DES演算法原理與Java實現
在上一篇的文章中介紹了Feistel密碼的原理與Java實現,這篇將帶來DES演算法的原理與Java實現,對於Java實現這裡只給出一份程式碼(還有其他方式實現,主要是處理二進位制位的方式不一樣)。
概述
DES是一個分組加密演算法,它以64位為分組對資料加密。同時DES也是一個對稱演算法:加密和解密用的是同一個演算法。DES是一個包含16個階段的“替換–置換”的分組加密演算法,64位的分組明文序列作為加密演算法的輸入,經過16輪加密得到64位的密文序列。
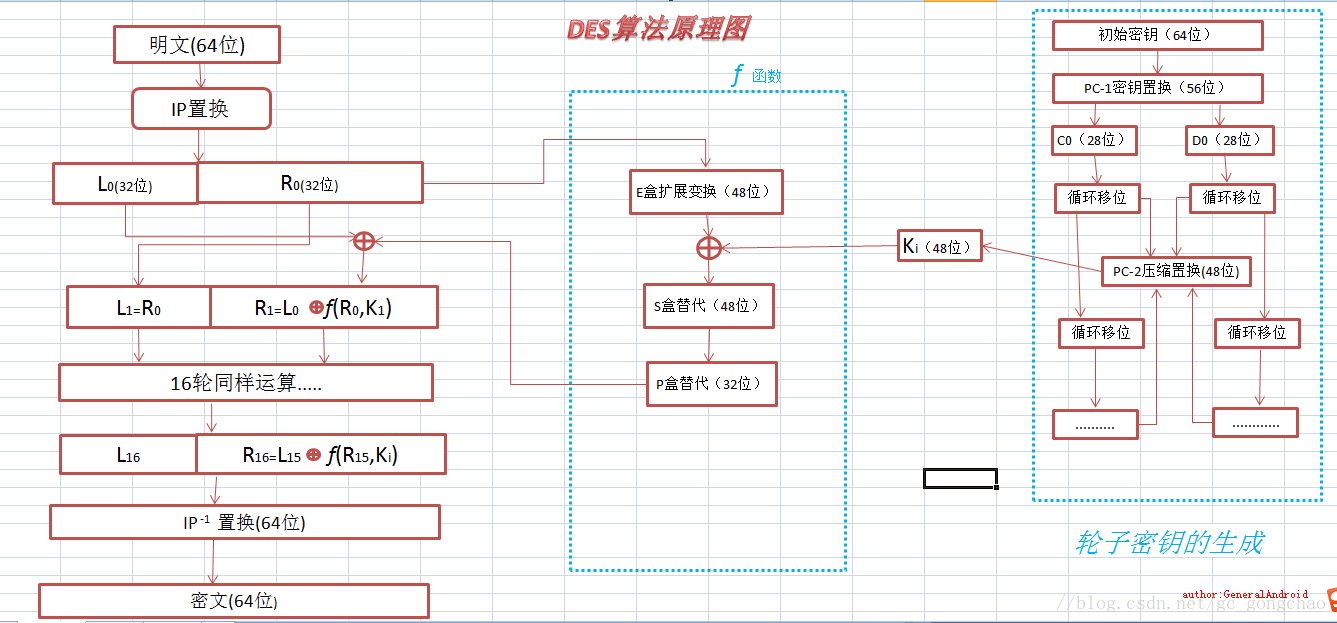
理論的概述總是枯燥的,而且也不好描述,直接上圖,演算法原理看下圖:
原理淺析
DES演算法主要分為3部分:加解密運算、f函式的處理、輪子金鑰的生成,從右往左分別簡單介紹一下。
輪子金鑰的生成
資料表1
//PC-1
private int[] PC1={57,49,41,33,25,17,9,
1,58,50,42,34,26,18,
10,2,59,51,43,35,27,
19,11,3,60,52,44,36,
63,55,47,39,31,23,15,
7,62,54,46,38,30,22,
14 16個子金鑰的生成主要是利用了資料表1中的數表,首先將64位的初始金鑰利用PC1壓縮置換位56位的金鑰,然後將其一分為二,這裡記為C0和D0。這裡28位的C0和28位的D0分別根據LET陣列相應位置的值進行左移位得到C1和D1。這是將C1和D1合併根據PC2進行壓縮置換得到48位的子金鑰,而且注意C1和D1作為下輪的輸入以用來產生下一個子金鑰。
f函式的運算
資料表2
//E擴充套件
private int[] E={32,1,2,3,4,5,
4,5,6,7,8,9,
8,9,10,11,12,13,
12,13,14,15,16,17,
16,17,18,19,20,21,
20,21,22,23,24,25,
24,25,26,27,28,29,
28,29,30,31,32,1};
//P置換
private int[] P={16,7,20,21,29,12,28,17,
1,15,23,26,5,18,31,10,
2,8,24,14,32,27,3,9,
19,13,30,6,22,11,4,25};
private static final int[][][] S_Box = {//S-盒
{// S_Box[1]
{ 14, 4, 13, 1, 2, 15, 11, 8, 3, 10, 6, 12, 5, 9, 0, 7 },
{ 0, 15, 7, 4, 14, 2, 13, 1, 10, 6, 12, 11, 9, 5, 3, 8 },
{ 4, 1, 14, 8, 13, 6, 2, 11, 15, 12, 9, 7, 3, 10, 5, 0 },
{ 15, 12, 8, 2, 4, 9, 1, 7, 5, 11, 3, 14, 10, 0, 6, 13 } },
{ // S_Box[2]
{ 15, 1, 8, 14, 6, 11, 3, 4, 9, 7, 2, 13, 12, 0, 5, 10 },
{ 3, 13, 4, 7, 15, 2, 8, 14, 12, 0, 1, 10, 6, 9, 11, 5 },
{ 0, 14, 7, 11, 10, 4, 13, 1, 5, 8, 12, 6, 9, 3, 2, 15 },
{ 13, 8, 10, 1, 3, 15, 4, 2, 11, 6, 7, 12, 0, 5, 14, 9 } },
{ // S_Box[3]
{ 10, 0, 9, 14, 6, 3, 15, 5, 1, 13, 12, 7, 11, 4, 2, 8 },
{ 13, 7, 0, 9, 3, 4, 6, 10, 2, 8, 5, 14, 12, 11, 15, 1 },
{ 13, 6, 4, 9, 8, 15, 3, 0, 11, 1, 2, 12, 5, 10, 14, 7 },
{ 1, 10, 13, 0, 6, 9, 8, 7, 4, 15, 14, 3, 11, 5, 2, 12 } },
{ // S_Box[4]
{ 7, 13, 14, 3, 0, 6, 9, 10, 1, 2, 8, 5, 11, 12, 4, 15 },
{ 13, 8, 11, 5, 6, 15, 0, 3, 4, 7, 2, 12, 1, 10, 14, 9 },
{ 10, 6, 9, 0, 12, 11, 7, 13, 15, 1, 3, 14, 5, 2, 8, 4 },
{ 3, 15, 0, 6, 10, 1, 13, 8, 9, 4, 5, 11, 12, 7, 2, 14 } },
{ // S_Box[5]
{ 2, 12, 4, 1, 7, 10, 11, 6, 8, 5, 3, 15, 13, 0, 14, 9 },
{ 14, 11, 2, 12, 4, 7, 13, 1, 5, 0, 15, 10, 3, 9, 8, 6 },
{ 4, 2, 1, 11, 10, 13, 7, 8, 15, 9, 12, 5, 6, 3, 0, 14 },
{ 11, 8, 12, 7, 1, 14, 2, 13, 6, 15, 0, 9, 10, 4, 5, 3 } },
{ // S_Box[6]
{ 12, 1, 10, 15, 9, 2, 6, 8, 0, 13, 3, 4, 14, 7, 5, 11 },
{ 10, 15, 4, 2, 7, 12, 9, 5, 6, 1, 13, 14, 0, 11, 3, 8 },
{ 9, 14, 15, 5, 2, 8, 12, 3, 7, 0, 4, 10, 1, 13, 11, 6 },
{ 4, 3, 2, 12, 9, 5, 15, 10, 11, 14, 1, 7, 6, 0, 8, 13 } },
{ // S_Box[7]
{ 4, 11, 2, 14, 15, 0, 8, 13, 3, 12, 9, 7, 5, 10, 6, 1 },
{ 13, 0, 11, 7, 4, 9, 1, 10, 14, 3, 5, 12, 2, 15, 8, 6 },
{ 1, 4, 11, 13, 12, 3, 7, 14, 10, 15, 6, 8, 0, 5, 9, 2 },
{ 6, 11, 13, 8, 1, 4, 10, 7, 9, 5, 0, 15, 14, 2, 3, 12 } },
{ // S_Box[8]
{ 13, 2, 8, 4, 6, 15, 11, 1, 10, 9, 3, 14, 5, 0, 12, 7 },
{ 1, 15, 13, 8, 10, 3, 7, 4, 12, 5, 6, 11, 0, 14, 9, 2 },
{ 7, 11, 4, 1, 9, 12, 14, 2, 0, 6, 10, 13, 15, 3, 5, 8 },
{ 2, 1, 14, 7, 4, 10, 8, 13, 15, 12, 9, 0, 3, 5, 6, 11 } }
};從原理圖中可以看到,f函式的輸入是明文分組的右半分組記為R和子金鑰記為K。32位的R首先要利用資料表2中的E進行E盒擴充套件變換得到48位的資料,這裡記為RE。然後將RE與K進行異或運算並將異或結果利用資料表2中的S_BOX進行S盒替換,得到48位的運算結果記為RS。再將RS利用資料表2中的P進行P盒替換,得到32位的最終結果,記為RF。到這裡f函式的運算任務就完成了。
加解密運算
//初始置換
private int[] IP={58,50,42,34,26,18,10,2,
60,52,44,36,28,20,12,4,
62,54,46,38,30,22,14,6,
64,56,48,40,32,24,16,8,
57,49,41,33,25,17,9,1,
59,51,43,35,27,19,11,3,
61,53,45,37,29,21,13,5,
63,55,47,39,31,23,15,7};
//逆初始置換
private int[] IP_1={40,8,48,16,56,24,64,32,
39,7,47,15,55,23,63,31,
38,6,46,14,54,22,62,30,
37,5,45,13,53,21,61,29,
36,4,44,12,52,20,60,28,
35,3,43,11,51,19,59,27,
34,2,42,10,50,18,58,26,
33,1,41,9,49,17,57,25};關於IP和IP-1 的置換運算就不說了,我只要說一下一輪的加密過程,在第一輪中將64位的明文分為L0和R0,則加密運算如下:
L1=R0
R1=L0⊕f(R0,K0)
然後按此公式進行16輪的運算。
程式碼實現
package com.general.encryanddecode;
import org.omg.PortableInterceptor.SYSTEM_EXCEPTION;
import java.util.Arrays;
/**
* @author generalandroid
*
* 根據DES演算法原理實現DES加密演算法,主要是為了更加深入地理解DES演算法
* **/
public class CustomDES {
//初始置換
private int[] IP={58,50,42,34,26,18,10,2,
60,52,44,36,28,20,12,4,
62,54,46,38,30,22,14,6,
64,56,48,40,32,24,16,8,
57,49,41,33,25,17,9,1,
59,51,43,35,27,19,11,3,
61,53,45,37,29,21,13,5,
63,55,47,39,31,23,15,7};
//逆初始置換
private int[] IP_1={40,8,48,16,56,24,64,32,
39,7,47,15,55,23,63,31,
38,6,46,14,54,22,62,30,
37,5,45,13,53,21,61,29,
36,4,44,12,52,20,60,28,
35,3,43,11,51,19,59,27,
34,2,42,10,50,18,58,26,
33,1,41,9,49,17,57,25};//手殘,陣列資料沒寫全
//E擴充套件
private int[] E={32,1,2,3,4,5,
4,5,6,7,8,9,
8,9,10,11,12,13,
12,13,14,15,16,17,
16,17,18,19,20,21,
20,21,22,23,24,25,
24,25,26,27,28,29,
28,29,30,31,32,1};
//P置換
private int[] P={16,7,20,21,29,12,28,17,
1,15,23,26,5,18,31,10,
2,8,24,14,32,27,3,9,
19,13,30,6,22,11,4,25};
private static final int[][][] S_Box = {
{
{ 14, 4, 13, 1, 2, 15, 11, 8, 3, 10, 6, 12, 5, 9, 0, 7 },
{ 0, 15, 7, 4, 14, 2, 13, 1, 10, 6, 12, 11, 9, 5, 3, 8 },
{ 4, 1, 14, 8, 13, 6, 2, 11, 15, 12, 9, 7, 3, 10, 5, 0 },
{ 15, 12, 8, 2, 4, 9, 1, 7, 5, 11, 3, 14, 10, 0, 6, 13 } },
{
{ 15, 1, 8, 14, 6, 11, 3, 4, 9, 7, 2, 13, 12, 0, 5, 10 },
{ 3, 13, 4, 7, 15, 2, 8, 14, 12, 0, 1, 10, 6, 9, 11, 5 },
{ 0, 14, 7, 11, 10, 4, 13, 1, 5, 8, 12, 6, 9, 3, 2, 15 },
{ 13, 8, 10, 1, 3, 15, 4, 2, 11, 6, 7, 12, 0, 5, 14, 9 } },
{
{ 10, 0, 9, 14, 6, 3, 15, 5, 1, 13, 12, 7, 11, 4, 2, 8 },
{ 13, 7, 0, 9, 3, 4, 6, 10, 2, 8, 5, 14, 12, 11, 15, 1 },
{ 13, 6, 4, 9, 8, 15, 3, 0, 11, 1, 2, 12, 5, 10, 14, 7 },
{ 1, 10, 13, 0, 6, 9, 8, 7, 4, 15, 14, 3, 11, 5, 2, 12 } },
{
{ 7, 13, 14, 3, 0, 6, 9, 10, 1, 2, 8, 5, 11, 12, 4, 15 },
{ 13, 8, 11, 5, 6, 15, 0, 3, 4, 7, 2, 12, 1, 10, 14, 9 },
{ 10, 6, 9, 0, 12, 11, 7, 13, 15, 1, 3, 14, 5, 2, 8, 4 },
{ 3, 15, 0, 6, 10, 1, 13, 8, 9, 4, 5, 11, 12, 7, 2, 14 } },
{
{ 2, 12, 4, 1, 7, 10, 11, 6, 8, 5, 3, 15, 13, 0, 14, 9 },
{ 14, 11, 2, 12, 4, 7, 13, 1, 5, 0, 15, 10, 3, 9, 8, 6 },
{ 4, 2, 1, 11, 10, 13, 7, 8, 15, 9, 12, 5, 6, 3, 0, 14 },
{ 11, 8, 12, 7, 1, 14, 2, 13, 6, 15, 0, 9, 10, 4, 5, 3 } },
{
{ 12, 1, 10, 15, 9, 2, 6, 8, 0, 13, 3, 4, 14, 7, 5, 11 },
{ 10, 15, 4, 2, 7, 12, 9, 5, 6, 1, 13, 14, 0, 11, 3, 8 },
{ 9, 14, 15, 5, 2, 8, 12, 3, 7, 0, 4, 10, 1, 13, 11, 6 },
{ 4, 3, 2, 12, 9, 5, 15, 10, 11, 14, 1, 7, 6, 0, 8, 13 } },
{
{ 4, 11, 2, 14, 15, 0, 8, 13, 3, 12, 9, 7, 5, 10, 6, 1 },
{ 13, 0, 11, 7, 4, 9, 1, 10, 14, 3, 5, 12, 2, 15, 8, 6 },
{ 1, 4, 11, 13, 12, 3, 7, 14, 10, 15, 6, 8, 0, 5, 9, 2 },
{ 6, 11, 13, 8, 1, 4, 10, 7, 9, 5, 0, 15, 14, 2, 3, 12 } },
{
{ 13, 2, 8, 4, 6, 15, 11, 1, 10, 9, 3, 14, 5, 0, 12, 7 },
{ 1, 15, 13, 8, 10, 3, 7, 4, 12, 5, 6, 11, 0, 14, 9, 2 },
{ 7, 11, 4, 1, 9, 12, 14, 2, 0, 6, 10, 13, 15, 3, 5, 8 },
{ 2, 1, 14, 7, 4, 10, 8, 13, 15, 12, 9, 0, 3, 5, 6, 11 } }
};
//PC-1
private int[] PC1={57,49,41,33,25,17,9,
1,58,50,42,34,26,18,
10,2,59,51,43,35,27,
19,11,3,60,52,44,36,
63,55,47,39,31,23,15,
7,62,54,46,38,30,22,
14,6,61,53,45,37,29,
21,13,5,28,20,12,4};
//PC-2
private int[] PC2={14,17,11,24,1,5,3,28,
15,6,21,10,23,19,12,4,
26,8,16,7,27,20,13,2,
41,52,31,37,47,55,30,40,
51,45,33,48,44,49,39,56,
34,53,46,42,50,36,29,32};
//Schedule of Left Shifts
private int[] LFT={1,1,2,2,2,2,2,2,1,2,2,2,2,2,2,1};
/**加密輪數**/
private static final int LOOP_NUM=16;
private String [] keys=new String[LOOP_NUM];
private String [] pContent;
private String [] cContent;
private int origin_length;
/**16個子金鑰**/
private int[][] sub_key=new int[16][48];
private String content;
private int p_origin_length;
public CustomDES(String key,String content){
this.content=content;
p_origin_length=content.getBytes().length;
generateKeys(key);
}
public static void main(String[] args){
String origin="Android將軍->GeneralAndroid->主部落格地址:https://blog.csdn.net/android_jiangjun";
System.out.println("原文:\n"+origin);
CustomDES customDES=new CustomDES("密碼學專欄",origin);
byte[] c=customDES.deal(origin.getBytes(),1);
System.out.println("密文:\n"+new String(c));
byte[]p=customDES.deal(c,0);
byte[] p_d=new byte[origin.getBytes().length];
System.arraycopy(p,0,p_d,0,origin.getBytes().length);
System.out.println("明文:\n"+new String(p));
}
/***程式碼執行結果:
*
原文:
Android將軍->GeneralAndroid->主部落格地址:https://blog.csdn.net/android_jiangjun
密文:
��Lm����=��� 4�zf4�����zj���}���~Dͪn�B��t���Du��U*e�VxC�̃Ynh\@NH ˙P�Ka�1y~4
明文:
Android將軍->GeneralAndroid->主部落格地址:https://blog.csdn.net/android_jiangjun
*
* **/
/****拆分分組****/
public byte[] deal(byte[] p ,int flag){
origin_length=p.length;
int g_num;
int r_num;
g_num=origin_length/8;
r_num=8-(origin_length-g_num*8);//8不填充
byte[] p_padding;
/****填充********/
if (r_num<8){
p_padding=new byte[origin_length+r_num];
System.arraycopy(p,0,p_padding,0,origin_length);
for(int i=0;i<r_num;i++){
p_padding[origin_length+i]=(byte)r_num;
}
}else{
p_padding=p;
}
g_num=p_padding.length/8;
byte[] f_p=new byte[8];
byte[] result_data=new byte[p_padding.length];
for(int i=0;i<g_num;i++){
System.arraycopy(p_padding,i*8,f_p,0,8);
System.arraycopy(descryUnit(f_p,sub_key,flag),0,result_data,i*8,8);
}
if (flag==0){//解密
byte[] p_result_data=new byte[p_origin_length];
System.arraycopy(result_data,0,p_result_data,0,p_origin_length);
return p_result_data;
}
return result_data;
}
/**加密**/
public byte[] descryUnit(byte[] p,int k[][],int flag){
int[] p_bit=new int[64];
StringBuilder stringBuilder=new StringBuilder();
for(int i=0;i<8;i++){
String p_b=Integer.toBinaryString(p[i]&0xff);
while (p_b.length()%8!=0){
p_b="0"+p_b;
}
stringBuilder.append(p_b);
}
String p_str=stringBuilder.toString();
for(int i=0;i<64;i++){
int p_t=Integer.valueOf(p_str.charAt(i));
if(p_t==48){
p_t=0;
}else if(p_t==49){
p_t=1;
}else{
System.out.println("To bit error!");
}
p_bit[i]=p_t;
}
/***IP置換***/
int [] p_IP=new int[64];
for (int i=0;i<64;i++){
p_IP[i]=p_bit[IP[i]-1];
}
if (flag == 1) { // 加密
for (int i = 0; i < 16; i++) {
L(p_IP, i, flag, k[i]);
}
} else if (flag == 0) { // 解密
for (int i = 15; i > -1; i--) {
L(p_IP, i, flag, k[i]);
}
}
int[] c=new int[64];
for(int i=0;i<IP_1.length;i++){
c[i]=p_IP[IP_1[i]-1];
}
byte[] c_byte=new byte[8];
for(int i=0;i<8;i++){
c_byte[i]=(byte) ((c[8*i]<<7)+(c[8*i+1]<<6)+(c[8*i+2]<<5)+(c[8*i+3]<<4)+(c[8*i+4]<<3)+(c[8*i+5]<<2)+(c[8*i+6]<<1)+(c[8*i+7]));
}
return c_byte;
}
public void L(int[] M, int times, int flag, int[] keyarray){
int[] L0=new int[32];
int[] R0=new int[32];
int[] L1=new int[32];
int[] R1=new int[32];
int[] f=new int[32];
System.arraycopy(M,0,L0,0,32);
System.arraycopy(M,32,R0,0,32);
L1=R0;
f=fFuction(R0,keyarray);
for(int j=0;j<32;j++){
R1[j]=L0[j]^f[j];
if (((flag == 0) && (times == 0)) || ((flag == 1) && (times == 15))) {
M[j] = R1[j];
M[j + 32] = L1[j];
}
else {
M[j] = L1[j];
M[j + 32] = R1[j];
}
}
}
public int[] fFuction(int [] r_content,int [] key){
int[] result=new int[32];
int[] e_k=new int[48];
for(int i=0;i<E.length;i++){
e_k[i]=r_content[E[i]-