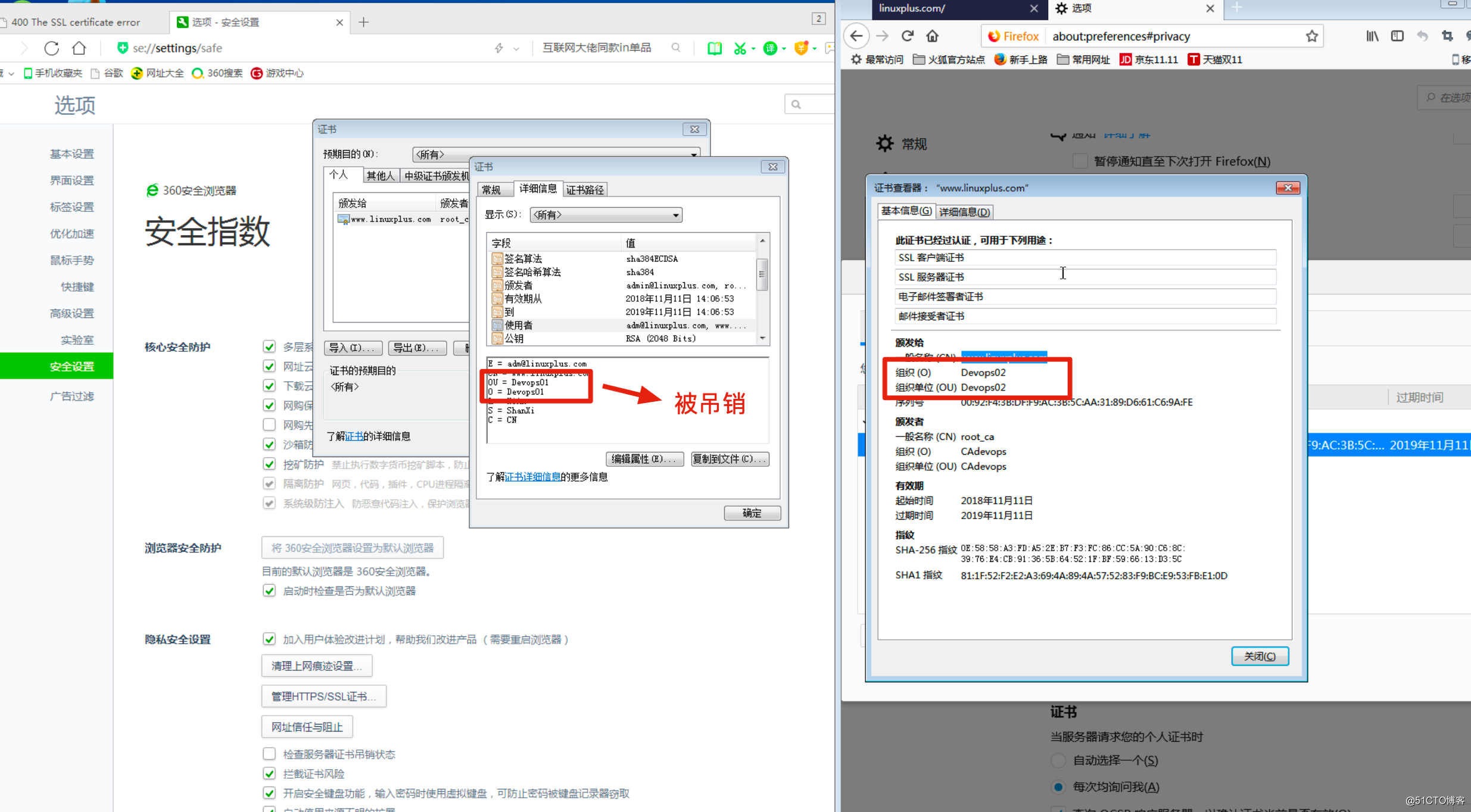
- 360瀏覽器匯入證書

[[email protected] certs]# openssl ca -in rsa_01cert.csr -days 300 -md sha384 -out rsa_01cert.crt -batch -notext^C
[[email protected] certs]# openssl req -new -key client02.key -out client02.csr -subj /C=CN/ST=ShanXi/L=XiAn/O=Devops02/OU=Devops02/CN=www.linuxplus.com/[email protected]
[[email protected] certs]# openssl ca -in client02.csr -md sha384 -out client02_cert.crt -batch -notext
Using configuration from /usr/local/openssl/openssl.cnf
Enter pass phrase for /usr/local/openssl/CA/private/root_prikey_ecdsa.pem:
Check that the request matches the signature
Signature ok
Certificate Details:
Serial Number:
92:f4:3b:df:f9:ac:3b:5c:aa:31:89:d6:61:c6:9a:fe
Validity
Not Before: Nov 11 14:00:18 2018 GMT
Not After : Nov 11 14:00:18 2019 GMT
Subject:
countryName = CN
stateOrProvinceName = ShanXi
localityName = XiAn
organizationName = Devops02
organizationalUnitName = Devops02
commonName = www.linuxplus.com
emailAddress = [email protected]
X509v3 extensions:
X509v3 Basic Constraints:
CA:FALSE
Netscape Comment:
OpenSSL Generated Certificate
X509v3 Subject Key Identifier:
6D:D2:63:9D:21:B1:82:4A:0F:19:B8:76:0F:B5:EA:E8:F0:F6:A3:6F
X509v3 Authority Key Identifier:
keyid:7A:15:85:5F:24:70:45:4C:86:C3:FD:AA:9A:88:3E:5B:E6:63:70:56
Certificate is to be certified until Nov 11 14:00:18 2019 GMT (365 days)
Write out database with 1 new entries
Data Base Updated
[[email protected] certs]# openssl pkcs12 -export -clcerts -passout pass:123456 -in client02_cert.crt -inkey client02.key -out client02.p12
#吊銷證書
[[email protected] certs]# openssl x509 -in client01_cert.crt -serial -noout
serial=92F43BDFF9AC3B5CAA3189D661C69AFD
[[email protected] certs]# openssl ca -revoke /usr/local/openssl/CA/newcerts/92F43BDFF9AC3B5CAA3189D661C69AFD.pem
Using configuration from /usr/local/openssl/openssl.cnf
Enter pass phrase for /usr/local/openssl/CA/private/root_prikey_ecdsa.pem:
Revoking Certificate 92F43BDFF9AC3B5CAA3189D661C69AFD.
Data Base Updated
[[email protected] certs]# openssl ca -gencrl -out /usr/local/openssl/CA/crl.pem
Using configuration from /usr/local/openssl/openssl.cnf
Enter pass phrase for /usr/local/openssl/CA/private/root_prikey_ecdsa.pem:
[[email protected] certs]# openssl crl -in /usr/local/openssl/CA/crl.pem -text
Certificate Revocation List (CRL):
Version 2 (0x1)
Signature Algorithm: ecdsa-with-SHA256
Issuer: C = CN, ST = BeiJing, L = BeiJing, O = CAdevops, OU = CAdevops, CN = root_ca, emailAddress = [email protected]
Last Update: Nov 11 14:33:36 2018 GMT
Next Update: Dec 11 14:33:36 2018 GMT
CRL extensions:
X509v3 CRL Number:
1048577
Revoked Certificates:
Serial Number: 92F43BDFF9AC3B5CAA3189D661C69AFD
Revocation Date: Nov 11 14:26:37 2018 GMT
Signature Algorithm: ecdsa-with-SHA256
30:45:02:21:00:e3:76:00:d4:07:22:2a:7f:43:1f:aa:8c:f5:
be:c7:f7:a9:bd:1f:fb:65:f0:0b:d8:0c:a0:15:7c:f3:37:5d:
63:02:20:08:d6:b8:4b:6b:3f:d2:7d:89:5f:2d:88:b5:ee:18:
cd:81:6d:fe:80:4f:0c:ef:78:b8:81:c1:dc:ca:85:a3:9b
-----BEGIN X509 CRL-----
MIIBTjCB9QIBATAKBggqhkjOPQQDAjCBjTELMAkGA1UEBhMCQ04xEDAOBgNVBAgM
B0JlaUppbmcxEDAOBgNVBAcMB0JlaUppbmcxETAPBgNVBAoMCENBZGV2b3BzMREw
DwYDVQQLDAhDQWRldm9wczEQMA4GA1UEAwwHcm9vdF9jYTEiMCAGCSqGSIb3DQEJ
ARYTYWRtaW5AbGludXhwbHVzLmNvbRcNMTgxMTExMTQzMzM2WhcNMTgxMjExMTQz
MzM2WjAkMCICEQCS9Dvf+aw7XKoxidZhxpr9Fw0xODExMTExNDI2MzdaoBAwDjAM
BgNVHRQEBQIDEAABMAoGCCqGSM49BAMCA0gAMEUCIQDjdgDUByIqf0Mfqoz1vsf3
qb0f+2XwC9gMoBV88zddYwIgCNa4S2s/0n2JXy2Ite4YzYFt/oBPDO94uIHB3MqF
o5s=
-----END X509 CRL-----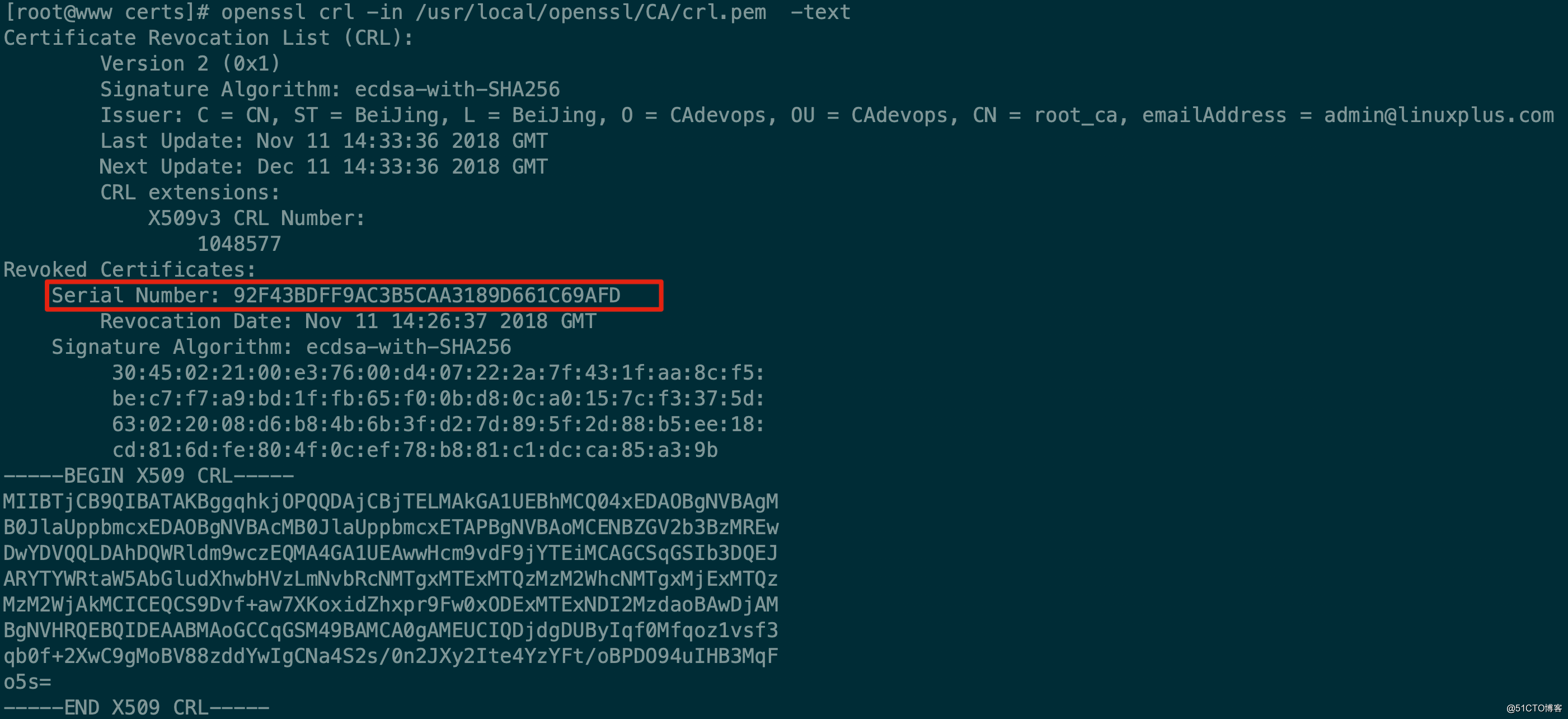
[[email protected] conf]# vim nginx.conf
log_format tls "$ssl_client_verify $pid $scheme $server_name $time_local $remote_addr $connection $connection_requests $ssl_protocol $ssl_cipher $ssl_session_id $ssl_session_reused $ssl_curves";
access_log /project/logs/nginx/access.log tls;
#$scheme:使用哪種協議
#$connection:TCP連線序號
#$connection_requests:表示在一個連線(長連線)裡面有多少次請求
[[email protected] logs]# tail -f access.log
SUCCESS 20481 https www.linuxplus.com 23/Nov/2018:23:12:03 +0800 172.16.216.181 315 1 TLSv1.2 ECDHE-ECDSA-AES128-GCM-SHA256 - . X25519:prime256v1:secp384r1:secp521r1:0x0100:0x0101
SUCCESS 20481 https www.linuxplus.com 23/Nov/2018:23:12:03 +0800 172.16.216.181 315 2 TLSv1.2 ECDHE-ECDSA-AES128-GCM-SHA256 - . X25519:prime256v1:secp384r1:secp521r1:0x0100:0x0101
SUCCESS 20481 https www.linuxplus.com 23/Nov/2018:23:12:28 +0800 172.16.216.181 315 3 TLSv1.2 ECDHE-ECDSA-AES128-GCM-SHA256 - . X25519:prime256v1:secp384r1:secp521r1:0x0100:0x0101
SUCCESS 20481 https www.linuxplus.com 23/Nov/2018:23:12:28 +0800 172.16.216.181 315 4 TLSv1.2 ECDHE-ECDSA-AES128-GCM-SHA256 - . X25519:prime256v1:secp384r1:secp521r1:0x0100:0x0101
........
#SUCCESS:表示成功
#20481:Nginx的PID
#ECDHE-ECDSA-AES128-GCM-SHA256:金鑰套件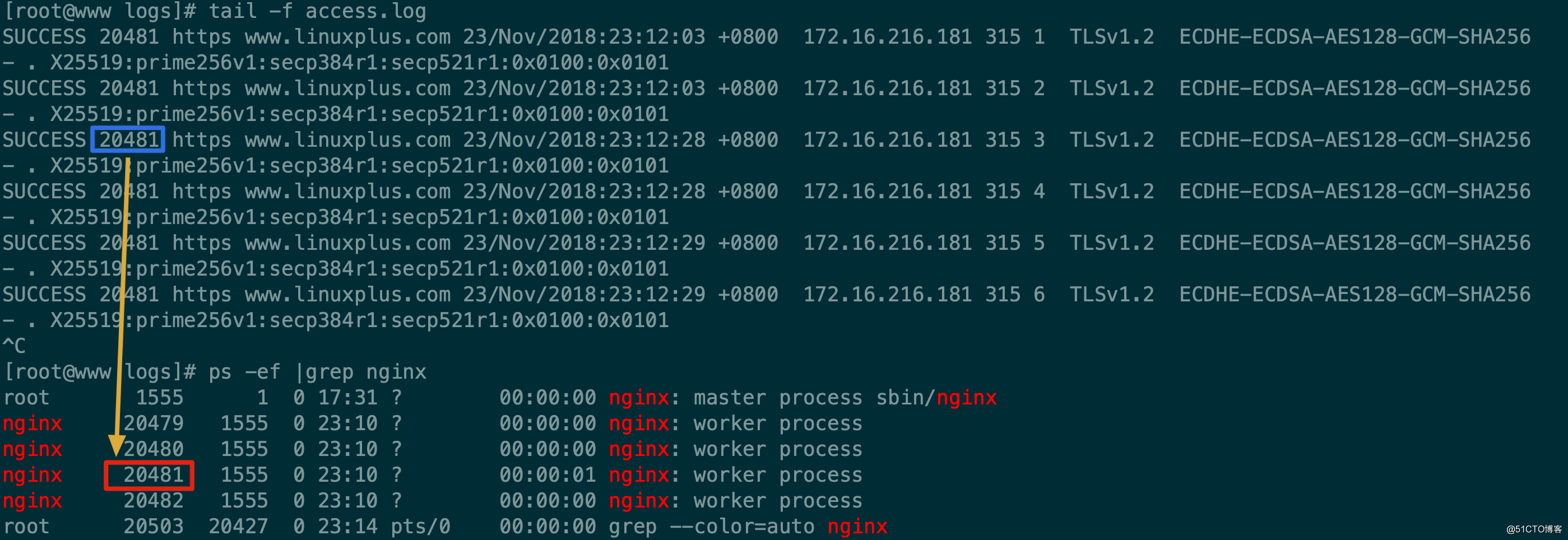
會話快取
- 獨立會話快取
[[email protected] nginx1.15.0]# vim conf/nginx.conf
ssl_session_tickets off;
ssl_session_cache shared:SSL:1m; #分配1MB的共享記憶體快取,使用1 MB的記憶體可以快取大約4000個會話
ssl_session_timeout 5m; #設定會話快取過期時間,預設的會話快取過期時間只有5分鐘
SUCCESS 20574 https www.linuxplus.com 23/Nov/2018:23:43:22 +0800 172.16.216.181 331 1 TLSv1.2 ECDHE-ECDSA-AES128-GCM-SHA256 20dfe772e67ea1fd9792ad5718cd416be900c51df38bf05ed87371049c1c41ed r -
SUCCESS 20574 https www.linuxplus.com 23/Nov/2018:23:43:22 +0800 172.16.216.181 331 2 TLSv1.2 ECDHE-ECDSA-AES128-GCM-SHA256 20dfe772e67ea1fd9792ad5718cd416be900c51df38bf05ed87371049c1c41ed r -
SUCCESS 20574 https www.linuxplus.com 23/Nov/2018:23:43:24 +0800 172.16.216.181 331 3 TLSv1.2 ECDHE-ECDSA-AES128-GCM-SHA256 20dfe772e67ea1fd9792ad5718cd416be900c51df38bf05ed87371049c1c41ed r -
SUCCESS 20574 https www.linuxplus.com 23/Nov/2018:23:43:24 +0800 172.16.216.181 331 4 TLSv1.2 ECDHE-ECDSA-AES128-GCM-SHA256 20dfe772e67ea1fd9792ad5718cd416be900c51df38bf05ed87371049c1c41ed r -
SUCCESS 20574 https www.linuxplus.com 23/Nov/2018:23:43:24 +0800 172.16.216.181 331 5 TLSv1.2 ECDHE-ECDSA-AES128-GCM-SHA256 20dfe772e67ea1fd9792ad5718cd416be900c51df38bf05ed87371049c1c41ed r -
SUCCESS 20574 https www.linuxplus.com 23/Nov/2018:23:43:24 +0800 172.16.216.181 331 6 TLSv1.2 ECDHE-ECDSA-AES128-GCM-SHA256 20dfe772e67ea1fd9792ad5718cd416be900c51df38bf05ed87371049c1c41ed r -
#r 則表示被重用,如果是.表示沒有重用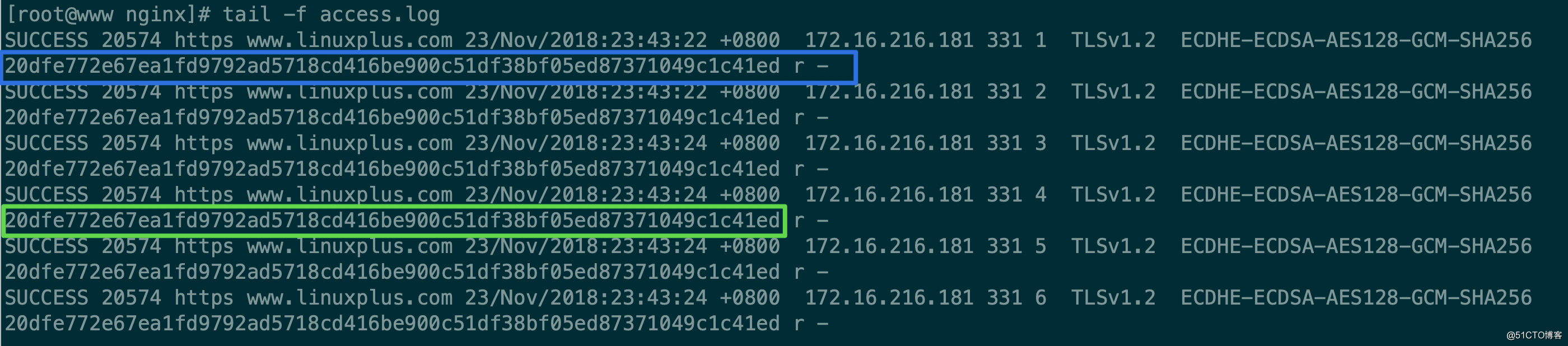
-
配置項使用格式:
ssl_session_cache off | none | [builtin[:size]] [shared:name:size]預設選項是 none;
off :禁用快取 。
none:禁用快取,但是通知客戶端可以重用會話(session),但是並不實際儲存。
builtin:內建,這個快取只能被一個worker程序使用(nginx可以有過個worker程序),與builtin 配合的單位引數是個數 builtin:100 表示快取100個session;如果沒有寫明數量 那麼預設是20480個session。使用builtin會引起一些記憶體碎片。
shared:共享, shared:xx_name:xxM;,在多個worker程序中共享session,單位是M(兆位元組),1M可以存放大概4000個session,共享的快取可以有1個名稱,名稱一樣的快取可以在多個 nginx 上配置的 server 塊上共享使用。
還可以混合使用 builtin 和 shared
ssl_session_cache builtin:1000 shared:SSL:10m; 只用共享快取而不用內建快取應該更有效率。根據專案情況來決定。 - 分散式會話票證
[[email protected] nginx1.15.0]# cd conf/certs/
[[email protected] certs]# openssl rand -out ticket48.key 48
[[email protected] certs]# openssl rand -out ticket80.key 80
[[email protected] certs]# ll -l ticket48.key
-rw-r--r--. 1 root root 48 11月 24 14:23 ticket48.key
[[email protected] certs]# ll -l ticket80.key
-rw-r--r--. 1 root root 80 11月 24 14:31 ticket80.key
[[email protected] certs]# cd ../..
[[email protected] nginx1.15.0]# vim conf/nginx.conf
ssl_session_tickets on;
ssl_session_ticket_key certs/ticket48.key; #設定新金鑰,用於新票證的加解密
ssl_session_ticket_key certs/ticket80.key; #保留前一個金鑰用於老票證的解密
[[email protected] nginx1.15.0]# sbin/nginx -s reload
[[email protected] nginx1.15.0]# openssl s_client -connect 172.16.216.188:443
.......
SSL-Session:
Protocol : TLSv1.2
Cipher : ECDHE-ECDSA-AES128-GCM-SHA256
Session-ID: 0734C4A2519DD91A6B03BA6E1A572FA2E8DAB69CC23A41A249E4219B6B16934E
Session-ID-ctx:
Master-Key: AC6A686B930A886990E031117F1032F5829C57EAFA2C363D9917973E401FE420D5F566BA5F5CD5ED2E922F5E6E6E1F1B
PSK identity: None
PSK identity hint: None
SRP username: None
TLS session ticket lifetime hint: 300 (seconds)
TLS session ticket:
0000 - 95 0a 94 18 66 9c fa fb-bb e7 79 81 19 46 a5 77 ....f.....y..F.w
0010 - ec a8 37 e6 6e a2 34 0d-4e 2b e2 ce 58 3c a8 23 ..7.n.4.N+..X<.#
0020 - 8f 73 59 fd 30 0a bf 37-e2 47 6d 9e 10 76 1a 90 .sY.0..7.Gm..v..
0030 - f5 5d 7c 8c e0 32 a5 d4-3a a5 c5 e9 dc 62 e5 eb .]|..2..:....b..
0040 - fc 7d c0 98 df dd 76 4c-29 d6 51 79 d9 6a c2 f7 .}....vL).Qy.j..
0050 - e2 a5 ec a3 46 d1 27 3c-75 12 38 18 ec 20 b1 18 ....F.'<u.8.. ..
0060 - 41 13 be 58 45 96 a5 1f-7a 90 aa a1 73 17 8b 27 A..XE...z...s..'
0070 - 89 7b 63 2a 2f ad 61 53-3d d8 4e 13 c6 41 97 1f .{c*/.aS=.N..A..
0080 - ec 75 d7 bf 7f 96 29 4d-cf f6 3e 0d 23 35 fc 9a .u....)M..>.#5..
0090 - 57 98 2a 81 2c e7 b0 e1-27 33 aa d7 fb 13 01 c3 W.*.,...'3......
00a0 - 91 86 f5 63 5c b5 be 1a-58 a5 99 61 1a 82 36 de ...c\...X..a..6.
......
使用兩個金鑰輪轉的方式,在金鑰更新時伺服器就不會丟棄更新前建立的會話。
在叢集中實施會話票證金鑰的輪替是不可靠的,因為無法完美的實現新的金鑰在同一個時刻被所有節點同時更新。如果某個節點在其他節點前使用了新金鑰,並給某個客戶端生成了票據,隨後客戶端再次傳送過來的請求被分配到其他節點處理,而其他節點可能無法解密資料(叢集未採取流量保持機制),而導致SSL重新握手,這樣會造成效能下降,甚至會出現一個瓶頸期;歸根結底是各個節點在重新載入配置的時候會不可避免的存在時間差。如果選擇使用會話票證,不要過於頻繁的更新金鑰,儘量在設計上會使用流量保持,把同一個使用者分發到相同節點。
如果要完美地實現叢集的會話票證金鑰輪轉,並且不介意操作兩次叢集配置,可以按以下步驟操作。
(1) 生成一個新金鑰。
(2) 將新的金鑰替換掉只用於解密的老金鑰,重啟各個節點;載入配置,使所有節點都只使用新金鑰。
(3) 將兩個金鑰交換位置,新金鑰作為加解密的金鑰,之前的金鑰作為只解密的老金鑰。
可以從容的依次重啟各個節點,因為所有節點在第一次配置中已經載入了新金鑰,所以可以正常解密由新金鑰加密的票據,不會有任何時間差帶來的問題。
