淺析Juniper IPsec VPN中的traffic selector
Juniper的IPSec VPN中的traffic selector(流量篩選器)主要用於多Proxy-ID的情況下,而且是在基於路由的VPN中才會用到。首先Proxy-ID在協商階段2的時候會被校驗,如果校驗失敗會導致第二階段IPsec VPN建立不起來。預設情況下,基於路由的IPsec的Proxy-ID是從安全策略中的源地址和目的地址提取出來的。如src.addr=192.168.1.0/24, dst.addr=192.168.2.0/24,則local proxy-id為192.168.1.0/24,remote proxy-id為192.168.2.0/24,源策略中包含的源或者目的地址為2個及以上個地址時,相應的proxy-id就會被0.0.0.0/0替代。
對於基於路由的IPsec VPN,local和remote proxy-id均為0.0.0.0/0。Proxy-ID只能有1個組合,而traffic selector卻可以有多組,以實現與其它廠家多proxy-id的VPN進行對接。
下面就以3組traffic selector的情況進行解析。
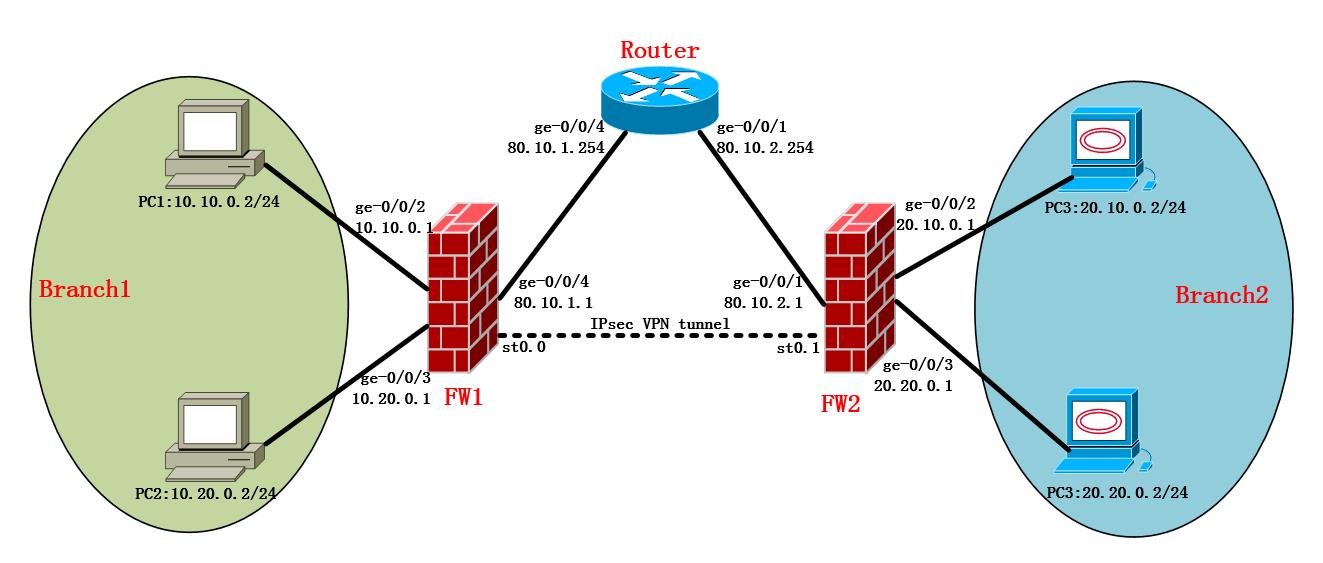
Branch1有2個網段10.10.0.0/24與10.20.0.0/24,Branch2也有2個網段:20.10.0.0/24,20.20.0.0/24,兩個辦公室通過Juniper SRX系列的防火牆配置Site-to-Site VPN打通,部署模式為main的IPsec VPN,繫結tunnel介面。如果是基於路由這種,直接配置靜態路由互相指對端網段的下一跳到tunnel介面是可以通的。這裡我們主要來驗證下traffic selector的用途,就刪除了靜態路由,配置traffic selector來實現兩邊互通。
本次demo通過配置traffic selector來實現10.10.0.0/24可以訪問20.10.0.0/24與20.20.0.0/24,以及10.20.0.0/24可以訪問20.20.0.0/24,但是10.20.0.0/24無法訪問20.10.0.0/24。
基礎網路配置如下:
#FW1介面配置
set security zones security-zone trust interfaces ge-0/0/2.0
set security zones security-zone trust interfaces ge-0/0/3.0
set security zones security-zone untrust interfaces ge-0/0/4.0
set security zones security-zone untrust interfaces st0.1
#FW1區域配置
set security zones security-zone trust host-inbound-traffic system-services all
set security zones security-zone trust host-inbound-traffic protocols all
set security zones security-zone untrust host-inbound-traffic system-services ike
set security zones security-zone untrust host-inbound-traffic system-services ping
#FW1路由配置
set routing-options static route 0.0.0.0/0 next-hop 80.10.1.254
#FW2介面配置
set interfaces ge-0/0/1 unit 0 family inet address 80.10.2.1/24
set interfaces ge-0/0/2 unit 0 family inet address 20.10.0.1/24
set interfaces ge-0/0/3 unit 0 family inet address 20.20.0.1/24
set interfaces st0 unit 0 family inet
#FW2區域配置
set security zones security-zone untrust host-inbound-traffic system-services ping
set security zones security-zone untrust host-inbound-traffic system-services ike
set security zones security-zone trust host-inbound-traffic system-services all
set security zones security-zone trust host-inbound-traffic protocols all
set security zones security-zone trust interfaces ge-0/0/2.0
set security zones security-zone trust interfaces ge-0/0/3.0
set security zones security-zone untrust interfaces ge-0/0/1.0
set security zones security-zone untrust interfaces st0.0
#FW2路由配置
set routing-options static route 0.0.0.0/0 next-hop 80.10.2.254
階段一和階段二的Proposal用的預設的Standard,2臺防火牆都有固定的靜態地址。
階段一配置如下:
FW1#show security ike
policy p1policy {
mode main;
proposal-set standard;
pre-shared-key ascii-text juniper
}
gateway fw2-gw {
ike-policy p1policy;
address 80.10.2.1;
external-interface ge-0/0/4.0;
}
FW2#show security ike
policy p1policy {
mode main;
proposal-set standard;
pre-shared-key ascii-text juniper
}
gateway fw1-gw {
ike-policy p1policy;
address 80.10.1.1;
external-interface ge-0/0/1.0;
}
階段二配置如下:
FW1#show security ipsec
policy p2policy {
proposal-set standard;
}
vpn fw2 {
bind-interface st0.1;
ike {
gateway fw2-gw;
ipsec-policy p2policy;
}
traffic-selector ts1 {
local-ip 10.10.0.0/24;
remote-ip 20.10.0.0/24;
}
traffic-selector ts2 {
local-ip 10.10.0.0/24;
remote-ip 20.20.0.0/24;
}
traffic-selector ts3 {
local-ip 10.20.0.0/24;
remote-ip 20.20.0.0/24;
}
establish-tunnels immediately;
}
FW2#show security ipsec
policy p2policy {
proposal-set standard;
}
vpn fw1 {
bind-interface st0.0;
ike {
gateway fw1-gw;
ipsec-policy p2policy;
}
traffic-selector ts1 {
local-ip 20.10.0.0/24;
remote-ip 10.10.0.0/24;
}
traffic-selector ts2 {
local-ip 20.20.0.0/24;
remote-ip 10.10.0.0/24;
}
traffic-selector ts3 {
local-ip 20.20.0.0/24;
remote-ip 10.20.0.0/24;
}
establish-tunnels immediately;
}
然後在FW上分別開通trust->untrust以及untrust->trust的安全策略,保證2個辦公區之間安全策略是放通的。
測試階段:
1.驗證IKE的SA狀態:2端的IKE SA都是UP的。
FW1> show security ike security-associations
Index State Initiator cookie Responder cookie Mode Remote Address
1787985 UP 2c37aef2870305f9 3d273cc05f9d4900 Main 80.10.2.1
FW2> show security ike security-associations
Index State Initiator cookie Responder cookie Mode Remote Address
4648322 UP 2c37aef2870305f9 3d273cc05f9d4900 Main 80.10.1.1
2.驗證IPsec的SA狀態:2端的IPsec各建立了3個SA用來匹配3個traffic selector
FW1> show security ipsec security-associations
Total active tunnels: 3
ID Algorithm SPI Life:sec/kb Mon lsys Port Gateway
<268173313 ESP:3des/sha1 fc88cb86 2073/ unlim - root 500 80.10.2.1
>268173313 ESP:3des/sha1 d0a32eb6 2073/ unlim - root 500 80.10.2.1
<268173314 ESP:3des/sha1 31048003 2104/ unlim - root 500 80.10.2.1
>268173314 ESP:3des/sha1 e0890688 2104/ unlim - root 500 80.10.2.1
<268173315 ESP:3des/sha1 7fb6e9ff 2077/ unlim - root 500 80.10.2.1
>268173315 ESP:3des/sha1 3888c097 2077/ unlim - root 500 80.10.2.1
FW2> show security ipsec security-associations
Total active tunnels: 3
ID Algorithm SPI Life:sec/kb Mon lsys Port Gateway
<268173313 ESP:3des/sha1 d0a32eb6 2058/ unlim - root 500 80.10.1.1
>268173313 ESP:3des/sha1 fc88cb86 2058/ unlim - root 500 80.10.1.1
<268173314 ESP:3des/sha1 e0890688 2089/ unlim - root 500 80.10.1.1
>268173314 ESP:3des/sha1 31048003 2089/ unlim - root 500 80.10.1.1
<268173315 ESP:3des/sha1 3888c097 2062/ unlim - root 500 80.10.1.1
>268173315 ESP:3des/sha1 7fb6e9ff 2062/ unlim - root 500 80.10.1.1
3.檢查traffic selector對應的IPsec SA:一個traffic selector對應一個IPsec SA。
FW2> show security ipsec security-associations traffic-selector ts1
Total active tunnels: 1
ID Algorithm SPI Life:sec/kb Mon lsys Port Gateway
<268173313 ESP:3des/sha1 d0a32eb6 1968/ unlim - root 500 80.10.1.1
>268173313 ESP:3des/sha1 fc88cb86 1968/ unlim - root 500 80.10.1.1
FW2> show security ipsec security-associations traffic-selector ts2
Total active tunnels: 1
ID Algorithm SPI Life:sec/kb Mon lsys Port Gateway
<268173314 ESP:3des/sha1 e0890688 1997/ unlim - root 500 80.10.1.1
>268173314 ESP:3des/sha1 31048003 1997/ unlim - root 500 80.10.1.1
FW2> show security ipsec security-associations traffic-selector ts3
Total active tunnels: 1
ID Algorithm SPI Life:sec/kb Mon lsys Port Gateway
<268173315 ESP:3des/sha1 3888c097 1968/ unlim - root 500 80.10.1.1
>268173315 ESP:3des/sha1 7fb6e9ff 1968/ unlim - root 500 80.10.1.1
4.檢查路由:發現防火牆通過traffic selector注入了對端的靜態路由,指向tunnel介面
FW1> show route protocol static
20.10.0.0/24 *[Static/5] 01:19:18
> via st0.1
20.20.0.0/24 *[Static/5] 01:19:18
> via st0.1
FW2> show route protocol static10.10.0.0/24 *[Static/5] 01:19:35
> via st0.0
10.20.0.0/24 *[Static/5] 01:19:35
> via st0.0
5.連通性測試:
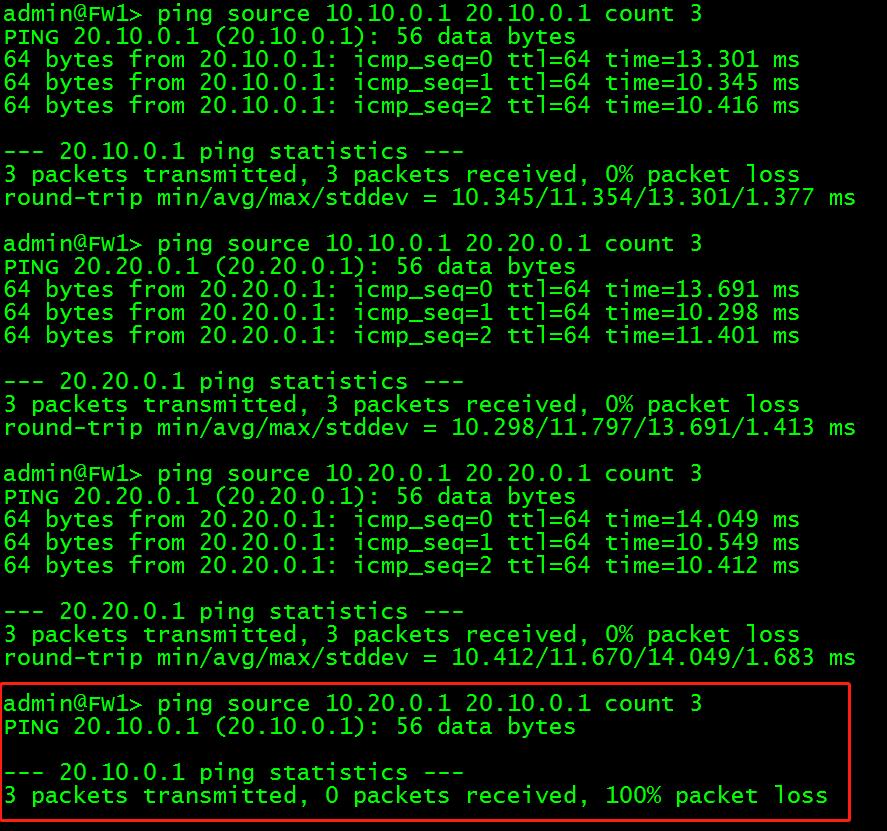
FW1到FW2,10.10.0.1到20.10.0.1與20.20.0.1是通的,10.20.0.1到20.20.0.1是通的,這是3個traffic selector實現的連通性;10.20.0.1到20.10.0.1不通,由於traffic selector未包含這個流量。
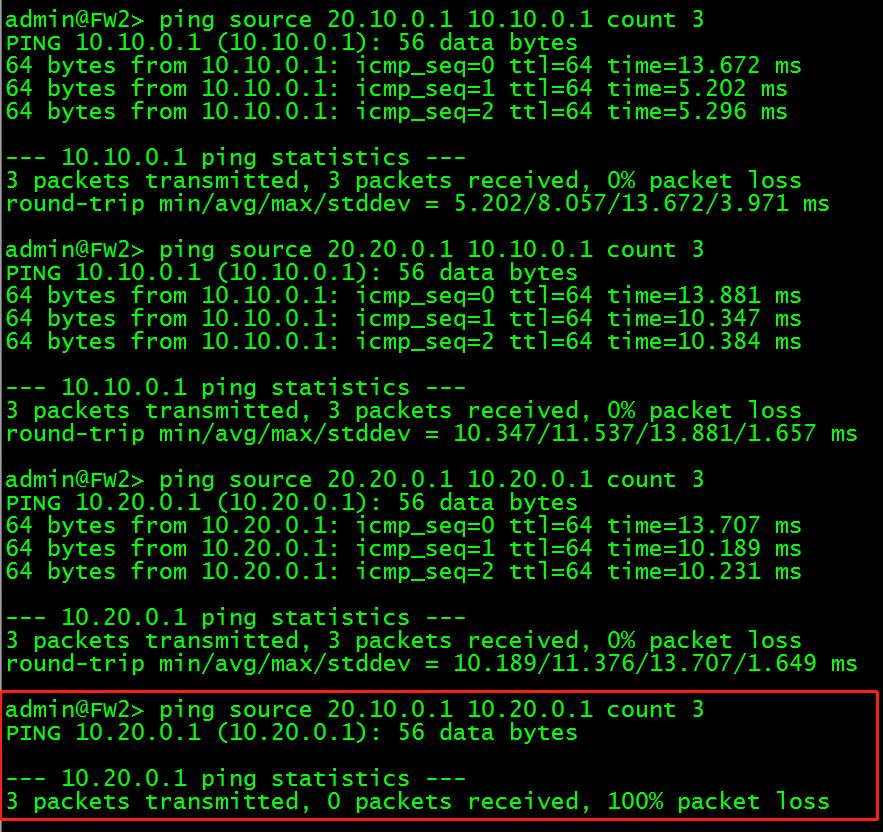
FW2到FW1,20.20.0.1到10.10.0.1與10.20.0.1是通的,20.10.0.1到10.10.0.1是通的,這是3個traffic selector實現的連通性;20.10.0.1到10.20.0.1不通,由於traffic selector未包含這個流量。
總結:經過上述測試,可以說明traffic selector可以實現多個proxy-id互聯的情況,同時traffic selector還可以控制不同網段的連通性。只有匹配到traffic selector的流量才可以正常通訊。