路由器逆向分析------binwalk工具的詳細使用說明
一、binwalk工具的基本用法介紹
1.獲取幫助資訊
$ binwalk -h
# 或者
$ binwalk --help$ binwalk firmware.bin
# 或者
$ binwalk firmware.bin | head3.提取檔案系統
# 使用預設的預定義配置檔案extract.conf
$ binwalk -e firmware.bin
# 使用指定自定義的配置檔案my_extract.conf
$ binwalk --extract=./my_extract.conf firmware.bin4.設定過濾選項
5.顯示完整的掃描結果
6.韌體檔案的比較
7.日誌記錄
8.指令系統分析
9.熵分析
10.啟發式分析
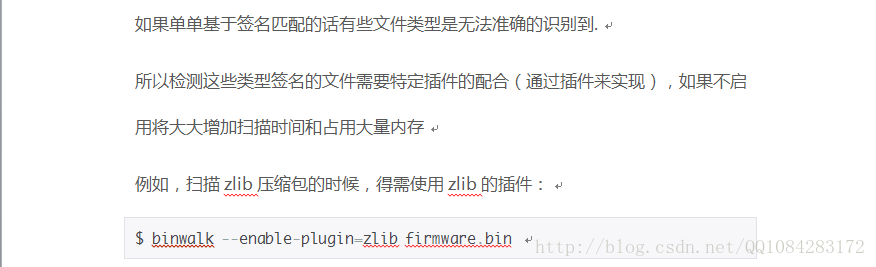
11.使用指定外掛分析掃描韌體(已經去掉)
$ binwalk --enable-plugin=zlib firmware.bin 12.手動提取檔案
-D, --dd=<type[:ext[:cmd]]>
Extracts files identified during a --signature scan. Multiple --dd options may be specified.
- type is a *lower case* string contained in the signature description (regular expressions are supported)
- ext is the file extension to use when saving the data disk (default none)
- cmd is an optional command to execute after the data has been saved to disk
By default, the file name is the hexadecimal offset where the signature was found, unless an alternate file name is specified in the signature itself.
The following example demonstrates specifying an extraction rule using the --dd option that will extract any signature that contains the string 'zip archive' with a file extension of 'zip', and subsequently execute the 'unzip' command. Additionally, PNG images are extracted as-is with a 'png' file extension.
Note the use of the '%e' placeholder. This placeholder will be replaced with the relative path to the extracted file when the unzip command is executed:
$ binwalk -D 'zip archive:zip:unzip %e' -D 'png image:png' firmware.bin
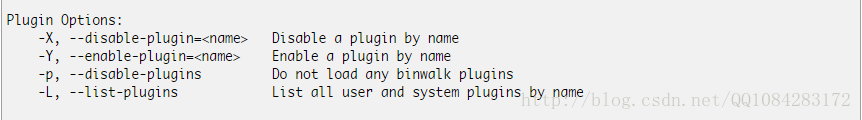
13.binwalk工具的外掛功能
在最新版的binwalk工具中關於外掛的功能已經沒有了,下圖是原來有的外掛功能。
參考資料:
《揭祕家用路由器0day漏洞挖掘技術》
《Binwalk:後門(韌體)分析利器》 錯誤不少,不少功能介紹在最新版的binwalk中已經去掉了。
二、binwalk工具的使用幫助
$ binwalk -hBinwalk v2.1.2b
Craig Heffner, http://www.binwalk.org
Usage: binwalk [OPTIONS] [FILE1] [FILE2] [FILE3] ...
Disassembly Scan Options:
-Y, --disasm Identify the CPU architecture of a file using the capstone disassembler
-T, --minsn=<int> Minimum number of consecutive instructions to be considered valid (default: 500)
-k, --continue Don't stop at the first match
Signature Scan Options:
-B, --signature Scan target file(s) for common file signatures
-R, --raw=<str> Scan target file(s) for the specified sequence of bytes
-A, --opcodes Scan target file(s) for common executable opcode signatures
-m, --magic=<file> Specify a custom magic file to use
-b, --dumb Disable smart signature keywords
-I, --invalid Show results marked as invalid
-x, --exclude=<str> Exclude results that match <str>
-y, --include=<str> Only show results that match <str>
Extraction Options:
-e, --extract Automatically extract known file types
-D, --dd=<type:ext:cmd> Extract <type> signatures, give the files an extension of <ext>, and execute <cmd>
-M, --matryoshka Recursively scan extracted files
-d, --depth=<int> Limit matryoshka recursion depth (default: 8 levels deep)
-C, --directory=<str> Extract files/folders to a custom directory (default: current working directory)
-j, --size=<int> Limit the size of each extracted file
-n, --count=<int> Limit the number of extracted files
-r, --rm Delete carved files after extraction
-z, --carve Carve data from files, but don't execute extraction utilities
Entropy Analysis Options:
-E, --entropy Calculate file entropy
-F, --fast Use faster, but less detailed, entropy analysis
-J, --save Save plot as a PNG
-Q, --nlegend Omit the legend from the entropy plot graph
-N, --nplot Do not generate an entropy plot graph
-H, --high=<float> Set the rising edge entropy trigger threshold (default: 0.95)
-L, --low=<float> Set the falling edge entropy trigger threshold (default: 0.85)
Raw Compression Options:
-X, --deflate Scan for raw deflate compression streams
-Z, --lzma Scan for raw LZMA compression streams
-P, --partial Perform a superficial, but faster, scan
-S, --stop Stop after the first result
Binary Diffing Options:
-W, --hexdump Perform a hexdump / diff of a file or files
-G, --green Only show lines containing bytes that are the same among all files
-i, --red Only show lines containing bytes that are different among all files
-U, --blue Only show lines containing bytes that are different among some files
-w, --terse Diff all files, but only display a hex dump of the first file
General Options:
-l, --length=<int> Number of bytes to scan
-o, --offset=<int> Start scan at this file offset
-O, --base=<int> Add a base address to all printed offsets
-K, --block=<int> Set file block size
-g, --swap=<int> Reverse every n bytes before scanning
-f, --log=<file> Log results to file
-c, --csv Log results to file in CSV format
-t, --term Format output to fit the terminal window
-q, --quiet Suppress output to stdout
-v, --verbose Enable verbose output
-h, --help Show help output
-a, --finclude=<str> Only scan files whose names match this regex
-p, --fexclude=<str> Do not scan files whose names match this regex
-s, --status=<int> Enable the status server on the specified port三、binwalk工具官方的使用幫助說明
-B, --signature
This performs a signature analysis of the specified files; if no other analysis options are specified, this is the default.
Use this option when you wish to combine the signature analysis with additional analyzers, such as--entropy:
$ binwalk --signature firmware.bin DECIMAL HEX DESCRIPTION ------------------------------------------------------------------------------------------------------------------- 0 0x0 DLOB firmware header, boot partition: "dev=/dev/mtdblock/2" 112 0x70 LZMA compressed data, properties: 0x5D, dictionary size: 33554432 bytes, uncompressed size: 3797616 bytes 1310832 0x140070 PackImg section delimiter tag, little endian size: 13644032 bytes; big endian size: 3264512 bytes 1310864 0x140090 Squashfs filesystem, little endian, version 4.0, compression:lzma, size: 3264162 bytes, 1866 inodes, blocksize: 65536 bytes, created: Tue Apr 3 04:12:22 2012
-R, --raw=<string>
This allows you to search the specified file(s) for a custom string. The search string can include escaped octal and/or hexadecimal values.
Use this option when you need to search for a custom sequence of raw bytes:
$ binwalk -R "\x00\x01\x02\x03\x04" firmware.bin
DECIMAL HEX DESCRIPTION
-------------------------------------------------------------------------------------------------------------------
377654 0x5C336 Raw string signature
-A, --opcodes
This instructs binwalk to search the specified file(s) for executable opcodes common to a variety of CPU architectures. Note that some opcode signatures are short and thus are prone to producing false positive results.
Use this when you need to locate executable code in a file, or if you need to determine the architecture of a executable file:
$ binwalk -A firmware.bin DECIMAL HEX DESCRIPTION ------------------------------------------------------------------------------------------------------------------- 268 0x10C MIPS instructions, function prologue 412 0x19C MIPS instructions, function prologue 636 0x27C MIPS instructions, function prologue 812 0x32C MIPS instructions, function epilogue 920 0x398 MIPS instructions, function epilogue 948 0x3B4 MIPS instructions, function prologue 1056 0x420 MIPS instructions, function epilogue 1080 0x438 MIPS instructions, function prologue 1356 0x54C MIPS instructions, function epilogue 1392 0x570 MIPS instructions, function prologue 1836 0x72C MIPS instructions, function epilogue 2012 0x7DC MIPS instructions, function prologue 2260 0x8D4 MIPS instructions, function epilogue 2512 0x9D0 MIPS instructions, function prologue 2552 0x9F8 MIPS instructions, function epilogue
-m, --magic=<file>
Load an alternate magic signature file instead of the default.
Use this if you have a custom magic signature file containing signatures you want to search for:
$ binwalk -m ./foobar.mgc firmware.bin DECIMAL HEX DESCRIPTION ------------------------------------------------------------------------------------------------------------------- 268 0x10C Foobar 412 0x19C Foobar 636 0x27C Foobar
-b, --dumb
Disables "smart" signature matching.
Useful when smart signature keywords in false positive signatures cause other valid signatures to be missed (e.g., via the jump-to-offset keyword):
$ binwalk -b firmware.bin
-I, --invalid
Displays all results, even those marked as invalid.
Useful if you think that binwalk is treating a valid file as invalid, but can produce a lot of garbage output:
$ binwalk -I firmware.bin
-x, --exclude=<filter>
Excludes signatures that match the specified exclude filter. Filters are lower-case regular expressions; multiple filters may be specified.
Magic signatures whose first line matches the specified filter will not be loaded at all; thus, the use of this filter can help decrease signature scan times.
Useful for excluding unneeded or uninteresting results:
$ binwalk -x 'mach-o' -x '^hp' firmware.bin # exclude HP calculator and OSX mach-o signatures
-y, --include=<filter>
Includes only signatures that match the specified include filter. Filters are lower-case regular expressions; multiple filters may be specified.
Only magic signatures whose first line matches the specified filter will be loaded; thus, the use of this filter can help decrease signature scan times.
Useful when searching only for specific signatures or types of signatures:
$ binwalk -y 'filesystem' firmware.bin # only search for filesystem signatures
-Y, --disasm
Attempts to identify the CPU architecture of executable code contained in a file using the capstone disassembler.
Specifying --verbose with this scan will additionally print the disassembled instructions.
Generally more robust than the simple signature analysis performed by --opcodes, but supports fewer architectures:
$ binwalk --disasm firmware.bin DECIMAL HEXADECIMAL DESCRIPTION -------------------------------------------------------------------------------- 428 0x1AC MIPS executable code, 32/64-bit, little endian, at least 750 valid instructions
-T, --minsn
Set the minimum number of consecutive instructions for a --disasm result to be considered valid. The default is 500 instructions:
$ binwalk --minsn=1200 -Y firmware.bin DECIMAL HEXADECIMAL DESCRIPTION -------------------------------------------------------------------------------- 428 0x1AC MIPS executable code, 32/64-bit, little endian, at least 1250 valid instructions
-k, --continue
Instruct --disasm to not stop at the first result:
$ binwalk --continue -Y firmware.bin DECIMAL HEXADECIMAL DESCRIPTION -------------------------------------------------------------------------------- 428 0x1AC MIPS executable code, 32/64-bit, little endian, at least 1250 valid instructions 1048576 0x100000 MIPS executable code, 32/64-bit, little endian, at least 1250 valid instructions ...
-E, --entropy
Performs an entropy analysis on the input file(s), prints raw entropy data and generates entropy graphs.
Entropy analysis can be combined with --signature, --raw, or --opcodes for a better understanding of the target file(s).
Useful for identifying sections of interesting data that a signature scan may have missed:
$ binwalk -E firmware.bin DECIMAL HEXADECIMAL ENTROPY -------------------------------------------------------------------------------- 0 0x0 Rising entropy edge (0.983751) 1155072 0x11A000 Falling entropy edge (0.000000) 1181696 0x120800 Rising entropy edge (0.990546) 3780608 0x39B000 Falling entropy edge (0.000000)
When combined with the --verbose option, the raw entropy calculated for each data block is printed:
$ binwalk -E --verbose firmware.bin DECIMAL HEX ENTROPY ANALYSIS -------------------------------------------------------------------------------- 0 0x0 0.964914 1024 0x400 0.978591 2048 0x800 0.973048 3072 0xC00 0.976195 4096 0x1000 0.976072 5120 0x1400 0.976734 6144 0x1800 0.976861 7168 0x1C00 0.972385 8192 0x2000 0.972518 ...
PYTHON API WARNING: The graphing module used by binwalk (pyqtgraph)
invokes os._exitupon completion; this is apparently necessary to handle various QT issues. When running binwalk from the command line, entropy analysis is always done last, causing little
worry. However, if invoking entropy analysis via the API, be sure to disable graphing (--nplot)
to prevent your script from exiting prematurely.
-J, --save
Automatically saves the entropy plot generated by --entropy to a PNG file instead of displaying it.
$ binwalk --save -E firmware.bin
-Q, --nlegend
Omits the legend from the entropy plot(s) generated by --entropy:
$ binwalk --entropy -Q firmware.bin
-N, --nplot
Disables graphical entropy plots for the --entropy scan.
$ binwalk --entropy -N firmware.bin
-H, --high=<float>
Sets the rising edge entropy trigger level. Only valid when used with --entropy. The specified value should be between 0 and 1:
$ binwalk --entropy -H .9 firmware.bin
-L, --low=<float>
Sets the falling edge entropy trigger level. Only valid when used with --entropy. The specified value should be between 0 and 1:
$ binwalk --entropy -L .3 firmware.bin
-W, --hexdump
Performs a hex dump of the input file(s) and color-codes bytes as follows:
- Green - These bytes were the same in all files
- Red - These bytes were different in all files
- Blue - These bytes were only different in some files
Any arbitrary number of files may be diffed; additional useful options are --block, --offset, --lengthand --terse:
$ binwalk -W --block=8 --length=64 firmware1.bin firmware2.bin firmware3.bin
-G, --green
Only display lines that contain green bytes during a --hexdump:
$ binwalk -W --green firmware1.bin firmware2.bin firmware3.bin
-i, --red
Only display lines that contain red bytes during a --hexdump:
$ binwalk -W --red firmware1.bin firmware2.bin firmware3.bin
-U, --blue
Only display lines that contain blue bytes during a --hexdump:
$ binwalk -W --blue firmware1.bin firmware2.bin firmware3.bin
-w, --terse
When performing a --hexdump, only display a hex dump of the first file.
Useful when diffing many files that don't all fit on the screen:
$ binwalk -W --terse firmware1.bin firmware2.bin firmware3.bin
-e, --extract
Loads common --dd extraction rules from a predefined file.
$ binwalk -e firmware.bin
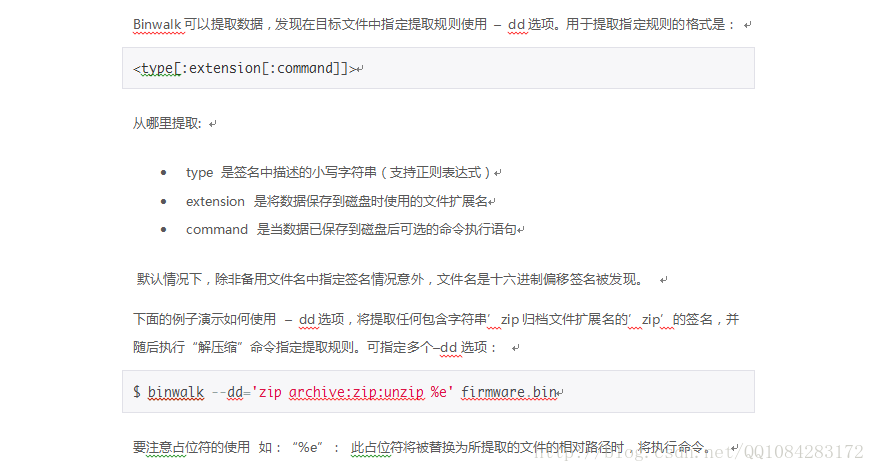
-D, --dd=<type[:ext[:cmd]]>
Extracts files identified during a --signature scan. Multiple --dd options may be specified.
- type is a *lower case* string contained in the signature description (regular expressions are supported)
- ext is the file extension to use when saving the data disk (default none)
- cmd is an optional command to execute after the data has been saved to disk
By default, the file name is the hexadecimal offset where the signature was found, unless an alternate file name is specified in the signature itself.
The following example demonstrates specifying an extraction rule using the --dd option that will extract any signature that contains the string 'zip archive' with a file extension of 'zip', and subsequently execute the 'unzip' command. Additionally, PNG images are extracted as-is with a 'png' file extension.
Note the use of the '%e' placeholder. This placeholder will be replaced with the relative path to the extracted file when the unzip command is executed:
$ binwalk -D 'zip archive:zip:unzip %e' -D 'png image:png' firmware.bin
-M, --matryoshka
This option will recursively scan extracted files during a --signature scan. Only valid when used with--extract or --dd.
$ binwalk -e -M firmware.bin
-C, --directory=<str>
Set the output directory for extracted data (default: current working directory).
Only applicable when used with the --extract or --dd options:
$ binwalk -e --directory=/tmp firmware.bin
-d, --depth=<int>
Limit the --matryoshka recursion depth. By default, the depth is set to 8.
Only applicable when used with the --matryoshka option:
$ binwalk -Me -d 5 firmware.bin
-j, --size=<int>
Limit the size of data carved out of the target file(s). By default, there is no size limit.
Only valid when used with --extract or --dd.
Note that this option does not limit the size of data extracted / decompressed by external extraction utilities.
Useful when carving or extracting data from large files with limited disk space:
$ binwalk -e --size=0x100000 firmware.bin
-r, --rm
Cleans up zero-size files and files that couldn't be processed by extraction utilities during extraction.
Only valid when used with --extract or --dd.
Useful for cleaning up false-positive files copied out of the target file(s) during extraction:
$ binwalk -e -r firmware.bin
-z, --carve
Performs data carving only, does not execute external extraction utilities.
Only valid when used with --extract or --dd.
Useful for when you want to simply carve data from the target file(s), but not automatically extract / decompress that data:
$ binwalk -e --carve firmware.bin
-X, --deflate
Identifies probable raw deflate compressed data streams by brute-force.
Useful for recovering data from files with corrupt/modified/missing headers. May be combined with --lzma.
This scan can be slow, so it is useful to limit the scanned area with --offset and/or --length:
$ binwalk --deflate -o 0x100 -l 10000 firmware.bin
-Z, --lzma
Identifies probable raw LZMA compressed data streams by brute-force.
Useful for recovering data from files with corrupt/modified/missing headers. May be combined with --deflate.
Due to the various number of LZMA compression options this scan can be very slow, so it is useful to limit the scanned area with --offset and/or --length:
$ binwalk --lzma -o 0x100 -l 10000 firmware.bin
-P, --partial
Only search for compression streams using common compression options. Can significantly improve the speed of --lzma scans:
$ binwalk --partial -Z -o 0x100 -l 10000 firmware.bin
-S, --stop
When used with the --lzma and/or --deflate options, this will stop the scan after the first result is displayed:
$ binwalk --stop -Z firmware.bin
-l, --length=<int>
Sets the number of bytes to analyze in a target file:
$ binwalk --length=0x100 firmware.bin
-o, --offset=<int>
Sets the starting offset at which to begin analyzing a target file. A negative offset (distance from End-Of-File) may also be specified:
$ binwalk --offset=0x100 firmware.bin
-O, --base=<int>
Sets the base address for all printed offsets. This value will be added to the raw file offset of all printed results:
$ binwalk --base=0x80001000 firmware.bin
相關推薦
路由器逆向分析------binwalk工具的詳細使用說明
一、binwalk工具的基本用法介紹
1.獲取幫助資訊
$ binwalk -h
# 或者
$ binwalk --help
2.韌體分析掃描
$ binwalk firmware.bin
# 或者
$ binwalk firmware.bin | head
路由器逆向分析------binwalk工具的安裝
一、binwalk工具執行支援的平臺
Operating System
Core Support
Optional Feature Support
Ease of Installation
Linux
Excellent
Excellent
Very easy
O
路由器逆向分析------sasquatch和squashfs-tools工具的安裝和使用
一、sasquatch工具的安裝和使用
sasquatch工具支援對
非標準的SquashFS格式的檔案映象 進行解壓並且sasquatch工具也binwalk工具整合的一個功能元件之一。最新版的sasquatch工具是基於squashfs 4.3的原始碼修改而來的
路由器逆向分析------firmware-mod-kit工具安裝和使用說明
一、firmware-mod-kit工具的安裝
firmware-mod-kit工具的功能和binwalk工具的類似,其實firmware-mod-kit工具在功能上有呼叫binwalk工具提供的功能以及其他的韌體解包工具的整合。下載firmware-mod-kit工
路由器逆向分析------MIPS交叉編譯環境的搭建(Buildroot)
為了能在我們熟悉的windows或者ubuntu下開發mips架構的程式,需要搭建mips程式的交叉編譯環境。mips程式的交叉編譯環境的構建需要用編譯Buildroot,Buildroot在編譯的過程中,會下載一些依賴包,所以在Buildroot的編譯安裝過程中必須確
路由器逆向分析------在Linux上安裝IDA Pro
Installing WineHQ packages
If you have previously installed a Wine package from another repository, please remove it and any packages that depend on it (
路由器逆向分析------QEMU的基本使用方法(MIPS)
一、QEMU的執行模式
直接摘抄自己《揭祕家用路由器0day漏洞挖掘技術》,網上查了一下也沒有找到令人滿意的QEMU的使用說明,就採用這本書上的介紹。如果後期能夠找到比較滿意的QEMU的使用方法的說明,再新增上來。
QEMU模擬器主要有兩種比較常見的運作模式:Use
記錄金盾加密視訊提取工具被逆向分析過程一
金盾2018SS加密視訊機器碼替換工具的分析過程三
上篇講替換機器碼工具的分析,本次繼續分析同一個包裡帶的視訊提取工具。看圖: 工具使用過程:這裡的WIN7.DLL是主要檔案,我們結合前面分析的,替換機器碼後,在把該DLL注入到播放器內,輸入密碼後,視訊就開始播放了,並在D盤根目錄下生成了一個AV
Andorid逆向-3.IDA工具介紹-靜態分析
IDA安裝就不說了,簡單無腦下一步啪啪就好了( ̄▽ ̄)
1.個人理解:不明白地方,多點幾次就明白意思了
2.這個就是點了Go出現的介面
3.拖拽需要反編譯的檔案,我是小學生英文暫時都看不懂。然後直接點OK
4.簡單介紹下
5. 視窗簡單應用
如何檢視檔
C# & dnspy 使用總結--逆向分析工具
dnspy工具: 非常優秀的C#的反編譯器
一、除錯
1.1 載入模組: 直接將exe或者dll,拖到dnspy中即可。或者 開啟exe,執行起來就會,相關的模組會自動載入進來。
1.2
c&c++反彙編與逆向分析學習筆記(2)--反彙編靜態分析工具IDA
所謂“靜態分析”,是相對於前面提到的“動態分析”而言的。在“動態分析”過程中,偵錯程式載入程式,並以除錯模式執行起來,分析者可以在程式的執行過程中觀察程式的執行流程和計算記過。但是,在實際分析中,很多場合不方便執行目標,比如軟體的某一模組(無法單獨執行)、病
逆向分析涉及的工具及OD快捷鍵
1.逆向工程的工具有哪些?
①16 進位制工具:010Editor,winhex
②PE 工具:PEID,LordPE,
③除錯工具:OD , IDA Pro, windbg
④ARK 工具:pchunter
⑤系統監控工具:火絨劍
⑥資料包分析工具(抓包工具):
Tcp/udp: WireS
Android逆向分析初體驗
目錄 搜索 比較 .com -1 動態調試 總結 為我 修改 一、 準備知識
1. 懂Java Android開發。
2. 懂NDK ,C 語言 Android 動態鏈接庫.SO開發。
3.
chrome谷歌瀏覽器-DevTool開發者工具-詳細總結
相關 tail justify 任務管理器 log 兩個 停用 表格 需要
chrome的開發者工具可以說是十分強大了,是web開發者的一大利器,作為我個人而言平時用到的幾率很大,相信大家也很常見,但是不要僅僅停留在點選元素看看樣式的層面上哦,跟著我的總結一起學習實踐一下
逆向分析學習指南
代碼 學習 release sdn log 調試器 ase art csdn 1、逆向問題記錄
2、調試器相關筆記
3、逆向分析核心代碼定位
逆向分析學習指南
分布式架構的演進,分析的很詳細,很到位
解決 配置管理 基本 關系型 class mysq 不能 lamp nosql 作者:李小翀鏈接:https://www.zhihu.com/question/22764869/answer/31277656來源:知乎著作權歸作者所有。商業轉載請聯系作者獲得授權,非商業轉載
《逆向分析實戰》數據的存儲及表示形式
函數 最簡 先來 職位 ascii碼表 封裝 process 社區 音頻 本文摘自人民郵電出版社異步社區《逆向分析實戰》一書,點擊查看http://www.epubit.com.cn/book/details/4918關註微信公眾號【異步社區】每周送書
學習過計算機的讀者都
逆向開發基礎工具
ssh協議 nts 之前 臺電 拷貝 解決 編譯 查看 aux 小白:小程,我一直想問,什麽是逆向來著?是逆向行駛嗎?
小程:理解為逆向行駛也沒錯。一般的項目是從無到有,從大唐而來到西方取經,而逆向是從已有的狀態入手,分析出已有的流程與結構的手段。
iOS上的逆向開發,是
Saltstack 自動化運維工具詳細介紹
pre 地址 .tar.gz 好的 publish net 組織 初始 int Saltstack 簡介什麽是saltstack? Saltstack是基於python開發的一套C/S架構配置管理工具? 使用SSL證書簽方的方式進行認證管理? 底層使用ZeroMQ消息隊列p
合金彈頭 逆向分析與外掛制作報告【內聯HOOK】
scm 代碼塊 opc 進行 void HR creat 其它 遊戲數據
一、工具及遊戲介紹
使用工具:Ollydbg,PEID,Cheat Engine
實現功能:玩家無敵
目標:找到全局數據,或關鍵代碼塊。
遊戲版本:合金彈頭1-5代珍藏版
路由器逆向分析------binwalk工具的詳細使用說明
一、binwalk工具的基本用法介紹 1.獲取幫助資訊 $ binwalk -h # 或者 $ binwalk --help 2.韌體分析掃描 $ binwalk firmware.bin # 或者 $ binwalk firmware.bin | head
路由器逆向分析------binwalk工具的安裝
一、binwalk工具執行支援的平臺 Operating System Core Support Optional Feature Support Ease of Installation Linux Excellent Excellent Very easy O
路由器逆向分析------sasquatch和squashfs-tools工具的安裝和使用
一、sasquatch工具的安裝和使用 sasquatch工具支援對 非標準的SquashFS格式的檔案映象 進行解壓並且sasquatch工具也binwalk工具整合的一個功能元件之一。最新版的sasquatch工具是基於squashfs 4.3的原始碼修改而來的
路由器逆向分析------firmware-mod-kit工具安裝和使用說明
一、firmware-mod-kit工具的安裝 firmware-mod-kit工具的功能和binwalk工具的類似,其實firmware-mod-kit工具在功能上有呼叫binwalk工具提供的功能以及其他的韌體解包工具的整合。下載firmware-mod-kit工
路由器逆向分析------MIPS交叉編譯環境的搭建(Buildroot)
為了能在我們熟悉的windows或者ubuntu下開發mips架構的程式,需要搭建mips程式的交叉編譯環境。mips程式的交叉編譯環境的構建需要用編譯Buildroot,Buildroot在編譯的過程中,會下載一些依賴包,所以在Buildroot的編譯安裝過程中必須確
路由器逆向分析------在Linux上安裝IDA Pro
Installing WineHQ packages If you have previously installed a Wine package from another repository, please remove it and any packages that depend on it (
路由器逆向分析------QEMU的基本使用方法(MIPS)
一、QEMU的執行模式 直接摘抄自己《揭祕家用路由器0day漏洞挖掘技術》,網上查了一下也沒有找到令人滿意的QEMU的使用說明,就採用這本書上的介紹。如果後期能夠找到比較滿意的QEMU的使用方法的說明,再新增上來。 QEMU模擬器主要有兩種比較常見的運作模式:Use
記錄金盾加密視訊提取工具被逆向分析過程一
金盾2018SS加密視訊機器碼替換工具的分析過程三 上篇講替換機器碼工具的分析,本次繼續分析同一個包裡帶的視訊提取工具。看圖: 工具使用過程:這裡的WIN7.DLL是主要檔案,我們結合前面分析的,替換機器碼後,在把該DLL注入到播放器內,輸入密碼後,視訊就開始播放了,並在D盤根目錄下生成了一個AV
Andorid逆向-3.IDA工具介紹-靜態分析
IDA安裝就不說了,簡單無腦下一步啪啪就好了( ̄▽ ̄) 1.個人理解:不明白地方,多點幾次就明白意思了 2.這個就是點了Go出現的介面 3.拖拽需要反編譯的檔案,我是小學生英文暫時都看不懂。然後直接點OK 4.簡單介紹下 5. 視窗簡單應用 如何檢視檔
C# & dnspy 使用總結--逆向分析工具
dnspy工具: 非常優秀的C#的反編譯器 一、除錯 1.1 載入模組: 直接將exe或者dll,拖到dnspy中即可。或者 開啟exe,執行起來就會,相關的模組會自動載入進來。 1.2
c&c++反彙編與逆向分析學習筆記(2)--反彙編靜態分析工具IDA
所謂“靜態分析”,是相對於前面提到的“動態分析”而言的。在“動態分析”過程中,偵錯程式載入程式,並以除錯模式執行起來,分析者可以在程式的執行過程中觀察程式的執行流程和計算記過。但是,在實際分析中,很多場合不方便執行目標,比如軟體的某一模組(無法單獨執行)、病
逆向分析涉及的工具及OD快捷鍵
1.逆向工程的工具有哪些? ①16 進位制工具:010Editor,winhex ②PE 工具:PEID,LordPE, ③除錯工具:OD , IDA Pro, windbg ④ARK 工具:pchunter ⑤系統監控工具:火絨劍 ⑥資料包分析工具(抓包工具): Tcp/udp: WireS
Android逆向分析初體驗
目錄 搜索 比較 .com -1 動態調試 總結 為我 修改 一、 準備知識 1. 懂Java Android開發。 2. 懂NDK ,C 語言 Android 動態鏈接庫.SO開發。 3.
chrome谷歌瀏覽器-DevTool開發者工具-詳細總結
相關 tail justify 任務管理器 log 兩個 停用 表格 需要 chrome的開發者工具可以說是十分強大了,是web開發者的一大利器,作為我個人而言平時用到的幾率很大,相信大家也很常見,但是不要僅僅停留在點選元素看看樣式的層面上哦,跟著我的總結一起學習實踐一下
逆向分析學習指南
代碼 學習 release sdn log 調試器 ase art csdn 1、逆向問題記錄 2、調試器相關筆記 3、逆向分析核心代碼定位 逆向分析學習指南
分布式架構的演進,分析的很詳細,很到位
解決 配置管理 基本 關系型 class mysq 不能 lamp nosql 作者:李小翀鏈接:https://www.zhihu.com/question/22764869/answer/31277656來源:知乎著作權歸作者所有。商業轉載請聯系作者獲得授權,非商業轉載
《逆向分析實戰》數據的存儲及表示形式
函數 最簡 先來 職位 ascii碼表 封裝 process 社區 音頻 本文摘自人民郵電出版社異步社區《逆向分析實戰》一書,點擊查看http://www.epubit.com.cn/book/details/4918關註微信公眾號【異步社區】每周送書 學習過計算機的讀者都
逆向開發基礎工具
ssh協議 nts 之前 臺電 拷貝 解決 編譯 查看 aux 小白:小程,我一直想問,什麽是逆向來著?是逆向行駛嗎? 小程:理解為逆向行駛也沒錯。一般的項目是從無到有,從大唐而來到西方取經,而逆向是從已有的狀態入手,分析出已有的流程與結構的手段。 iOS上的逆向開發,是
Saltstack 自動化運維工具詳細介紹
pre 地址 .tar.gz 好的 publish net 組織 初始 int Saltstack 簡介什麽是saltstack? Saltstack是基於python開發的一套C/S架構配置管理工具? 使用SSL證書簽方的方式進行認證管理? 底層使用ZeroMQ消息隊列p
合金彈頭 逆向分析與外掛制作報告【內聯HOOK】
scm 代碼塊 opc 進行 void HR creat 其它 遊戲數據 一、工具及遊戲介紹 使用工具:Ollydbg,PEID,Cheat Engine 實現功能:玩家無敵 目標:找到全局數據,或關鍵代碼塊。 遊戲版本:合金彈頭1-5代珍藏版