letsencrypt證書-使用certbot申請wildcard證書
目錄
- 1. certbot安裝
- 2. 認證方式
- 3. 運行命令
- 4. 更新
- 1:下載
- 2:配置
- 3:申請證書
- 4:續期證書
1. certbot安裝
cd /usr/local/src
wget https://dl.eff.org/certbot-auto
chmod a+x certbot-auto2. 認證方式
客戶在申請 Let’s Encrypt 證書的時候,需要校驗域名的所有權,證明操作者有權利為該域名申請證書,目前支持三種驗證方式:
dns-01:給域名添加一個 DNS TXT 記錄。 http-01:在域名對應的 Web 服務器下放置一個 HTTP well-known URL 資源文件。 tls-sni-01:在域名對應的 Web 服務器下放置一個 HTTPS well-known URL 資源文件。
3. 運行命令
./certbot-auto certonly -d *.archerwong.cn -d archerwong.cn --manual --preferred-challenges dns --server https://acme-v02.api.letsencrypt.org/directory 註意這裏 -d archerwong.cn 最好寫上,否則archerwong.cn將無法被信任,只有xxx.archerwong.cn這樣的二級 域名才被信任
介紹下相關參數:
certonly,表示安裝模式,Certbot 有安裝模式和驗證模式兩種類型的插件。 --manual 表示手動安裝插件,Certbot 有很多插件,不同的插件都可以申請證書,用戶可以根據需要自行選擇 -d 為那些主機申請證書,如果是通配符,輸入 *.newyingyong.cn(可以替換為你自己的域名) --preferred-challenges dns,使用 DNS 方式校驗域名所有權 --server,Let's Encrypt ACME v2 版本使用的服務器不同於 v1 版本,需要顯示指定。
交互界面如下
[root@host src]# sudo ./certbot-auto certonly -d *.archerwong.cn -d archerwong.cn --manual --preferred-challenges dns --server https://acme-v02.api.letsencrypt.org/directory Saving debug log to /var/log/letsencrypt/letsencrypt.log Plugins selected: Authenticator manual, Installer None Enter email address (used for urgent renewal and security notices) (Enter 'c' to cancel): [email protected] - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - Please read the Terms of Service at https://letsencrypt.org/documents/LE-SA-v1.2-November-15-2017.pdf. You must agree in order to register with the ACME server at https://acme-v02.api.letsencrypt.org/directory - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - (A)gree/(C)ancel: A - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - Would you be willing to share your email address with the Electronic Frontier Foundation, a founding partner of the Let's Encrypt project and the non-profit organization that develops Certbot? We'd like to send you email about our work encrypting the web, EFF news, campaigns, and ways to support digital freedom. - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - (Y)es/(N)o: Y Obtaining a new certificate Performing the following challenges: dns-01 challenge for archerwong.cn - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - NOTE: The IP of this machine will be publicly logged as having requested this certificate. If you're running certbot in manual mode on a machine that is not your server, please ensure you're okay with that. Are you OK with your IP being logged? - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - (Y)es/(N)o: (Y)es/(N)o: Y - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - Please deploy a DNS TXT record under the name _acme-challenge.archerwong.cn with the following value: apQPzp-NYZ0md_D_2_fKr465Il3dDbdR_BlOSOJTYAo Before continuing, verify the record is deployed. - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - Press Enter to Continue
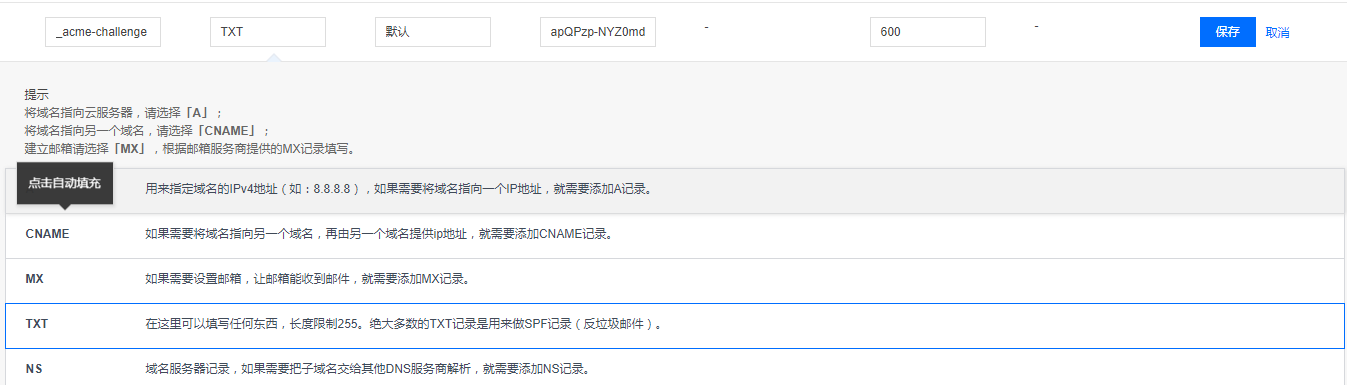
註意這裏我把交互頁面截斷,很重要,先不要回車,將上面的txt值,填到你的域名解析裏面,等確認生效後再回車,我填寫如下
然後測試是否生效
$ dig -t txt _acme-challenge.archerwong.cn @8.8.8.8
; <<>> DiG 9.9.4-RedHat-9.9.4-51.el7_4.1 <<>> -t txt _acme-challenge.archerwong.cn @8.8.8.8
;; global options: +cmd
;; Got answer:
;; ->>HEADER<<- opcode: QUERY, status: NOERROR, id: 25704
;; flags: qr rd ra; QUERY: 1, ANSWER: 1, AUTHORITY: 0, ADDITIONAL: 1
;; OPT PSEUDOSECTION:
; EDNS: version: 0, flags:; udp: 512
;; QUESTION SECTION:
;_acme-challenge.archerwong.cn. IN TXT
;; ANSWER SECTION:
_acme-challenge.archerwong.cn. 599 IN TXT "apQPzp-NYZ0md_D_2_fKZ465Il3dDbdR_BlOSOJTYbo"
;; Query time: 306 msec
;; SERVER: 8.8.8.8#53(8.8.8.8)
;; WHEN: Mon Dec 17 21:34:43 CST 2018
;; MSG SIZE rcvd: 114
確認生效後,按回車鍵,交互界面繼續
Waiting for verification...
Cleaning up challenges
IMPORTANT NOTES:
- Congratulations! Your certificate and chain have been saved at:
/etc/letsencrypt/live/archerwong.cn/fullchain.pem
Your key file has been saved at:
/etc/letsencrypt/live/archerwong.cn/privkey.pem
Your cert will expire on 2019-03-17. To obtain a new or tweaked
version of this certificate in the future, simply run certbot-auto
again. To non-interactively renew *all* of your certificates, run
"certbot-auto renew"
- If you like Certbot, please consider supporting our work by:
Donating to ISRG / Let's Encrypt: https://letsencrypt.org/donate
Donating to EFF: https://eff.org/donate-le至此已經成功生成了wildcard證書,查看下證書
tree /etc/letsencrypt/live/archerwong.cn
/etc/letsencrypt/live/archerwong.cn
├── cert.pem -> ../../archive/archerwong.cn/cert1.pem
├── chain.pem -> ../../archive/archerwong.cn/chain1.pem
├── fullchain.pem -> ../../archive/archerwong.cn/fullchain1.pem
├── privkey.pem -> ../../archive/archerwong.cn/privkey1.pem
└── README生成證書後,配置 Nginx
打開 nginx server 配置文件加入如下設置:
server {
listen 443
ssl on;
ssl_certificate /etc/letsencrypt/live/網站域名/fullchain.pem;
ssl_certificate_key /etc/letsencrypt/live/網站域名/privkey.pem;
## 其他配置
}強制跳轉 https
https 默認是監聽 443 端口的,沒開啟 https 訪問的話一般默認是 80 端口。如果你確定網站 80 端口上的站點都支持 https 的話加入下面的配件可以自動重定向到 https
server {
listen 80;
server_name your.domain.com;
return 301 https://$server_name$request_uri;
}4. 更新
使用的庫:letsencrypt通配符證書,其實這個庫就是寫了一個鉤子,通過鉤子來自動填寫txt dns記錄。當然這個庫也可以方便的申請通配符證書,感謝作者的付出。
1:下載
$ git clone https://github.com/ywdblog/certbot-letencrypt-wildcardcertificates-alydns-au
$ cd certbot-letencrypt-wildcardcertificates-alydns-au
$ chmod 0777 au.sh autxy.sh python-version/au.sh
// 我是移動到了/etc/letsencrypt目錄下,然後重命名manual-auth-hook2:配置
目前該工具支持三種運行環境:
- au.sh:操作阿裏雲 DNS hook shell(PHP 環境)。
- autxy.sh:操作騰訊雲 DNS hook shell(PHP 環境)。
- python-version/au.py:操作阿裏雲 DNS hook shell(Python 2.7/3.6),感謝 @Duke-Wu 的 PR。
這三種運行環境什麽意思呢?就是可根據自己服務器環境和域名服務商選擇任意一個 hook shell(操作的時候任選其一即可)。
DNS API 密鑰:
- alydns.php,修改 accessKeyId、accessSecrec 變量,阿裏雲 API key 和 Secrec 官方申請文檔。
- txydns.php,修改 txyaccessKeyId、txyaccessSecrec 變量,騰訊雲 API 密鑰官方申請文檔。
- python-version/alydns27.py,修改 ACCESS_KEY_ID、ACCESS_KEY_SECRET,阿裏雲 API key 和 Secrec 官方申請文檔。
- 這個 API 密鑰什麽意思呢?由於需要通過 API 操作阿裏雲 DNS 或騰訊雲 DNS 的記錄,所以需要去域名服務商哪兒獲取 API 密鑰。
3:申請證書
特別說明: --manual-auth-hook 指定的 hook 文件三個任選其一(au.sh、autxy.sh、python-version/au.sh),其他操作完全相同。
測試是否有錯誤
$ ./certbot-auto certonly -d *.example.com --manual --preferred-challenges dns --manual-auth-hook /腳本目錄/au.sh(autxy.sh 或 python-version/27.py,下面統一以 au.sh 介紹) --dry-run
# 實際申請
$ ./certbot-auto certonly -d *.example.com --manual --preferred-challenges dns --manual-auth-hook /腳本目錄/au.sh 這裏我實際運行了測試
[root@host src]# ./certbot-auto certonly -d *.archerwong.cn --manual --preferred-challenges dns --manual-auth-hook /etc/letsencrypt/manual-auth-hook/autxy.sh --dry-run
Saving debug log to /var/log/letsencrypt/letsencrypt.log
Plugins selected: Authenticator manual, Installer None
Obtaining a new certificate
Performing the following challenges:
dns-01 challenge for archerwong.cn
- - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - -
NOTE: The IP of this machine will be publicly logged as having requested this
certificate. If you're running certbot in manual mode on a machine that is not
your server, please ensure you're okay with that.
Are you OK with your IP being logged?
- - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - -
(Y)es/(N)o: y
Output from autxy.sh:
/etc/letsencrypt/manual-auth-hook/alydns.php
archerwong.cn_acme-challengevnc1ol1jxXcQnX8ggc40-HFXPdca7xTzhDZRDKzHla8
END
Waiting for verification...
Cleaning up challenges
IMPORTANT NOTES:
- The dry run was successful.4:續期證書
1、對機器上所有證書 renew
$ ./certbot-auto renew --manual --preferred-challenges dns --manual-auth-hook /腳本目錄/au.sh 實際更新下,結果如下
[root@host src]# ./certbot-auto renew --manual --preferred-challenges dns --manual-auth-hook /etc/letsencrypt/manual-auth-hook/autxy.sh
Saving debug log to /var/log/letsencrypt/letsencrypt.log
- - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - -
Processing /etc/letsencrypt/renewal/archerwong.cn.conf
- - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - -
Cert not yet due for renewal
- - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - -
The following certs are not due for renewal yet:
/etc/letsencrypt/live/archerwong.cn/fullchain.pem expires on 2019-03-18 (skipped)
No renewals were attempted.
- - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - -
[root@host src]# ./certbot-auto renew --manual --preferred-challenges dns --manual-auth-hook /etc/letsencrypt/manual-auth-hook/autxy.sh --force-renewal
Saving debug log to /var/log/letsencrypt/letsencrypt.log
- - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - -
Processing /etc/letsencrypt/renewal/archerwong.cn.conf
- - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - -
Plugins selected: Authenticator manual, Installer None
Renewing an existing certificate
Performing the following challenges:
dns-01 challenge for archerwong.cn
dns-01 challenge for archerwong.cn
Output from autxy.sh:
/etc/letsencrypt/manual-auth-hook/alydns.php
archerwong.cn_acme-challengeapQPzp-NYaZfafamd_D_2_fKr46fafafaR_BlOSOJTYAo
END
Output from autxy.sh:
/etc/letsencrypt/manual-auth-hook/alydns.php
archerwong.cn_acme-challengeNnS-4PfafavlFuvgm1vjzfafafaD5Ux_JfQoohs
END
Waiting for verification...
Cleaning up challenges
- - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - -
new certificate deployed without reload, fullchain is
/etc/letsencrypt/live/archerwong.cn/fullchain.pem
- - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - -
- - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - -
Congratulations, all renewals succeeded. The following certs have been renewed:
/etc/letsencrypt/live/archerwong.cn/fullchain.pem (success)
- - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - -2、對某一張證書進行續期
先看看機器上有多少證書:
$ ./certbot-auto certificates
Saving debug log to /var/log/letsencrypt/letsencrypt.log
- - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - -
Found the following certs:
Certificate Name: archerwong.cn-0001
Domains: *.archerwong.cn archerwong.cn
Expiry Date: 2019-03-17 13:24:57+00:00 (VALID: 89 days)
Certificate Path: /etc/letsencrypt/live/archerwong.cn-0001/fullchain.pem
Private Key Path: /etc/letsencrypt/live/archerwong.cn-0001/privkey.pem
Certificate Name: test.archerwong.cn-0001
Domains: test.archerwong.cn
Expiry Date: 2019-03-18 05:36:23+00:00 (INVALID: TEST_CERT)
Certificate Path: /etc/letsencrypt/live/test.archerwong.cn-0001/fullchain.pem
Private Key Path: /etc/letsencrypt/live/test.archerwong.cn-0001/privkey.pem
Certificate Name: archerwong.cn
Domains: *.archerwong.cn
Expiry Date: 2019-03-17 12:34:52+00:00 (VALID: 89 days)
Certificate Path: /etc/letsencrypt/live/archerwong.cn/fullchain.pem
Private Key Path: /etc/letsencrypt/live/archerwong.cn/privkey.pem記住證書名,比如 archerwong.cn,然後運行下列命令 renew:
$ ./certbot-auto renew --cert-name archerwong.cn --manual-auth-hook /腳本目錄/au.sh 3、加入 crontab
編輯文件 /etc/crontab :
1 1 */1 * * root certbot-auto renew --manual --preferred-challenges dns --manual-auth-hook /腳本目錄/au.sh 上面的意思是,每隔一天的一點一分運行一次腳本
crontab的文件格式
分 時 日 月 星期 要運行的命令
- 第1列分鐘0~59
- 第2列小時0~23(0表示子夜)
- 第3列日1~31
- 第4列月1~12
- 第5列星期0~7(0和7表示星期天)
- 第6列要運行的命令
參考:
https://www.jianshu.com/p/c5c9d071e395
https://github.com/ywdblog/certbot-letencrypt-wildcardcertificates-alydns-au
letsencrypt證書-使用certbot申請wildcard證書
